ISSN 1977-0677
Official Journal
of the European Union
L 139

English edition
Legislation
Volume 59
26 May 2016
|
ISSN 1977-0677 |
||
|
Official Journal of the European Union |
L 139 |
|

|
||
|
English edition |
Legislation |
Volume 59 |
|
|
|
|
|
(1) Text with EEA relevance |
|
EN |
Acts whose titles are printed in light type are those relating to day-to-day management of agricultural matters, and are generally valid for a limited period. The titles of all other Acts are printed in bold type and preceded by an asterisk. |
II Non-legislative acts
REGULATIONS
|
26.5.2016 |
EN |
Official Journal of the European Union |
L 139/1 |
COMMISSION IMPLEMENTING REGULATION (EU) 2016/799
of 18 March 2016
implementing Regulation (EU) No 165/2014 of the European Parliament and of the Council laying down the requirements for the construction, testing, installation, operation and repair of tachographs and their components
(Text with EEA relevance)
THE EUROPEAN COMMISSION,
Having regard to the Treaty on the Functioning of the European Union,
Having regard to Regulation (EU) No 165/2014 of the European Parliament and of the Council of 4 February 2014 on tachographs in road transport (1), and in particular Articles 11 and 12(7) thereof,
Whereas:
|
(1) |
Regulation (EU) No 165/2014 has introduced second-generation digital tachographs called smart tachographs, which include a connection to the global navigation satellite system (‘GNSS’) facility, a remote early detection communication facility, and an interface with intelligent transport systems. The specifications for the technical requirements for the construction of smart tachographs should be set up. |
|
(2) |
The remote early detection facility established by Article 9(4) of Regulation (EU) No 165/2014 should transmit to a roadside control officer the data of the digital tachograph and the information concerning the weights and weight per axles of the complete vehicle combination (tractor and trailers or semi-trailers), in accordance with Directive 96/53/EC of the European Parliament and of the Council (2). That should enable an effective and quick check of vehicles by the control authorities, with fewer electronic devices in the vehicle cab. |
|
(3) |
In accordance with Directive 96/53/EC, the remote early detection facility should use the CEN DSRC standards (3) referred to in that Directive, at the frequency band of 5 795-5 805 MHz. As that frequency band is used for electronic tolling as well, and in order to avoid interference between tolling and control applications, control officers should not use the remote early detection facility on a toll plaza. |
|
(4) |
New security mechanisms for maintaining the level of security of the digital tachograph should be introduced with the smart tachograph to address current security vulnerabilities. One of such vulnerabilities is the absence of expiry dates of digital certificates. In order to comply with the best practices in security matters, it is recommended that the use of digital certificates without expiry dates should be avoided. The normal operation validity period of vehicle units should be 15 years, starting on the issuing date of the vehicle unit digital certificates. Vehicle units should be replaced after that validity period. |
|
(5) |
The provision of secured and reliable positioning information is an essential element of the effective operation of smart tachographs. Therefore, it is appropriate to ensure their compatibility with the added value services provided by the Galileo programme as set out in Regulation (EU) No 1285/2013 of the European Parliament and of the Council (4) in order to improve the security of the smart tachograph. |
|
(6) |
In accordance with Articles 8(1), 9(1) and 10(1) and (2) of Regulation (EU) No 165/2014, the security mechanisms introduced by that Regulation should apply 36 months after the entry into force of the necessary implementing acts in order to allow the manufacturers to develop the new generation of smart tachographs, and receive their type-approval certificates from the competent authorities. |
|
(7) |
In accordance with Regulation (EU) No 165/2014, vehicles registered for the first time in a Member State 36 months after the entry into force of this Commission Regulation, should be equipped with a smart tachograph compliant with the requirements of this Commission Regulation. In any case, all vehicles operating in a Member State other than their Member State of registration should be equipped with a compliant smart tachograph 15 years after the date of application of those requirements. |
|
(8) |
Commission Regulation (EC) No 68/2009 (5) allowed, during a transitional period expiring on 31 December 2013, the use of an adaptor to make possible the installation of tachographs in M1 and N1 type vehicles. Due to technical difficulties related to finding an alternative to the use of the adaptor, the experts of the automotive and tachograph industry, together with the Commission, concluded that no alternative solution to the adaptor was feasible without entailing high costs for industry, which would be disproportionate to the size of the market. Therefore, the use of the adaptor in M1 and N1 type vehicles should be allowed indefinitely. |
|
(9) |
The measures provided for in this Regulation are in accordance with the opinion of the Committee referred to in Article 42(3) of Regulation (EU) No 165/2014, |
HAS ADOPTED THIS REGULATION:
Article 1
Subject matter and scope
1. This Regulation lays down the provisions necessary for the uniform application of the following aspects regarding tachographs:
|
(a) |
recording of the position of the vehicle at certain points during the daily working period of the driver; |
|
(b) |
remote early detection of possible manipulation or misuse of smart tachographs; |
|
(c) |
interface with intelligent transport systems; |
|
(d) |
the administrative and technical requirements for the type-approval procedures of tachographs, including the security mechanisms. |
2. The construction, testing, installation, inspection, operation and repair of smart tachographs and their components, shall comply with the technical requirements set out in Annex 1C to this Regulation.
3. Tachographs other than smart tachographs shall continue, as regards construction, testing, installation, inspection, operation and repair, to comply with the requirements of either Annex 1 or Annex 1B to Council Regulation (EEC) No 3821/85 (6), as applicable.
4. Pursuant to Article 10d of Directive 96/53/EC, the remote early detection facility shall also transmit the weight data provided by an internal on-board weighing system, for the purpose of early fraud detection.
Article 2
Definitions
For the purposes of this Regulation, the definitions laid down in Article 2 of Regulation (EU) No 165/2014 shall apply.
In addition, the following definitions shall apply:
|
(1) |
‘digital tachograph’ or ‘first generation tachograph’ means a digital tachograph other than a smart tachograph; |
|
(2) |
‘external GNSS facility’ means a facility which contains the GNSS receiver when the vehicle unit is not a single unit, as well as other components needed to protect the communication of data about position to the rest of the vehicle unit; |
|
(3) |
‘information folder’ means the complete folder, in electronic or paper form, containing all the information supplied by the manufacturer or its agent to the type-approval authority for the purpose of the type-approval of a tachograph or a component thereof, including the certificates referred to in Article 12(3) of Regulation (EU) No 165/2014, the performance of the tests defined in Annex 1C to this Regulation, as well as drawings, photographs, and other relevant documents; |
|
(4) |
‘information package’ means the information folder, in electronic or paper form, accompanied by any other documents added by the type-approval authority to the information folder in the course of carrying out their functions including, at the end of the type-approval process, the EC type-approval certificate of the tachograph or a component thereof; |
|
(5) |
‘index to the information package’ means the document listing the numbered contents of the information package identifying all the relevant parts of this package. The format of that document shall distinguish the successive steps in the EC type-approval process, including the dates of any revisions and updating of that package; |
|
(6) |
‘remote early detection facility’ means the equipment of the vehicle unit which is used to perform targeted roadside checks; |
|
(7) |
‘smart tachograph’ or ‘second generation tachograph’ means a digital tachograph complying with Articles 8, 9 and 10 of Regulation (EU) No 165/2014 as well as with Annex 1C to this Regulation; |
|
(8) |
‘tachograph component’ or ‘component’ means any of the following elements: the vehicle unit, the motion sensor, the tachograph card, the record sheet, the external GNSS facility and the remote early detection facility; |
|
(9) |
‘type-approval authority’ means the authority of a Member State competent to carry out the type-approval of the tachograph or of its components, the authorisation process, the issuing and, if appropriate, withdrawing of type-approval certificates, acting as the contact point for the type-approval authorities of other Member States and ensuring that the manufacturers meet their obligations relating to the conformity with the requirement of this Regulation. |
Article 3
Location-based services
1. Manufacturers shall ensure that smart tachographs are compatible with the positioning services provided by the Galileo and the European Geostationary Navigation Overlay Service (‘EGNOS’) systems.
2. In addition to the systems referred to in paragraph 1, manufacturers may also choose to ensure compatibility with other satellite navigation systems.
Article 4
Procedure for type-approval of a tachograph and tachograph components
1. A manufacturer or its agent shall submit an application for type-approval of a tachograph or any of its components, or group of components, to the type-approval authorities designated by each Member State. It shall consist of an information folder containing the information for each of the components concerned including, where applicable, the type-approval certificates of other components necessary to complete the tachograph, as well as any other relevant documents.
2. A Member State shall grant type-approval to any tachograph, component or group of components that conforms to the administrative and technical requirements referred to in Article 1(2) or (3), as applicable. In that case, the type-approval authority shall issue to the applicant a type-approval certificate that shall conform to the model laid down in Annex II to this Regulation.
3. The type-approval authority may request the manufacturer or its agent to supply any additional information.
4. The manufacturer or its agent shall make available to the type-approval authorities, as well as to the entities responsible for issuing the certificates referred to in Article 12(3) of Regulation (EU) No 165/2014, as many tachographs or tachograph components as are necessary to enable the type-approval procedure to be conducted satisfactorily.
5. Where the manufacturer or its agent seeks a type-approval of certain components or groups of components of a tachograph, he shall provide the type-approval authorities with the other components, already type-approved, as well as other parts necessary for the construction of the complete tachograph, in order for those authorities to conduct the necessary tests.
Article 5
Modifications to type-approvals
1. The manufacturer or its agent shall inform without delay the type-approval authorities that granted the original type-approval, about any modification in software or hardware of the tachograph or in the nature of the materials used for its manufacture which are recorded in the information package and shall submit an application for the modification of the type-approval.
2. The type-approval authorities may revise or extend an existing type-approval, or issue a new type-approval according to the nature and characteristics of the modifications.
A ‘revision’ shall be made where the type-approval authority considers that the modifications in software or hardware of the tachograph or in the nature of materials used for its manufacture are minor. In such cases, the type-approval authority shall issue the revised documents of the information package, indicating the nature of the modifications made and the date of their approval. An updated version of the information package in a consolidated form, accompanied by a detailed description of the modifications made, shall be sufficient to meet this requirement.
An ‘extension’ shall be made where the type-approval authority considers that the modifications in software or hardware of the tachograph or in the nature of materials used for its manufacture are substantial. In such cases, it may request that new tests be conducted and inform the manufacturer or its agent accordingly. If those tests prove satisfactory, the type-approval authority shall issue a revised type-approval certificate containing a number referring to the extension granted. The type-approval certificate shall mention the reason of the extension and its date of issue.
3. The index to the information package shall indicate the date of the most recent extension or revision of the type-approval, or the date of the most recent consolidation of the updated version of the type-approval.
4. A new type-approval shall be necessary when the requested modifications to the type-approved tachograph or its components would lead to the issuance of a new security or interoperability certificate.
Article 6
Entry into force
This Regulation shall enter into force on the twentieth day following that of its publication in the Official Journal of the European Union.
It shall apply from 2 March 2016.
However, the Annexes shall apply from 2 March 2019 with the exception of Appendix 16 which shall apply from 2 March 2016.
This Regulation shall be binding in its entirety and directly applicable in all Member States.
Done at Brussels, 18 March 2016.
For the Commission
The President
Jean-Claude JUNCKER
(2) Council Directive 96/53/EC of 25 July 1996 laying down for certain road vehicles circulating within the Community the maximum authorized dimensions in national and international traffic and the maximum authorized weights in international traffic (OJ L 235, 17.9.1996, p.59)
(3) Dedicated Short Range Communications standards of the European Standardisation Committee (CEN) EN 12253, EN 12795, EN 12834, EN 13372 and ISO 14906.
(4) Regulation (EU) No 1285/2013 of the European Parliament and of the Council of 11 December 2013 on the implementation and exploitation of European satellite navigation systems and repealing Council Regulation (EC) No 876/2002 and Regulation (EC) No 683/2008 of the European Parliament and of the Council (OJ L 347, 20.12.2013, p. 1).
(5) Commission Regulation (EC) No 68/2009 of 23 January 2009 adapting for the ninth time to technical progress Council Regulation (EEC) No 3821/85 on recording equipment in road transport (OJ L 21, 24.1.2009, p.3).
(6) Council Regulation (EEC) No 3821/85 of 20 December 1985 on recording equipment in road transport (OJ L 370, 31.12.1985, p.8).
ANNEX I C
Requirements for construction, testing, installation, and inspection
| INTRODUCTION | 12 |
|
1. |
DEFINITIONS | 13 |
|
2. |
GENERAL CHARACTERISTICS AND FUNCTIONS OF THE RECORDING EQUIPMENT | 19 |
|
2.1 |
General characteristics | 19 |
|
2.2 |
Functions | 20 |
|
2.3 |
Modes of operation | 21 |
|
2.4 |
Security | 22 |
|
3. |
CONSTRUCTION AND FUNCTIONAL REQUIREMENTS FOR RECORDING EQUIPMENT | 22 |
|
3.1 |
Monitoring cards insertion and withdrawal | 22 |
|
3.2 |
Speed, position and distance measurement | 23 |
|
3.2.1 |
Measurement of distance travelled | 23 |
|
3.2.2 |
Measurement of speed | 23 |
|
3.2.3 |
Measurement of position | 24 |
|
3.3 |
Time measurement | 24 |
|
3.4 |
Monitoring driver activities | 24 |
|
3.5 |
Monitoring driving status | 25 |
|
3.6 |
Driver's entries | 25 |
|
3.6.1 |
Entry of places where daily work periods begin and/or end | 25 |
|
3.6.2 |
Manual entry of driver activities and driver consent for ITS interface | 25 |
|
3.6.3 |
Entry of specific conditions | 27 |
|
3.7 |
Company locks management | 27 |
|
3.8 |
Monitoring control activities | 28 |
|
3.9 |
Detection of events and/or faults | 28 |
|
3.9.1 |
‘Insertion of a non-valid card’ event | 28 |
|
3.9.2 |
‘Card conflict’ event | 28 |
|
3.9.3 |
‘Time overlap’ event | 28 |
|
3.9.4 |
‘Driving without an appropriate card’ event | 29 |
|
3.9.5 |
‘Card insertion while driving’ event | 29 |
|
3.9.6 |
‘Last card session not correctly closed’ event | 29 |
|
3.9.7 |
‘Over speeding’ event | 29 |
|
3.9.8 |
‘Power supply interruption’ event | 29 |
|
3.9.9 |
‘Communication error with the remote communication facility’ event | 29 |
|
3.9.10 |
‘Absence of position information from GNSS receiver’ event | 29 |
|
3.9.11 |
‘Communication error with the external GNSS facility’ event | 30 |
|
3.9.12 |
‘Motion data error’ event | 30 |
|
3.9.13 |
‘Vehicle motion conflict’ event | 30 |
|
3.9.14 |
‘Security breach attempt’ event | 30 |
|
3.9.15 |
‘Time conflict’ event | 30 |
|
3.9.16 |
‘Card’ fault | 30 |
|
3.9.17 |
‘Recording equipment’ fault | 30 |
|
3.10 |
Built-in and self-tests | 31 |
|
3.11 |
Reading from data memory | 31 |
|
3.12 |
Recording and storing in the data memory | 31 |
|
3.12.1 |
Equipment identification data | 32 |
|
3.12.1.1 |
Vehicle unit identification data | 32 |
|
3.12.1.2 |
Motion sensor identification data | 32 |
|
3.12.1.3 |
Global Navigation Satellite Systems identification data | 33 |
|
3.12.2 |
Keys and certificates | 33 |
|
3.12.3 |
Driver or workshop card insertion and withdrawal data | 33 |
|
3.12.4 |
Driver activity data | 34 |
|
3.12.5 |
Places and positions where daily work periods begin, end, and/or where 3 hours' continuous driving time is reached | 34 |
|
3.12.6 |
Odometer data | 35 |
|
3.12.7 |
Detailed speed data | 35 |
|
3.12.8 |
Events data | 35 |
|
3.12.9 |
Faults data | 37 |
|
3.12.10 |
Calibration data | 38 |
|
3.12.11 |
Time adjustment data | 39 |
|
3.12.12 |
Control activity data | 39 |
|
3.12.13 |
Company locks data | 39 |
|
3.12.14 |
Download activity data | 39 |
|
3.12.15 |
Specific conditions data | 40 |
|
3.12.16 |
Tachograph card data | 40 |
|
3.13 |
Reading from tachograph cards | 40 |
|
3.14 |
Recording and storing on tachograph cards | 40 |
|
3.14.1 |
Recording and storing in first generation tachograph cards | 40 |
|
3.14.2 |
Recording and storing in second generation tachograph cards | 41 |
|
3.15 |
Displaying | 41 |
|
3.15.1 |
Default display | 42 |
|
3.15.2 |
Warning display | 43 |
|
3.15.3 |
Menu access | 43 |
|
3.15.4 |
Other displays | 43 |
|
3.16 |
Printing | 43 |
|
3.17 |
Warnings | 44 |
|
3.18 |
Data downloading to external media | 45 |
|
3.19 |
Remote communication for targeted roadside checks | 45 |
|
3.20 |
Output data to additional external devices | 46 |
|
3.21 |
Calibration | 47 |
|
3.22 |
Roadside calibration checking | 47 |
|
3.23 |
Time adjustment | 48 |
|
3.24 |
Performance characteristics | 48 |
|
3.25 |
Materials | 48 |
|
3.26 |
Markings | 49 |
|
4. |
CONSTRUCTION AND FUNCTIONAL REQUIREMENTS FOR TACHOGRAPH CARDS | 49 |
|
4.1 |
Visible data | 49 |
|
4.2 |
Security | 52 |
|
4.3 |
Standards | 53 |
|
4.4 |
Environmental and electrical specifications | 53 |
|
4.5 |
Data storage | 53 |
|
4.5.1 |
Elementary files for identification and card management | 54 |
|
4.5.2 |
IC card identification | 54 |
|
4.5.2.1 |
Chip identification | 54 |
|
4.5.2.2 |
DIR (only present in second generation tachograph cards) | 54 |
|
4.5.2.3 |
ATR information (conditional, only present in second generation tachograph cards) | 54 |
|
4.5.2.4 |
Extended length information (conditional, only present in second generation tachograph cards) | 55 |
|
4.5.3 |
Driver card | 55 |
|
4.5.3.1 |
Tachograph application (accessible to first and second generation vehicle units) | 55 |
|
4.5.3.1.1 |
Application identification | 55 |
|
4.5.3.1.2 |
Key and certificates | 55 |
|
4.5.3.1.3 |
Card identification | 55 |
|
4.5.3.1.4 |
Card holder identification | 55 |
|
4.5.3.1.5 |
Card download | 55 |
|
4.5.3.1.6 |
Driving licence information | 55 |
|
4.5.3.1.7 |
Events data | 56 |
|
4.5.3.1.8 |
Faults data | 56 |
|
4.5.3.1.9 |
Driver activity data | 57 |
|
4.5.3.1.10 |
Vehicles used data | 57 |
|
4.5.3.1.11 |
Places where daily work periods start and/or end | 58 |
|
4.5.3.1.12 |
Card session data | 58 |
|
4.5.3.1.13 |
Control activity data | 58 |
|
4.5.3.1.14 |
Specific conditions data | 58 |
|
4.5.3.2 |
Tachograph generation 2 application (not accessible to first generation vehicle unit) | 59 |
|
4.5.3.2.1 |
Application identification | 59 |
|
4.5.3.2.2 |
Keys and certificates | 59 |
|
4.5.3.2.3 |
Card identification | 59 |
|
4.5.3.2.4 |
Card holder identification | 59 |
|
4.5.3.2.5 |
Card download | 59 |
|
4.5.3.2.6 |
Driving licence information | 59 |
|
4.5.3.2.7 |
Events data | 59 |
|
4.5.3.2.8 |
Faults data | 60 |
|
4.5.3.2.9 |
Driver activity data | 61 |
|
4.5.3.2.10 |
Vehicles used data | 61 |
|
4.5.3.2.11 |
Places and positions where daily work periods start and/or end | 62 |
|
4.5.3.2.12 |
Card session data | 62 |
|
4.5.3.2.13 |
Control activity data | 62 |
|
4.5.3.2.14 |
Specific conditions data | 63 |
|
4.5.3.2.15 |
Vehicle units used data | 63 |
|
4.5.3.2.16 |
Three hours' continuous driving places data | 63 |
|
4.5.4 |
Workshop card | 63 |
|
4.5.4.1 |
Tachograph application (accessible to first and second generation vehicle units) | 63 |
|
4.5.4.1.1 |
Application identification | 63 |
|
4.5.4.1.2 |
Keys and certificates | 63 |
|
4.5.4.1.3 |
Card identification | 64 |
|
4.5.4.1.4 |
Card holder identification | 64 |
|
4.5.4.1.5 |
Card download | 64 |
|
4.5.4.1.6 |
Calibration and time adjustment data | 64 |
|
4.5.4.1.7 |
Events and faults data | 65 |
|
4.5.4.1.8 |
Driver activity data | 65 |
|
4.5.4.1.9 |
Vehicles used data | 65 |
|
4.5.4.1.10 |
Daily work periods start and/or end data | 65 |
|
4.5.4.1.11 |
Card session data | 65 |
|
4.5.4.1.12 |
Control activity data | 65 |
|
4.5.4.1.13 |
Specific conditions data | 65 |
|
4.5.4.2 |
Tachograph generation 2 application (not accessible to first generation vehicle unit) | 65 |
|
4.5.4.2.1 |
Application identification | 65 |
|
4.5.4.2.2 |
Keys and certificates | 66 |
|
4.5.4.2.3 |
Card identification | 66 |
|
4.5.4.2.4 |
Card holder identification | 66 |
|
4.5.4.2.5 |
Card download | 66 |
|
4.5.4.2.6 |
Calibration and time adjustment data | 66 |
|
4.5.4.2.7 |
Events and faults data | 67 |
|
4.5.4.2.8 |
Driver activity data | 67 |
|
4.5.4.2.9 |
Vehicles used data | 67 |
|
4.5.4.2.10 |
Daily work periods start and/or end data | 67 |
|
4.5.4.2.11 |
Card session data | 67 |
|
4.5.4.2.12 |
Control activity data | 67 |
|
4.5.4.2.13 |
Vehicle units used data | 67 |
|
4.5.4.2.14 |
Three hours' continuous driving places data | 68 |
|
4.5.4.2.15 |
Specific conditions data | 68 |
|
4.5.5 |
Control card | 68 |
|
4.5.5.1 |
Tachograph application (accessible to first and second generation vehicle units) | 68 |
|
4.5.5.1.1 |
Application identification | 68 |
|
4.5.5.1.2 |
Keys and certificates | 68 |
|
4.5.5.1.3 |
Card identification | 68 |
|
4.5.5.1.4 |
Card holder identification | 68 |
|
4.5.5.1.5 |
Control activity data | 69 |
|
4.5.5.2 |
Tachograph G2 application (not accessible to first generation vehicle unit) | 69 |
|
4.5.5.2.1 |
Application identification | 69 |
|
4.5.5.2.2 |
Keys and certificates | 69 |
|
4.5.5.2.3 |
Card identification | 69 |
|
4.5.5.2.4 |
Card holder identification | 69 |
|
4.5.5.2.5 |
Control activity data | 70 |
|
4.5.6 |
Company card | 70 |
|
4.5.6.1 |
Tachograph application (accessible to first and second generation vehicle units) | 70 |
|
4.5.6.1.1 |
Application identification | 70 |
|
4.5.6.1.2 |
Keys and certificates | 70 |
|
4.5.6.1.3 |
Card identification | 70 |
|
4.5.6.1.4 |
Card holder identification | 70 |
|
4.5.6.1.5 |
Company activity data | 70 |
|
4.5.6.2 |
Tachograph G2 application (not accessible to first generation vehicle unit) | 71 |
|
4.5.6.2.1 |
Application identification | 71 |
|
4.5.6.2.2 |
Keys and certificates | 71 |
|
4.5.6.2.3 |
Card identification | 71 |
|
4.5.6.2.4 |
Card holder identification | 71 |
|
4.5.6.2.5 |
Company activity data | 71 |
|
5. |
INSTALLATION OF RECORDING EQUIPMENT | 72 |
|
5.1 |
Installation | 72 |
|
5.2 |
Installation plaque | 73 |
|
5.3 |
Sealing | 74 |
|
6. |
CHECKS, INSPECTIONS AND REPAIRS | 74 |
|
6.1 |
Approval of fitters, workshops and vehicle manufacturers | 74 |
|
6.2 |
Check of new or repaired instruments | 75 |
|
6.3 |
Installation inspection | 75 |
|
6.4 |
Periodic inspections | 75 |
|
6.5 |
Measurement of errors | 76 |
|
6.6 |
Repairs | 76 |
|
7. |
CARD ISSUING | 76 |
|
8. |
TYPE-APPROVAL OF RECORDING EQUIPMENT AND TACHOGRAPH CARDS | 77 |
|
8.1 |
General points | 77 |
|
8.2 |
Security certificate | 78 |
|
8.3 |
Functional certificate | 78 |
|
8.4 |
Interoperability certificate | 78 |
|
8.5 |
Type-approval certificate | 79 |
|
8.6 |
Exceptional procedure: first interoperability certificates for 2nd generation recording equipment and tachograph cards | 80 |
INTRODUCTION
The first generation digital tachograph system has been deployed since 1 May 2006. It may be used until its end of life for domestic transportation. For international transportation, instead, 15 years after the entry into force of this Commission Regulation, all vehicles shall be equipped with a compliant second generation smart tachograph, introduced by this Regulation.
This Annex contains second generation recording equipment and tachograph cards requirements. Starting from its introduction date, second generation recording equipment shall be installed in vehicles registered for the first time, and second generation tachograph cards shall be issued.
In order to foster a smooth introduction of the second generation tachograph system:
|
— |
second generation tachograph cards shall be designed to be also used in first generation vehicle units, |
|
— |
replacement of valid first generation tachograph cards at the introduction date shall not be requested. |
This will allow drivers to keep their unique driver card and use both systems with it.
Second generation recording equipment shall however only be calibrated using second generation workshop cards.
This Annex contains all requirements related to the interoperability between the first and the second generation tachograph system.
Appendix 15 contains additional details about how the coexistence of the two systems shall be managed.
List of Appendixes
|
App 1: |
DATA DICTIONARY |
|
App 2: |
TACHOGRAPH CARDS SPECIFICATION |
|
App 3: |
PICTOGRAMS |
|
App 4: |
PRINTOUTS |
|
App 5: |
DISPLAY |
|
App 6: |
FRONT CONNECTOR FOR CALIBRATION AND DOWNLOAD |
|
App 7: |
DATA DOWNLOADING PROTOCOLS |
|
App 8: |
CALIBRATION PROTOCOL |
|
App 9: |
TYPE-APPROVAL AND LIST OF MINIMUM REQUIRED TESTS |
|
App 10: |
SECURITY REQUIREMENTS |
|
App 11: |
COMMON SECURITY MECHANISMS |
|
App 12: |
POSITIONING BASED ON GLOBAL NAVIGATION SATELLITE SYSTEM (GNSS) |
|
App 13: |
ITS INTERFACE |
|
App 14: |
REMOTE COMMUNICATION FUNCTION |
|
App 15: |
MIGRATION: MANAGING THE COEXISTENCE OF EQUIPMENT GENERATIONS |
|
App 16: |
ADAPTOR FOR M1 AND N1 CATEGORY VEHICLES |
1. DEFINITIONS
In this Annex:
|
(a) |
‘activation’ means: the phase in which the tachograph becomes fully operational and implements all functions, including security functions, through the use of a workshop card; |
|
(b) |
‘authentication’ means: a function intended to establish and verify a claimed identity; |
|
(c) |
‘authenticity’ means: the property that information is coming from a party whose identity can be verified; |
|
(d) |
‘built-in test (BIT)’ means: tests run at request, triggered by the operator or by external equipment; |
|
(e) |
‘calendar day’ means: a day ranging from 00:00 hours to 24:00 hours. All calendar days relate to UTC time (Universal Time Coordinated); |
|
(f) |
‘calibration’ of a smart tachograph means: updating or confirming vehicle parameters to be held in the data memory. Vehicle parameters include vehicle identification (VIN, VRN and registering Member State) and vehicle characteristics (w, k, l, tyre size, speed-limiting device setting (if applicable), current UTC time, current odometer value); during the calibration of a recording equipment, the types and identifiers of all type-approval relevant seals in place shall also be stored in the data memory; any update or confirmation of UTC time only, shall be considered as a time adjustment and not as a calibration, provided it does not contradict Requirement 409; calibrating recording equipment requires the use of a workshop card; |
|
(g) |
‘card number’ means: a 16-alphanumerical character number that uniquely identifies a tachograph card within a Member State. The card number includes a card consecutive index (if applicable), a card replacement index and a card renewal index; a card is therefore uniquely identified by the code of the issuing Member State and the card number; |
|
(h) |
‘card consecutive index’ means: the 14th alphanumerical character of a card number that is used to differentiate the different cards issued to a company, a workshop or a control authority entitled to be issued several tachograph cards. The company, the workshop or the control authority is uniquely identified by the 13 first characters of the card number; |
|
(i) |
‘card renewal index’ means: the 16th alphanumerical character of a card number which is incremented each time a tachograph card is renewed; |
|
(j) |
‘card replacement index’ means: the 15th alpha-numerical character of a card number which is incremented each time a tachograph card is replaced; |
|
(k) |
‘characteristic coefficient of the vehicle’ means: the numerical characteristic giving the value of the output signal emitted by the part of the vehicle linking it with the recording equipment (gearbox output shaft or axle) while the vehicle travels a distance of one kilometre under standard test conditions as defined under requirement 414. The characteristic coefficient is expressed in impulses per kilometre (w = … imp/km); |
|
(l) |
‘company card’ means: a tachograph card issued by the authorities of a Member State to a transport undertaking needing to operate vehicles fitted with a tachograph, which identifies the transport undertaking and allows for the displaying, downloading and printing of the data, stored in the tachograph, which have been locked by that transport undertaking; |
|
(m) |
‘constant of the recording equipment’ means: the numerical characteristic giving the value of the input signal required to show and record a distance travelled of one kilometre; this constant shall be expressed in impulses per kilometre (k = … imp/km); |
|
(n) |
‘continuous driving time’ is computed within the recording equipment as (1): the continuous driving time is computed as the current accumulated driving times of a particular driver, since the end of his last AVAILABILITY or BREAK/REST or UNKNOWN (2) period of 45 minutes or more (this period may have been split according to Regulation (EC) No 561/2006 of the European Parliament and of the Council (3)). The computations involved take into account, as needed, past activities stored on the driver card. When the driver has not inserted his card, the computations involved are based on the data memory recordings related to the current period where no card was inserted and related to the relevant slot; |
|
(o) |
‘control card’ means: a tachograph card issued by the authorities of a Member State to a national competent control authority which identifies the control body and, optionally, the control officer, and which allows access to the data stored in the data memory or in the driver cards and, optionally, in the workshop cards for reading, printing and/or downloading; It shall also give access to the roadside calibration checking function and to data on the remote early detection communication reader; |
|
(p) |
‘cumulative break time’ is computed within the recording equipment as (1): the cumulative break from driving time is computed as the current accumulated AVAILABILITY or BREAK/REST or UNKNOWN (2) times of 15 minutes or more of a particular driver, since the end of his last AVAILABILITY or BREAK/REST or UNKNOWN (2) period of 45 minutes or more (this period may have been split according to Regulation (EC) No 561/2006). The computations involved take into account, as needed, past activities stored on the driver card. Unknown periods of negative duration (start of unknown period > end of unknown period) due to time overlaps between two different sets of recording equipment, are not taken into account for the computation. When the driver has not inserted his card, the computations involved are based on the data memory recordings related to the current period where no card was inserted and related to the relevant slot; |
|
(q) |
‘data memory’ means: an electronic data storage device built into the recording equipment; |
|
(r) |
‘digital signature’ means: data appended to, or a cryptographic transformation of, a block of data that allows the recipient of the block of data to prove the authenticity and integrity of the block of data; |
|
(s) |
‘downloading’ means: the copying, together with the digital signature, of a part, or of a complete set, of data files recorded in the data memory of the vehicle unit or in the memory of a tachograph card, provided that this process does not alter or delete any stored data; manufacturers of smart tachograph vehicle units and manufacturers of equipment designed and intended to download data files shall take all reasonable steps to ensure that the downloading of such data can be performed with the minimum delay by transport undertakings or drivers; The downloading of the detailed speed file may not be necessary to establish compliance with Regulation (EC) No 561/2006, but may be used for other purposes such as accident investigation; |
|
(t) |
‘driver card’ means: a tachograph card, issued by the authorities of a Member State to a particular driver, which identifies the driver and allows for the storage of driver activity data; |
|
(u) |
‘effective circumference of the wheels’ means: the average of the distances travelled by each of the wheels moving the vehicle (driving wheels) in the course of one complete rotation. The measurement of these distances shall be made under standard test conditions as defined under requirement 414 and is expressed in the form ‘l = … mm’. Vehicle manufacturers may replace the measurement of these distances by a theoretical calculation which takes into account the distribution of the weight on the axles, vehicle unladen in normal running order (4). The methods for such theoretical calculation are subject to approval by a competent Member State authority and can take place only before tachograph activation; |
|
(v) |
‘event’ means: an abnormal operation detected by the smart tachograph which may result from a fraud attempt; |
|
(w) |
‘external GNSS facility’ means a facility which contains the GNSS receiver when the vehicle unit is not a single unit as well as other components needed to protect the communication of position data to the rest of the vehicle unit; |
|
(x) |
‘fault’ means: abnormal operation detected by the smart tachograph which may come from an equipment malfunction or failure; |
|
(y) |
‘GNSS receiver’ means: an electronic device that receives and digitally processes the signals from one or more Global Navigation Satellite System(s) (GNSS in English) in order to provide position, speed and time information; |
|
(z) |
‘installation’ means: the mounting of a tachograph in a vehicle; |
|
(aa) |
‘interoperability’ means: the capacity of systems and the underlying business processes to exchange data and to share information; |
|
(bb) |
‘interface’ means: a facility between systems which provides the media through which they can connect and interact; |
|
(cc) |
‘position’ means: geographical coordinates of the vehicle at a given time; |
|
(dd) |
‘motion sensor’ means: a part of the tachograph, providing a signal representative of vehicle speed and/or distance travelled; |
|
(ee) |
‘non-valid card’ means: a card detected as faulty, or which initial authentication failed, or whose start of validity date is not yet reached, or whose expiry date has passed; |
|
(ff) |
‘open standard’ means: a standard set out in a standard specification document available freely or at a nominal charge which it is permissible to copy, distribute or use for no fee or for a nominal fee; |
|
(gg) |
‘out of scope’ means: when the use of the recording equipment is not required, according to the provisions of Regulation (EC) No 561/2006; |
|
(hh) |
‘over speeding’ means: exceeding the authorised speed of the vehicle, defined as any period of more than 60 seconds during which the vehicle's measured speed exceeds the limit for setting the speed limitation device laid down in Council Directive 92/6/EEC (5), as last amended; |
|
(ii) |
‘periodic inspection’ means: a set of operations performed to check that the tachograph works properly, that its settings correspond to the vehicle parameters, and that no manipulation devices are attached to the tachograph; |
|
(jj) |
‘printer’ means: component of the recording equipment which provides printouts of stored data; |
|
(kk) |
‘remote early detection communication’ means: communication between the remote early detection communication facility and the remote early detection communication reader during targeted roadside checks with the aim of remotely detecting possible manipulation or misuse of recording equipment; |
|
(ll) |
‘remote communication facility’ means: the equipment of the vehicle unit which is used to perform targeted roadside checks; |
|
(mm) |
‘remote early detection communication reader’ means: the system used by control officers for targeted roadside checks. |
|
(nn) |
‘renewal’ means: issue of a new tachograph card when an existing card reaches its expiry date, or is malfunctioning and has been returned to the issuing authority. Renewal always implies the certainty that two valid cards do not coexist; |
|
(oo) |
‘repair’ means: any repair of a motion sensor or of a vehicle unit or of a cable that requires the disconnection of its power supply, or its disconnection from other tachograph components, or the opening of the motion sensor or vehicle unit; |
|
(pp) |
‘card replacement’ means: issue of a tachograph card in replacement of an existing card, which has been declared lost, stolen or malfunctioning and has not been returned to the issuing authority. Replacement always implies a risk that two valid cards may coexist; |
|
(qq) |
‘security certification’ means: process to certify, by a common criteria certification body, that the recording equipment (or component) or the tachograph card under investigation fulfils the security requirements defined in the relative protection profiles; |
|
(rr) |
‘self test’ means: tests run cyclically and automatically by the recording equipment to detect faults; |
|
(ss) |
‘time measurement’ means: a permanent digital record of the coordinated universal date and time (UTC); |
|
(tt) |
‘time adjustment’ means: an automatic adjustment of current time at regular intervals and within a maximum tolerance of one minute, or an adjustment performed during calibration; |
|
(uu) |
‘tyre size’ means: the designation of the dimensions of the tyres (external driving wheels) in accordance with Council Directive 92/23/EEC (6) as last amended; |
|
(vv) |
‘vehicle identification’ means: numbers identifying the vehicle: vehicle registration number (VRN) with indication of the registering Member State and vehicle identification number (VIN) (7); |
|
(ww) |
for computing sake in the recording equipment ‘week’ means: the period between 00:00 hours UTC on Monday and 24:00 UTC on Sunday; |
|
(xx) |
‘workshop card’ means: a tachograph card issued by the authorities of a Member State to designated staff of a tachograph manufacturer, a fitter, a vehicle manufacturer or a workshop, approved by that Member State, which identifies the cardholder and allows for the testing, calibration and activation of tachographs, and/or downloading from them; |
|
(yy) |
‘adaptor’ means: a device, providing a signal permanently representative of vehicle speed and/or distance travelled, other than the one used for the independent movement detection, and which is:
use of such an adaptor in those vehicles described above shall allow for the installation and correct use of a vehicle unit compliant with all the requirements of this Annex, for those vehicles, the smart tachograph includes cables, an adaptor, and a vehicle unit; |
|
(zz) |
‘data integrity’ means: the accuracy and consistency of stored data, indicated by an absence of any alteration in data between two updates of a data record. Integrity implies that the data is an exact copy of the original version, e.g. that it has not been corrupted in the process of being written to, and read back from, a tachograph card or a dedicated equipment or during transmission via any communications channel; |
|
(aaa) |
‘data privacy’ means: the overall technical measures taken to ensure the proper implementation of the principles laid down in Directive 95/46/EC of the European Parliament and of the Council (9) as well as of those laid down in Directive 2002/58/EC of the European Parliament and of the Council (10); |
|
(bbb) |
‘smart tachograph’ system means: the recording equipment, tachograph cards and the set of all directly or indirectly interacting equipment during their construction, installation, use, testing and control, such as cards, remote communication reader and any other equipment for data downloading, data analysis, calibration, generating, managing or introducing security elements, etc.; |
|
(ccc) |
‘introduction date’: 36 months after the entry into force of the detailed provisions referred to in Article 11 of Regulation (EU) No 165/2014 of the European Parliament and of the Council (11) This is the date after which vehicles registered for the first time:
|
|
(ddd) |
‘protection profile’ means: a document used as part of certification process according Common Criteria, providing implementation independent specification of information assurance security requirements; |
|
(eee) |
‘GNSS accuracy’: in the context of recording the position from a Global Navigation Satellite System (GNSS) with tachographs, means the value of the horizontal dilution of precision (HDOP) calculated as the minimum of the HDOP values collected on the available GNSS systems. |
2. GENERAL CHARACTERISTICS AND FUNCTIONS OF THE RECORDING EQUIPMENT
2.1 General characteristics
The purpose of the recording equipment is to record, store, display, print, and output data related to driver activities.
Any vehicle fitted with the recording equipment complying with the provisions of this Annex, must include a speed display and an odometer. These functions may be included within the recording equipment.
|
(1) |
The recording equipment includes cables, a motion sensor, and a vehicle unit. |
|
(2) |
The interface between motion sensors and vehicle units shall comply with the requirements specified in Appendix 11. |
|
(3) |
The vehicle unit shall be connected to global navigation satellite system(s), as specified in Appendix 12. |
|
(4) |
The vehicle unit shall communicate with remote early detection communication readers, as specified in Appendix 14. |
|
(5) |
The vehicle unit may include an ITS interface, which is specified in Appendix 13 The recording equipment may be connected to other facilities through additional interfaces and/or through the optional ITS interface. |
|
(6) |
Any inclusion in or connection to the recording equipment of any function, device, or devices, approved or otherwise, shall not interfere with, or be capable of interfering with, the proper and secure operation of the recording equipment and the provisions of this Regulation. Recording equipment users identify themselves to the equipment via tachograph cards. |
|
(7) |
The recording equipment provides selective access rights to data and functions according to user's type and/or identity. |
The recording equipment records and stores data in its data memory, in the remote communication facility and in tachograph cards.
This is done in accordance with Directive 95/46/EC of 24 October 1995 on the protection of individuals with regard to the processing of personal data and on the free movement of such data (12), with Directive 2002/58/EC of 12 July 2002 concerning the processing of personal data and the protection of privacy in the electronic communications sector (13) and in compliance with Article 7 of Regulation (EU) No. 165/2014.
2.2 Functions
|
(8) |
The recording equipment shall ensure the following functions:
|
2.3 Modes of operation
|
(9) |
The recording equipment shall possess four modes of operation:
|
|
(10) |
The recording equipment shall switch to the following mode of operation according to the valid tachograph cards inserted into the card interface devices. In order to determine the mode of operation, the tachograph card generation is irrelevant, provided the inserted card is valid. A first generation workshop card shall always be considered as non-valid when it is inserted in a second generation VU.
|
||||||||||||||||||||||||||||||||||||||||||||
|
(11) |
The recording equipment shall ignore non-valid cards inserted, except displaying, printing or downloading data held on an expired card which shall be possible. |
|
(12) |
All functions listed in 2.2. shall work in any mode of operation with the following exceptions:
|
|
(13) |
The recording equipment can output any data to display, printer or external interfaces with the following exceptions:
|
2.4 Security
The system security aims at protecting the data memory in such a way as to prevent unauthorised access to and manipulation of the data and detecting any such attempts, protecting the integrity and authenticity of data exchanged between the motion sensor and the vehicle unit, protecting the integrity and authenticity of data exchanged between the recording equipment and the tachograph cards, protecting the integrity and authenticity of data exchanged between the recording equipment and the external GNSS facility, protecting the confidentiality, integrity and authenticity of data exchanged through the remote early detection communication for control purposes, and verifying the integrity and authenticity of data downloaded.
|
(14) |
In order to achieve the system security, the following components shall meet the security requirements specified in their Protection Profiles, as required in Appendix 10:
|
3. CONSTRUCTION AND FUNCTIONAL REQUIREMENTS FOR RECORDING EQUIPMENT
3.1 Monitoring cards insertion and withdrawal
|
(15) |
The recording equipment shall monitor the card interface devices to detect card insertions and withdrawals. |
|
(16) |
Upon card insertion the recording equipment shall detect whether the card inserted is a valid tachograph card and in such a case identify the card type and the card generation. If a card with the same card number and a higher renewal index has already been inserted in the recording equipment, the card shall be declared as non-valid. If a card with the same card number and renewal index but with a higher replacement index has already been inserted in the recording equipment, the card shall be declared as non-valid. |
|
(17) |
First generation tachograph cards shall be considered as non-valid by the recording equipment, after the possibility of using first generation tachograph cards has been suppressed by a workshop, in compliance with Appendix 15 (req. MIG003). |
|
(18) |
First generation workshop cards which are inserted in the second generation recording equipment shall be considered as non-valid. |
|
(19) |
The recording equipment shall be so designed that the tachograph cards are locked in position on their proper insertion into the card interface devices. |
|
(20) |
The release of tachograph cards may function only when the vehicle is stopped and after the relevant data have been stored on the cards. The release of the card shall require positive action by the user. |
3.2 Speed, position and distance measurement
|
(21) |
The motion sensor (possibly embedded in the adaptor) is the main source for speed and distance measurement. |
|
(22) |
This function shall continuously measure and be able to provide the odometer value corresponding to the total distance travelled by the vehicle using the pulses provided by the motion sensor. |
|
(23) |
This function shall continuously measure and be able to provide the speed of the vehicle using the pulses provided by the motion sensor. |
|
(24) |
The speed measurement function shall also provide the information whether the vehicle is moving or stopped. The vehicle shall be considered as moving as soon as the function detects more than 1 imp/sec for at least 5 seconds from the motion sensor, otherwise the vehicle shall be considered as stopped. |
|
(25) |
Devices displaying speed (speedometer) and total distance travelled (odometer) installed in any vehicle fitted with a recording equipment complying with the provisions of this Regulation, shall comply with the requirements relating to maximum tolerances (see 3.2.1 and 3.2.2) laid down in this Annex. |
|
(26) |
To detect manipulation of motion data, information from the motion sensor shall be corroborated by vehicle motion information derived from the GNSS receiver and optionally by other source(s) independent from the motion sensor. |
|
(27) |
This function shall measure the position of the vehicle in order to allow for the automatic recording of:
|
3.2.1 Measurement of distance travelled
|
(28) |
The distance travelled may be measured either:
|
|
(29) |
The recording equipment shall measure distance from 0 to 9 999 999,9 km. |
|
(30) |
Distance measured shall be within the following tolerances (distances of at least 1 000 m.):
|
|
(31) |
Distance measured shall have a resolution better than or equal to 0,1 km. |
3.2.2 Measurement of speed
|
(32) |
The recording equipment shall measure speed from 0 to 220 km/h. |
|
(33) |
To ensure a maximum tolerance on speed displayed of ± 6 km/h in use, and taking into account:
the recording equipment shall, for speeds between 20 and 180 km/h, and for characteristic coefficients of the vehicle between 4 000 and 25 000 imp/km, measure the speed with a tolerance of ± 1 km/h (at constant speed). Note: The resolution of data storage brings an additional tolerance of ± 0,5 km/h to speed stored by the recording equipment. |
|
(34) |
The speed shall be measured correctly within the normal tolerances within 2 seconds of the end of a speed change when the speed has changed at a rate up to 2 m/s2. |
|
(35) |
Speed measurement shall have a resolution better than or equal to 1 km/h. |
3.2.3 Measurement of position
|
(36) |
The recording equipment shall measure the absolute position of the vehicle using the GNSS receiver. |
|
(37) |
The absolute position is measured in geographical coordinates of latitude and longitude in degrees and minutes with a resolution of 1/10 of a minute. |
3.3 Time measurement
|
(38) |
The time measurement function shall measure permanently and digitally provide UTC date and time. |
|
(39) |
UTC date and time shall be used for dating data inside the recording equipment (recordings, data exchange) and for all printouts specified in Appendix 4 ‘Printouts’. |
|
(40) |
In order to visualise the local time, it shall be possible to change the offset of the time displayed, in half hour steps. No other offsets than negative or positive multiples of half hours shall be allowed; |
|
(41) |
Time drift shall be within ± 2 seconds per day in type approval conditions, in the absence of any time adjustment. |
|
(42) |
Time measured shall have a resolution better than or equal to 1 second. |
|
(43) |
Time measurement shall not be affected by an external power supply cut-off of less than 12 months in type approval conditions. |
3.4 Monitoring driver activities
|
(44) |
This function shall permanently and separately monitor the activities of one driver and one co-driver. |
|
(45) |
Driver activity shall be DRIVING, WORK, AVAILABILITY or BREAK/REST. |
|
(46) |
It shall be possible for the driver and/or the co-driver to manually select WORK, AVAILABILITY or BREAK/REST. |
|
(47) |
When the vehicle is moving, DRIVING shall be selected automatically for the driver and AVAILABILITY shall be selected automatically for the co-driver. |
|
(48) |
When the vehicle stops, WORK shall be selected automatically for the driver. |
|
(49) |
The first change of activity to REST or AVAILABILITY arising within 120 seconds of the automatic change to WORK due to the vehicle stop shall be assumed to have happened at the time of vehicle stop (therefore possibly cancelling the change to WORK). |
|
(50) |
This function shall output activity changes to the recording functions at a resolution of one minute. |
|
(51) |
Given a calendar minute, if DRIVING is registered as the activity of both the immediately preceding and the immediately succeeding minute, the whole minute shall be regarded as DRIVING. |
|
(52) |
Given a calendar minute that is not regarded as DRIVING according to requirement 051, the whole minute shall be regarded to be of the same type of activity as the longest continuous activity within the minute (or the latest of the equally long activities). |
|
(53) |
This function shall also permanently monitor the continuous driving time and the cumulative break time of the driver. |
3.5 Monitoring driving status
|
(54) |
This function shall permanently and automatically monitor the driving status. |
|
(55) |
The driving status CREW shall be selected when two valid driver cards are inserted in the equipment, the driving status SINGLE shall be selected in any other case. |
3.6 Driver's entries
3.6.1 Entry of places where daily work periods begin and/or end
|
(56) |
This function shall allow for the entry of places where, according to the driver and/or the co-driver, his daily work periods begin and/or end. |
|
(57) |
Places are defined as the country and, in addition where applicable, the region, which are entered or confirmed manually. |
|
(58) |
At the time of a driver card withdrawal, the recording equipment shall prompt the (co-)driver to enter a ‘place where the daily work period ends’. |
|
(59) |
The driver shall then enter the current place of the vehicle, which shall be considered as a temporary entry. |
|
(60) |
It shall be possible to input places where daily work periods begin and/or end through commands in the menus. If more than one such input is done within one calendar minute, only the last begin place input and the last end place input done within that time shall be kept recorded. |
3.6.2 Manual entry of driver activities and driver consent for ITS interface
|
(61) |
Upon driver (or workshop) card insertion, and only at this time, the recording equipment shall allow manual entries of activities. Manual entries of activities shall be performed using local time and date values of the time zone (UTC offset) currently set for the vehicle unit. At driver or workshop card insertion the cardholder shall be reminded of:
At the first insertion of a given driver card or workshop card currently unknown to the vehicle unit, the cardholder shall be invited to express his consent for tachograph related personal data output through the optional ITS interface. At any moment, the driver (resp. workshop) consent can be enabled or disabled through commands in the menu, provided the driver (resp. workshop) card is inserted. It shall be possible to input activities with the following restrictions:
It shall be possible to make manual entries, if required, at the first insertion of a previously unused driver (or workshop) card. The procedure for manual entries of activities shall include as many consecutive steps as necessary to set a type, a start time and an end time for each activity. For any part of the time period between last card withdrawal and current card insertion, the cardholder shall have the option not to declare any activity. During the manual entries associated with card insertion and if applicable, the card holder shall have the opportunity to input:
If the card holder doesn't enter any place where the work period begins or ended, during the manual entries associated with card insertion, this shall be considered as a declaration that his work period has not changed since the last card withdrawal. The next entry of a place where a previous daily work period ends shall then overwrite the temporary entry made at the last card withdrawal. If a place is entered, it shall be recorded in the relevant tachograph card. Manual entries shall be interrupted if:
Additional interruptions are allowed, e.g. a timeout after a certain period of user inactivity. If manual entries are interrupted, the recording equipment shall validate any complete place and activity entries (having either unambiguous place and time, or activity type, begin time and end time) already made. If a second driver or workshop card is inserted while manual entries of activities are in progress for a previously inserted card, the manual entries for this previous card shall be allowed to be completed before manual entries start for the second card. The cardholder shall have the option to insert manual entries according to the following minimum procedure:
The procedure shall end when the end time of a manually entered activity equals the card insertion time. The recording equipment may then optionally allow the card holder to modify any activity manually entered, until validation by selection of a specific command. Thereafter, any such modification shall be forbidden. |
3.6.3 Entry of specific conditions
|
(62) |
The recording equipment shall allow the driver to enter, in real time, the following two specific conditions:
A ‘FERRY / TRAIN CROSSING’ may not occur if an ‘OUT OF SCOPE’ condition is opened. An opened ‘OUT OF SCOPE’ condition must be automatically closed, by the recording equipment, if a driver card is inserted or withdrawn. An opened ‘OUT OF SCOPE’ condition shall inhibit the following events and warnings:
The FERRY / TRAIN CROSSING begin flag shall be set before shutting down the engine on the ferry/train. An opened FERRY / TRAIN CROSSING must end when any of following options occurs:
An opened FERRY/TRAIN CROSSING shall end when it is no longer valid based on the rules stated in Regulation (EC) No. 561/2006. |
3.7 Company locks management
|
(63) |
This function shall allow the management of the locks placed by a company to restrict data access in company mode to itself. |
|
(64) |
Company locks consist in a start date/time (lock-in) and an end date/time (lock-out) associated with the identification of the company as denoted by the company card number (at lock-in). |
|
(65) |
Locks may be turned ‘in’ or ‘out’ in real time only. |
|
(66) |
Locking-out shall only be possible for the company whose lock is ‘in’ (as identified by the first 13 digits of the company card number), or, |
|
(67) |
Locking-out shall be automatic if another company locks in. |
|
(68) |
In the case where a company locks in and where the previous lock was for the same company, then it will be assumed that the previous lock has not been turned ‘out’ and is still ‘in’. |
3.8 Monitoring control activities
|
(69) |
This function shall monitor DISPLAYING, PRINTING, VU and card DOWNLOADING, and ROADSIDE CALIBRATION check activities carried while in control mode. |
|
(70) |
This function shall also monitor OVER SPEEDING CONTROL activities while in control mode. An over speeding control is deemed to have happened when, in control mode, the ‘over speeding’ printout has been sent to the printer or to the display, or when ‘events and faults’ data have been downloaded from the VU data memory. |
3.9 Detection of events and/or faults
|
(71) |
This function shall detect the following events and/or faults: |
3.9.1 ‘Insertion of a non-valid card’ event
|
(72) |
This event shall be triggered at the insertion of any non-valid card, at the insertion of a driver card already replaced and/or when an inserted valid card expires. |
3.9.2 ‘Card conflict’ event
|
(73) |
This event shall be triggered when any of the valid cards combination noted X in the following table arises:
|
||||||||||||||||||||||||||||||||||||||||||||
3.9.3 ‘Time overlap’ event
|
(74) |
This event shall be triggered when the date / time of last withdrawal of a driver card, as read from the card, is later than the current date / time of the recording equipment in which the card is inserted. |
3.9.4 ‘Driving without an appropriate card’ event
|
(75) |
This event shall be triggered for any valid tachograph cards combination noted X in the following table, when driver activity changes to DRIVING, or when there is a change of the mode of operation while driver activity is DRIVING:
|
||||||||||||||||||||||||||||||||||||||||||||
3.9.5 ‘Card insertion while driving’ event
|
(76) |
This event shall be triggered when a tachograph card is inserted in any slot, while driver activity is DRIVING. |
3.9.6 ‘Last card session not correctly closed’ event
|
(77) |
This event shall be triggered when at card insertion the recording equipment detects that, despite the provisions laid down in paragraph 3.1., the previous card session has not been correctly closed (the card has been withdrawn before all relevant data have been stored on the card). This event shall be triggered by driver and workshop cards only. |
3.9.7 ‘Over speeding’ event
|
(78) |
This event shall be triggered for each over speeding. |
3.9.8 ‘Power supply interruption’ event
|
(79) |
This event shall be triggered, while not in calibration or control mode, in case of any interruption exceeding 200 milliseconds of the power supply of the motion sensor and/or of the vehicle unit. The interruption threshold shall be defined by the manufacturer. The drop in power supply due to the starting of the engine of the vehicle shall not trigger this event. |
3.9.9 ‘Communication error with the remote communication facility’ event
|
(80) |
This event shall be triggered, while not in calibration mode, when the remote communication facility does not acknowledge the successful reception of remote communication data sent from the vehicle unit for more than three attempts. |
3.9.10 ‘Absence of position information from GNSS receiver’ event
|
(81) |
This event shall be triggered, while not in calibration mode, in case of absence of position information originating from the GNSS receiver (whether internal or external) for more than three hours of accumulated driving time. |
3.9.11 ‘Communication error with the external GNSS facility’ event
|
(82) |
This event shall be triggered, while not in calibration mode, in case of interruption of the communication between the external GNSS facility and the vehicle unit for more than 20 continuous minutes, when the vehicle is moving. |
3.9.12 ‘Motion data error’ event
|
(83) |
This event shall be triggered, while not in calibration mode, in case of interruption of the normal data flow between the motion sensor and the vehicle unit and/or in case of data integrity or data authentication error during data exchange between the motion sensor and the vehicle unit. |
3.9.13 ‘Vehicle motion conflict’ event
|
(84) |
This event shall be triggered, while not in calibration mode, in case motion information calculated from the motion sensor is contradicted by motion information calculated from the internal GNSS receiver or from the external GNSS facility and optionally by other independent sources, as specified in Appendix 12. This event shall not be triggered during a ferry/train crossing, an OUT OF SCOPE condition, or when the position information from the GNSS receiver is not available. |
3.9.14 ‘Security breach attempt’ event
|
(85) |
This event shall be triggered for any other event affecting the security of the motion sensor and/or of the vehicle unit and/or the external GNSS facility as required in Appendix 10, while not in calibration mode. |
3.9.15 ‘Time conflict’ event
|
(86) |
This event shall be triggered, while not in calibration mode, when the VU detects a discrepancy of more than 1 minute between the time of the vehicle unit's time measurement function and the time originating from the GNSS receiver. This event is recorded together with the internal clock value of the vehicle unit and comes together with an automatic time adjustment. After a time conflict event has been triggered, the VU will not generate other time conflict events for the next 12 hours. This event shall not be triggered in cases no valid GNSS signal was detectable by the GNSS receiver within the last 30 days. However, when the position information from the GNSS receiver is available again, the automatic time adjustment shall be done. |
3.9.16 ‘Card’ fault
|
(87) |
This fault shall be triggered when a tachograph card failure occurs during operation. |
3.9.17 ‘Recording equipment’ fault
|
(88) |
This fault shall be triggered for any of these failures, while not in calibration mode:
|
3.10 Built-in and self-tests
|
(89) |
The recording equipment shall self-detect faults through self-tests and built-in-tests, according to the following table:
|
3.11 Reading from data memory
|
(90) |
The recording equipment shall be able to read any data stored in its data memory. |
3.12 Recording and storing in the data memory
For the purpose of this paragraph,
|
— |
‘365 days’ is defined as 365 calendar days of average drivers' activity in a vehicle. The average activity per day in a vehicle is defined as at least 6 drivers or co-drivers, 6 card insertion withdrawal cycles, and 256 activity changes. ‘365 days’ therefore include at least 2 190 (co-)drivers, 2 190 card insertion withdrawal cycles, and 93 440 activity changes, |
|
— |
the average number of positions per day is defined as at least 6 positions where the daily work period begins, 6 positions when the driver's continuous driving time reaches a multiple of three hours, and 6 positions where the daily work period ends, so that ‘365 days’ include at least 6 570 positions, |
|
— |
times are recorded with a resolution of one minute, unless otherwise specified, |
|
— |
odometer values are recorded with a resolution of one kilometre, |
|
— |
speeds are recorded with a resolution of 1 km/h, |
|
— |
positions (latitudes and longitudes) are recorded in degrees and minutes, with a resolution of 1/10 of minute, with the associated GNSS accuracy and acquisition time. |
|
(91) |
Data stored into the data memory shall not be affected by an external power supply cut-off of less than twelve months in type approval conditions. In addition, data stored in the external remote communication facility, as defined in Appendix 14, shall not be affected by power-supply cut-off of less than 28 days. |
|
(92) |
The recording equipment shall be able to record and store implicitly or explicitly in its data memory the following: |
3.12.1 Equipment identification data
3.12.1.1
|
(93) |
The recording equipment shall be able to store in its data memory the following vehicle unit identification data:
|
|
(94) |
Vehicle unit identification data are recorded and stored once and for all by the vehicle unit manufacturer, except the software related data and the approval number which may be changed in case of software upgrade and the ability to use first generation tachograph cards. |
3.12.1.2
|
(95) |
The motion sensor shall be able to store in its memory the following identification data:
|
|
(96) |
Motion sensor identification data are recorded and stored once and for all in the motion sensor, by the motion sensor manufacturer. |
|
(97) |
The vehicle unit shall be able to record and store in its data memory the following data related to the 20 most recent pairing of motion sensors (if several pairings happen within one calendar day, only the first and the last one of the day shall be stored): The following data shall be recorded for each of these pairings:
|
3.12.1.3
|
(98) |
The external GNSS facility shall be able to store in its memory the following identification data:
|
|
(99) |
The identification data are recorded and stored once and for all in the external GNSS facility, by the external GNSS facility manufacturer. |
|
(100) |
The vehicle unit shall be able to record and store in its data memory the following data related to the 20 most recent couplings of external GNSS facilities (if several couplings happen within one calendar day, only the first and the last one of the day shall be stored). The following data shall be recorded for each of these couplings:
|
3.12.2 Keys and certificates
|
(101) |
The recording equipment shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part A and part B. |
3.12.3 Driver or workshop card insertion and withdrawal data
|
(102) |
For each insertion and withdrawal cycle of a driver or workshop card in the equipment, the recording equipment shall record and store in its data memory:
|
|
(103) |
The data memory shall be able to hold these data for at least 365 days. |
|
(104) |
When storage capacity is exhausted, new data shall replace oldest data. |
3.12.4 Driver activity data
|
(105) |
The recording equipment shall record and store in its data memory whenever there is a change of activity for the driver and/or the co-driver, and/or whenever there is a change of driving status, and/or whenever there is an insertion or withdrawal of a driver or workshop card:
INSERTED means that a valid driver or workshop card is inserted in the slot. NOT INSERTED means the opposite i.e. no valid driver or workshop card is inserted in the slot (e.g. a company card is inserted or no card is inserted) Activity data manually entered by a driver are not recorded in the data memory. |
|
(106) |
The data memory shall be able to hold driver activity data for at least 365 days. |
|
(107) |
When storage capacity is exhausted, new data shall replace oldest data. |
3.12.5 Places and positions where daily work periods begin, end, and/or where 3 hours' continuous driving time is reached
|
(108) |
The recording equipment shall record and store in its data memory:
|
|
(109) |
When the position of the vehicle is not available from the GNSS receiver at these times, the recording equipment shall use the latest available position, and the related date and time. |
|
(110) |
Together with each place or position, the recording equipment shall record and store in its data memory:
|
|
(111) |
The data memory shall be able to hold places and positions where daily work periods begin, end and/or where 3 hours continuous driving time is reached for at least 365 days. |
|
(112) |
When storage capacity is exhausted, new data shall replace oldest data. |
3.12.6 Odometer data
|
(113) |
The recording equipment shall record in its data memory the vehicle odometer value and the corresponding date at midnight every calendar day. |
|
(114) |
The data memory shall be able to store midnight odometer values for at least 365 calendar days. |
|
(115) |
When storage capacity is exhausted, new data shall replace oldest data. |
3.12.7 Detailed speed data
|
(116) |
The recording equipment shall record and store in its data memory the instantaneous speed of the vehicle and the corresponding date and time at every second of at least the last 24 hours that the vehicle has been driven. |
3.12.8 Events data
For the purpose of this subparagraph, time shall be recorded with a resolution of 1 second.
|
(117) |
The recording equipment shall record and store in its data memory the following data for each event detected according to the following storage rules:
|
3.12.9 Faults data
For the purpose of this subparagraph, time shall be recorded with a resolution of 1 second.
|
(118) |
The recording equipment shall attempt to record and store in its data memory the following data for each fault detected according to the following storage rules:
|
3.12.10 Calibration data
|
(119) |
The recording equipment shall record and store in its data memory data relevant to:
|
|
(120) |
The following data shall be recorded for each of these calibrations:
|
|
(121) |
In addition, the recording equipment shall record and store in its data memory its ability to use first generation tachograph cards (still activated or not). |
|
(122) |
The motion sensor shall record and store in its memory the following motion sensor installation data:
|
|
(123) |
The external GNSS facility shall record and store in its memory the following external GNSS facility installation data:
|
3.12.11 Time adjustment data
|
(124) |
The recording equipment shall record and store in its data memory data relevant to time adjustments performed in calibration mode outside the frame of a regular calibration (def. f)):
|
|
(125) |
The following data shall be recorded for each of these time adjustments:
|
3.12.12 Control activity data
|
(126) |
The recording equipment shall record and store in its data memory the following data relevant to the 20 most recent control activities:
|
|
(127) |
In case of downloading, the dates of the oldest and of the most recent days downloaded shall also be recorded. |
3.12.13 Company locks data
|
(128) |
The recording equipment shall record and store in its data memory the following data relevant to the 255 most recent company locks:
Data previously locked by a lock removed from memory due to the limit above, shall be treated as not locked. |
3.12.14 Download activity data
|
(129) |
The recording equipment shall record and store in its data memory the following data relevant to the last data memory downloading to external media while in company or in calibration mode:
|
3.12.15 Specific conditions data
|
(130) |
The recording equipment shall record in its data memory the following data relevant to specific conditions:
|
|
(131) |
The data memory shall be able to hold specific conditions data for at least 365 days (with the assumption that on average, 1 condition is opened and closed per day). When storage capacity is exhausted, new data shall replace oldest data. |
3.12.16 Tachograph card data
|
(132) |
The recording equipment shall be able to store the following data related to the different tachograph cards in which had been used in the VU:
|
|
(133) |
The recording equipment shall be able to store at least 88 such records. |
3.13 Reading from tachograph cards
|
(134) |
The recording equipment shall be able to read from first and second generation tachograph cards, where applicable, the necessary data:
This requirement only applies to first generation tachograph cards if their use has not been suppressed by a workshop. |
|
(135) |
In case of a reading error, the recording equipment shall try again, three times maximum, the same read command, and then if still unsuccessful, declare the card faulty and non-valid. |
3.14 Recording and storing on tachograph cards
3.14.1 Recording and storing in first generation tachograph cards
|
(136) |
Provided first generation tachograph cards use has not been suppressed by a workshop, the recording equipment shall record and store data exactly in the same way as a first generation recording equipment would do. |
|
(137) |
The recording equipment shall set the ‘card session data’ in the driver or workshop card right after the card insertion. |
|
(138) |
The recording equipment shall update data stored on valid driver, workshop, company and/or control cards with all necessary data relevant to the period while the card is inserted and relevant to the card holder. Data stored on these cards are specified in Chapter 4. |
|
(139) |
The recording equipment shall update driver activity and places data (as specified in 4.5.3.1.9 and 4.5.3.1.11), stored on valid driver and/or workshop cards, with activity and places data manually entered by the cardholder. |
|
(140) |
All events not defined for the first generation recording equipment, shall not be stored on the driver and workshop cards. |
|
(141) |
Tachograph cards data update shall be such that, when needed and taking into account card actual storage capacity, most recent data replace oldest data. |
|
(142) |
In the case of a writing error, the recording equipment shall try again, three times maximum, the same write command and then if still unsuccessful, declare the card faulty and non-valid. |
|
(143) |
Before releasing a driver card and after all relevant data have been stored on the card, the recording equipment shall reset the ‘card session data’. |
3.14.2 Recording and storing in second generation tachograph cards
|
(144) |
Second generation tachograph cards shall contain 2 different card applications, the first of which shall be exactly the same as the TACHO application of first generation tachograph cards, and the second the ‘TACHO_G2’ application, as specified in Chapter 4 and Appendix 2. |
|
(145) |
The recording equipment shall set the ‘card session data’ in the driver or workshop card right after the card insertion. |
|
(146) |
The recording equipment shall update data stored on the 2 card applications of valid driver, workshop, company and/or control cards with all necessary data relevant to the period while the card is inserted and relevant to the card holder. Data stored on these cards are specified in Chapter 4. |
|
(147) |
The recording equipment shall update driver activity places and positions data (as specified in 4.5.3.1.9, 4.5.3.1.11, 4.5.3.2.9 and 4.5.3.2.11), stored on valid driver and/or workshop cards, with activity and places data manually entered by the cardholder. |
|
(148) |
Tachograph cards data update shall be such that, when needed and taking into account card actual storage capacity, most recent data replace oldest data. |
|
(149) |
In the case of a writing error, the recording equipment shall try again, three times maximum, the same write command and then if still unsuccessful, declare the card faulty and non-valid. |
|
(150) |
Before releasing a driver card and after all relevant data have been stored on the 2 card applications of the card, the recording equipment shall reset the ‘card session data’. |
3.15 Displaying
|
(151) |
The display shall include at least 20 characters. |
|
(152) |
The minimum character size shall be 5 mm high and 3.5 mm wide. |
|
(153) |
The display shall support the characters specified in Appendix 1 Chapter 4 ‘Character sets’. The display may use simplified glyphs (e.g. accented characters may be displayed without accent, or lower case letters may be shown as upper case letters). |
|
(154) |
The display shall be provided with adequate non-dazzling lighting. |
|
(155) |
Indications shall be visible from outside the recording equipment. |
|
(156) |
The recording equipment shall be able to display:
Additional information may be displayed by the recording equipment, provided that it is clearly distinguishable from information required above. |
|
(157) |
The display of the recording equipment shall use the pictograms or pictograms combinations listed in Appendix 3. Additional pictograms or pictograms combinations may also be provided by the display, if clearly distinguishable from the aforementioned pictograms or pictograms combinations. |
|
(158) |
The display shall always be ON when the vehicle is moving. |
|
(159) |
The recording equipment may include a manual or automatic feature to turn the display OFF when the vehicle is not moving. Displaying format is specified in Appendix 5. |
3.15.1 Default display
|
(160) |
When no other information needs to be displayed, the recording equipment shall display, by default, the following:
|
|
(161) |
Display of data related to each driver shall be clear, plain and unambiguous. In the case where the information related to the driver and the co-driver cannot be displayed at the same time, the recording equipment shall display by default the information related to the driver and shall allow the user to display the information related to the co-driver. |
|
(162) |
In the case where the display width does not allow displaying by default the mode of operation, the recording equipment shall briefly display the new mode of operation when it changes. |
|
(163) |
The recording equipment shall briefly display the card holder name at card insertion. |
|
(164) |
When an ‘OUT OF SCOPE’ or FERRY/TRAIN condition is opened, then the default display must show using the relevant pictogram that the particular condition is opened (it is acceptable that the driver's current activity may not be shown at the same time). |
3.15.2 Warning display
|
(165) |
The recording equipment shall display warning information using primarily the pictograms of Appendix 3, completed where needed by additional numerically coded information. A literal description of the warning may also be added in the driver's preferred language. |
3.15.3 Menu access
|
(166) |
The recording equipment shall provide necessary commands through an appropriate menu structure. |
3.15.4 Other displays
|
(167) |
It shall be possible to display selectively on request:
optional:
|
|
(168) |
Printout content display shall be sequential, line by line. If the display width is less than 24 characters the user shall be provided with the complete information through an appropriate mean (several lines, scrolling, …). Printout lines devoted to hand-written information may be omitted for display. |
3.16 Printing
|
(169) |
The recording equipment shall be able to print information from its data memory and/or from tachograph cards in accordance with the seven following printouts:
The detailed format and content of these printouts are specified in Appendix 4. Additional data may be provided at the end of the printouts. Additional printouts may also be provided by the recording equipment, if clearly distinguishable from the seven aforementioned printouts. |
|
(170) |
The ‘driver activities from card daily printout’ and ‘Events and faults from card printout’ shall be available only when a driver card or a workshop card is inserted in the recording equipment. The recording equipment shall update data stored on the relevant card before starting printing. |
|
(171) |
In order to produce the ‘driver activities from card daily printout’ or the ‘events and faults from card printout’, the recording equipment shall:
|
|
(172) |
The printer shall be able to print 24 characters per line. |
|
(173) |
The minimum character size shall be 2.1 mm high and 1.5 mm wide. |
|
(174) |
The printer shall support the characters specified in Appendix 1 Chapter 4 ‘Character sets’. |
|
(175) |
Printers shall be so designed as to produce these printouts with a degree of definition likely to avoid any ambiguity when they are read. |
|
(176) |
Printouts shall retain their dimensions and recordings under normal conditions of humidity (10-90 %) and temperature. |
|
(177) |
The type approved paper used by the recording equipment shall bear the relevant type approval mark and an indication of the type(s) of recording equipment with which it may be used. |
|
(178) |
Printouts shall remain clearly legible and identifiable under normal conditions of storage, in terms of light intensity, humidity and temperature, for at least two years. |
|
(179) |
Printouts shall conform at least to the test specifications defined in Appendix 9. |
|
(180) |
It shall also be possible to add hand-written notes, such as the driver's signature, to these documents. |
|
(181) |
The recording equipment shall manage ‘paper out’ events while printing by, once paper has been re-loaded, restarting printing from printout beginning or by continuing printing and providing an unambiguous reference to previously printed part. |
3.17 Warnings
|
(182) |
The recording equipment shall warn the driver when detecting any event and/or fault. |
|
(183) |
Warning of a power supply interruption event may be delayed until the power supply is reconnected. |
|
(184) |
The recording equipment shall warn the driver 15 minutes before and at the time of exceeding the maximum allowed continuous driving time. |
|
(185) |
Warnings shall be visual. Audible warnings may also be provided in addition to visual warnings. |
|
(186) |
Visual warnings shall be clearly recognisable by the user, shall be situated in the driver's field of vision and shall be clearly legible both by day and by night. |
|
(187) |
Visual warnings may be built into the recording equipment and/or remote from the recording equipment. |
|
(188) |
In the latter case it shall bear a ‘T’ symbol. |
|
(189) |
Warnings shall have a duration of at least 30 seconds, unless acknowledged by the user by hitting one or more specific keys of the recording equipment. This first acknowledgement shall not erase warning cause display referred to in next paragraph. |
|
(190) |
Warning cause shall be displayed on the recording equipment and remain visible until acknowledged by the user using a specific key or command of the recording equipment. |
|
(191) |
Additional warnings may be provided, as long as they do not confuse drivers in relation to previously defined ones. |
3.18 Data downloading to external media
|
(192) |
The recording equipment shall be able to download on request data from its data memory or from a driver card to external storage media via the calibration/downloading connector. The recording equipment shall update data stored on the relevant card before starting downloading. |
|
(193) |
In addition and as an optional feature, the recording equipment may, in any mode of operation, download data through any another means to a company authenticated through this channel. In such a case, company mode data access rights shall apply to this download. |
|
(194) |
Downloading shall not alter or delete any stored data. |
|
(195) |
The calibration/downloading connector electrical interface is specified in Appendix 6. |
|
(196) |
Downloading protocols are specified in Appendix 7. |
3.19 Remote communication for targeted roadside checks
|
(197) |
When the ignition is on, the Vehicle Unit shall store every 60 seconds in the remote communication facility the most recent data necessary for the purpose of targeted roadside checks. Such data shall be encrypted and signed as specified in Appendix 11 and Appendix 14. |
|
(198) |
Data to be checked remotely shall be available to remote communication readers through wireless communication, as specified in Appendix 14. |
|
(199) |
Data necessary for the purpose of targeted roadside checks shall be related to:
|
3.20 Output data to additional external devices
|
(200) |
The recording equipment may also be equipped with standardised interfaces allowing the data recorded or produced by tachograph to be used in operational or calibration mode, by an external facility. In Appendix 13, an optional ITS interface is specified and standardized. Other similar interfaces may co-exist, provided they fully comply with the requirements of Appendix 13 in term of minimum list of data, security and driver consent. The following requirements apply to ITS data made available through that interface:
Other data may also be output in addition to the set of selected existing data, considered as the minimum list, provided they cannot be considered as personal data. The recording equipment shall notify other external facilities about the consent of the driver. When the ignition of the vehicle is ON, these data shall be permanently broadcasted. |
|
(201) |
The serial link interface as specified in Annex 1B to Regulation (EEC) No. 3821/85, as last amended, can continue to equip tachographs for back compatibility. Anyhow, the driver consent is still required in case personal data are transmitted. |
3.21 Calibration
|
(202) |
The calibration function shall allow:
|
|
(203) |
In addition, the calibration function shall allow to supress the use of first generation tachograph cards in the recording equipment, provided the conditions specified in Appendix 15 are met. |
|
(204) |
Pairing the motion sensor to the VU shall consist, at least, in:
|
|
(205) |
Coupling the external GNSS facility to the VU shall consist, at least, in:
The coupling shall be followed by the verification of the GNSS position information. |
|
(206) |
The calibration function shall be able to input necessary data through the calibration/downloading connector in accordance with the calibration protocol defined in Appendix 8. The calibration function may also input necessary data through other means. |
3.22 Roadside calibration checking
|
(207) |
The roadside calibration checking function shall allow reading the motion sensor serial number (possibly embedded in the adaptor) and the external GNSS facility serial number (when applicable), connected to the vehicle unit, at the time of the request. |
|
(208) |
This reading shall at least be possible on the vehicle unit display through commands in the menus. |
|
(209) |
The roadside calibration checking function shall also allow controlling the selection of the I/O mode of the calibration I/O signal line specified in Appendix 6, via the K-line interface. This shall be done through the ECUAdjustmentSession, as specified in Appendix 8, section 7 Control of Test Pulses — Input output control functional unit. |
3.23 Time adjustment
|
(210) |
The time adjustment function shall allow for automatically adjusting the current time. Two time sources are used in the recording equipment for time adjustment: 1) the internal VU clock, 2) the GNSS receiver. |
|
(211) |
The time setting of the VU internal clock shall be automatically re-adjusted at intervals of 12 hours maximum. When this delay has expired and the GNSS signal is not available, the time setting shall be done as soon as the VU can access a valid time provided by GNSS receiver, according to the vehicle ignition conditions. The time reference for the automatic time setting of the VU internal clock shall be derived from the GNSS receiver. A time conflict event shall be triggered if the current time deviates more than one (1) minute from the time information provided by the GNSS receiver. |
|
(212) |
The time adjustment function shall also allow for triggered adjustment of the current time, in calibration mode. |
3.24 Performance characteristics
|
(213) |
The Vehicle Unit shall be fully operational in the temperature range – 20 °C to 70 °C, the external GNSS facility in the temperature range – 20 °C to 70 °C, and the motion sensor in the temperature range – 40 °C to 135 °C. Data memory content shall be preserved at temperatures down to – 40 °C. |
|
(214) |
The tachograph shall be fully operational in the humidity range 10 % to 90 %. |
|
(215) |
The seals used in the smart tachograph shall withstand the same conditions than those applicable to the tachograph components to which they are affixed. |
|
(216) |
The recording equipment shall be protected against over-voltage, inversion of its power supply polarity, and short circuits. |
|
(217) |
Motion sensors shall either:
|
|
(218) |
The recording equipment and the external GNSS facility shall conform to international regulation UN ECE R10 and shall be protected against electrostatic discharges and transients. |
3.25 Materials
|
(219) |
All the constituent parts of the recording equipment shall be made of materials of sufficient stability and mechanical strength and with stable electrical and magnetic characteristics. |
|
(220) |
For normal conditions of use, all the internal parts of the equipment shall be protected against damp and dust. |
|
(221) |
The Vehicle Unit and the external GNSS facility shall meet the protection grade IP 40 and the motion sensor shall meet the protection grade IP 64, as per standard IEC 60529:1989 including A1:1999 and A2:2013. |
|
(222) |
The recording equipment shall conform to applicable technical specifications related to ergonomic design. |
|
(223) |
The recording equipment shall be protected against accidental damage. |
3.26 Markings
|
(224) |
If the recording equipment displays the vehicle odometer value and speed, the following details shall appear on its display:
The recording equipment may also be switched to display the speed in miles per hour, in which case the unit of measurement of speed shall be shown by the abbreviation ‘mph’. The recording equipment may also be switched to display the distance in miles, in which case the unit of measurement of distance shall be shown by the abbreviation ‘mi’. |
|
(225) |
A descriptive plaque shall be affixed to each separate component of the recording equipment and shall show the following details:
|
|
(226) |
When physical space is not sufficient to show all above mentioned details, the descriptive plaque shall show at least: the manufacturer's name or logo, and the equipment's part number. |
4. CONSTRUCTION AND FUNCTIONAL REQUIREMENTS FOR TACHOGRAPH CARDS
4.1 Visible data
The front page shall contain:
|
(227) |
the words ‘Driver card’ or ‘Control card’ or ‘Workshop card’ or ‘Company card’ printed in capital letters in the official language or languages of the Member State issuing the card, according to the type of the card. |
|
(228) |
the name of the Member State issuing the card (optional); |
|
(229) |
the distinguishing sign of the Member State issuing the card, printed in negative in a blue rectangle and encircled by 12 yellow stars. The distinguishing signs shall be as follows:
|
|
(230) |
information specific to the card issued, numbered as follows:
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||
|
(231) |
dates shall be written using a ‘dd/mm/yyyy’ or ‘dd.mm.yyyy’ format (day, month, year). |
The reverse page shall contain:
|
(232) |
an explanation of the numbered items which appear on the front page of the card; |
|
(233) |
with the specific written agreement of the holder, information which is not related to the administration of the card may also be added, such addition will not alter in any way the use of the model as a tachograph card. |
|
(234) |
Tachograph cards shall be printed with the following background predominant colours: — driver card: white, — control card: blue, — workshop card: red, — company card: yellow. |
|
(235) |
Tachograph cards shall bear at least the following features for protection of the card body against counterfeiting and tampering:
|
|
(236) |
After consulting the Commission, Member States may add colours or markings, such as national symbols and security features, without prejudice to the other provisions of this Annex. |
|
(237) |
Temporary cards referred to in Article 26.4 of Regulation (EU) No. 165/2014 shall comply with the provisions of this Annex. |
4.2 Security
The system security aims at protecting integrity and authenticity of data exchanged between the cards and the recording equipment, protecting the integrity and authenticity of data downloaded from the cards, allowing certain write operations onto the cards to recording equipment only, decrypting certain data, ruling out any possibility of falsification of data stored in the cards, preventing tampering and detecting any attempt of that kind.
|
(238) |
In order to achieve the system security, the tachograph cards shall meet the security requirements defined in Appendixes 10 and 11. |
|
(239) |
Tachograph cards shall be readable by other equipment such as personal computers. |
4.3 Standards
|
(240) |
Tachograph cards shall comply with the following standards:
|
4.4 Environmental and electrical specifications
|
(241) |
Tachograph cards shall be capable of operating correctly in all the climatic conditions normally encountered in Community territory and at least in the temperature range – 25 °C to + 70 °C with occasional peaks of up to + 85 °C, ‘occasional’ meaning not more than 4 hours each time and not over 100 times during the life time of the card. |
|
(242) |
Tachograph cards shall be capable of operating correctly in the humidity range 10 % to 90 %. |
|
(243) |
Tachograph cards shall be capable of operating correctly for a five-year period if used within the environmental and electrical specifications. |
|
(244) |
During operation, tachograph cards shall conform to ECE R10, related to electromagnetic compatibility, and shall be protected against electrostatic discharges. |
4.5 Data storage
For the purpose of this paragraph,
|
— |
times are recorded with a resolution of one minute, unless otherwise specified, |
|
— |
odometer values are recorded with a resolution of one kilometre, |
|
— |
speeds are recorded with a resolution of 1 km/h, |
|
— |
positions (latitudes and longitudes) are recorded in degrees and minutes with a resolution of 1/10 of minute. |
The tachograph cards functions, commands and logical structures, fulfilling data storage requirements are specified in Appendix 2.
If not otherwise specified, data storage on tachograph cards shall be organized in such a way, that new data replaces stored oldest data in case the foreseen memory size for the particular records is exhausted.
|
(245) |
This paragraph specifies minimum storage capacity for the various application data files. Tachograph cards shall be able to indicate to the recording equipment the actual storage capacity of these data files. |
|
(246) |
Any additional data that may be stored on tachograph cards, related to other applications possibly borne by the card, shall be stored in accordance with Directive 95/46/EC and with Directive 2002/58/EC and in compliance with Article 7 of Regulation (EU) No. 165/2014. |
|
(247) |
Each Master File (MF) of any tachograph card shall contain up to five Elementary Files (EF) for card management, application and chip identifications, and two Dedicated Files (DF):
The full details of the tachograph cards structure are specified in Appendix 2. |
4.5.1 Elementary files for identification and card management
4.5.2 IC card identification
|
(248) |
Tachograph cards shall be able to store the following smart card identification data:
|
4.5.2.1
|
(249) |
Tachograph cards shall be able to store the following Integrated Circuit (IC) identification data:
|
4.5.2.2
|
(250) |
Tachograph cards shall be able to store the application identification data objects specified in Appendix 2. |
4.5.2.3
|
(251) |
Tachograph cards shall be able to store the following extended length information data object:
|
4.5.2.4
|
(252) |
Tachograph cards shall be able to store the following extended length information data objects:
|
4.5.3 Driver card
4.5.3.1
4.5.3.1.1 Application identification
|
(253) |
The driver card shall be able to store the following application identification data:
|
4.5.3.1.2 Key and certificates
|
(254) |
The driver card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part A. |
4.5.3.1.3 Card identification
|
(255) |
The driver card shall be able to store the following card identification data:
|
4.5.3.1.4 Card holder identification
|
(256) |
The driver card shall be able to store the following card holder identification data:
|
4.5.3.1.5 Card download
|
(257) |
The driver card shall be able to store the following data related to card download:
|
|
(258) |
The driver card shall be able to hold one such record. |
4.5.3.1.6 Driving licence information
|
(259) |
The driver card shall be able to store the following driving licence data:
|
4.5.3.1.7 Events data
For the purpose of this subparagraph, time shall be stored with a resolution of 1 second.
|
(260) |
The driver card shall be able to store data related to the following events detected by the recording equipment while the card was inserted:
|
|
(261) |
The driver card shall be able to store the following data for these events:
Note: For the ‘Time overlap’ event:
Note: For the ‘Last card session not correctly closed’ event:
|
|
(262) |
The driver card shall be able to store data for the six most recent events of each type (i.e. 36 events). |
4.5.3.1.8 Faults data
For the purpose of this subparagraph, time shall be recorded with a resolution of 1 second.
|
(263) |
The driver card shall be able to store data related to the following faults detected by the recording equipment while the card was inserted:
|
|
(264) |
The driver card shall be able to store the following data for these faults:
|
|
(265) |
The driver card shall be able to store data for the twelve most recent faults of each type (i.e. 24 faults). |
4.5.3.1.9 Driver activity data
|
(266) |
The driver card shall be able to store, for each calendar day where the card has been used or for which the driver has entered activities manually, the following data:
|
|
(267) |
The driver card memory shall be able to hold driver activity data for at least 28 days (the average activity of a driver is defined as 93 activity changes per day). |
|
(268) |
The data listed under requirements 261, 264 and 266 shall be stored in a way allowing the retrieval of activities in the order of their occurrence, even in case of a time overlap situation. |
4.5.3.1.10 Vehicles used data
|
(269) |
The driver card shall be able to store, for each calendar day where the card has been used, and for each period of use of a given vehicle that day (a period of use includes all consecutive insertion / withdrawal cycle of the card in the vehicle, as seen from the card point of view), the following data:
|
|
(270) |
The driver card shall be able to store at least 84 such records. |
4.5.3.1.11 Places where daily work periods start and/or end
|
(271) |
The driver card shall be able to store the following data related to places where daily work periods begin and/or end, entered by the driver:
|
|
(272) |
The driver card memory shall be able to hold at least 42 pairs of such records. |
4.5.3.1.12 Card session data
|
(273) |
The driver card shall be able to store data related to the vehicle which opened its current session:
|
4.5.3.1.13 Control activity data
|
(274) |
The driver card shall be able to store the following data related to control activities:
Note: card downloading will only be recorded if performed through a recording equipment. |
|
(275) |
The driver card shall be able to hold one such record. |
4.5.3.1.14 Specific conditions data
|
(276) |
The driver card shall be able to store the following data related to specific conditions entered while the card was inserted (whatever the slot):
|
|
(277) |
The driver card shall be able to store at least 56 such records. |
4.5.3.2
4.5.3.2.1 Application identification
|
(278) |
The driver card shall be able to store the following application identification data:
|
4.5.3.2.2 Keys and certificates
|
(279) |
The driver card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part B. |
4.5.3.2.3 Card identification
|
(280) |
The driver card shall be able to store the following card identification data:
|
4.5.3.2.4 Card holder identification
|
(281) |
The driver card shall be able to store the following card holder identification data:
|
4.5.3.2.5 Card download
|
(282) |
The driver card shall be able to store the following data related to card download:
|
|
(283) |
The driver card shall be able to hold one such record. |
4.5.3.2.6 Driving licence information
|
(284) |
The driver card shall be able to store the following driving licence data:
|
4.5.3.2.7 Events data
For the purpose of this subparagraph, time shall be stored with a resolution of 1 second.
|
(285) |
The driver card shall be able to store data related to the following events detected by the recording equipment while the card was inserted:
|
|
(286) |
The driver card shall be able to store the following data for these events:
Note: For the ‘Time overlap’ event:
Note: For the ‘Last card session not correctly closed’ event:
|
|
(287) |
The driver card shall be able to store data for the six most recent events of each type (i.e. 66 events). |
4.5.3.2.8 Faults data
For the purpose of this subparagraph, time shall be recorded with a resolution of 1 second.
|
(288) |
The driver card shall be able to store data related to the following faults detected by the recording equipment while the card was inserted:
|
|
(289) |
The driver card shall be able to store the following data for these faults:
|
|
(290) |
The driver card shall be able to store data for the twelve most recent faults of each type (i.e. 24 faults). |
4.5.3.2.9 Driver activity data
|
(291) |
The driver card shall be able to store, for each calendar day where the card has been used or for which the driver has entered activities manually, the following data:
|
|
(292) |
The driver card memory shall be able to hold driver activity data for at least 28 days (the average activity of a driver is defined as 93 activity changes per day). |
|
(293) |
The data listed under requirements 286, 289 and 291 shall be stored in a way allowing the retrieval of activities in the order of their occurrence, even in case of a time overlap situation. |
4.5.3.2.10 Vehicles used data
|
(294) |
The driver card shall be able to store, for each calendar day where the card has been used, and for each period of use of a given vehicle that day (a period of use includes all consecutive insertion / withdrawal cycle of the card in the vehicle, as seen from the card point of view), the following data:
|
|
(295) |
The driver card shall be able to store at least 84 such records. |
4.5.3.2.11 Places and positions where daily work periods start and/or end
|
(296) |
The driver card shall be able to store the following data related to places where daily work periods begin and/or end, entered by the driver:
|
|
(297) |
The driver card memory shall be able to hold at least 84 pairs of such records. |
4.5.3.2.12 Card session data
|
(298) |
The driver card shall be able to store data related to the vehicle which opened its current session:
|
4.5.3.2.13 Control activity data
|
(299) |
The driver card shall be able to store the following data related to control activities:
Note: security requirements imply that card downloading will only be recorded if performed through a recording equipment. |
|
(300) |
The driver card shall be able to hold one such record. |
4.5.3.2.14 Specific conditions data
|
(301) |
The driver card shall be able to store the following data related to specific conditions entered while the card was inserted (whatever the slot):
|
|
(302) |
The driver card shall be able to store at least 56 such records. |
4.5.3.2.15 Vehicle units used data
|
(303) |
The driver card shall be able to store the following data related to the different vehicle units in which the card was used:
|
|
(304) |
The driver card shall be able to store at least 84 such records. |
4.5.3.2.16 Three hours' continuous driving places data
|
(305) |
The driver card shall be able to store the following data related to the position of the vehicle where the continuous driving time of the driver reaches a multiple of three hours:
|
|
(306) |
The driver card shall be able to store at least 252 such records. |
4.5.4 Workshop card
4.5.4.1
4.5.4.1.1 Application identification
|
(307) |
The workshop card shall be able to store the following application identification data:
|
4.5.4.1.2 Keys and certificates
|
(308) |
The workshop card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part A. |
|
(309) |
The workshop card shall be able to store a Personal Identification Number (PIN code). |
4.5.4.1.3 Card identification
|
(310) |
The workshop card shall be able to store the following card identification data:
|
4.5.4.1.4 Card holder identification
|
(311) |
The workshop card shall be able to store the following card holder identification data:
|
4.5.4.1.5 Card download
|
(312) |
The workshop card shall be able to store a card download data record in the same manner as a driver card. |
4.5.4.1.6 Calibration and time adjustment data
|
(313) |
The workshop card shall be able to hold records of calibrations and/or time adjustments performed while the card is inserted in a recording equipment. |
|
(314) |
Each calibration record shall be able to hold the following data:
|
|
(315) |
The workshop card shall be able to store at least 88 such records. |
|
(316) |
The workshop card shall hold a counter indicating the total number of calibrations performed with the card. |
|
(317) |
The workshop card shall hold a counter indicating the number of calibrations performed since its last download. |
4.5.4.1.7 Events and faults data
|
(318) |
The workshop card shall be able to store events and faults data records in the same manner as a driver card. |
|
(319) |
The workshop card shall be able to store data for the three most recent events of each type (i.e. 18 events) and the six most recent faults of each type (i.e. 12 faults). |
4.5.4.1.8 Driver activity data
|
(320) |
The workshop card shall be able to store driver activity data in the same manner as a driver card. |
|
(321) |
The workshop card shall be able to hold driver activity data for at least 1 day of average driver activity. |
4.5.4.1.9 Vehicles used data
|
(322) |
The workshop card shall be able to store vehicles used data records in the same manner as a driver card. |
|
(323) |
The workshop card shall be able to store at least 4 such records. |
4.5.4.1.10 Daily work periods start and/or end data
|
(324) |
The workshop card shall be able to store daily works period start and/or end data records in the same manner as a driver card. |
|
(325) |
The workshop card shall be able to hold at least 3 pairs of such records. |
4.5.4.1.11 Card session data
|
(326) |
The workshop card shall be able to store a card session data record in the same manner as a driver card. |
4.5.4.1.12 Control activity data
|
(327) |
The workshop card shall be able to store a control activity data record in the same manner as a driver card. |
4.5.4.1.13 Specific conditions data
|
(328) |
The workshop card shall be able to store data relevant to specific conditions in the same manner as the driver card. |
|
(329) |
The workshop card shall be able to store at least 2 such records. |
4.5.4.2
4.5.4.2.1 Application identification
|
(330) |
The workshop card shall be able to store the following application identification data:
|
4.5.4.2.2 Keys and certificates
|
(331) |
The workshop card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part B. |
|
(332) |
The workshop card shall be able to store a Personal Identification Number (PIN code). |
4.5.4.2.3 Card identification
|
(333) |
The workshop card shall be able to store the following card identification data:
|
4.5.4.2.4 Card holder identification
|
(334) |
The workshop card shall be able to store the following card holder identification data:
|
4.5.4.2.5 Card download
|
(335) |
The workshop card shall be able to store a card download data record in the same manner as a driver card. |
4.5.4.2.6 Calibration and time adjustment data
|
(336) |
The workshop card shall be able to hold records of calibrations and/or time adjustments performed while the card is inserted in a recording equipment. |
|
(337) |
Each calibration record shall be able to hold the following data:
|
|
(338) |
The workshop card shall be able to store at least 88 such records. |
|
(339) |
The workshop card shall hold a counter indicating the total number of calibrations performed with the card. |
|
(340) |
The workshop card shall hold a counter indicating the number of calibrations performed since its last download. |
4.5.4.2.7 Events and faults data
|
(341) |
The workshop card shall be able to store events and faults data records in the same manner as a driver card. |
|
(342) |
The workshop card shall be able to store data for the three most recent events of each type (i.e. 33 events) and the six most recent faults of each type (i.e. 12 faults). |
4.5.4.2.8 Driver activity data
|
(343) |
The workshop card shall be able to store driver activity data in the same manner as a driver card. |
|
(344) |
The workshop card shall be able to hold driver activity data for at least 1 day of average driver activity. |
4.5.4.2.9 Vehicles used data
|
(345) |
The workshop card shall be able to store vehicles used data records in the same manner as a driver card. |
|
(346) |
The workshop card shall be able to store at least 4 such records. |
4.5.4.2.10 Daily work periods start and/or end data
|
(347) |
The workshop card shall be able to store daily works period start and/or end data records in the same manner as a driver card. |
|
(348) |
The workshop card shall be able to hold at least 3 pairs of such records. |
4.5.4.2.11 Card session data
|
(349) |
The workshop card shall be able to store a card session data record in the same manner as a driver card. |
4.5.4.2.12 Control activity data
|
(350) |
The workshop card shall be able to store a control activity data record in the same manner as a driver card. |
4.5.4.2.13 Vehicle units used data
|
(351) |
The workshop card shall be able to store the following data related to the different vehicle units in which the card was used:
|
|
(352) |
The workshop card shall be able to store at least 4 such records. |
4.5.4.2.14 Three hours' continuous driving places data
|
(353) |
The workshop card shall be able to store the following data related to the position of the vehicle where the continuous driving time of the driver reaches a multiple of three hours:
|
|
(354) |
The workshop card shall be able to store at least 18 such records. |
4.5.4.2.15 Specific conditions data
|
(355) |
The workshop card shall be able to store data relevant to specific conditions in the same manner as the driver card. |
|
(356) |
The workshop card shall be able to store at least 2 such records. |
4.5.5 Control card
4.5.5.1
4.5.5.1.1 Application identification
|
(357) |
The control card shall be able to store the following application identification data:
|
4.5.5.1.2 Keys and certificates
|
(358) |
The control card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part A. |
4.5.5.1.3 Card identification
|
(359) |
The control card shall be able to store the following card identification data:
|
4.5.5.1.4 Card holder identification
|
(360) |
The control card shall be able to store the following card holder identification data:
|
4.5.5.1.5 Control activity data
|
(361) |
The control card shall be able to store the following control activity data:
|
|
(362) |
The control card shall be able to hold at least 230 such records. |
4.5.5.2
4.5.5.2.1 Application identification
|
(363) |
The control card shall be able to store the following application identification data:
|
4.5.5.2.2 Keys and certificates
|
(364) |
The control card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part B. |
4.5.5.2.3 Card identification
|
(365) |
The control card shall be able to store the following card identification data:
|
4.5.5.2.4 Card holder identification
|
(366) |
The control card shall be able to store the following card holder identification data:
|
4.5.5.2.5 Control activity data
|
(367) |
The control card shall be able to store the following control activity data:
|
|
(368) |
The control card shall be able to hold at least 230 such records. |
4.5.6 Company card
4.5.6.1
4.5.6.1.1 Application identification
|
(369) |
The company card shall be able to store the following application identification data:
|
4.5.6.1.2 Keys and Certificates
|
(370) |
The company card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part A. |
4.5.6.1.3 Card identification
|
(371) |
The company card shall be able to store the following card identification data:
|
4.5.6.1.4 Card holder identification
|
(372) |
The company card shall be able to store the following card holder identification data:
|
4.5.6.1.5 Company activity data
|
(373) |
The company card shall be able to store the following company activity data:
|
|
(374) |
The company card shall be able to hold at least 230 such records. |
4.5.6.2
4.5.6.2.1 Application identification
|
(375) |
The company card shall be able to store the following application identification data:
|
4.5.6.2.2 Keys and certificates
|
(376) |
The company card shall be able to store a number of cryptographic keys and certificates, as specified in Appendix 11 part B. |
4.5.6.2.3 Card identification
|
(377) |
The company card shall be able to store the following card identification data:
|
4.5.6.2.4 Card holder identification
|
(378) |
The company card shall be able to store the following card holder identification data:
|
4.5.6.2.5 Company activity data
|
(379) |
The company card shall be able to store the following company activity data:
|
|
(380) |
The company card shall be able to hold at least 230 such records. |
5. INSTALLATION OF RECORDING EQUIPMENT
5.1 Installation
|
(381) |
New recording equipment shall be delivered non-activated to fitters or vehicle manufacturers, with all calibration parameters, as listed in Chapter 3.21, set to appropriate and valid default values. Where no particular value is appropriate, literal parameters shall be set to strings of ‘?’ and numeric parameters shall be set to ‘0’. Delivery of security relevant parts of the recording equipment can be restricted if required during security certification. |
|
(382) |
Before its activation, the recording equipment shall give access to the calibration function even if not in calibration mode. |
|
(383) |
Before its activation, the recording equipment shall neither record nor store data referred by points 3.12.3, 3.12.9 and 3.12.12 to 3.12.15 inclusive. |
|
(384) |
During installation, vehicle manufacturers shall pre-set all known parameters. |
|
(385) |
Vehicle manufacturers or fitters shall activate the installed recording equipment at the latest before the vehicle is used in scope of Regulation (EC) No 561/2006. |
|
(386) |
The activation of the recording equipment shall be triggered automatically by the first insertion of a valid workshop card in either of its card interface devices. |
|
(387) |
Specific pairing operations required between the motion sensor and the vehicle unit, if any, shall take place automatically before or during activation. |
|
(388) |
In a similar way, specific coupling operations between the external GNSS facility and the vehicle unit, if any, shall take place automatically before or during activation. |
|
(389) |
After its activation, the recording equipment shall fully enforce functions and data access rights. |
|
(390) |
After its activation, the recording equipment shall communicate to the remote communication facility the secured data necessary for the purpose of targeted roadside checks. |
|
(391) |
The recording and storing functions of the recording equipment shall be fully operational after its activation. |
|
(392) |
Installation shall be followed by a calibration. The first calibration may not necessarily include entry of the vehicle registration number (VRN), when it is not known by the approved workshop having to undertake this calibration. In these circumstances, it shall be possible, for the vehicle owner, and at this time only, to enter the VRN using his Company Card prior to using the vehicle in scope of Regulation (EC) No 561/2006 (e.g by using commands through an appropriate menu structure of the vehicle unit's man-machine interface.) (14). Any update or confirmation of this entry shall only be possible using a Workshop Card. |
|
(393) |
The installation of an external GNSS facility requires the coupling with the vehicle unit and the subsequent verification of the GNSS position information. |
|
(394) |
The recording equipment must be positioned in the vehicle in such a way as to allow the driver to access the necessary functions from his seat. |
5.2 Installation plaque
|
(395) |
After the recording equipment has been checked on installation, an installation plaque, engraved or printed in a permanent way, which is clearly visible and easily accessible shall be affixed onto the recording equipment. In cases where this is not possible, the plaque shall be affixed to the vehicle's ‘B’ pillar so that it is clearly visible. For vehicles that do not have a ‘B’ pillar, the installation plaque should be affixed to the doorframe on the driver's side of the vehicle and be clearly visible in all cases. After every inspection by an approved fitter or workshop, a new plaque shall be affixed in place of the previous one. |
|
(396) |
The plaque shall bear at least the following details:
|
|
(397) |
For M1 and N1 vehicles only, and which are fitted with an adaptor in conformity with Commission Regulation (EC) No 68/2009 (15) as last amended and where it is not possible to include all the information necessary, as described in Requirement 396, a second, additional, plaque may be used. In such cases, this additional plaque shall contain at least the last four indents described in Requirement 396. This second, additional plaque, if used, shall be affixed next to or beside the first primary plaque described in Requirement 396, and shall have the same protection level. Furthermore the secondary plaque shall also bear the name, address or trade name of the approved fitter or workshop that carried out the installation, and the date of installation. |
5.3 Sealing
|
(398) |
The following parts shall be sealed:
|
|
(399) |
The seals mentioned above may be removed:
|
|
(400) |
On each occasion that these seals are broken a written statement giving the reasons for such action shall be prepared and made available to the competent authority. |
|
(401) |
Seals shall hold an identification number, allocated by its manufacturer. This number shall be unique and distinct from any other seal number allocated by any other seals manufacturer. This unique identification number is defined as: MMNNNNNN by non-removable marking, with MM as unique manufacturer identification (database registration to be managed by EC) and NNNNNN seal alpha-numeric number, unique in the manufacturer domain. |
|
(402) |
The seals shall have a free space where approved fitters, workshops or vehicle manufacturers can add a special mark according the Article 22(3) of Regulation (EU) No 165/2014. This mark shall not cover the seal identification number. |
|
(403) |
Seals manufacturers shall be registered in a dedicated database and shall make their identification seals numbers public through a procedure to be established by the European Commission. |
|
(404) |
Approved workshops and vehicle manufacturers shall, in the frame of Regulation (EU) No 165/2014, only use seals from those of the seals manufacturers listed in the data base mentioned above. |
|
(405) |
Seal manufacturers and their distributors shall maintain full traceability records of the seals sold to be used in the frame of Regulation (EU) No 165/2014 and shall be prepared to produce them to competent national authorities whenever need be. |
|
(406) |
Seals unique identification numbers shall be visible on the installation plaque. |
6. CHECKS, INSPECTIONS AND REPAIRS
Requirements on the circumstances in which seals may be removed, as referred to in Article 22(5) of Regulation (EU) No 165/2014, are defined in Chapter 5.3 of this annex.
6.1 Approval of fitters, workshops and vehicle manufacturers
The Member States approve, regularly control and certify the bodies to carry out:
|
— |
installations, |
|
— |
checks, |
|
— |
inspections, |
|
— |
repairs. |
Workshop cards shall be issued only to fitters and/or workshops approved for the activation and/or the calibration of recording equipment in conformity with this annex and, unless duly justified:
|
— |
who are not eligible for a company card; |
|
— |
and whose other professional activities do not present a potential compromise of the overall security of the system as required in Appendix 10. |
6.2 Check of new or repaired instruments
|
(407) |
Every individual device, whether new or repaired, shall be checked in respect of its proper operation and the accuracy of its reading and recordings, within the limits laid down in Chapter 3.2.1, 3.2.2, 3.2.3 and 3.3 by means of sealing in accordance with Chapter 5.3 and calibration. |
6.3 Installation inspection
|
(408) |
When being fitted to a vehicle, the whole installation (including the recording equipment) shall comply with the provisions relating to maximum tolerances laid down in Chapter 3.2.1, 3.2.2, 3.2.3 and 3.3. |
6.4 Periodic inspections
|
(409) |
Periodic inspections of the equipment fitted to the vehicles shall take place after any repair of the equipment, or after any alteration of the characteristic coefficient of the vehicle or of the effective circumference of the tyres, or after equipment UTC time is wrong by more than 20 minutes, or when the VRN has changed, and at least once within two years (24 months) of the last inspection. |
|
(410) |
These inspections shall include the following checks:
|
|
(411) |
If one of the events listed in Chapter 3.9 (Detection of Events and/or Faults) is found to have occurred since the last inspection and is considered by tachograph manufacturers and/or national authorities as potentially putting the security of the equipment at risk, the workshop shall:
|
|
(412) |
Workshops shall keep traces in their inspection reports of any findings concerning broken seals or manipulations devices. These reports shall be kept by workshops for at least 2 years and made available to the Competent Authority whenever requested to do so. |
|
(413) |
These inspections shall include a calibration and a preventive replacement of the seals whose fitting is under the responsibility of workshops. |
6.5 Measurement of errors
|
(414) |
The measurement of errors on installation and during use shall be carried out under the following conditions, which are to be regarded as constituting standard test conditions:
|
6.6 Repairs
|
(415) |
Workshops shall be able to download data from the recording equipment to give the data back to the appropriate transport company. |
|
(416) |
Approved workshops shall issue to transport companies a certificate of data un-downloadability where the malfunction of the recording equipment prevents previously recorded data to be downloaded, even after repair by this workshop. The workshops will keep a copy of each issued certificate for at least two years. |
7. CARD ISSUING
The card issuing processes set-up by the Member States shall conform to the following:
|
(417) |
The card number of the first issue of a tachograph card to an applicant shall have a consecutive index (if applicable) and a replacement index and a renewal index set to “0”. |
|
(418) |
The card numbers of all non-personal tachograph cards issued to a single control body or a single workshop or a single transport company shall have the same first 13 digits, and shall all have a different consecutive index. |
|
(419) |
A tachograph card issued in replacement of an existing tachograph card shall have the same card number than the replaced one except the replacement index which shall be raised by “1” (in the order 0, …, 9, A, …, Z). |
|
(420) |
A tachograph card issued in replacement of an existing tachograph card shall have the same card expiry date as the replaced one. |
|
(421) |
A tachograph card issued in renewal of an existing tachograph card shall have the same card number as the renewed one except the replacement index which shall be reset to “0” and the renewal index which shall be raised by “1” (in the order 0, …, 9, A, …, Z). |
|
(422) |
The exchange of an existing tachograph card, in order to modify administrative data, shall follow the rules of the renewal if within the same Member State, or the rules of a first issue if performed by another Member State. |
|
(423) |
The ‘card holder surname’ for non-personal workshop or control cards shall be filled with workshop or control body name or with the fitter or control officer's name would Member States so decide. |
|
(424) |
Member States shall exchange data electronically in order to ensure the uniqueness of driver cards that they issue in accordance with Article 31 of Regulation (EU) No 165/2014. |
8. TYPE-APPROVAL OF RECORDING EQUIPMENT AND TACHOGRAPH CARDS
8.1 General points
For the purpose of this chapter, the words ‘recording equipment’ mean ‘recording equipment or its components’. No type approval is required for the cable(s) linking the motion sensor to the VU, the external GNSS facility to the VU or the remote communication facility to the VU. The paper, for use by the recording equipment, shall be considered as a component of the recording equipment.
Any manufacturer may ask for type approval of its component with any type of motion sensor, external GNSS facility and vice versa, provided each component complies with the requirements of this annex. Alternately, manufacturers may also ask for type approval of recording equipment.
|
(425) |
Recording equipment shall be submitted for approval complete with any integrated additional devices. |
|
(426) |
Type approval of recording equipment and of tachograph cards shall include security related tests, functional tests and interoperability tests. Positive results to each of these tests are stated by an appropriate certificate. |
|
(427) |
Member States type approval authorities will not grant a type approval certificate as long as they do not hold:
for the recording equipment or the tachograph card, subject of the request for type approval. |
|
(428) |
Any modification in software or hardware of the equipment or in the nature of materials used for its manufacture shall, before being used, be notified to the authority which granted type-approval for the equipment. This authority shall confirm to the manufacturer the extension of the type approval, or may require an update or a confirmation of the relevant functional, security and/or interoperability certificates. |
|
(429) |
Procedures to upgrade in-situ recording equipment software shall be approved by the authority which granted type approval for the recording equipment. Software upgrade must not alter nor delete any driver activity data stored in the recording equipment. Software may be upgraded only under the responsibility of the equipment manufacturer. |
|
(430) |
Type approval of software modifications aimed to upgrade a previously type approved recording equipment may not be refused if such modifications only apply to functions not specified in this Annex. Software upgrade of a recording equipment may exclude the introduction of new character sets, if not technically feasible. |
8.2 Security certificate
|
(431) |
The security certificate is delivered in accordance with the provisions of Appendix 10 of this Annex. Recording equipment components to be certified are vehicle unit, motion sensor, external GNSS facility and tachograph cards. |
|
(432) |
In the exceptional circumstance that the security certification authorities refuse to certify new equipment on the ground of obsolescence of the security mechanisms, type approval shall continue to be granted only in these specific and exceptional circumstances, and when no alternative solution, compliant with the Regulation, exists. |
|
(433) |
In this circumstance the Member State concerned shall, without delay, inform the European Commission, which shall, within twelve calendar months of the grant of the type approval, launch a procedure to ensure that the level of security is restored to its original levels. |
8.3 Functional certificate
|
(434) |
Each candidate for type approval shall provide the Member State's type approval authority with all the material and documentation that the authority deems necessary. |
|
(435) |
Manufacturers shall provide the relevant samples of type approval candidate products and associated documentation required by laboratories appointed to perform functional tests, and within one month of the request being made. Any costs resulting from this request shall be borne by the requesting entity. Laboratories shall treat all commercially sensitive information in confidence. |
|
(436) |
A functional certificate shall be delivered to the manufacturer only after all functional tests specified in Appendix 9, at least, have been successfully passed. |
|
(437) |
The type approval authority delivers the functional certificate. This certificate shall indicate, in addition to the name of its beneficiary and the identification of the model, a detailed list of the tests performed and the results obtained. |
|
(438) |
The functional certificate of any recording equipment component shall also indicate the type approval numbers of the other type approved compatible recording equipment components tested for its certification. |
|
(439) |
The functional certificate of any recording equipment component shall also indicate the ISO or CEN standard against which the functional interface has been certified. |
8.4 Interoperability certificate
|
(440) |
Interoperability tests are carried out by a single laboratory under the authority and responsibility of the European Commission. |
|
(441) |
The laboratory shall register interoperability test requests introduced by manufacturers in the chronological order of their arrival. |
|
(442) |
Requests will be officially registered only when the laboratory is in possession of:
The date of the registration of the request shall be notified to the manufacturer. |
|
(443) |
No interoperability tests shall be carried out by the laboratory, for recording equipment or tachograph cards that have not been granted a security certificate and a functional certificate, except in the exceptional circumstances described in Requirement 432. |
|
(444) |
Any manufacturer requesting interoperability tests shall commit to leave to the laboratory in charge of these tests the entire set of material and documents which he provided to carry out the tests. |
|
(445) |
The interoperability tests shall be carried out, in accordance with the provisions of Appendix 9 of this Annex, with respectively all the types of recording equipment or tachograph cards:
|
|
(446) |
The interoperability tests shall cover all generations of recording equipment or tachograph cards still in use. |
|
(447) |
The interoperability certificate shall be delivered by the laboratory to the manufacturer only after all required interoperability tests have been successfully passed. |
|
(448) |
If the interoperability tests are not successful with one or more of the recording equipment or tachograph card(s), the interoperability certificate shall not be delivered, until the requesting manufacturer has realised the necessary modifications and has succeeded the interoperability tests. The laboratory shall identify the cause of the problem with the help of the manufacturers concerned by this interoperability fault and shall attempt to help the requesting manufacturer in finding a technical solution. In the case where the manufacturer has modified its product, it is the manufacturer's responsibility to ascertain from the relevant authorities that the security certificate and the functional certificates are still valid. |
|
(449) |
The interoperability certificate is valid for six months. It is revoked at the end of this period if the manufacturer has not received a corresponding type approval certificate. It is forwarded by the manufacturer to the type approval authority of the Member State who has delivered the functional certificate. |
|
(450) |
Any element that could be at the origin of an interoperability fault shall not be used for profit or to lead to a dominant position. |
8.5 Type-approval certificate
|
(451) |
The type approval authority of the Member State may deliver the type approval certificate as soon as it holds the three required certificates. |
|
(452) |
The type approval certificate of any recording equipment component shall also indicate the type approval numbers of the other type approved interoperable recording equipment. |
|
(453) |
The type approval certificate shall be copied by the type approval authority to the laboratory in charge of the interoperability tests at the time of deliverance to the manufacturer. |
|
(454) |
The laboratory competent for interoperability tests shall run a public web site on which will be updated the list of recording equipment or tachograph cards models:
|
8.6 Exceptional procedure: first interoperability certificates for 2nd generation recording equipment and tachograph cards
|
(455) |
Until four months after a first couple of 2nd generation recording equipment and 2nd generation tachograph cards (driver, workshop, control and company cards) have been certified to be interoperable, any interoperability certificate delivered (including the first ones), regarding requests registered during this period, shall be considered provisional. |
|
(456) |
If at the end of this period, all products concerned are mutually interoperable, all corresponding interoperability certificates shall become definitive. |
|
(457) |
If during this period, interoperability faults are found, the laboratory in charge of interoperability tests shall identify the causes of the problems with the help of all manufacturers involved and shall invite them to realize the necessary modifications. |
|
(458) |
If at the end of this period, interoperability problems still remain, the laboratory in charge of interoperability tests, with the collaboration of the manufacturers concerned and with the type approval authorities who delivered the corresponding functional certificates shall find out the causes of the interoperability faults and establish which modifications should be made by each of the manufacturers concerned. The search for technical solutions shall last for a maximum of two months, after which, if no common solution is found, the Commission, after having consulted the laboratory in charge of interoperability tests, shall decide which equipment(s) and cards get a definitive interoperability certificate and state the reasons why. |
|
(459) |
Any request for interoperability tests, registered by the laboratory between the end of the four month period after the first provisional interoperability certificate has been delivered and the date of the decision by the Commission referred to in requirement 455, shall be postponed until the initial interoperability problems have been solved. Those requests are then processed in the chronological order of their registration. |
(1) This way of computing the continuous driving time and the cumulative break time serves in the recording equipment for computing the continuous driving time warning. It does not prejudge the legal interpretation to be made of these times. Alternative ways of computing the continuous driving time and the cumulative break time may be used to replace these definitions if they have been made obsolete by updates in other relevant legislation.
(2) UNKNOWN periods correspond to periods where the driver card was not inserted in the recording equipment and for which no manual entry of driver activities was made.
(3) Regulation (EC) No 561/2006 of the European Parliament and of the Council of 15 March 2006 on the harmonisation of certain social legislation relating to road transport and amending Council Regulations (EEC) No 3821/85 and (EC) No 2135/98 and repealing Council Regulation (EEC) No 3820/85 (OJ L 102, 11.4.2006, p. 1).
(4) Commission Regulation (EU) No 1230/2012 of 12 December 2012 implementing Regulation (EC) No 661/2009 of the European Parliament and of the Council with regard to type-approval requirements for masses and dimensions of motor vehicles and their trailers and amending Directive 2007/46/EC of the European Parliament and of the Council (OJ L 353, 21.12.2012, p. 31) as last amended.
(5) Council Directive 92/6/EEC of 10 February 1992 on the installation and use of speed limitation devices for certain categories of motor vehicles in the Community (OJ L 57, 2.3.1992, p. 27).
(6) Council Directive 92/23/EEC of 31 March 1992 relating to tyres for motor vehicles and their trailers and to their fitting (OJ L 129, 14.5.1992, p. 95).
(7) Council Directive 76/114/EEC of 18 December 1975 on the approximation of the laws of the Member States relating to statutory plates and inscriptions for motor vehicles and their trailers, and their location and method of attachment (OJ L 24, 30.1.1976, p. 1).
(8) Directive 2007/46/EC of the European Parliament and of the Council of 5 September 2007 establishing a framework for the approval of motor vehicles and their trailers, and of systems, components and separate technical units intended for such vehicles (Framework Directive) (OJ L 263, 9.10.2007, p. 1).
(9) Directive 95/46/EC of the European Parliament and of the Council of 24 October 1995 on the protection of individuals with regard to the processing of personal data and on the free movement of such data (OJ L 281, 23.11.1995, p. 31).
(10) Directive 2002/58/EC of the European Parliament and of the Council of 12 July 2002 concerning the processing of personal data and the protection of privacy in the electronic communications sector (Directive on privacy and electronic communications) (OJ L 201, 31.7.2002, p. 37).
(11) Regulation (EU) No 165/2014 of the European Parliament and of the Council of 4 February 2014 on tachographs in road transport, repealing Council Regulation (EEC) No 3821/85 on recording equipment in road transport and amending Regulation (EC) No 561/2006 of the European Parliament and of the Council on the harmonisation of certain social legislation relating to road transport (OJ L 60, 28.2.2014, p. 1).
(12) OJ L 281, 23.11.1995, p.31.
(13) OJ L 201, 31.7.2002, p.37
(*) In these situations the recording equipment shall use only the tachograph card inserted in the driver slot.
(15) Commission Regulation (EC) No 68/2009 of 23 January 2009 adapting for the ninth time to technical progress Council Regulation (EEC) No 3821/85 on recording equipment in road transport (OJ L 21, 24.1.2009, p. 3).
Appendix 1
DATA DICTIONARY
TABLE OF CONTENT
|
1. |
INTRODUCTION | 88 |
|
1.1. |
Approach for definitions of data types | 88 |
|
1.2. |
References | 88 |
|
2. |
DATA TYPE DEFINITIONS | 89 |
|
2.1. |
ActivityChangeInfo | 89 |
|
2.2. |
Address | 90 |
|
2.3. |
AESKey | 91 |
|
2.4. |
AES128Key | 91 |
|
2.5. |
AES192Key | 91 |
|
2.6. |
AES256Key | 92 |
|
2.7. |
BCDString | 92 |
|
2.8. |
CalibrationPurpose | 92 |
|
2.9. |
CardActivityDailyRecord | 93 |
|
2.10. |
CardActivityLengthRange | 93 |
|
2.11. |
CardApprovalNumber | 93 |
|
2.12. |
CardCertificate | 94 |
|
2.13. |
CardChipIdentification | 94 |
|
2.14. |
CardConsecutiveIndex | 94 |
|
2.15. |
CardControlActivityDataRecord | 94 |
|
2.16. |
CardCurrentUse | 95 |
|
2.17. |
CardDriverActivity | 95 |
|
2.18. |
CardDrivingLicenceInformation | 95 |
|
2.19. |
CardEventData | 96 |
|
2.20. |
CardEventRecord | 96 |
|
2.21. |
CardFaultData | 96 |
|
2.22. |
CardFaultRecord | 97 |
|
2.23. |
CardIccIdentification | 97 |
|
2.24. |
CardIdentification | 97 |
|
2.25. |
CardMACertificate | 98 |
|
2.26. |
CardNumber | 98 |
|
2.27. |
CardPlaceDailyWorkPeriod | 99 |
|
2.28. |
CardPrivateKey | 99 |
|
2.29. |
CardPublicKey | 99 |
|
2.30. |
CardRenewalIndex | 99 |
|
2.31. |
CardReplacementIndex | 99 |
|
2.32. |
CardSignCertificate | 100 |
|
2.33. |
CardSlotNumber | 100 |
|
2.34. |
CardSlotsStatus | 100 |
|
2.35. |
CardSlotsStatusRecordArray | 100 |
|
2.36. |
CardStructureVersion | 101 |
|
2.37. |
CardVehicleRecord | 101 |
|
2.38. |
CardVehiclesUsed | 102 |
|
2.39. |
CardVehicleUnitRecord | 102 |
|
2.40. |
CardVehicleUnitsUsed | 102 |
|
2.41. |
Certificate | 103 |
|
2.42. |
CertificateContent | 103 |
|
2.43. |
CertificateHolderAuthorisation | 104 |
|
2.44. |
CertificateRequestID | 104 |
|
2.45. |
CertificationAuthorityKID | 104 |
|
2.46. |
CompanyActivityData | 105 |
|
2.47. |
CompanyActivityType | 106 |
|
2.48. |
CompanyCardApplicationIdentification | 106 |
|
2.49. |
CompanyCardHolderIdentification | 106 |
|
2.50. |
ControlCardApplicationIdentification | 106 |
|
2.51. |
ControlCardControlActivityData | 107 |
|
2.52. |
ControlCardHolderIdentification | 107 |
|
2.53. |
ControlType | 108 |
|
2.54. |
CurrentDateTime | 109 |
|
2.55. |
CurrentDateTimeRecordArray | 109 |
|
2.56. |
DailyPresenceCounter | 109 |
|
2.57. |
Datef | 109 |
|
2.58. |
DateOfDayDownloaded | 110 |
|
2.59. |
DateOfDayDownloadedRecordArray | 110 |
|
2.60. |
Distance | 110 |
|
2.61. |
DriverCardApplicationIdentification | 110 |
|
2.62. |
DriverCardHolderIdentification | 111 |
|
2.63. |
DSRCSecurityData | 112 |
|
2.64. |
EGFCertificate | 112 |
|
2.65. |
EmbedderIcAssemblerId | 112 |
|
2.66. |
EntryTypeDailyWorkPeriod | 113 |
|
2.67. |
EquipmentType | 113 |
|
2.68. |
EuropeanPublicKey | 114 |
|
2.69. |
EventFaultRecordPurpose | 114 |
|
2.70. |
EventFaultType | 114 |
|
2.71. |
ExtendedSealIdentifier | 115 |
|
2.72. |
ExtendedSerialNumber | 116 |
|
2.73. |
FullCardNumber | 116 |
|
2.74. |
FullCardNumberAndGeneration | 117 |
|
2.75. |
Generation | 117 |
|
2.76. |
GeoCoordinates | 117 |
|
2.77. |
GNSSAccuracy | 118 |
|
2.78. |
GNSSContinuousDriving | 118 |
|
2.79. |
GNSSContinuousDrivingRecord | 118 |
|
2.80. |
GNSSPlaceRecord | 118 |
|
2.81. |
HighResOdometer | 119 |
|
2.82. |
HighResTripDistance | 119 |
|
2.83. |
HolderName | 119 |
|
2.84. |
InternalGNSSReceiver | 119 |
|
2.85. |
K-ConstantOfRecordingEquipment | 119 |
|
2.86. |
KeyIdentifier | 120 |
|
2.87. |
KMWCKey | 120 |
|
2.88. |
Language | 120 |
|
2.89. |
LastCardDownload | 120 |
|
2.90. |
LinkCertificate | 120 |
|
2.91. |
L-TyreCircumference | 121 |
|
2.92. |
MAC | 121 |
|
2.93. |
ManualInputFlag | 121 |
|
2.94. |
ManufacturerCode | 121 |
|
2.95. |
ManufacturerSpecificEventFaultData | 121 |
|
2.96. |
MemberStateCertificate | 122 |
|
2.97. |
MemberStateCertificateRecordArray | 122 |
|
2.98. |
MemberStatePublicKey | 122 |
|
2.99. |
Name | 122 |
|
2.100. |
NationAlpha | 123 |
|
2.101. |
NationNumeric | 123 |
|
2.102. |
NoOfCalibrationRecords | 123 |
|
2.103. |
NoOfCalibrationsSinceDownload | 123 |
|
2.104. |
NoOfCardPlaceRecords | 123 |
|
2.105. |
NoOfCardVehicleRecords | 124 |
|
2.106. |
NoOfCardVehicleUnitRecords | 124 |
|
2.107. |
NoOfCompanyActivityRecords | 124 |
|
2.108. |
NoOfControlActivityRecords | 124 |
|
2.109. |
NoOfEventsPerType | 124 |
|
2.110. |
NoOfFaultsPerType | 124 |
|
2.111. |
NoOfGNSSCDRecords | 124 |
|
2.112. |
NoOfSpecificConditionRecords | 125 |
|
2.113. |
OdometerShort | 125 |
|
2.114. |
OdometerValueMidnight | 125 |
|
2.115. |
OdometerValueMidnightRecordArray | 125 |
|
2.116. |
OverspeedNumber | 125 |
|
2.117. |
PlaceRecord | 126 |
|
2.118. |
PreviousVehicleInfo | 126 |
|
2.119. |
PublicKey | 127 |
|
2.120. |
RecordType | 127 |
|
2.121. |
RegionAlpha | 128 |
|
2.122. |
RegionNumeric | 128 |
|
2.123. |
RemoteCommunicationModuleSerialNumber | 129 |
|
2.124. |
RSAKeyModulus | 129 |
|
2.125. |
RSAKeyPrivateExponent | 129 |
|
2.126. |
RSAKeyPublicExponent | 129 |
|
2.127. |
RtmData | 129 |
|
2.128. |
SealDataCard | 129 |
|
2.129. |
SealDataVu | 130 |
|
2.130. |
SealRecord | 130 |
|
2.131. |
SensorApprovalNumber | 130 |
|
2.132. |
SensorExternalGNSSApprovalNumber | 131 |
|
2.133. |
SensorExternalGNSSCoupledRecord | 131 |
|
2.134. |
SensorExternalGNSSIdentification | 131 |
|
2.135. |
SensorExternalGNSSInstallation | 132 |
|
2.136. |
SensorExternalGNSSOSIdentifier | 132 |
|
2.137. |
SensorExternalGNSSSCIdentifier | 132 |
|
2.138. |
SensorGNSSCouplingDate | 133 |
|
2.139. |
SensorGNSSSerialNumber | 133 |
|
2.140. |
SensorIdentification | 133 |
|
2.141. |
SensorInstallation | 133 |
|
2.142. |
SensorInstallationSecData | 134 |
|
2.143. |
SensorOSIdentifier | 134 |
|
2.144. |
SensorPaired | 134 |
|
2.145. |
SensorPairedRecord | 135 |
|
2.146. |
SensorPairingDate | 135 |
|
2.147. |
SensorSCIdentifier | 135 |
|
2.148. |
SensorSerialNumber | 135 |
|
2.149. |
Signature | 135 |
|
2.150. |
SignatureRecordArray | 136 |
|
2.151. |
SimilarEventsNumber | 136 |
|
2.152. |
SpecificConditionRecord | 136 |
|
2.153. |
SpecificConditions | 136 |
|
2.154. |
SpecificConditionType | 137 |
|
2.155. |
Speed | 137 |
|
2.156. |
SpeedAuthorised | 137 |
|
2.157. |
SpeedAverage | 138 |
|
2.158. |
SpeedMax | 138 |
|
2.159. |
TachographPayload | 138 |
|
2.160. |
TachographPayloadEncrypted | 138 |
|
2.161. |
TDesSessionKey | 138 |
|
2.162. |
TimeReal | 139 |
|
2.163. |
TyreSize | 139 |
|
2.164. |
VehicleIdentificationNumber | 139 |
|
2.165. |
VehicleIdentificationNumberRecordArray | 139 |
|
2.166. |
VehicleRegistrationIdentification | 139 |
|
2.167. |
VehicleRegistrationNumber | 140 |
|
2.168. |
VehicleRegistrationNumberRecordArray | 140 |
|
2.169. |
VuAbility | 140 |
|
2.170. |
VuActivityDailyData | 141 |
|
2.171. |
VuActivityDailyRecordArray | 141 |
|
2.172. |
VuApprovalNumber | 141 |
|
2.173. |
VuCalibrationData | 142 |
|
2.174. |
VuCalibrationRecord | 142 |
|
2.175. |
VuCalibrationRecordArray | 143 |
|
2.176. |
VuCardIWData | 144 |
|
2.177. |
VuCardIWRecord | 144 |
|
2.178. |
VuCardIWRecordArray | 145 |
|
2.179. |
VuCardRecord | 145 |
|
2.180. |
VuCardRecordArray | 146 |
|
2.181. |
VuCertificate | 146 |
|
2.182. |
VuCertificateRecordArray | 146 |
|
2.183. |
VuCompanyLocksData | 147 |
|
2.184. |
VuCompanyLocksRecord | 147 |
|
2.185. |
VuCompanyLocksRecordArray | 148 |
|
2.186. |
VuControlActivityData | 148 |
|
2.187. |
VuControlActivityRecord | 148 |
|
2.188. |
VuControlActivityRecordArray | 149 |
|
2.189. |
VuDataBlockCounter | 149 |
|
2.190. |
VuDetailedSpeedBlock | 149 |
|
2.191. |
VuDetailedSpeedBlockRecordArray | 150 |
|
2.192. |
VuDetailedSpeedData | 150 |
|
2.193. |
VuDownloadablePeriod | 150 |
|
2.194. |
VuDownloadablePeriodRecordArray | 151 |
|
2.195. |
VuDownloadActivityData | 151 |
|
2.196. |
VuDownloadActivityDataRecordArray | 151 |
|
2.197. |
VuEventData | 152 |
|
2.198. |
VuEventRecord | 152 |
|
2.199. |
VuEventRecordArray | 153 |
|
2.200. |
VuFaultData | 154 |
|
2.201. |
VuFaultRecord | 154 |
|
2.202. |
VuFaultRecordArray | 155 |
|
2.203. |
VuGNSSCDRecord | 155 |
|
2.204. |
VuGNSSCDRecordArray | 156 |
|
2.205. |
VuIdentification | 156 |
|
2.206. |
VuIdentificationRecordArray | 157 |
|
2.207. |
VuITSConsentRecord | 157 |
|
2.208. |
VuITSConsentRecordArray | 158 |
|
2.209. |
VuManufacturerAddress | 158 |
|
2.210. |
VuManufacturerName | 158 |
|
2.211. |
VuManufacturingDate | 158 |
|
2.212. |
VuOverSpeedingControlData | 159 |
|
2.213. |
VuOverSpeedingControlDataRecordArray | 159 |
|
2.214. |
VuOverSpeedingEventData | 159 |
|
2.215. |
VuOverSpeedingEventRecord | 159 |
|
2.216. |
VuOverSpeedingEventRecordArray | 160 |
|
2.217. |
VuPartNumber | 161 |
|
2.218. |
VuPlaceDailyWorkPeriodData | 161 |
|
2.219. |
VuPlaceDailyWorkPeriodRecord | 161 |
|
2.220. |
VuPlaceDailyWorkPeriodRecordArray | 162 |
|
2.221. |
VuPrivateKey | 162 |
|
2.222. |
VuPublicKey | 162 |
|
2.223. |
VuSerialNumber | 162 |
|
2.224. |
VuSoftInstallationDate | 162 |
|
2.225. |
VuSoftwareIdentification | 163 |
|
2.226. |
VuSoftwareVersion | 163 |
|
2.227. |
VuSpecificConditionData | 163 |
|
2.228. |
VuSpecificConditionRecordArray | 163 |
|
2.229. |
VuTimeAdjustmentData | 164 |
|
2.230. |
VuTimeAdjustmentGNSSRecord | 164 |
|
2.231. |
VuTimeAdjustmentGNSSRecordArray | 164 |
|
2.232. |
VuTimeAdjustmentRecord | 165 |
|
2.233. |
VuTimeAdjustmentRecordArray | 165 |
|
2.234. |
WorkshopCardApplicationIdentification | 166 |
|
2.235. |
WorkshopCardCalibrationData | 166 |
|
2.236. |
WorkshopCardCalibrationRecord | 167 |
|
2.237. |
WorkshopCardHolderIdentification | 168 |
|
2.238. |
WorkshopCardPIN | 168 |
|
2.239. |
W-VehicleCharacteristicConstant | 169 |
|
2.240. |
VuPowerSupplyInterruptionRecord | 169 |
|
2.241. |
VuPowerSupplyInterruptionRecordArray | 169 |
|
2.242. |
VuSensorExternalGNSSCoupledRecordArray | 170 |
|
2.243. |
VuSensorPairedRecordArray | 170 |
|
3. |
VALUE AND SIZE RANGE DEFINITIONS | 171 |
|
4. |
CHARACTER SETS | 171 |
|
5. |
ENCODING | 171 |
|
6. |
OBJECT IDENTIFIERS UND APPLICATION IDENTIFIERS | 171 |
|
6.1. |
Object Identifiers | 171 |
|
6.2. |
Application Identifiers | 172 |
1. INTRODUCTION
This appendix specifies data formats, data elements, and data structures for use within the recording equipment and tachograph cards.
1.1. Approach for definitions of data types
This appendix uses Abstract Syntax Notation One (ASN.1) to define data types. This enables simple and structured data to be defined without implying any specific transfer syntax (encoding rules) which will be application and environment dependent.
ASN.1 type naming conventions are done in accordance with ISO/IEC 8824-1. This implies that:
|
— |
where possible, the meaning of the data type is implied through the names being selected, |
|
— |
where a data type is a composition of other data types, the data type name is still a single sequence of alphabetical characters commencing with a capital letter, however capitals are used within the name to impart the corresponding meaning, |
|
— |
in general, the data types names are related to the name of the data types from which they are constructed, the equipment in which data is stored and the function related to the data. |
If an ASN.1 type is already defined as part of another standard and if it is relevant for usage in the recording equipment, then this ASN.1 type will be defined in this appendix.
To enable several types of encoding rules, some ASN.1 types in this appendix are constrained by value range identifiers. The value range identifiers are defined in paragraph 3 and Appendix 2.
1.2. References
The following references are used in this Appendix:
|
ISO 639 |
Code for the representation of names of languages. First Edition: 1988. |
|
ISO 3166 |
Codes for the representation of names of countries and their subdivisions — Part 1: Country codes, 2013 |
|
ISO 3779 |
Road vehicles — Vehicle identification number (VIN) — Content and structure. 2009 |
|
ISO/IEC 7816-5 |
Identification cards — Integrated circuit cards — Part 5: Registration of application providers. Second edition: 2004. |
|
ISO/IEC 7816-6 |
Identification cards — Integrated circuit cards — Part 6: Interindustry data elements for interchange, 2004 + Technical Corrigendum 1: 2006 |
|
ISO/IEC 8824-1 |
Information technology — Abstract Syntax Notation One (ASN.1): Specification of basic notation. 2008 + Technical Corrigendum 1: 2012 and Technical Corrigendum 2: 2014. |
|
ISO/IEC 8825-2 |
Information technology — ASN.1 encoding rules: Specification of Packed Encoding Rules (PER). 2008. |
|
ISO/IEC 8859-1 |
Information technology — 8 bit single-byte coded graphic character sets — Part 1: Latin alphabet No.1. First edition: 1998. |
|
ISO/IEC 8859-7 |
Information technology — 8 bit single-byte coded graphic character sets — Part 7: Latin/Greek alphabet. 2003. |
|
ISO 16844-3 |
Road vehicles — Tachograph systems — Motion Sensor Interface. 2004 + Technical Corrigendum 1: 2006.. |
|
TR-03110-3 |
BSI / ANSSI Technical Guideline TR-03110-3, Advanced Security Mechanisms for Machine Readable Travel Documents and eIDAS Token — Part 3 Common Specifications, version 2.20, 3. February 2015 |
2. DATA TYPE DEFINITIONS
For any of the following data types, the default value for an ‘unknown’ or a ‘not applicable’ content will consist in filling the data element with ‘FF’ bytes.
All data types are used for Generation 1 and Generation 2 applications unless otherwise specified.
2.1. ActivityChangeInfo
This data type enables to code, within a two bytes word, a slot status at 00:00 and/or a driver status at 00:00 and/or changes of activity and/or changes of driving status and/or changes of card status for a driver or a co-driver. This data type is related to Annex 1C requirements 105, 266, 291, 320, 321, 343, and 344.
![]()
Value assignment — Octet Aligned: ‘scpaattttttttttt’B (16 bits)
For Data Memory recordings (or slot status):
|
‘s’B |
Slot:
|
||||||||
|
‘c’B |
Driving status:
|
||||||||
|
‘p’B |
Driver (or workshop) card status in the relevant slot:
|
||||||||
|
‘aa’B |
Activity:
|
||||||||
|
‘ttttttttttt’B |
Time of the change: Number of minutes since 00h00 on the given day. |
For Driver (or Workshop) card recordings (and driver status):
|
‘s’B |
Slot (not relevant when ‘p’=1 except note below):
|
||||||||
|
‘c’B |
Driving status (case ‘p’=0) or Following activity status (case ‘p’=1):
|
||||||||
|
‘p’B |
Card status:
|
||||||||
|
‘aa’B |
Activity (not relevant when ‘p’=1 and ‘c’=0 except note below):
|
||||||||
|
‘ttttttttttt’B |
Time of the change: Number of minutes since 00h00 on the given day. |
Note for the case ‘card withdrawal’:
When the card is withdrawn:
|
— |
‘s’ is relevant and indicates the slot from which the card is withdrawn, |
|
— |
‘c’ must be set to 0, |
|
— |
‘p’ must be set to 1, |
|
— |
‘aa’ must code the current activity selected at that time, |
As a result of a manual entry, the bits ‘c’ and ‘aa’ of the word (stored in a card) may be overwritten later to reflect the entry.
2.2. Address
An address.

codePage specifies a character set defined in Chapter 4,
address is an address encoded using the specified character set.
2.3. AESKey
Generation 2:
An AES key with a length of 128, 192 or 256 bits.

Value assignment: not further specified.
2.4. AES128Key
Generation 2:
An AES128 key.

length denotes the length of the AES128 key in octets.
aes128Key is an AES key with a length of 128 bits.
Value assignment:
The length shall have the value 16.
2.5. AES192Key
Generation 2:
An AES192 key.

length denotes the length of the AES192 key in octets.
aes192Key is an AES key with a length of 192 bits.
Value assignment:
The length shall have the value 24.
2.6. AES256Key
Generation 2:
An AES256 key.

length denotes the length of the AES256 key in octets.
aes256Key is an AES key with a length of 256 bits.
Value assignment:
The length shall have the value 32.
2.7. BCDString
BCDString is applied for Binary Code Decimal (BCD) representation. This data type is used to represent one decimal digit in one semi octet (4 bits). BCDString is based on the ISO/IEC 8824-1 ‘CharacterStringType’.
![]()
BCDString uses an ‘hstring’ notation. The leftmost hexadecimal digit shall be the most significant semi octet of the first octet. To produce a multiple of octets, zero trailing semi octets shall be inserted, as needed, from the leftmost semi octet position in the first octet.
Permitted digits are: 0, 1, .. 9.
2.8. CalibrationPurpose
Code explaining why a set of calibration parameters was recorded. This data type is related to Annex 1B requirements 097 and 098 and Annex 1C requirements 119.
![]()
Value assignment:
|
|
Generation 1:
|
|
|
Generation 2: In addition to generation 1 the following values are used:
|
2.9. CardActivityDailyRecord
Information, stored in a card, related to the driver activities for a particular calendar day. This data type is related to Annex 1C requirements 266, 291, 320 and 343.

activityPreviousRecordLength is the total length in bytes of the previous daily record. The maximum value is given by the length of the OCTET STRING containing these records (see CardActivityLengthRange Appendix 2 paragraph 4). When this record is the oldest daily record, the value of activityPreviousRecordLength must be set to 0.
activityRecordLength is the total length in bytes of this record. The maximum value is given by the length of the OCTET STRING containing these records.
activityRecordDate is the date of the record.
activityDailyPresenceCounter is the daily presence counter for the card this day.
activityDayDistance is the total distance travelled this day.
activityChangeInfo is the set of ActivityChangeInfo data for the driver this day. It may contain at maximum 1440 values (one activity change per minute). This set always includes the activityChangeInfo coding the driver status at 00:00.
2.10. CardActivityLengthRange
Number of bytes in a driver or a workshop card, available to store driver activity records.
![]()
Value assignment: see Appendix 2.
2.11. CardApprovalNumber
Type approval number of the card.
![]()
Value assignment:
The approval number shall be provided as published on the corresponding European Commission web site, i.e. for example including hyphens if any. The approval number shall be left-aligned.
2.12. CardCertificate
Generation 1:
Certificate of the public key of a card.
![]()
2.13. CardChipIdentification
Information, stored in a card, related to the identification of the card's Integrated Circuit (IC) (Annex 1C requirement 249). The icSerialNumber together with the icManufacturingReferences identifies the card chip uniquely. The icSerialNumber alone does not uniquely identify the card chip.

icSerialNumber is the IC serial number.
icManufacturingReferences is the IC manufacturer specific identifier.
2.14. CardConsecutiveIndex
A card consecutive index (definition h)).
![]()
Value assignment: (see Annex 1C chapter 7)
Order for increase: ‘0, …, 9, A, …, Z, a, …, z’
2.15. CardControlActivityDataRecord
Information, stored in a driver or workshop card, related to the last control the driver has been subject to (Annex 1C requirements 274, 299, 327, and 350).

controlType is the type of the control.
controlTime is the date and time of the control.
controlCardNumber is the FullCardNumber of the control officer having performed the control.
controlVehicleRegistration is the VRN and registering Member State of the vehicle in which the control happened.
controlDownloadPeriodBegin and controlDownloadPeriodEnd is the period downloaded, in case of downloading.
2.16. CardCurrentUse
Information about the actual usage of the card (Annex 1C requirement 273, 298, 326, and 349).

sessionOpenTime is the time when the card is inserted for the current usage. This element is set to zero at card removal.
sessionOpenVehicle is the identification of the currently used vehicle, set at card insertion. This element is set to zero at card removal.
2.17. CardDriverActivity
Information, stored in a driver or a workshop card, related to the activities of the driver (Annex 1C requirements 267, 268, 292, 293, 321 and 344).

activityPointerOldestDayRecord is the specification of the begin of the storage place (number of bytes from the beginning of the string) of the oldest complete day record in the activityDailyRecords string. The maximum value is given by the length of the string.
activityPointerNewestRecord is the specification of the begin of the storage place (number of bytes from the beginning of the string) of the most recent day record in the activityDailyRecords string. The maximum value is given by the length of the string.
activityDailyRecords is the space available to store the driver activity data (data structure: CardActivityDailyRecord) for each calendar day where the card has been used.
Value assignment: this octet string is cyclically filled with records of CardActivityDailyRecord. At the first use storing is started at the first byte of the string. All new records are appended at the end of the previous one. When the string is full, storing continues at the first byte of the string independently of a break being inside a data element. Before placing new activity data in the string (enlarging current activityDailyRecord, or placing a new activityDailyRecord) that replaces older activity data, activityPointerOldestDayRecord must be updated to reflect the new location of the oldest complete day record, and activityPreviousRecordLength of this (new) oldest complete day record must be reset to 0.
2.18. CardDrivingLicenceInformation
Information, stored in a driver card, related to the card holder driver licence data (Annex 1C requirement 259 and 284).

drivingLicenceIssuingAuthority is the authority responsible for issuing the driving licence.
drivingLicenceIssuingNation is the nationality of the authority that issued the driving licence.
drivingLicenceNumber is the number of the driving licence.
2.19. CardEventData
Information, stored in a driver or workshop card, related to the events associated with the card holder (Annex 1C requirements 260, 285, 318 and 341).
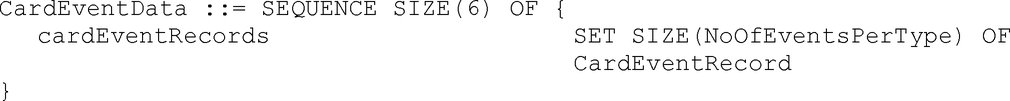
CardEventData is a sequence, ordered by ascending value of EventFaultType, of cardEventRecords (except security breach attempts related records which are gathered in the last set of the sequence).
cardEventRecords is a set of event records of a given event type (or category for security breach attempts events).
2.20. CardEventRecord
Information, stored in a driver or a workshop card, related to an event associated to the card holder (Annex 1C requirements 261, 286, 318 and 341).

eventType is the type of the event.
eventBeginTime is the date and time of beginning of event.
eventEndTime is the date and time of end of event.
eventVehicleRegistration is the VRN and registering Member State of vehicle in which the event happened.
2.21. CardFaultData
Information, stored in a driver or a workshop card, related to the faults associated to the card holder (Annex 1C requirements 263, 288, 318, and 341).

CardFaultData is a sequence of Recording Equipment faults set of records followed by card faults set of records.
cardFaultRecords is a set of fault records of a given fault category (Recording Equipment or card).
2.22. CardFaultRecord
Information, stored in a driver or a workshop card, related to a fault associated to the card holder (Annex 1C requirement 264, 289, 318, and 341).

faultType is the type of the fault.
faultBeginTime is the date and time of beginning of fault.
faultEndTime is the date and time of end of fault.
faultVehicleRegistration is the VRN and registering Member State of vehicle in which the fault happened.
2.23. CardIccIdentification
Information, stored in a card, related to the identification of the integrated circuit (IC) card (Annex 1C requirement 248).

clockStop is the Clockstop mode as defined in appendix 2.
cardExtendedSerialNumber is the IC card unique serial number as further specified by the ExtendedSerialNumber data type.
cardApprovalNumber is the type approval number of the card.
cardPersonaliserID is the card personaliser ID encoded as ManufacturerCode.
embedderIcAssemblerId provides information about the embedder/IC assembler.
icIdentifier is the Identifier of the IC on the card and its IC manufacturer as defined in ISO/IEC 7816-6.
2.24. CardIdentification
Information, stored in a card, related to the identification of the card (Annex 1C requirements 255, 280, 310, 333, 359, 365, 371, and 377).
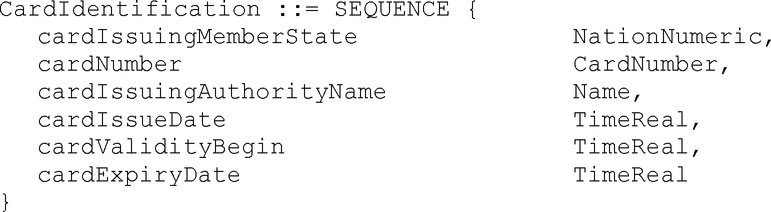
cardIssuingMemberState is the code of the Member State issuing the card.
cardNumber is the card number of the card.
cardIssuingAuthorityName is the name of the authority having issued the Card.
cardIssueDate is the issue date of the Card to the current holder.
cardValidityBegin is the first date of validity of the card.
cardExpiryDate is the date when the validity of the card ends.
2.25. CardMACertificate
Generation 2:
Certificate of the card public key for mutual authentication with a VU. The structure of this certificate is specified in Appendix 11.
![]()
2.26. CardNumber
A card number as defined by definition g).

driverIdentification is the unique identification of a driver in a Member State.
ownerIdentification is the unique identification of a company or a workshop or a control body within a member state.
cardConsecutiveIndex is the card consecutive index.
cardReplacementIndex is the card replacement index.
cardRenewalIndex is the card renewal index.
The first sequence of the choice is suitable to code a driver card number, the second sequence of the choice is suitable to code workshop, control, and company card numbers.
2.27. CardPlaceDailyWorkPeriod
Information, stored in a driver or a workshop card, related to the places where daily work periods begin and/or end (Annex 1C requirements 272, 297, 325, and 348).

placePointerNewestRecord is the index of the last updated place record.
Value assignment: Number corresponding to the numerator of the place record, beginning with ‘0’ for the first occurrence of the place records in the structure.
placeRecords is the set of records containing the information related to the places entered.
2.28. CardPrivateKey
Generation 1:
The private key of a card.
![]()
2.29. CardPublicKey
The public key of a card.
![]()
2.30. CardRenewalIndex
A card renewal index (definition i)).
![]()
Value assignment: (see this Annex chapter VII).
|
‘0’ |
First issue. |
Order for increase: ‘0, …, 9, A, …, Z’
2.31. CardReplacementIndex
A card replacement index (definition j)).
![]()
Value assignment: (see this Annex chapter VII).
|
‘0’ |
Original card. |
Order for increase: ‘0, …, 9, A, …, Z’
2.32. CardSignCertificate
Generation 2:
Certificate of the card public key for signature. The structure of this certificate is specified in Appendix 11.
![]()
2.33. CardSlotNumber
Code to distinguish between the two slots of a Vehicle Unit.

Value assignment: not further specified.
2.34. CardSlotsStatus
Code indicating the type of cards inserted in the two slots of the vehicle unit.
![]()
Value assignment — Octet Aligned: ‘ccccdddd’B
|
‘cccc’B |
Identification of the type of card inserted in the co-driver slot, |
|
‘dddd’B |
Identification of the type of card inserted in the driver slot, |
with the following identification codes:
|
‘0000’B |
no card is inserted, |
|
‘0001’B |
a driver card is inserted, |
|
‘0010’B |
a workshop card is inserted, |
|
‘0011’B |
a control card is inserted, |
|
‘0100’B |
a company card is inserted. |
2.35. CardSlotsStatusRecordArray
Generation 2:
The CardSlotsStatus plus metadata as used in the download protocol.

recordType denotes the type of the record (CardSlotsStatus). Value Assignment: See RecordType
recordSize is the size of the CardSlotsStatus in bytes.
noOfRecords is the number of records in the set records.
records is the set of CardSlotsStatus records.
2.36. CardStructureVersion
Code indicating the version of the implemented structure in a tachograph card.

Value assignment: ‘aabb’H:
|
‘aa’H |
Index for changes of the structure.
|
||||
|
‘bb’H |
Index for changes concerning the use of the data elements defined for the structure given by the high byte.
|
2.37. CardVehicleRecord
Information, stored in a driver or workshop card, related to a period of use of a vehicle during a calendar day (Annex 1C requirements 269, 294, 322, and 345).
|
|
Generation 1:  Text of image
Text of image
vehicleOdometerBegin is the vehicle odometer value at the beginning of the period of use of the vehicle. vehicleOdometerEnd is the vehicle odometer value at the end of the period of use of the vehicle. vehicleFirstUse is the date and time of the beginning of the period of use of the vehicle. vehicleLastUse is the date and time of the end of the period of use of the vehicle. vehicleRegistration is the VRN and the registering Member State of the vehicle. vuDataBlockCounter is the value of the VuDataBlockCounter at last extraction of the period of use of the vehicle. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data element is used: VehicleIdentificationNumber is the vehicle identification number referring to the vehicle as a whole. |
2.38. CardVehiclesUsed
Information, stored in a driver or workshop card, related to the vehicles used by the card holder (Annex 1C requirements 270, 295, 323, and 346).

vehiclePointerNewestRecord is the index of the last updated vehicle record.
Value assignment: Number corresponding to the numerator of the vehicle record, beginning with ‘0’ for the first occurrence of the vehicle records in the structure.
cardVehicleRecords is the set of records containing information on vehicles used.
2.39. CardVehicleUnitRecord
Generation 2:
Information, stored in a driver or workshop card, related to a vehicle unit that was used (Annex 1C requirement 303 and 351).

timeStamp is the beginning of the period of use of the vehicle unit (i.e. first card insertion in the vehicle unit for the period).
manufacturerCode identifies the manufacturer of the Vehicle Unit.
deviceID identifies the Vehicle Unit type of a manufacturer. The value is manufacturer specific.
vuSoftwareVersion is the software version number of the Vehicle Unit.
2.40. CardVehicleUnitsUsed
Generation 2:
Information, stored in a driver or workshop card, related to the vehicle units used by the card holder (Annex 1C requirement 306 and 352).
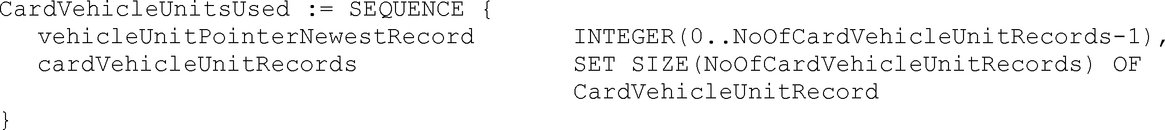
vehicleUnitPointerNewestRecord is the index of the last updated vehicle unit record.
Value assignment: Number corresponding to the numerator of the vehicle unit record, beginning with ‘0’ for the first occurrence of the vehicle unit records in the structure.
cardVehicleUnitRecords is the set of records containing information on vehicle units used.
2.41. Certificate
The certificate of a public key issued by a Certification Authority.
|
|
Generation 1:  Text of image
Text of image
Value assignment: digital signature with partial recovery of a CertificateContent according to Appendix 11 common security mechanisms: Signature (128 bytes) || Public Key remainder (58 bytes) || Certification Authority Reference (8 bytes). |
|
|
Generation 2:  Text of image
Text of image
Value assignment: See Appendix 11 |
2.42. CertificateContent
Generation 1:
The (clear) content of the certificate of a public key according to Appendix 11 common security mechanisms.

certificateProfileIdentifier is the version of the corresponding certificate.
Value assignment: ‘01h’ for this version.
certificationAuthorityReference identifies the Certification Authority issuing the certificate. It also references the Public Key of this Certification Authority.
certificateHolderAuthorisation identifies the rights of the certificate holder.
certificateEndOfValidity is the date when the certificate expires administratively.
certificateHolderReference identifies the certificate holder. It also references his Public Key.
publicKey is the public key that is certified by this certificate.
2.43. CertificateHolderAuthorisation
Identification of the rights of a certificate holder.

|
|
Generation 1:
|
|
|
Generation 2:
|
2.44. CertificateRequestID
Unique identification of a certificate request. It can also be used as a Vehicle Unit Public Key Identifier if the serial number of the vehicle Unit to which the key is intended is not known at certificate generation time.

requestSerialNumber is a serial number for the certificate request, unique for the manufacturer and the month below.
requestMonthYear is the identification of the month and the year of the certificate request.
Value assignment: BCD coding of Month (two digits) and Year (two last digits).
crIdentifier: is an identifier to distinguish a certificate request from an extended serial number.
Value assignment: ‘FFh’.
manufacturerCode: is the numerical code of the manufacturer requesting the certificate.
2.45. CertificationAuthorityKID
Identifier of the Public Key of a Certification Authority (a Member State or the European Certification Authority).

nationNumeric is the numerical nation code of the Certification Authority.
nationAlpha is the alphanumerical nation code of the Certification Authority.
keySerialNumber is a serial number to distinguish the different keys of the Certification Authority in the case keys are changed.
additionalInfo is a two byte field for additional coding (Certification Authority specific).
caIdentifier is an identifier to distinguish a Certification Authority Key Identifier from other Key Identifiers.
Value assignment: ‘01h’.
2.46. CompanyActivityData
Information, stored in a company card, related to activities performed with the card (Annex 1C requirement 373 and 379).

companyPointerNewestRecord is the index of the last updated companyActivityRecord.
Value assignment: Number corresponding to the numerator of the company activity record, beginning with ‘0’ for the first occurrence of the company activity record in the structure.
companyActivityRecords is the set of all company activity records.
companyActivityRecord is the sequence of information related to one company activity.
companyActivityType is the type of the company activity.
companyActivityTime is the date and time of the company activity.
cardNumberInformation is the card number and the card issuing Member State of the card downloaded, if any.
vehicleRegistrationInformation is the VRN and registering Member State of the vehicle downloaded or locked in or out.
downloadPeriodBegin and downloadPeriodEnd is the period downloaded from the VU, if any.
2.47. CompanyActivityType
Code indicating an activity carried out by a company using its company card.

2.48. CompanyCardApplicationIdentification
Information, stored in a company card related to the identification of the application of the card (Annex 1C requirement 369 and 375).

typeOfTachographCardId is specifying the implemented type of card.
cardStructureVersion is specifying the the version of the structure that is implemented in the card.
noOfCompanyActivityRecords is the number of company activity records the card can store.
2.49. CompanyCardHolderIdentification
Information, stored in a company card, related to the cardholder identification (Annex 1C requirement 372 and 378).

companyName is the name of the holder company.
companyAddress is the address of the holder company.
cardHolderPreferredLanguage is the preferred language of the card holder.
2.50. ControlCardApplicationIdentification
Information, stored in a control card related to the identification of the application of the card (Annex 1C requirement 357 and 363).

typeOfTachographCardId is specifying the implemented type of card.
cardStructureVersion is specifying the version of the structure that is implemented in the card.
noOfControlActivityRecords is the number of control activity records the card can store.
2.51. ControlCardControlActivityData
Information, stored in a control card, related to control activity performed with the card (Annex 1C requirement 361 and 367).

controlPointerNewestRecord is the index of the last updated control activity record.
Value assignment: Number corresponding to the numerator of the control activity record, beginning with ‘0’ for the first occurrence of the control activity record in the structure.
controlActivityRecords is the set of all control activity records.
controlActivityRecord is the sequence of information related to one control.
controlType is the type of the control.
controlTime is the date and time of the control.
controlledCardNumber is the card number and the card issuing Member State of the card controlled.
controlledVehicleRegistration is the VRN and registering Member State of the vehicle in which the control happened.
controlDownloadPeriodBegin and controlDownloadPeriodEnd is the period eventually downloaded.
2.52. ControlCardHolderIdentification
Information, stored in a control card, related to the identification of the cardholder (Annex 1C requirement 360 and 366).

controlBodyName is the name of the control body of the card holder.
controlBodyAddress is the address of the control body of the card holder.
cardHolderName is the name and first name(s) of the holder of the Control Card.
cardHolderPreferredLanguage is the preferred language of the card holder.
2.53. ControlType
Code indicating the activities carried out during a control. This data type is related to Annex 1C requirements 126, 274, 299, 327, and 350.
![]()
|
|
Generation 1: Value assignment — Octet aligned: ‘cvpdxxxx’B (8 bits)
|
|
|
Generation 2: Value assignment — Octet aligned: ‘cvpdexxx’B (8 bits)
|
2.54. CurrentDateTime
The current date and time of the recording equipment.
![]()
Value assignment: not further specified.
2.55. CurrentDateTimeRecordArray
Generation 2:
The current date and time plus metadata as used in the download protocol.

recordType denotes the type of the record (CurrentDateTime). Value Assignment: See RecordType
recordSize is the size of the CurrentDateTime in bytes.
noOfRecords is the number of records in the set records.
records is a set of current date and time records.
2.56. DailyPresenceCounter
Counter, stored in a driver or workshop card, increased by one for each calendar day the card has been inserted in a VU. This data type is related to Annex 1C requirements 266, 299, 320, and 343.
![]()
Value assignment: Consecutive Number with maximum value = 9 999, starting again with 0. At the time of first issuing of the card the number is set to 0.
2.57. Datef
Date expressed in a readily printable numeric format.

Value assignment:
|
yyyy |
Year |
|
mm |
Month |
|
dd |
Day |
|
‘00000000’H |
denotes explicitly no date. |
2.58. DateOfDayDownloaded
Generation 2:
The date and time of the download.
![]()
Value assignment: not further specified.
2.59. DateOfDayDownloadedRecordArray
Generation 2:
The date and time of the download plus metadata as used in the download protocol.

recordType denotes the type of the record (DateOfDayDownloaded). Value Assignment: See RecordType
recordSize is the size of the CurrentDateTime in bytes.
noOfRecords is the number of records in the set records.
records is the set of date and time of the download records.
2.60. Distance
A distance travelled (result of the calculation of the difference between two vehicle's odometer values in kilometers).

Value assignment: Unsigned binary. Value in km in the operational range 0 to 9 999 km.
2.61. DriverCardApplicationIdentification
Information, stored in a driver card related to the identification of the application of the card (Annex 1C requirement 253 and 278).
|
|
Generation 1:  Text of image
Text of image
typeOfTachographCardId is specifying the implemented type of card. cardStructureVersion is specifying the the version of the structure that is implemented in the card. noOfEventsPerType is the number of events per type of event the card can record. noOfFaultsPerType is the number of faults per type of fault the card can record. activityStructureLength indicates the number of bytes available for storing activity records. noOfCardVehicleRecords is the number of vehicle records the card can contain. noOfCardPlaceRecords is the number of places the card can record. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data elements are used:
|
2.62. DriverCardHolderIdentification
Information, stored in a driver card, related to the identification of the cardholder (Annex 1C requirement 256 and 281).

cardHolderName is the name and first name(s) of the holder of the Driver Card.
cardHolderBirthDate is the date of birth of the holder of the Driver Card.
cardHolderPreferredLanguage is the preferred language of the card holder.
2.63. DSRCSecurityData
Generation 2:
The plain text information and the MAC to be transmitted via DSRC from the tachograph to the Remote Interrogator (RI), see Appendix 11 Part B chapter 13 for details.

tagLength is part of the DER-TLV encoding and shall be set to ‘81 10’ (see Appendix 11 Part B chapter 13).
currentDateTime is the current date and time of the vehicle unit.
counter enumerates the RTM messages.
vuSerialNumber is the serial number of the vehicle unit.
dSRCMKVersionNumber is the version number of the DSRC Master Key from which the VU specific DSRC keys were derived.
tagLengthMac is the tag and length of the MAC data object as part of the DER-TLV encoding. The tag shall be set to ‘8E’, the length shall encode the length of the MAC in octets (see Appendix 11 Part B chapter 13).
mac is the MAC calculated over the RTM message (see Appendix 11 Part B chapter 13).
2.64. EGFCertificate
Generation 2:
Certificate of the external GNSS facility public key for mutual authentication with a VU. The structure of this certificate is specified in Appendix 11.
![]()
2.65. EmbedderIcAssemblerId
Provides information about the IC embedder.

countryCode is the 2 letter country code of the module embedder according to ISO 3166.
moduleEmbedder identifies the module embedder.
manufacturerInformation for manufacturer internal usage.
2.66. EntryTypeDailyWorkPeriod
Code to distinguish between begin and end for an entry of a daily work period place and condition of the entry.
|
|
Generation 1  Text of image
Text of image
Value assignment: according to ISO/IEC8824-1. |
|
|
Generation 2  Text of image
Text of image
Value assignment: according to ISO/IEC8824-1. |
2.67. EquipmentType
Code to distinguish different types of equipment for the tachograph application.
![]()
|
|
Generation 1:  Text of image
Text of image
Value assignment: According to ISO/IEC8824-1. Value 0 is reserved for the purpose of designating a Member State or Europe in the CHA field of certificates. |
|
|
Generation 2: The same values as in generation 1 are used with the following additions:  Text of image
Text of image
Note: The generation 2 values for the Plaque, Adapter and the External GNSS connection as well as the generation 1 values for the Vehicle Unit and Motion Sensor may be used in SealRecord, i.e. if applicable. |
2.68. EuropeanPublicKey
Generation 1:
The European public key.
![]()
2.69. EventFaultRecordPurpose
Code explaining why an event or a fault has been recorded.
![]()
Value assignment:
|
|
one of the 10 most recent (or last) events or faults the longest event for one of the last 10 days of occurrence one of the 5 longest events over the last 365 days the last event for one of the last 10 days of occurrence the most serious event for one of the last 10 days of occurrence one of the 5 most serious events over the last 365 days the first event or fault having occurred after the last calibration an active/on-going event or fault RFU manufacturer specific |
2.70. EventFaultType
Code qualifying an event or a fault.
![]()
Value assignment:
|
|
Generation 1:
|
|
|
Generation 2: The same values as in generation 1 are used with the following additions:
|
2.71. ExtendedSealIdentifier
Generation 2:
The extended seal identifier uniquely identifies a seal (Annex 1C requirement 401).

manufacturerCode is a code of the manufacturer of the seal.
sealIdentifier is an identifier for the seal which is unique for the manufacturer.
2.72. ExtendedSerialNumber
Unique identification of an equipment. It can also be used as an equipment Public Key Identifier.
|
|
Generation 1:  Text of image
Text of image
serialNumber is a serial number for the equipment, unique for the manufacturer, the equipment's type and the month and year below. monthYear is the identification of the month and the year of manufacturing (or of serial number assignment). Value assignment: BCD coding of Month (two digits) and Year (two last digits). type is an identifier of the type of equipment. Value assignment: manufacturer specific, with ‘FFh’ reserved value. manufacturerCode: is the numerical code identifying a manufacturer of type approved equipment. |
|
|
Generation 2:  Text of image
Text of image
serialNumber see Generation 1 monthYear see Generation 1 type indicates the type of equipment manufacturerCode: see Generation 1. |
2.73. FullCardNumber
Code fully identifying a tachograph card.

cardType is the type of the tachograph card.
cardIssuingMemberState is the code of the Member State having issued the card.
cardNumber is the card number.
2.74. FullCardNumberAndGeneration
Generation 2:
Code fully identifying a tachograph card and its generation.

fullcardNumber identifies the tachograph card.
generation indicates the generation of the tachograph card used.
2.75. Generation
Generation 2:
Indicates the generation of tachograph used.

Value assignment:
|
‘00’H |
RFU |
|
‘01’H |
Generation 1 |
|
‘02’H |
Generation 2 |
|
‘03’H .. ‘FF’H |
RFU |
2.76. GeoCoordinates
Generation 2:
The geo-coordinates are encoded as integers. These integers are multiples of the ±DDMM.M encoding for the latitude and ±DDDMM.M for the longitude. Here ±DD respectively ±DDD denotes the degrees and MM.M the minutes.

latitude is encoded as a multiple (factor 10) of the ±DDMM.M representation.
longitude is encoded as a multiple (factor 10) of the ±DDDMM.M representation.
2.77. GNSSAccuracy
Generation 2:
The accuracy of the GNSS position data (definition eee)). This accuracy is encoded as integer and is a multiple (factor 10) of the X.Y value provided by the GSA NMEA sentence.
![]()
2.78. GNSSContinuousDriving
Generation 2:
Information, stored in a driver or workshop card, related to the GNSS position of the vehicle if the continuous driving time of the driver reaches a multiple of three hours (Annex 1C requirement 306 and 354).

gnssCDPointerNewestRecord is the index of the last updated GNSS continuous driving record.
Value assignment: Number corresponding to the numerator of the GNSS continuous driving record, beginning with ‘0’ for the first occurrence of the GNSS continuous driving record in the structure.
gnssContinuousDrivingRecords is the set of records containing the date and time the continuous driving reaches a multiple of three hours and information on the position of the vehicle.
2.79. GNSSContinuousDrivingRecord
Generation 2:
Information, stored in a driver or workshop card, related to the GNSS position of the vehicle if the continuous driving time of the driver reaches a multiple of three hours (Annex 1C requirement 305 and 353).

timeStamp is the date and time when the continuous driving time of the card holder reaches a multiple of three hours.
gnssPlaceRecord contains information related to the position of the vehicle.
2.80. GNSSPlaceRecord
Generation 2:
Information related to the GNSS position of the vehicle (Annex 1C requirements 108, 109, 110, 296, 305, 347, and 353).

timeStamp is the date and time when the GNSS position of the vehicle was determined.
gnssAccuracy is the accuracy of the GNSS position data.
geoCoordinates is the recorded location using GNSS.
2.81. HighResOdometer
Odometer value of the vehicle: Accumulated distance travelled by the vehicle during its operation.
![]()
Value assignment: Unsigned binary. Value in 1/200 km in the operating range 0 to 21 055 406 km.
2.82. HighResTripDistance
A distance travelled during all or part of a journey.
![]()
Value assignment: Unsigned binary. Value in 1/200 km in the operating range 0 to 21 055 406 km.
2.83. HolderName
The surname and first name(s) of a card holder.

holderSurname is the surname (family name) of the holder. This surname does not include titles.
Value assignment: When a card is not personal, holderSurname contains the same information as companyName or workshopName or controlBodyName.
holderFirstNames is the first name(s) and initials of the holder.
2.84. InternalGNSSReceiver
Generation 2:
Information if the GNSS receiver is internal or external to the vehicle unit. True means that the GNSS receiver is internal to the VU. False means that the GNSS receiver is external.
![]()
2.85. K-ConstantOfRecordingEquipment
Constant of the recording equipment (definition m)).
![]()
Value assignment: Pulses per kilometer in the operating range 0 to 64 255 pulses/km.
2.86. KeyIdentifier
A unique identifier of a Public Key used to reference and select the key. It also identifies the holder of the key.

The first choice is suitable to reference the public key of a Vehicle Unit or of a tachograph card.
The second choice is suitable to reference the public key of a Vehicle Unit (in the case the serial number of the Vehicle Unit cannot be known at certificate generation time).
The third choice is suitable to reference the public key of a Member State.
2.87. KMWCKey
Generation 2:
AES key and its associated key version used for VU — Motion Sensor pairing. For details see Appendix 11.

kMWCKey is the length of the AES key concatenated with the key which is used for VU — Motion Sensor pairing.
keyVersion denotes the key version of the AES key.
2.88. Language
Code identifying a language.
![]()
Value assignment: Two-letter lower-case coding according to ISO 639.
2.89. LastCardDownload
Date and time, stored on a driver card, of last card download (for other purposes than control) Annex 1C requirement 257 and 282. This date is updateable by a VU or any card reader.
![]()
Value assignment: not further specified.
2.90. LinkCertificate
Generation 2:
The link certificate between European Root CA key pairs.
![]()
2.91. L-TyreCircumference
Effective circumference of the wheel tyres (definition u)).
![]()
Value assignment: Unsigned binary, value in 1/8 mm in the operating range 0 to 8 031 mm.
2.92. MAC
Generation 2:
A cryptographic checksum of 8, 12 or 16 bytes length corresponding to the cipher suites specified in Appendix 11.

2.93. ManualInputFlag
Code identifying whether a cardholder has manually entered driver activities at card insertion or not (Annex 1B requirement 081 and Annex 1C requirement 102).

Value assignment: not further specified.
2.94. ManufacturerCode
Code identifying a manufacturer of type approved equipment.
![]()
The laboratory competent for interoperability tests maintains and publishes the list of manufacturer codes on its web site (Annex 1C requirement 454).
ManufacturerCodes are provisionally assigned to developers of tachograph equipment on application to the laboratory competent for interoperability tests.
2.95. ManufacturerSpecificEventFaultData
Generation 2:
Manufacturer specific error codes simplify the error analysis and maintenance of vehicle units.

manufacturerCode identifies the manufacturer of the Vehicle Unit.
manufacturerSpecificErrorCode is an error code specific to the manufacturer.
2.96. MemberStateCertificate
The certificate of the public key of a member state issued by the European certification authority.
![]()
2.97. MemberStateCertificateRecordArray
Generation 2:
The member state certificate plus metadata as used in the download protocol.

recordType denotes the type of the record (MemberStateCertificate). Value Assignment: See RecordType
recordSize is the size of the MemberStateCertificate in bytes.
noOfRecords is the number of records in the set records. The value shall be set to 1 as the certficates may have different lengths.
records is the set of member state certificates.
2.98. MemberStatePublicKey
Generation 1:
The public key of a Member State.
![]()
2.99. Name
A name.

codePage specifies a character set defined in Chapter 4,
name is a name encoded using the specified character set.
2.100. NationAlpha
Alphabetic reference to a country shall be in accordance with the distinguishing signs used on vehicles in international traffic (United Nations Vienna Convention on Road Traffic, 1968).
![]()
The Nation Alpha and Numeric codes shall be held on a list maintained on the website of the laboratory appointed to carry out interoperability testing, as set out in Annex 1C requirement 440.
2.101. NationNumeric
Numerical reference to a country.

Value assignment: see data type 2.100 (NationAlpha).
Any amendment or updating of the Nation Alpha or Numeric specification described in the above paragraph shall only be made out after the appointed laboratory has obtained the views of type approved digital and smart tachograph vehicle unit manufacturers.
2.102. NoOfCalibrationRecords
Number of calibration records, a workshop card can store.
|
|
Generation 1:  Text of image
Text of image
Value assignment: see Appendix 2. |
|
|
Generation 2:  Text of image
Text of image
Value assignment: see Appendix 2. |
2.103. NoOfCalibrationsSinceDownload
Counter indicating the number of calibrations performed with a workshop card since its last download (Annex 1C requirement 317 and 340).

Value assignment: Not specified further.
2.104. NoOfCardPlaceRecords
Number of place records a driver or workshop card can store.
|
|
Generation 1: Value assignment: see Appendix 2. |
|
|
Generation 2:  Text of image
Text of image
Value assignment: see Appendix 2. |
2.105. NoOfCardVehicleRecords
Number of vehicles used records a driver or workshop card can store.

Value assignment: see Appendix 2.
2.106. NoOfCardVehicleUnitRecords
Generation 2:
Number of vehicle units used records a driver or workshop card can store.

Value assignment: see Appendix 2.
2.107. NoOfCompanyActivityRecords
Number of company activity records, a company card can store.
![]()
Value assignment: see Appendix 2.
2.108. NoOfControlActivityRecords
Number of control activity records, a control card can store.
![]()
Value assignment: see Appendix 2.
2.109. NoOfEventsPerType
Number of events per type of event a card can store.
![]()
Value assignment: see Appendix 2.
2.110. NoOfFaultsPerType
Number of faults per type of fault a card can store.
![]()
Value assignment: see Appendix 2.
2.111. NoOfGNSSCDRecords
Generation 2:
Number of GNSS continuous driving records a card can store.

Value assignment: see Appendix 2.
2.112. NoOfSpecificConditionRecords
Generation 2:
Number of specific condition records a card can store.
![]()
Value assignment: see Appendix 2.
2.113. OdometerShort
Odometer value of the vehicle in a short form.

Value assignment: Unsigned binary. Value in km in the operating range 0 to 9 999 999 km.
2.114. OdometerValueMidnight
The vehicle's odometer value at midnight on a given day (Annex 1B requirement 090 and Annex 1C requirement 113).
![]()
Value assignment: not further specified.
2.115. OdometerValueMidnightRecordArray
Generation 2:
The OdometerValueMidnight plus metadata used in the download protocol.

recordType denotes the type of the record (OdometerValueMidnight). Value Assignment: See RecordType
recordSize is the size of the OdometerValueMidnight in bytes.
noOfRecords is the number of records in the set records.
records is the set of OdometerValueMidnight records.
2.116. OverspeedNumber
Number of over speeding events since the last over speeding control.
![]()
Value assignment: 0 means that no over speeding event has occurred since the last over speeding control, 1 means that one over speeding event has occurred since the last over speeding control …255 means that 255 or more over speeding events have occurred since the last over speeding control.
2.117. PlaceRecord
Information related to a place where a daily work period begins or ends (Annex 1C requirements 108, 271, 296, 324, and 347).
|
|
Generation 1:  Text of image
Text of image
entryTime is a date and time related to the entry. entryTypeDailyWorkPeriod is the type of entry. dailyWorkPeriodCountry is the country entered. dailyWorkPeriodRegion is the region entered. vehicleOdometerValue is the odometer value at the time of place entry. |
|
|
Generation 2:  Text of image
Text of image
In addition to Generation 1 the following component is used: entryGNSSPlaceRecord is the recorded location and time. |
2.118. PreviousVehicleInfo
Information related to the vehicle previously used by a driver when inserting his card in a vehicle unit (Annex 1B requirement 081 and Annex 1C requirement 102).
|
|
Generation 1:  Text of image
Text of image
vehicleRegistrationIdentification is the VRN and the registering Member State of the vehicle. cardWithdrawalTime is the card withdrawal date and time. |
|
|
Generation 2: 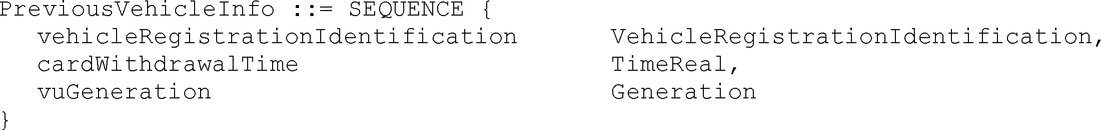 Text of image
Text of image
In addition to generation 1 the following data element is used: vuGeneration identifies the generation of the vehicle unit. |
2.119. PublicKey
Generation 1:
A public RSA key.

rsaKeyModulus is the Modulus of the key pair.
rsaKeyPublicExponent is the public exponent of the key pair.
2.120. RecordType
Generation 2:
Reference to a record type. This data type is used in RecordArrays.
![]()
Value assignment:
|
|
ActivityChangeInfo, CardSlotsStatus, CurrentDateTime, MemberStateCertificate, OdometerValueMidnight, DateOfDayDownloaded, SensorPaired, Signature, SpecificConditionRecord, VehicleIdentificationNumber, VehicleRegistrationNumber, VuCalibrationRecord, VuCardIWRecord, VuCardRecord, VuCertificate, VuCompanyLocksRecord, VuControlActivityRecord, VuDetailedSpeedBlock, VuDownloadablePeriod, VuDownloadActivityData, VuEventRecord, VuGNSSCDRecord, VuITSConsentRecord, VuFaultRecord, VuIdentification, VuOverSpeedingControlData, VuOverSpeedingEventRecord, VuPlaceDailyWorkPeriodRecord, VuTimeAdjustmentGNSSRecord, VuTimeAdjustmentRecord, VuPowerSupplyInterruptionRecord, SensorPairedRecord, SensorExternalGNSSCoupledRecord, RFU, Manufacturer specific. |
2.121. RegionAlpha
Alphabetic reference to a region within a specified country.
![]()
|
|
Generation 1: Value assignment:  Text of image
Text of image
|
|
|
Generation 2: The RegionAlpha codes shall be held on a list maintained on the website of the laboratory appointed to carry out interoperability testing. |
2.122. RegionNumeric
Numerical reference to a region within a specified country.
![]()
|
|
Generation 1: Value assignment:  Text of image
Text of image
|
|
|
Generation 2: The RegionNumeric codes shall be held on a list maintained on the website of the laboratory appointed to carry out interoperability testing. |
2.123. RemoteCommunicationModuleSerialNumber
Generation 2:
Serial number of the Remote Communication Module.
![]()
2.124. RSAKeyModulus
Generation 1:
The modulus of a RSA key pair.
![]()
Value assignment: Unspecified.
2.125. RSAKeyPrivateExponent
Generation 1:
The private exponent of a RSA key pair.
![]()
Value assignment: Unspecified.
2.126. RSAKeyPublicExponent
Generation1:
The public exponent of a RSA key pair.
![]()
Value assignment: Unspecified.
2.127. RtmData
Generation2:
For the definition of this data type see Appendix 14.
2.128. SealDataCard
Generation 2:
This data type stores information about the seals that are attached to the different components of a vehicle and is intended for storage on a card. This data type is related to Annex 1C requirement 337.

noOfSealRecords is the number of records in sealRecords.
sealRecords is a set of seal records.
2.129. SealDataVu
Generation 2:
This data type stores information about the seals that are attached to the different components of a vehicle and is intended for storage in a Vehicle Unit.
![]()
sealRecords is a set of seal records. If there are less than 5 seals available the value of the EquipmentType in all unused sealRecords shall be set to 16, i.e. unused.
2.130. SealRecord
Generation 2:
This data type stores information about a seal that is attached to a component. This data type is related to Annex 1C requirement 337.

equipmentType identifies the type of equipment the seal is attached to.
extendedSealIdentifier is the identifier of the seal attached to the equipment.
2.131. SensorApprovalNumber
Type approval number of the sensor.
|
|
Generation 1: Value assignment: Unspecified. |
|
|
Generation 2: Value assignment: The approval number shall be provided as published on the corresponding European Commission web site, i.e. for example including hyphens if any. The approval number shall be left-aligned. |
2.132. SensorExternalGNSSApprovalNumber
Generation 2:
Type approval number of the external GNSS facility.
![]()
Value assignment:
The approval number shall be provided as published on the corresponding European Commission web site, i.e. for example including hyphens if any. The approval number shall be left-aligned.
2.133. SensorExternalGNSSCoupledRecord
Generation 2:
Information, stored in a vehicle unit, related to the identification of the external GNSS facility coupled with the vehicle unit (Annex 1C requirement 100).

sensorSerialNumber is the serial number of the external GNSS facility coupled with the vehicle unit.
sensorApprovalNumber is the approval number of this external GNSS facility.
sensorCouplingDate is a date of coupling of this external GNSS facility with the vehicle unit.
2.134. SensorExternalGNSSIdentification
Generation 2:
Information related to the identification of the external GNSS facility (Annex 1C requirement 98).

sensorSerialNumber is the extended serial number of the external GNSS facility.
sensorApprovalNumber is the approval number of the external GNSS facility.
sensorSCIdentifier is the identifier of the security component of the external GNSS facility.
sensorOSIdentifier is the identifier of the operating system of the external GNSS facility.
2.135. SensorExternalGNSSInstallation
Generation 2:
Information, stored in an external GNSS facility, related to the installation of the external GNSS sensor (Annex 1C requirement 123).

sensorCouplingDateFirst is the date of the first coupling of external GNSS facility with a vehicle unit.
firstVuApprovalNumber is the approval number of the first vehicle unit coupled with the external GNSS facility.
firstVuSerialNumber is the serial number of the first vehicle unit paired with the external GNSS facility.
sensorCouplingDateCurrent is the date of the current coupling of external GNSS facility with a vehicle unit.
currentVuApprovalNumber is the approval number of the vehicle unit currently coupled with the external GNSS facility.
currentVUSerialNumber is the serial number of the vehicle unit currently coupled with the external GNSS facility.
2.136. SensorExternalGNSSOSIdentifier
Generation 2:
Identifier of the operating system of the external GNSS facility.
![]()
Value assignment: manufacturer specific.
2.137. SensorExternalGNSSSCIdentifier
Generation 2:
This type is used e.g. to identify the cryptographic module of the external GNSS facility.
Identifier of the security component of the external GNSS facility.
![]()
Value assignment: component manufacturer specific.
2.138. SensorGNSSCouplingDate
Generation 2:
Date of a coupling of the external GNSS facility with a vehicle unit.
![]()
Value assignment: Unspecified.
2.139. SensorGNSSSerialNumber
Generation 2:
This type is used to store the serial number of the GNSS receiver both when it is inside the VU and when it is outside the VU.
Serial number of the GNSS receiver.
![]()
2.140. SensorIdentification
Information, stored in a motion sensor, related to the identification of the motion sensor (Annex 1B requirement 077 and Annex 1C requirement 95).

sensorSerialNumber is the extended serial number of the motion sensor (includes part number and manufacturer code).
sensorApprovalNumber is the approval number of the motion sensor.
sensorSCIdentifier is the identifier of the security component of the motion sensor.
sensorOSIdentifier is the identifier of the operating system of the motion sensor.
2.141. SensorInstallation
Information, stored in a motion sensor, related to the installation of the motion sensor (Annex 1B requirement 099 and Annex 1C requirement 122).

sensorPairingDateFirst is the date of the first pairing of the motion sensor with a vehicle unit.
firstVuApprovalNumber is the approval number of the first vehicle unit paired with the motion sensor.
firstVuSerialNumber is the serial number of the first vehicle unit paired with the motion sensor.
sensorPairingDateCurrent is the date of the current pairing of the motion sensor with the vehicle unit.
currentVuApprovalNumber is the approval number of the vehicle unit currently paired with the motion sensor.
currentVUSerialNumber is the serial number of the vehicle unit currently paired with the motion sensor.
2.142. SensorInstallationSecData
Information, stored in a workshop card, related to the security data needed for pairing motion sensors to vehicle units (Annex 1C requirement 308 and 331).
|
|
Generation 1: Value assignment: in accordance with ISO 16844-3. |
|
|
Generation 2: As described in Appendix 11 a workshop card shall store up to three keys for VU Motion Sensor pairing. These keys have different key versions. 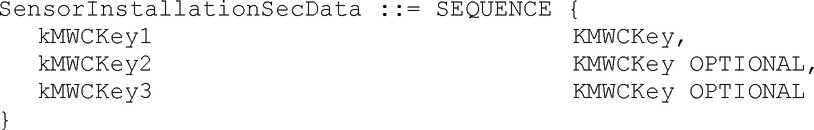 Text of image
Text of image
|
2.143. SensorOSIdentifier
Identifier of the operating system of the motion sensor.
![]()
Value assignment: manufacturer specific.
2.144. SensorPaired
Generation 1:
Information, stored in a vehicle unit, related to the identification of the motion sensor paired with the vehicle unit (Annex 1B requirement 079).

sensorSerialNumber is the serial number of the motion sensor currently paired with the vehicle unit.
sensorApprovalNumber is the approval number of the motion sensor currently paired with the vehicle unit.
sensorPairingDateFirst is the date of the first pairing with a vehicle unit of the motion sensor currently paired with the vehicle unit.
2.145. SensorPairedRecord
Generation 2:
Information, stored in a vehicle unit, related to the identification of a motion sensor paired with the vehicle unit (Annex 1C requirement 97).

sensorSerialNumber is the serial number of a motion sensor paired with the vehicle unit.
sensorApprovalNumber is the approval number of this motion sensor.
sensorPairingDate is a date of pairing of this motion sensor with the vehicle unit.
2.146. SensorPairingDate
Date of a pairing of the motion sensor with a vehicle unit.
![]()
Value assignment: Unspecified.
2.147. SensorSCIdentifier
Identifier of the security component of the motion sensor.
![]()
Value assignment: component manufacturer specific.
2.148. SensorSerialNumber
Serial number of the motion sensor.
![]()
2.149. Signature
A digital signature.
|
|
Generation 1: Value assignment: in accordance with Appendix 11 Common security mechanisms. |
|
|
Generation 2: Value assignment: in accordance with Appendix 11 Common security mechanisms. |
2.150. SignatureRecordArray
Generation 2:
A set of signatures plus metadata used in the download protocol.

recordType denotes the type of the record (Signature). Value Assignment: See RecordType
recordSize is the size of the Signature in bytes.
noOfRecords is the number of records in the set records. The value shall be set to 1 as the signatures may have different lengths.
records is the set of signatures.
2.151. SimilarEventsNumber
The number of similar events for one given day (Annex 1B requirement 094 and Annex 1C requirement 117).

Value assignment: 0 is not used, 1 means that only one event of that type has occurred and has been stored on that day, 2 means that 2 events of that type has occurred on that day (one only has been stored), …255 means that 255 or more events of that type have occurred on that day.
2.152. SpecificConditionRecord
Information, stored in a driver card, a workshop card or a vehicle unit, related to a specific condition (requirements Annex 1C 130, 276, 301, 328, and 355).

entryTime is the date and time of the entry.
specificConditionType is the code identifying the specific condition.
2.153. SpecificConditions
Information, stored in a driver card, a workshop card or a vehicle unit, related to a specific condition (Annex 1C requirement 131, 277, 302, 329, and 356).
Generation 2:

conditionPointerNewestRecord is the index of the last updated specific condition record.
Value assignment: Number corresponding to the numerator of the specific condition record, beginning with ‘0’ for the first occurrence of the specific condition record in the structure.
specificConditionRecords is the set of records containing information on the specific conditions recorded.
2.154. SpecificConditionType
Code identifying a specific condition (Annex 1B requirements 050b, 105a, 212a and 230a and Annex 1C requirements 62).
![]()
|
|
Generation 1: Value assignment:
|
|
|
Generation 2: Value assignment:
|
2.155. Speed
Speed of the vehicle (km/h).
![]()
Value assignment: kilometers per hour in the operational range 0 to 220 km/h.
2.156. SpeedAuthorised
Maximum authorised Speed of the vehicle (definition hh)).
![]()
2.157. SpeedAverage
Average speed in a previously defined duration (km/h).
![]()
2.158. SpeedMax
Maximum speed measured in a previously defined duration.
![]()
2.159. TachographPayload
Generation 2:
For the definition of this data type see Appendix 14.
2.160. TachographPayloadEncrypted
Generation 2:
The DER-TLV encrypted tachograph payload, i.e. the data sent encrypted in the RTM message. For the encryption see Appendix 11 Part B chapter 13.
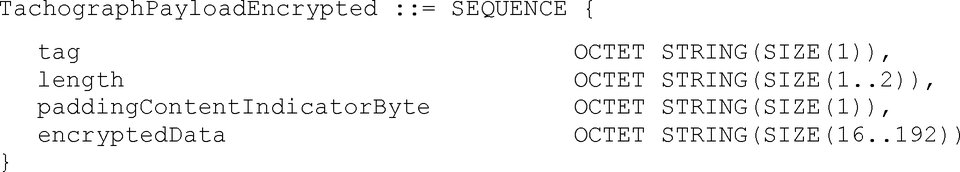
tag is part of the DER-TLV encoding and shall be set to ‘87’ (see Appendix 11 Part B chapter 13).
length is part of the DER-TLV encoding and shall encode the length of the following paddingContentIndicatorByte and the encryptedData.
paddingContentIndicatorByte shall be set to ‘00’.
encryptedData is encrypted tachographPayload as specified in Appendix 11 Part B chapter 13. The length of this data in octests shall always be a multiple of 16.
2.161. TDesSessionKey
Generation 1:
A triple DES session key.

Value assignment: not further specified.
2.162. TimeReal
Code for a combined date and time field, where the date and time are expressed as seconds past 00h.00m.00s. on 1 January 1970 GMT.
![]()
Value assignment — Octet Aligned: Number of seconds since midnight 1 January 1970 GMT.
The max. possible date/time is in the year 2106.
2.163. TyreSize
Designation of tyre dimensions.
![]()
Value assignment: in accordance with Directive 92/23 (EEC) 31/03/92 O.J. L129 p.95.
2.164. VehicleIdentificationNumber
Vehicle Identification Number (VIN) referring to the vehicle as a whole, normally chassis serial number or frame number.
![]()
Value assignment: As defined in ISO 3779.
2.165. VehicleIdentificationNumberRecordArray
Generation 2:
The Vehicle Idenification Number plus metadata as used in the download protocol.

recordType denotes the type of the record (VehicleIdentificationNumber). Value Assignment: See RecordType
recordSize is the size of the VehicleIdentificationNumber in bytes.
noOfRecords is the number of records in the set records.
records is the set of vehicle identification numbers.
2.166. VehicleRegistrationIdentification
Identification of a vehicle, unique for Europe (VRN and Member State).

vehicleRegistrationNation is the nation where the vehicle is registered.
vehicleRegistrationNumber is the registration number of the vehicle (VRN).
2.167. VehicleRegistrationNumber
Registration number of the vehicle (VRN). The registration number is assigned by the vehicle licensing authority.

codePage specifies a character set defined in Chapter 4,
vehicleRegNumber is a VRN encoded using the specified character set.
Value assignment: Country specific.
2.168. VehicleRegistrationNumberRecordArray
Generation 2:
The Vehicle Registration Number plus metadata as used in the download protocol.

recordType denotes the type of the record (VehicleRegistrationNumber). Value Assignment: See RecordType
recordSize is the size of the VehicleRegistrationNumber in bytes.
noOfRecords is the number of records in the set records.
records is the set of vehicle registration numbers.
2.169. VuAbility
Generation 2:
Information stored in a VU on the ability of the VU to use generation 1 tachograph cards or not (Annex 1C requirement 121).
![]()
Value assignment — Octet Aligned:‘xxxxxxxa’B (8 bits)
For the ability to support of generation 1:
|
‘a’B |
Ability to support generation 1 tachograph cards:
|
||||
|
‘xxxxxxx’B |
RFU |
2.170. VuActivityDailyData
Generation 1:
Information, stored in a VU, related to changes of activity and/or changes of driving status and/or changes of card status for a given calendar day (Annex 1B requirement 084 and Annex 1C requirement 105, 106, 107) and to slots status at 00:00 that day.

noOfActivityChanges is the number of ActivityChangeInfo words in the activityChangeInfos set.
activityChangeInfos is the set of ActivityChangeInfo words stored in the VU for the day. It always includes two ActivityChangeInfo words giving the status of the two slots at 00:00 that day.
2.171. VuActivityDailyRecordArray
Generation 2:
Information, stored in a VU, related to changes of activity and/or changes of driving status and/or changes of card status for a given calendar day (Annex 1C requirement 105, 106, 107) and to slots status at 00:00 that day.

recordType denotes the type of the record (ActivityChangeInfo). Value Assignment: See RecordType
recordSize is the size of the ActivityChangeInfo in bytes.
noOfRecords is the number of records in the set records.
records is the set of ActivityChangeInfo words stored in the VU for the day. It always includes two ActivityChangeInfo words giving the status of the two slots at 00:00 that day.
2.172. VuApprovalNumber
Type approval number of the vehicle unit.
|
|
Generation 1: Value assignment: Unspecified. |
|
|
Generation 2: Value assignment: The approval number shall be provided as published on the corresponding European Commission web site, i.e. for example including hyphens if any. The approval number shall be left-aligned. |
2.173. VuCalibrationData
Generation 1:
Information, stored in a vehicle unit, related to the calibrations of the recording equipment (Annex 1B requirement 098).

noOfVuCalibrationRecords is the number of records contained in the vuCalibrationRecords set.
vuCalibrationRecords is the set of calibration records.
2.174. VuCalibrationRecord
Information, stored in a vehicle unit, related a calibration of the recording equipment (Annex 1B requirement 098 and Annex 1C requirement 119 and 120).
|
|
Generation 1:  Text of image
Text of image
calibrationPurpose is the purpose of the calibration. workshopName, workshopAddress are the workshop name and address. workshopCardNumber identifies the workshop card used during the calibration. workshopCardExpiryDate is the card expiry date. vehicleIdentificationNumber is the VIN. vehicleRegistrationIdentification contains the VRN and registering Member State. wVehicleCharacteristicConstant is the characteristic coefficient of the vehicle. kConstantOfRecordingEquipment is the constant of the recording equipment. lTyreCircumference is the effective circumference of the wheel tyres. tyreSize is the designation of the dimension of the tyres mounted on the vehicle authorisedSpeed is the authorised speed of the vehicle. oldOdometerValue, newOdometerValue are the old and new values of the odometer. oldTimeValue, newTimeValue are the old and new values of date and time. nextCalibrationDate is the date of the next calibration of the type specified in CalibrationPurpose to be carried out by the authorised inspection authority. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data element is used: sealDataVu gives information about the seals that are attached to different components of the vehicle. |
2.175. VuCalibrationRecordArray
Generation 2:
Information, stored in a vehicle unit, related to the calibrations of the recording equipment (Annex 1C requirement 119 and 120).

recordType denotes the type of the record (VuCalibrationRecord). Value Assignment: See RecordType
recordSize is the size of the VuCalibrationRecord in bytes.
noOfRecords is the number of records in the set records.
records is the set of calibration records.
2.176. VuCardIWData
Generation 1:
Information, stored in a vehicle unit, related to insertion and withdrawal cycles of driver cards or of workshop cards in the vehicle unit (Annex 1B requirement 081 and Annex 1C requirement 103).

noOfIWRecords is the number of records in the set vuCardIWRecords.
vuCardIWRecords is a set of records related to card insertion withdrawal cycles.
2.177. VuCardIWRecord
Information, stored in a vehicle unit, related to an insertion and withdrawal cycle of a driver card or of a workshop card in the vehicle unit (Annex 1B requirement 081 and Annex 1C requirement 102).
|
|
Generation 1:  Text of image
Text of image
cardHolderName is the driver or workshop card holder's surname and first names as stored in the card. fullCardNumber is the type of card, its issuing Member State and its card number as stored in the card. cardExpiryDate is the card's expiry date as stored in the card. cardInsertionTime is the insertion date and time. vehicleOdometerValueAtInsertion is the vehicle odometer value at card insertion. cardSlotNumber is the slot in which the card is inserted. cardWithdrawalTime is the withdrawal date and time. vehicleOdometerValueAtWithdrawal is the vehicle odometer value at card withdrawal. previousVehicleInfo contains information about the previous vehicle used by the driver, as stored in the card. manualInputFlag is a flag identifying if the cardholder has manually entered driver activities at card insertion. |
|
|
Generation 2:  Text of image
Text of image
Instead of fullCardNumber the generation 2 data structure makes use of the following data element. fullCardNumberAndGeneration is the type of card, its issuing Member State, its card number and generation as stored in the card. |
2.178. VuCardIWRecordArray
Generation 2:
Information, stored in a vehicle unit, related to insertion and withdrawal cycles of driver cards or of workshop cards in the vehicle unit (Annex 1C requirement 103).

recordType denotes the type of the record (VuCardIWRecord). Value Assignment: See RecordType
recordSize is the size of the VuCardIWRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of records related to card insertion withdrawal cycles.
2.179. VuCardRecord
Generation 2:
Information, stored in a vehicle unit, about a tachograph card used (Annex 1C requirement 132).

cardExtendedSerialNumber as read from the file EF_ICC under the MF of the card.
cardPersonaliserID as read from the file EF_ICC under the MF of the card.
typeOfTachographCardId as read from the file EF_Application_Identification under the DF_Tachograph_G2
cardStructureVersion as read from the file EF_Application_Identification under the DF_Tachograph_G2.
cardNumber as read from the file EF_Identification under the DF_Tachograph_G2.
2.180. VuCardRecordArray
Generation 2:
Information stored in a vehicle unit about the tachograph cards used with this VU. This information is intended for the analysis of VU — card problems (Annex 1C requirement 132).

recordType denotes the type of the record (VuCardRecord). Value Assignment: See RecordType
recordSize is the size of the VuCardRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of records related to the tachograph cards used with the VU.
2.181. VuCertificate
Certificate of the public key of a vehicle unit.
![]()
2.182. VuCertificateRecordArray
Generation 2:
The VU certificate plus metadata as used in the download protocol.

recordType denotes the type of the record (VuCertificate). Value Assignment: See RecordType
recordSize is the size of the VuCertificate in bytes.
noOfRecords is the number of records in the set records. The value shall be set to 1 as the certificates may have different lengths.
records is a set of VU certificates.
2.183. VuCompanyLocksData
Generation 1:
Information, stored in a vehicle unit, related to company locks (Annex 1B requirement 104).

noOfLocks is the number of locks listed in vuCompanyLocksRecords.
vuCompanyLocksRecords is the set of company locks records.
2.184. VuCompanyLocksRecord
Information, stored in a vehicle unit, related to one company lock (Annex 1B requirement 104 and Annex 1C requirement 128).
|
|
Generation 1:  Text of image
Text of image
lockInTime, lockOutTime are the date and time of lock-in and lock-out. companyName, companyAddress are the company name and address related with the lock-in. companyCardNumber identifies the card used at lock-in. |
|
|
Generation 2:  Text of image
Text of image
Instead of companyCardNumber the generation 2 data structure makes use of the following data element. companyCardNumberAndGeneration identifies the card including its generation used at lock-in. |
2.185. VuCompanyLocksRecordArray
Generation 2:
Information, stored in a vehicle unit, related to company locks (Annex 1C requirement 128).

recordType denotes the type of the record (VuCompanyLocksRecord). Value Assignment: See RecordType
recordSize is the size of the VuCompanyLocksRecord in bytes.
noOfRecords is the number of records in the set records. Value 0..255.
records is the set of company locks records.
2.186. VuControlActivityData
Generation 1:
Information, stored in a vehicle unit, related to controls performed using this VU (Annex 1B requirement 102).

noOfControls is the number of controls listed in vuControlActivityRecords.
vuControlActivityRecords is the set of control activity records.
2.187. VuControlActivityRecord
Information, stored in a vehicle unit, related to a control performed using this VU (Annex 1B requirement 102 and Annex 1C requirement 126).
|
|
Generation 1:  Text of image
Text of image
controlType is the type of the control. controlTime is the date and time of the control. controlCardNumber identifies the control card used for the control. downloadPeriodBeginTime is the begin time of the downloaded period, in case of downloading. downloadPeriodEndTime is the end time of the downloaded period, in case of downloading. |
|
|
Generation 2: 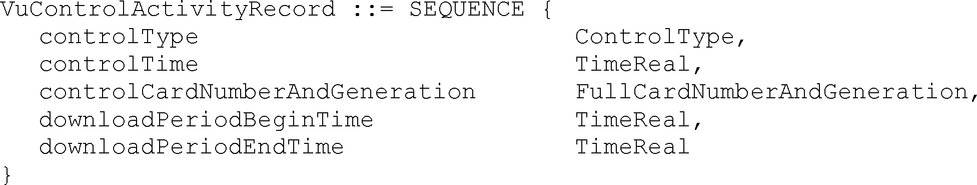 Text of image
Text of image
Instead of controlCardNumber the generation 2 data structure makes use of the following data element. controlCardNumberAndGeneration identifies the control card including its generation used for the control. |
2.188. VuControlActivityRecordArray
Generation 2:
Information, stored in a vehicle unit, related to controls performed using this VU (Annex 1C requirement 126).
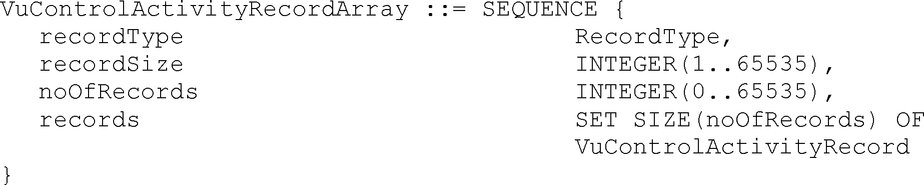
recordType denotes the type of the record (VuControlActivityRecord). Value Assignment: See RecordType
recordSize is the size of the VuControlActivityRecord in bytes.
noOfRecords is the number of records in the set records.
records is the set of VU control activity records.
2.189. VuDataBlockCounter
Counter, stored in a card, identifying sequentially the insertion withdrawal cycles of the card in vehicle units.
![]()
Value assignment: Consecutive Number with max, value 9 999, starting again with 0.
2.190. VuDetailedSpeedBlock
Information, stored in a vehicle unit, related to the vehicle's detailed speed for a minute during which the vehicle has been moving (Annnex 1B requirement 093 and Annex 1C requirement 116).

speedBlockBeginDate is the date and time of the first speed value within the block.
speedsPerSecond is the chronological sequence of measured speeds every seconds for the minute starting at speedBlockBeginDate (included).
2.191. VuDetailedSpeedBlockRecordArray
Generation 2:
Information, stored in a vehicle unit, related to the detailed speed of the vehicle.

recordType denotes the type of the record (VuDetailedSpeedBlock). Value Assignment: See RecordType
recordSize is the size of the VuDetailedSpeedBlock in bytes.
noOfRecords is the number of records in the set records.
records is the set of detailed speed blocks.
2.192. VuDetailedSpeedData
Generation 1:
Information, stored in a vehicle unit, related to the detailed speed of the vehicle.

noOfSpeedBlocks is the number of speed blocks in the vuDetailedSpeedBlocks set.
vuDetailedSpeedBlocks is the set of detailed speed blocks.
2.193. VuDownloadablePeriod
Oldest and latest dates for which a vehicle unit holds data related to drivers activities (Annex 1B requirements 081, 084 or 087 and Annex 1C requirements 102, 105, 108).

minDownloadableTime is the oldest card insertion or activity change or place entry date and time stored in the VU.
maxDownloadableTime is the latest card withdrawal or activity change or place entry date and time stored in the VU.
2.194. VuDownloadablePeriodRecordArray
Generation 2:
The VUDownloadablePeriod plus metadata used in the download protocol.

recordType denotes the type of the record (VuDownloadablePeriod). Value Assignment: See RecordType
recordSize is the size of the VuDownloadablePeriod in bytes.
noOfRecords is the number of records in the set records.
records is the set of VuDownloadablePeriod records.
2.195. VuDownloadActivityData
Information, stored in a vehicle unit, related to its last download (Annex 1B requirement 105 and Annex 1C requirement 129).
|
|
Generation 1:  Text of image
Text of image
downloadingTime is the date and time of downloading. fullCardNumber identifies the card used to authorise the download. companyOrWorkshopName is the company or workshop name. |
|
|
Generation 2:  Text of image
Text of image
Instead of fullCardNumber the generation 2 data structure makes use of the following data element. fullCardNumberAndGeneration identifies the card including its generation used to authorise the download. |
2.196. VuDownloadActivityDataRecordArray
Generation 2:
Information related to the last VU download (Annex 1C requirement 129).
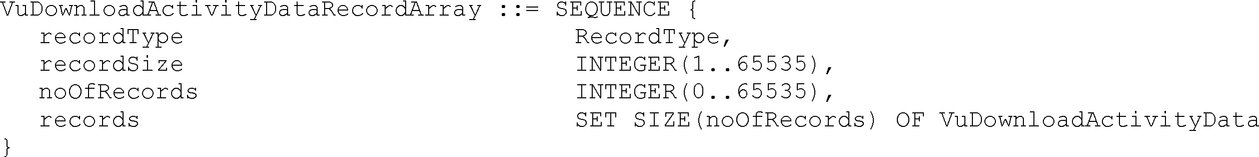
recordType denotes the type of the record (VuDownloadActivityData). Value Assignment: See RecordType
recordSize is the size of the VuDownloadActivityData in bytes.
noOfRecords is the number of records in the set records.
records is the set of download activity data records.
2.197. VuEventData
Generation 1:
Information, stored in a vehicle unit, related to events (Annex 1B requirement 094 except over speeding event).

noOfVuEvents is the number of events listed in the vuEventRecords set.
vuEventRecords is a set of events records.
2.198. VuEventRecord
Information, stored in a vehicle unit, related to an event (Annex 1B requirement 094 and Annex 1C requirement 117 except over speeding event).
|
|
Generation 1:  Text of image
Text of image
eventType is the type of the event. eventRecordPurpose is the purpose for which this event has been recorded. eventBeginTime is the date and time of beginning of event. eventEndTime is the date and time of end of event. cardNumberDriverSlotBegin identifies the card inserted in the driver slot at the beginning of the event. cardNumberCodriverSlotBegin identifies the card inserted in the co-driver slot at the beginning of the event. cardNumberDriverSlotEnd identifies the card inserted in the driver slot at the end of the event. cardNumberCodriverSlotEnd identifies the card inserted in the co-driver slot at the end of the event. similarEventsNumber is the number of similar events that day. This sequence can be used for all events other than over speeding events. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data elements are used: manufacturerSpecificEventFaultData contains additional, manufacturer specific information about the event. Instead of cardNumberDriverSlotBegin, cardNumberCodriverSlotBegin, cardNumberDriverSlotEnd, and cardNumberCodriverSlotEnd the generation 2 data structure makes use of the following data elements:
If the event is a time conflict the eventBeginTime and eventEndTime are to be interpreted as follows:
|
2.199. VuEventRecordArray
Generation 2:
Information, stored in a vehicle unit, related to events (Annex 1C requirement 117 except over speeding event).

recordType denotes the type of the record (VuEventRecord). Value Assignment: See RecordType
recordSize is the size of the VuEventRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of events records.
2.200. VuFaultData
Generation 1:
Information, stored in a vehicle unit, related to faults (Annex 1B requirement 096).

noOfVuFaults is the number of faults listed in the vuFaultRecords set.
vuFaultRecords is a set of faults records.
2.201. VuFaultRecord
Information, stored in a vehicle unit, related to a fault (Annex 1B requirement 096 and Annex 1C requirement 118).
|
|
Generation 1:  Text of image
Text of image
faultType is the type of recording equipment fault. faultRecordPurpose is the purpose for which this fault has been recorded. faultBeginTime is the date and time of beginning of fault. faultEndTime is the date and time of end of fault. cardNumberDriverSlotBegin identifies the card inserted in the driver slot at the beginning of the fault. cardNumberCodriverSlotBegin identifies the card inserted in the co-driver slot at the beginning of the fault. cardNumberDriverSlotEnd identifies the card inserted in the driver slot at the end of the fault. cardNumberCodriverSlotEnd identifies the card inserted in the co-driver slot at the end of the fault. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data element is used: manufacturerSpecificEventFaultData contains additional, manufacturer specific information about the fault. Instead of cardNumberDriverSlotBegin, cardNumberCodriverSlotBegin, cardNumberDriverSlotEnd, and cardNumberCodriverSlotEnd the generation 2 data structure makes use of the following data elements:
|
2.202. VuFaultRecordArray
Generation 2:
Information, stored in a vehicle unit, related to faults (Annex 1C requirement 118).

recordType denotes the type of the record (VuFaultRecord). Value Assignment: See RecordType
recordSize is the size of the VuFaultRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of faults records.
2.203. VuGNSSCDRecord
Generation 2:
Information, stored in a vehicle unit, related to the GNSS position of the vehicle if the continuous driving time of the driver reaches a multiple of three hours (Annex 1C requirement 108, 110).

timeStamp is the date and time when the continuous driving time of the card holder reaches a multiple of three hours.
cardNumberAndGenDriverSlot identifies the card including its generation which is inserted in the driver slot.
cardNumberAndGenCodriverSlot identifies the card including its generation which is inserted in the co-driver slot.
gnssPlaceRecord contains information related to the position of the vehicle.
2.204. VuGNSSCDRecordArray
Generation 2:
Information, stored in a vehicle unit, related to the GNSS position of the vehicle if the continuous driving time of the driver reaches a multiple of three hours (Annex 1C requirement 108 and 110).

recordType denotes the type of the record (VuGNSSCDRecord). Value Assignment: See RecordType
recordSize is the size of the VuGNSSCDRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of GNSS continuous driving records.
2.205. VuIdentification
Information, stored in a vehicle unit, related to the identification of the vehicle unit (Annex 1B requirement 075 and Annex 1C requirement 93 and 121).
|
|
Generation 1:  Text of image
Text of image
vuManufacturerName is the name of the manufacturer of the vehicle unit. vuManufacturerAddress is the address of the manufacturer of the vehicle unit. vuPartNumber is the part number of the vehicle unit. vuSerialNumber is the serial number of the vehicle unit. vuSoftwareIdentification identifies the software implemented in the vehicle unit. vuManufacturingDate is the manufacturing date of the vehicle unit. vuApprovalNumber is the type approval number of the vehicle unit. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data element are used:
|
2.206. VuIdentificationRecordArray
Generation 2:
The VuIdentification plus metadata used in the download protocol.

recordType denotes the type of the record (VuIdentification). Value Assignment: See RecordType
recordSize is the size of the VuIdentification in bytes.
noOfRecords is the number of records in the set records.
records is a set of VuIdentification records.
2.207. VuITSConsentRecord
Generation 2:
Information stored in a vehicle unit, related to the consent of a driver to use Intelligent Transport Systems.

cardNumberAndGen identifies the card including its generation. This must be a driver card or a workshop card.
consent is a flag which indicates whether the driver has given his consent on the usage of Intelligent Transport Systems with this vehicle / vehicle unit.
Value assignment:
|
TRUE |
indicates the driver's consent to use Intelligent Transport Systems |
|
FALSE |
indicates the driver's denial to use Intelligent Transport Systems |
2.208. VuITSConsentRecordArray
Generation 2:
Information, stored in a vehicle unit, related to drivers' consent on the usage of Intelligent Transport Systems (Annex 1C requirement 200).

recordType denotes the type of the record (VuITSConsentRecord). Value Assignment: See RecordType
recordSize is the size of the VuITSConsentRecord in bytes.
noOfRecords is the number of records in the set records.
records is the set of ITS consent records.
2.209. VuManufacturerAddress
Address of the manufacturer of the vehicle unit.
![]()
Value assignment: Unspecified.
2.210. VuManufacturerName
Name of the manufacturer of the vehicle unit.
![]()
Value assignment: Unspecified.
2.211. VuManufacturingDate
Date of manufacture of the vehicle unit.
![]()
Value assignment: Unspecified.
2.212. VuOverSpeedingControlData
Information, stored in a vehicle unit, related to over speeding events since the last over speeding control (Annex 1B requirement 095 and Annex 1C requirement 117).

lastOverspeedControlTime is the date and time of the last over speeding control.
firstOverspeedSince is the date and time of the first over speeding following this over speeding control.
numberOfOverspeedSince is the number of over speeding events since the last over speeding control.
2.213. VuOverSpeedingControlDataRecordArray
Generation 2:
The VuOverSpeedingControlData plus metadata used in the download protocol.

recordType denotes the type of the record (VuOverSpeedingControlData). Value Assignment: See RecordType
recordSize is the size of the VuOverSpeedingControlData in bytes.
noOfRecords is the number of records in the set records.
records is a set of over speeding control data records.
2.214. VuOverSpeedingEventData
Generation 1:
Information, stored in a vehicle unit, related to over speeding events (Annex 1B requirement 094).

noOfVuOverSpeedingEvents is the number of events listed in the vuOverSpeedingEventRecords set.
vuOverSpeedingEventRecords is a set of over speeding events records.
2.215. VuOverSpeedingEventRecord
|
|
Generation 1: Information, stored in a vehicle unit, related to over speeding events (Annex 1B requirement 094 and Annex 1C requirement 117).  Text of image
Text of image
eventType is the type of the event. eventRecordPurpose is the purpose for which this event has been recorded. eventBeginTime is the date and time of beginning of event. eventEndTime is the date and time of end of event. maxSpeedValue is the maximum speed measured during the event. averageSpeedValue is the arithmetic average speed measured during the event. cardNumberDriverSlotBegin identifies the card inserted in the driver slot at the beginning of the event. similarEventsNumber is the number of similar events that day. |
|
|
Generation 2: Information, stored in a vehicle unit, related to over speeding events (Annex 1B requirement 094 and Annex 1C requirement 117).  Text of image
Text of image
Instead of cardNumberDriverSlotBegin, the generation 2 data structure makes use of the following data element: cardNumberAndGenDriverSlotBegin identifies the card including its generation which is inserted in the driver slot at the beginning of the event. |
2.216. VuOverSpeedingEventRecordArray
Generation 2:
Information, stored in a vehicle unit, related to over speeding events (Annex 1C requirement 117).

recordType denotes the type of the record (VuOverSpeedingEventRecord). Value Assignment: See RecordType
recordSize is the size of the VuOverSpeedingEventRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of over speeding events records.
2.217. VuPartNumber
Part number of the vehicle unit.
![]()
Value assignment: VU manufacturer specific.
2.218. VuPlaceDailyWorkPeriodData
Generation 1:
Information, stored in a vehicle unit, related to places where drivers begin or end a daily work period (Annex 1B requirement 087 and Annex 1C requirement 108 and 110).

noOfPlaceRecords is the number of records listed in the vuPlaceDailyWorkPeriodRecords set.
vuPlaceDailyWorkPeriodRecords is a set of place related records.
2.219. VuPlaceDailyWorkPeriodRecord
|
|
Generation 1: Information, stored in a vehicle unit, related to a place where a driver begins or ends a daily work period (Annex 1B requirement 087 and Annex 1C requirement 108 and 110).  Text of image
Text of image
fullCardNumber is the driver's card type, card issuing Member State and card number. placeRecord contains the information related to the place entered. |
|
|
Generation 2: Information, stored in a vehicle unit, related to a place where a driver begins or ends a daily work period (Annex 1B requirement 087 and Annex 1C requirement 108 and 110).  Text of image
Text of image
Instead of fullCardNumber, the generation 2 data structure makes use of the following data element: fullCardNumberAndGeneration is the type of card, its issuing Member State, its card number and generation as stored in the card. |
2.220. VuPlaceDailyWorkPeriodRecordArray
Generation 2:
Information, stored in a vehicle unit, related to places where drivers begin or end a daily work period (Annex 1C requirement 108 and 110).

recordType denotes the type of the record (VuPlaceDailyWorkPeriodRecord). Value Assignment: See RecordType
recordSize is the size of the VuPlaceDailyWorkPeriodRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of place related records.
2.221. VuPrivateKey
Generation 1:
The private key of a vehicle unit.
![]()
2.222. VuPublicKey
Generation 1:
The public key of a vehicle unit.
![]()
2.223. VuSerialNumber
Serial number of the vehicle unit (Annex 1B requirement 075 and Annex 1C requirement 93).
![]()
2.224. VuSoftInstallationDate
Date of installation of the vehicle unit software version.
![]()
Value assignment: Unspecified.
2.225. VuSoftwareIdentification
Information, stored in a vehicle unit, related to the software installed.

vuSoftwareVersion is the software version number of the Vehicle Unit.
vuSoftInstallationDate is the software version installation date.
2.226. VuSoftwareVersion
Software version number of the vehicle unit.
![]()
Value assignment: Unspecified.
2.227. VuSpecificConditionData
Generation 1:
Information, stored in a vehicle unit, related to specific conditions.

noOfSpecificConditionRecords is the number of records listed in the specificConditionRecords set.
specificConditionRecords is a set of specific conditions related records.
2.228. VuSpecificConditionRecordArray
Generation 2:
Information, stored in a vehicle unit, related to specific conditions (Annex 1C requirement 130).

recordType denotes the type of the record (SpecificConditionRecord). Value Assignment: See RecordType
recordSize is the size of the SpecificConditionRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of specific conditions related records.
2.229. VuTimeAdjustmentData
Generation 1:
Information, stored in a vehicle unit, related to time adjustments performed outside the frame of a regular calibration (Annex 1B requirement 101).

noOfVuTimeAdjRecords is the number of records in vuTimeAdjustmentRecords.
vuTimeAdjustmentRecords is a set of time adjustment records.
2.230. VuTimeAdjustmentGNSSRecord
Generation 2:
Information, stored in a vehicle unit, related to a time adjustment based on time data from GNSS (Annex 1C requirement 124 and 125).

oldTimeValue, newTimeValue are the old and new values of date and time.
2.231. VuTimeAdjustmentGNSSRecordArray
Generation 2:
Information, stored in a vehicle unit, related to to a time adjustment performed bybased on time data from GNSS (Annex 1C requirement 124 and 125).

recordType denotes the type of the record (VuTimeAdjustmentGNSSRecord). Value Assignment: See RecordType
recordSize is the size of the VuTimeAdjustmentGNSSRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of GNSS time adjustment records.
2.232. VuTimeAdjustmentRecord
Information, stored in a vehicle unit, related a time adjustment performed outside the frame of a regular calibration (Annex 1B requirement 101 and Annex 1C requirement 124 and 125).
|
|
Generation 1:  Text of image
Text of image
oldTimeValue, newTimeValue are the old and new values of date and time. workshopName, workshopAddress are the workshop name and address. workshopCardNumber identifies the workshop card used to perform the time adjustment. |
|
|
Generation 2: 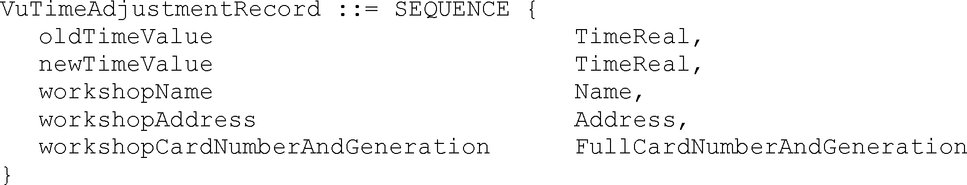 Text of image
Text of image
Instead of workshopCardNumber the generation 2 data structure makes use of the following data element. workshopCardNumberAndGeneration identifies the workshop card including its generation used to perform the time adjustment. |
2.233. VuTimeAdjustmentRecordArray
Generation 2:
Information, stored in a vehicle unit, related to time adjustments performed outside the frame of a regular calibration (Annex 1C requirement 124 and 125).
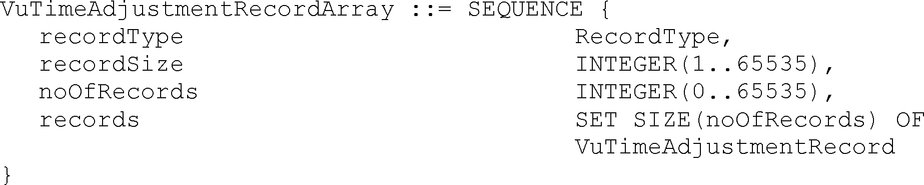
recordType denotes the type of the record (VuTimeAdjustmentRecord). Value Assignment: See RecordType
recordSize is the size of the VuTimeAdjustmentRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of time adjustment records.
2.234. WorkshopCardApplicationIdentification
Information, stored in a workshop card related to the identification of the application of the card (Annex 1C requirement 307 and 330).
|
|
Generation 1:  Text of image
Text of image
typeOfTachographCardId is specifying the implemented type of card. cardStructureVersion is specifying the the version of the structure that is implemented in the card. noOfEventsPerType is the number of events per type of event the card can record. noOfFaultsPerType is the number of faults per type of fault the card can record. activityStructureLength indicates the number of bytes available for storing activity records. noOfCardVehicleRecords is the number of vehicle records the card can contain. noOfCardPlaceRecords is the number of places the card can record. noOfCalibrationRecords is the number of calibration records the card can store. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data elements are used:
|
2.235. WorkshopCardCalibrationData
Information, stored in a workshop card, related to workshop activity performed with the card (Annex 1C requirements 314, 316, 337, and 339).

calibrationTotalNumber is the total number of calibrations performed with the card.
calibrationPointerNewestRecord is the index of the last updated calibration record.
Value assignment: Number corresponding to the numerator of the calibration record, beginning with ‘0’ for the first occurrence of the calibration records in the structure.
calibrationRecords is the set of records containing calibration and/or time adjustment information.
2.236. WorkshopCardCalibrationRecord
Information, stored in a workshop card, related to a calibration performed with the card (Annex 1C requirement 314 and 337).
|
|
Generation 1:  Text of image
Text of image
calibrationPurpose is the purpose of the calibration. vehicleIdentificationNumber is the VIN. vehicleRegistration contains the VRN and registering Member State. wVehicleCharacteristicConstant is the characteristic coefficient of the vehicle. kConstantOfRecordingEquipment is the constant of the recording equipment. lTyreCircumference is the effective circumference of the wheel tyres. tyreSize is the designation of the dimensions of the tyres mounted on the vehicle. authorisedSpeed is the maximum authorised speed of the vehicle. oldOdometerValue, newOdometerValue are the old and new values of the odometer. oldTimeValue, newTimeValue are the old and new values of date and time. nextCalibrationDate is the date of the next calibration of the type specified in CalibrationPurpose to be carried out by the authorised inspection authority. vuPartNumber, vuSerialNumber and sensorSerialNumber are the data elements for recording equipment identification. |
|
|
Generation 2:  Text of image
Text of image
In addition to generation 1 the following data elements are used:
|
2.237. WorkshopCardHolderIdentification
Information, stored in a workshop card, related to the identification of the cardholder (Annex 1C requirement 311 and 334).

workshopName is name of the workshop of the card holder.
workshopAddress is the address of the workshop of the card holder.
cardHolderName is the name and first name(s) of the holder (e.g. the name of the mechanic).
cardHolderPreferredLanguage is the preferred language of the card holder.
2.238. WorkshopCardPIN
Personal identification number of the Workshop Card (Annex 1C requirement 309 and 332).
![]()
Value assignment: The PIN known to the cardholder, right padded with ‘FF’ bytes up to 8 bytes.
2.239. W-VehicleCharacteristicConstant
Characteristic coefficient of the vehicle (definition k)).

Value assignment: Impulses per kilometer in the operating range 0 to 64 255 pulses/km.
2.240. VuPowerSupplyInterruptionRecord
Generation 2:
Information, stored in a vehicle unit, related to Power Supply Interruption events (Annex 1C requirement 117).

eventType is the type of the event.
eventRecordPurpose is the purpose for which this event has been recorded.
eventBeginTime is the date and time of beginning of event.
eventEndTime is the date and time of end of event.
cardNumberAndGenDriverSlotBegin identifies the card including its generation inserted in the driver slot at the beginning of the event.
cardNumberAndGenDriverSlotEnd identifies the card including its generation inserted in the driver slot at the end of the event.
cardNumberAndGenCodriverSlotBegin identifies the card including its generation inserted in the co-driver slot at the beginning of the event.
cardNumberAndGenCodriverSlotEnd identifies the card including its generation inserted in the co-driver slot at the end of the event.
similarEventsNumber is the number of similar events that day.
2.241. VuPowerSupplyInterruptionRecordArray
Generation 2:
Information, stored in a vehicle unit, related to Power Supply Interruption events (Annex 1C requirement 117).

recordType denotes the type of the record (VuPowerSupplyInterruptionRecord). Value Assignment: See RecordType
recordSize is the size of the VuPowerSupplyInterruptionRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of power supply interruption events records.
2.242. VuSensorExternalGNSSCoupledRecordArray
Generation 2:
A set of SensorExternalGNSSCoupledRecord plus metadata used in the download protocol.

recordType denotes the type of the record (SensorExternalGNSSCoupledRecord). Value Assignment: See RecordType
recordSize is the size of the SensorExternalGNSSCoupledRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of Sensor External GNSS Coupled records.
2.243. VuSensorPairedRecordArray
Generation 2:
A set of SensorPairedRecord plus metadata used in the download protocol.

recordType denotes the type of the record (SensorPairedRecord). Value Assignment: See RecordType
recordSize is the size of the SensorPairedRecord in bytes.
noOfRecords is the number of records in the set records.
records is a set of sensor paired records.
3. VALUE AND SIZE RANGE DEFINITIONS
Definition of variable values used for definitions in paragraph 2.
![]()
4. CHARACTER SETS
IA5Strings use the ASCII characters as defined by ISO/IEC 8824-1. For readability and for easy referencing the value assignment is given below. The ISO/IEC 8824-1 supersedes this informative note in case of discrepancy.
![]()
|
Other character strings (Address, Name, VehicleRegistrationNumber) use, in addition, characters from the decimal character code range 161 — 255 of the following 8-bit, standard character sets, specified by the Code Page number: Standard Character Set |
Code Page (Decimal) |
|
ISO/IEC 8859-1 Latin-1 Western European |
1 |
|
ISO/IEC 8859-2 Latin-2 Central European |
2 |
|
ISO/IEC 8859-3 Latin-3 South European |
3 |
|
ISO/IEC 8859-5 Latin / Cyrillic |
5 |
|
ISO/IEC 8859-7 Latin / Greek |
7 |
|
ISO/IEC 8859-9 Latin-5 Turkish |
9 |
|
ISO/IEC 8859-13 Latin-7 Baltic Rim |
13 |
|
ISO/IEC 8859-15 Latin-9 |
15 |
|
ISO/IEC 8859-16 Latin-10 South Eastern European |
16 |
|
KOI8-R Latin / Cyrillic |
80 |
|
KOI8-U Latin / Cyrillic |
85 |
5. ENCODING
When encoded with ASN.1 encoding rules, all data types defined shall be encoded according to ISO/IEC 8825-2, aligned variant.
6. OBJECT IDENTIFIERS UND APPLICATION IDENTIFIERS
6.1. Object Identifiers
The Object Identifiers (OIDs) listed in this chapter are only relevant for generation 2. These OIDs are specified in TR-03110-3 and repeated here for the sake of completeness. These OIDs are contained in the subtree of bsi-de:

VU Authentication protocol identifiers

|
|
Dot notation |
Byte notation |
|
|
|
‘04 00 7F 00 07 02 02 02 02 03’ |
|
|
|
‘04 00 7F 00 07 02 02 02 02 04’ |
|
|
|
‘04 00 7F 00 07 02 02 02 02 05’ |
Chip Authentication protocol identifiers

|
|
Dot notation |
Byte notation |
|
|
|
‘04 00 7F 00 07 02 02 03 02 02’ |
|
|
|
‘04 00 7F 00 07 02 02 03 02 03’ |
|
|
|
‘04 00 7F 00 07 02 02 03 02 04’ |
6.2. Application Identifiers
Generation 2:
The Application Identifier (AID) for the External GNSS Facility (Generation 2) is given by ‘FF 44 54 45 47 4D’. This is a proprietary AID according to ISO/IEC 7816-4.
Note: The last 5 bytes encode DTEGM for smart Tachograph External GNSS Facility.
The Application Identifier for the generation 2 tachograph card application is given by ‘FF 53 4D 52 44 54’. This is a proprietary AID according to ISO/IEC 7816-4.
Appendix 2
TACHOGRAPH CARDS SPECIFICATION
TABLE OF CONTENT
|
1. |
INTRODUCTION | 175 |
|
1.1. |
Abbreviations | 175 |
|
1.2. |
References | 176 |
|
2. |
ELECTRICAL AND PHYSICAL CHARACTERISTICS | 176 |
|
2.1. |
Supply Voltage and Current Consumption | 177 |
|
2.2. |
Programming Voltage Vpp | 177 |
|
2.3. |
Clock generation and Frequency | 177 |
|
2.4. |
I/O Contact | 177 |
|
2.5. |
States of the Card | 177 |
|
3. |
HARDWARE AND COMMUNICATION | 177 |
|
3.1. |
Introduction | 177 |
|
3.2. |
Transmission Protocol | 178 |
|
3.2.1 |
Protocols | 178 |
|
3.2.2 |
ATR | 179 |
|
3.2.3 |
PTS | 179 |
|
3.3. |
Access Rules | 180 |
|
3.4. |
Commands and error codes overview | 183 |
|
3.5. |
Command descriptions | 185 |
|
3.5.1 |
SELECT | 186 |
|
3.5.2 |
READ BINARY | 187 |
|
3.5.3 |
UPDATE BINARY | 194 |
|
3.5.4 |
GET CHALLENGE | 200 |
|
3.5.5 |
VERIFY | 200 |
|
3.5.6 |
GET RESPONSE | 202 |
|
3.5.7 |
PSO: VERIFY CERTIFICATE | 202 |
|
3.5.8 |
INTERNAL AUTHENTICATE | 204 |
|
3.5.9 |
EXTERNAL AUTHENTICATE | 205 |
|
3.5.10 |
GENERAL AUTHENTICATE | 206 |
|
3.5.11 |
MANAGE SECURITY ENVIRONMENT | 207 |
|
3.5.12 |
PSO: HASH | 210 |
|
3.5.13 |
PERFORM HASH OF FILE | 211 |
|
3.5.14 |
PSO: COMPUTE DIGITAL SIGNATURE | 212 |
|
3.5.15 |
PSO: VERIFY DIGITAL SIGNATURE | 213 |
|
3.5.16 |
PROCESS DSRC MESSAGE | 214 |
|
4. |
TACHOGRAPH CARDS STRUCTURE | 216 |
|
4.1. |
Master File MF | 216 |
|
4.2. |
Driver card applications | 217 |
|
4.2.1 |
Driver card application generation 1 | 217 |
|
4.2.2 |
Driver card application generation 2 | 221 |
|
4.3. |
Workshop card applications | 224 |
|
4.3.1 |
Workshop card application generation 1 | 224 |
|
4.3.2 |
Workshop card application generation 2 | 228 |
|
4.4. |
Control card applications | 233 |
|
4.4.1 |
Control Card application generation 1 | 233 |
|
4.4.2 |
Control card application generation 2 | 235 |
|
4.5. |
Company card applications | 237 |
|
4.5.1 |
Company card application generation 1 | 237 |
|
4.5.2 |
Company card application generation 2 | 238 |
1. INTRODUCTION
1.1. Abbreviations
For the purpose of this appendix, the following abbreviations apply.
|
AC |
Access conditions |
|
AES |
Advanced Encryption Standard |
|
AID |
Application Identifier |
|
ALW |
Always |
|
APDU |
Application Protocol Data Unit (structure of a command) |
|
ATR |
Answer To Reset |
|
AUT |
Authenticated. |
|
C6, C7 |
Contacts No 6 and 7 of the card as described in ISO/IEC 7816-2 |
|
cc |
clock cycles |
|
CHV |
Card holder Verification Information |
|
CLA |
Class byte of an APDU command |
|
DSRC |
Dedicated Short Range Communication |
|
DF |
Dedicated File. A DF can contain other files (EF or DF) |
|
ECC |
Elliptic Curve Cryptography |
|
EF |
Elementary File |
|
etu |
elementary time unit |
|
G1 |
Generation 1 |
|
G2 |
Generation 2 |
|
IC |
Integrated Circuit |
|
ICC |
Integrated Circuit Card |
|
ID |
Identifier |
|
IFD |
Interface Device |
|
IFS |
Information Field Size |
|
IFSC |
Information Field Size for the card |
|
IFSD |
Information Field Size Device (for the Terminal) |
|
INS |
Instruction byte of an APDU command |
|
Lc |
Length of the input data for a APDU command |
|
Le |
Length of the expected data (output data for a command) |
|
MF |
Master File (root DF) |
|
NAD |
Node Address used in T=1 protocol |
|
NEV |
Never |
|
P1-P2 |
Parameter bytes |
|
PIN |
Personal Identification Number |
|
PRO SM |
Protected with secure messaging |
|
PTS |
Protocol Transmission Selection |
|
RFU |
Reserved for Future Use |
|
RST |
Reset (of the card) |
|
SFID |
Short EF Identifier |
|
SM |
Secure Messaging |
|
SW1-SW2 |
Status bytes |
|
TS |
Initial ATR character |
|
VPP |
Programming Voltage |
|
VU |
Vehicle Unit |
|
XXh |
Value XX in hexadecimal notation |
|
‘XXh’ |
Value XX in hexadecimal notation |
|
|| |
Concatenation symbol 03||04=0304 |
1.2. References
The following references are used in this Appendix:
|
ISO/IEC 7816-2 |
Identification cards — Integrated circuit cards — Part 2: Dimensions and location of the contacts. ISO/IEC 7816-2:2007. |
|
ISO/IEC 7816-3 |
Identification cards — Integrated circuit cards — Part 3: Electrical interface and transmission protocols. ISO/IEC 7816-3:2006. |
|
ISO/IEC 7816-4 |
Identification cards — Integrated circuit cards — Part 4: Organization, security and commands for interchange. ISO/IEC 7816-4:2013 + Cor 1: 2014. |
|
ISO/IEC 7816-6 |
Identification cards — Integrated circuit cards — Part 6: Interindustry data elements for interchange. ISO/IEC 7816-6:2004 + Cor 1: 2006. |
|
ISO/IEC 7816-8 |
Identification cards — Integrated circuit cards — Part 8: Commands for security operations. ISO/IEC 7816-8:2004. |
|
ISO/IEC 9797-2 |
Information technology — Security techniques — Message Authentication Codes (MACs) — Part 2: Mechanisms using a dedicated hash-function. ISO/IEC 9797-2:2011 |
2. ELECTRICAL AND PHYSICAL CHARACTERISTICS
|
TCS_01 |
All electronic signals shall be in accordance with ISO/IEC 7816-3 unless specified otherwise. |
|
TCS_02 |
The location and dimensions of the card contacts shall comply with the ISO/IEC 7816-2. |
2.1. Supply Voltage and Current Consumption
|
TCS_03 |
The card shall work according to specifications within the consumption limits specified in ISO/IEC 7816-3. |
|
TCS_04 |
The card shall work with Vcc = 3V (± 0,3V) or with Vcc = 5V (± 0,5V). Voltage selection shall be performed according to ISO/IEC 7816-3. |
2.2. Programming Voltage Vpp
|
TCS_05 |
The card shall not require a programming voltage at pin C6. It is expected that pin C6 is not connected in an IFD. Contact C6 may be connected to Vcc in the card but shall not be connected to ground. This voltage should not be interpreted in any case. |
2.3. Clock generation and Frequency
|
TCS_06 |
The card shall operate within a frequency range of 1 to 5 MHz and may support higher frequencies. Within one card session the clock frequency may vary ± 2 %. The clock frequency is generated by the Vehicle Unit and not the card itself. The duty cycle may vary between 40 and 60 %. |
|
TCS_07 |
Under conditions contained into the card file EF ICC, the external clock can be stopped. The first byte of the EF ICC file body codes the Clockstop mode conditions:
Bits 4 to 8 are not used. |
2.4. I/O Contact
|
TCS_08 |
The I/O contact C7 is used to receive data from and to transmit data to the IFD. During operation only either the card or the IFD shall be in transmit mode. Should both units be in transmit mode no damage shall occur to the card. Unless transmitting, the card shall enter the reception mode. |
2.5. States of the Card
|
TCS_09 |
The card works in two states while the supply voltage is applied:
|
3. HARDWARE AND COMMUNICATION
3.1. Introduction
This paragraph describes the minimum functionality required by Tachograph cards and VUs to ensure correct operation and interoperability.
Tachograph cards are as compliant as possible with the available ISO/IEC applicable norms (especially ISO/IEC 7816). However, commands and protocols are fully described in order to specify some restricted usage or some differences if they exist. The commands specified are fully compliant with the referred norms except where indicated.
3.2. Transmission Protocol
|
TCS_10 |
The Transmission protocol shall be compliant with ISO/IEC 7816-3 for T = 0 and T = 1. In particular, the VU shall recognise waiting time extensions sent by the card. |
3.2.1 Protocols
|
TCS_11 |
The card shall provide both protocol T=0 and protocol T=1. In addition the card may support further contact-oriented protocols. |
|
TCS_12 |
T=0 is the default protocol, a PTS command is therefore necessary to change the protocol to T=1. |
|
TCS_13 |
Devices shall support direct convention in both protocols: the direct convention is hence mandatory for the card. |
|
TCS_14 |
The Information Field Size Card byte shall be presented at the ATR in character TA3. This value shall be at least ‘F0h’ (=240 bytes). |
The following restrictions apply to the protocols:
|
TCS_15 |
T=0
|
|
TCS_16 |
T=1
|
3.2.2 ATR
|
TCS_17 |
The device checks ATR bytes, according to ISO/IEC 7816-3. No verification shall be done on ATR Historical Characters. Example of Basic Biprotocol ATR according to ISO/IEC 7816-3
|
|
TCS_18 |
After the Answer To Reset (ATR), the Master File (MF) is implicitly selected and becomes the Current Directory. |
3.2.3 PTS
|
TCS_19 |
The default Protocol is T=0. To set the T=1 protocol, a PTS (also known as PPS) must be sent to the card by the device. |
|
TCS_20 |
As both T=0 and T=1 protocols are mandatory for the card, the basic PTS for protocol switching is mandatory for the card. The PTS can be used, as indicated in ISO/IEC 7816-3, to switch to higher baud rates than the default one proposed by the card in the ATR if any (TA(1) byte). Higher baud rates are optional for the card. |
|
TCS_21 |
If no other baud rate than the default one are supported (or if the selected baud rate is not supported), the card shall respond to the PTS correctly according to ISO/IEC 7816-3 by omitting the PPS1 byte. Examples of basic PTS for protocol selection are the following:
|
3.3. Access Rules
|
TCS_22 |
An access rule specifies for an access mode, i.e. command, the corresponding security conditions. If these security conditions are fulfilled the corresponding command is processed. |
|
TCS_23 |
The following security conditions are used for the tachograph card:
|
|
TCS_24 |
These security conditions can be linked in the following ways: AND : All security conditions must be fulfilled OR : At least one security condition must be fulfilled The access rules for the file system, i.e. the SELECT, READ BINARY and UPDATE BINARY command, are specified in chapter 4. The access rules for the remaining commands are specified in the following tables. |
|
TCS_25 |
In the DF Tachograph G1 application the following access rules are used:
|
|
TCS_26 |
In the DF Tachograph_G2 application the following access rules are used:
|
|
TCS_27 |
In the MF the following access rules are used:
|
|
TCS_28 |
A tachograph card may or may not accept a command with a higher level of security than the one specified in the security conditions. I.e. if the security condition is ALW (or PLAIN-C) the card may accept a command with secure messaging (encryption and / or authentication mode). If the security condition requires secure messaging with authentication mode, the tachograph card may accept a command with secure messaging of the same generation in authentication and encryption mode. Note: The command descriptions provide more information on the support of the commands for the different tachograph card types and the different DFs. |
3.4. Commands and error codes overview
Commands and file organisation are deduced from and complies with ISO/IEC 7816-4.
This section describes the following APDU command-response pairs. The command variants which are supported by a generation 1 and 2 application are specified in the corresponding command descriptions.
|
Command |
INS |
||
|
SELECT |
‘A4h’ |
||
|
READ BINARY |
‘B0h’, ‘B1h’ |
||
|
UPDATE BINARY |
‘D6h’, ‘D7h’ |
||
|
GET CHALLENGE |
‘84h’ |
||
|
VERIFY |
‘20h’ |
||
|
GET RESPONSE |
‘C0h’ |
||
|
PERFORM SECURITY OPERATION |
‘2Ah’ |
||
|
|
||
|
|
||
|
|
||
|
|
||
|
|
||
|
|
||
|
INTERNAL AUTHENTICATE |
‘88h’ |
||
|
EXTERNAL AUTHENTICATE |
‘82h’ |
||
|
MANAGE SECURITY ENVIRONMENT |
‘22h’ |
||
|
|
||
|
|
||
|
GENERAL AUTHENTICATE |
‘86h’ |
|
TCS_29 |
The status words SW1 SW2 are returned in any response message and denote the processing state of the command.
|
|
TCS_30 |
If more than one error condition is fulfilled in one command APDU the card may return any of the appropriate status words. |
3.5. Command descriptions
The mandatory commands for the Tachograph cards are described in this chapter.
Additional relevant details, related to cryptographic operations involved, are given in Appendix 11 Common security mechanisms for Tachograph Generation 1 and Generation 2.
All commands are described independently of the used protocol (T=0 or T=1). The APDU bytes CLA, INS, P1, P2, Lc and Le are always indicated. If Lc or Le is not needed for the described command, the associated length, value and description are empty.
|
TCS_31 |
If both length bytes (Lc and Le) are requested, the described command has to be split in two parts if the IFD is using protocol T=0: the IFD sends the command as described with P3=Lc + data and then sends a GET RESPONSE (see § 3.5.6) command with P3=Le. |
|
TCS_32 |
If both length bytes are requested, and Le=0 (secure messaging):
|
|
TCS_33 |
A tachograph card may support extended length fields according to ISO/IEC 7816-4 as an optional feature. A tachograph card that supports extended length fields shall
Notes: All commands are specified for short length fields. The usage of extended length APDUs is clear from ISO/IEC 7816-4. In general the commands are specified for the plain mode, i.e. without secure messaging, as the secure messaging layer is specified in Appendix 11. It is clear from the access rules for a command whether the command shall support secure messaging or not and whether the command shall support generation 1 and / or generation 2 secure messaging. Some command variants are described with secure messaging to illustrate the usage of secure messaging. |
|
TCS_34 |
The VU shall perform the complete generation 2 VU — card mutual authentication protocol for a session including the certificate verification (if required) either in the DF Tachograph, the DF Tachograph_G2 or the MF. |
3.5.1 SELECT
This command is compliant with ISO/IEC 7816-4, but has a restricted usage compared to the command defined in the norm.
The SELECT command is used:
|
— |
to select an application DF (selection by name must be used) |
|
— |
to select an elementary file corresponding to the submitted file ID |
3.5.1.1
This command allows selecting an application DF in the card.
|
TCS_35 |
This command can be performed from anywhere in the file structure (after the ATR or at any time). |
|
TCS_36 |
The selection of an application resets the current security environment. After performing the application selection, no current public key is selected anymore. The EXT-AUT-G1 access condition is also lost. If the command was performed without secure messaging, the former secure messaging session keys are no longer available. |
|
TCS_37 |
Command Message
No response to the SELECT command is needed (Le absent in T=1, or no response asked in T=0). |
|
TCS_38 |
Response Message (no response asked)
|
3.5.1.2
|
TCS_39 |
Command Message |
|
TCS_40 |
A tachograph card shall support the generation 2 secure messaging as specified in Appendix 11 Part B for this command variant.
No response to the SELECT command is needed (Le absent in T=1, or no response asked in T=0). |
|
TCS_41 |
Response Message (no response asked)
|
3.5.2 READ BINARY
This command is compliant with ISO/IEC 7816-4, but has a restricted usage compared to the command defined in the norm.
The READ BINARY command is used to read data from a transparent file.
The response of the card consists of returning the data read, optionally encapsulated in a secure messaging structure.
3.5.2.1
This command enables the IFD to read data from the EF currently selected, without secure messaging.
Note: This command without secure messaging can only be used to read a file that supports the ALW security condition for the Read access mode.
|
TCS_42 |
Command Message
Note: bit 8 of P1 must be set to 0. |
|
TCS_43 |
Response Message
|
3.5.2.1.1
This command enables the IFD to read data from the EF currently selected with secure messaging, in order to verify the integrity of the data received and to protect the confidentiality of the data if the security condition SM-R-ENC-MAC-G1 (generation 1) or SM-R-ENC-MAC-G2 (generation 2) is applied.
|
TCS_44 |
Command Message
|
|
TCS_45 |
Response Message if SM-R-ENC-MAC-G1 (generation 1) / SM-R-ENC-MAC-G2 (generation 2) is not required and if Secure Messaging input format is correct:
|
|
TCS_46 |
Response Message if SM-R-ENC-MAC-G1 (generation 1) / SM-R-ENC-MAC-G2 (generation 2) is required and if Secure Messaging input format is correct:
The READ BINARY command may return regular processing states listed in TCS_43 under Tag ‘99h’ as described in TCS_59 using the secure messaging response structure. Additionally, some errors specifically related to secure messaging can happen. In that case, the processing state is simply returned, with no secure messaging structure involved: |
|
TCS_47 |
Response Message if incorrect Secure Messaging input format
|
3.5.2.2
This command variant enables the IFD to select an EF by means of a short EF identifier and read data from this EF.
|
TCS_48 |
A tachograph card shall support this command variant for all Elementary Files with a specified short EF identifier. These short EF identifiers are specified in chapter 4. |
|
TCS_49 |
Command Message
Note: The short EF identifiers used for the Generation 2 tachograph application are specified in chapter 4. If P1 encodes a short EF identifier and the command is successful, the identified EF becomes the currently selected EF (current EF). |
|
TCS_50 |
Response Message
|
3.5.2.3
This command variant enables the IFD to read data from an EF with 32 768 bytes or more.
|
TCS_51 |
A tachograph card which supports EFs with 32 768 bytes or more shall support this command variant for these EFs. A tachograph card may or may not support this command variant for other EFs with the exception of the EF Sensor_Installation_Data see TCS_156 and TCS_160. |
|
TCS_52 |
Command Message
The IFD shall encode the offset data object's length with a minimum possible number of octets, i.e. using the length byte ‘01h’ the IFD shall encode an offset from 0 to 255 and using the length byte ‘02h’ an offset from ‘256’ up to ‘65 535’ bytes. |
|
TCS_53 |
Response Message
|
3.5.2.3.1
The following example illustrates the usage of secure messaging if the security condition SM-MAC-G2 applies.
|
TCS_54 |
Command message
|
|
TCS_55 |
Response message if the command is successful
|
3.5.3 UPDATE BINARY
This command is compliant with ISO/IEC 7816-4, but has a restricted usage compared to the command defined in the norm.
The UPDATE BINARY command message initiates the update (erase + write) of the bits already present in an EF binary with the bits given in the command APDU.
3.5.3.1
This command enables the IFD to write data into the EF currently selected, without the card verifying the integrity of data received.
Note: This command without secure messaging can only be used to update a file that supports the ALW security condition for the Update access mode.
|
TCS_56 |
Command Message
Note: bit 8 of P1 must be set to 0. |
|
TCS_57 |
Response Message
|
3.5.3.1.1
This command enables the IFD to write data into the EF currently selected, with the card verifying the integrity of data received. As no confidentiality is required, the data are not encrypted.
|
TCS_58 |
Command Message
|
|
TCS_59 |
Response message if correct Secure Messaging input format
The ‘regular’ processing states, described for the UPDATE BINARY command with no secure messaging (see §3.5.3.1), can be returned using the response message structure described above. Additionally, some errors specifically related to secure messaging can happen. In that case, the processing state is simply returned, with no secure messaging structure involved: |
|
TCS_60 |
Response Message if error in secure messaging
|
3.5.3.2
This command variant enables the IFD to select an EF by means of a short EF identifier and write data from this EF.
|
TCS_61 |
A tachograph card shall support this command variant for all Elementary Files with a specified short EF identifier. These short EF identifiers are specified in chapter 4. |
|
TCS_62 |
Command Message
|
|
TCS_63 |
Response Message
Note: The short EF identifiers used for the generation 2 tachograph application are specified in chapter 4. If P1 encodes a short EF identifier and the command is successful, the identified EF becomes the currently selected EF (current EF).
|
3.5.3.3
This command variant enables the IFD to write data to an EF with 32 768 bytes or more.
|
TCS_64 |
A tachograph card which supports EFs with 32 768 bytes or more shall support this command variant for these EFs. A tachograph card may or may not support this command variant for other EFs. |
|
TCS_65 |
Command Message
The IFD shall encode the offset data object's and the discretionary data object's length with the minimum possible number of octets, i.e. using the length byte ‘01h’ the IFD shall encode an offset / length from 0 to 255 and using the length byte ‘02h’ an offset / length from ‘256’ up to ‘65 535’ bytes. |
|
TCS_66 |
Response Message
|
3.5.3.3.1
The following example illustrates the usage of secure messaging if the security condition SM-MAC-G2 applies.
|
TCS_67 |
Command message
|
|
TCS_68 |
Response message if the command is successful
|
3.5.4 GET CHALLENGE
This command is compliant with ISO/IEC 7816-4, but has a restricted usage compared to the command defined in the norm.
The GET CHALLENGE command asks the card to issue a challenge in order to use it in a security related procedure in which a cryptogram or some ciphered data are sent to the card.
|
TCS_69 |
The Challenge issued by the card is only valid for the next command, which uses a challenge, sent to the card. |
|
TCS_70 |
Command Message
|
|
TCS_71 |
Response Message
|
3.5.5 VERIFY
This command is compliant with ISO/IEC 7816-4, but has a restricted usage compared to the command defined in the norm.
Only the workshop card is required to support this command.
Other types of tachograph cards may or may not implement this command, but for these cards no reference CHV is personalized. Therefore these cards cannot perform this commend successfully. For other types of tachograph cards than workshop cards the behavior, i.e. the error code returned, is out of the scope of this specification, if this command is sent.
The Verify command initiates the comparison in the card of the CHV (PIN) data sent from the command with the reference CHV stored in the card.
|
TCS_72 |
The PIN entered by the user must be ASCI encoded and right padded with ‘FFh’ bytes up to a length of 8 bytes by the IFD, see also the data type WorkshopCardPIN in Appendix 1. |
|
TCS_73 |
The tachograph applications generation 1 and 2 shall use the same reference CHV. |
|
TCS_74 |
The tachograph card shall check whether the command is encoded correctly. If the command is not encoded correctly the card shall not compare the CHV values, not decrement the remaining CHV attempt counter and not reset the security status ‘PIN_Verified’, but abort the command. A command is encoded correctly, if the CLA, INS, P1, P2, Lc bytes have the specified values, Le is absent, and the command data field has the correct length. |
|
TCS_75 |
If the command is successful, the remaining CHV attempt counter is reinitialised. The initial value of the remaining CHV attempt counter is 5. If the command is successful the card shall set the internal security status ‘PIN_Verified’. The card shall reset this security status, if the card is reset or if the CHV code transmitted in the command does not match the stored reference CHV. Note: Using the same reference CHV and a global security status prevents that a workshop employee must re-enter the PIN after a selection of another tachograph application DF. |
|
TCS_76 |
An unsuccessful comparison is recorded in the card, i.e. the remaining CHV attempts counter shall be decremented by one, in order to limit the number of further attempts of the use of the reference CHV. |
|
TCS_77 |
Command Message
|
|
TCS_78 |
Response Message
|
3.5.6 GET RESPONSE
This command is compliant with ISO/IEC 7816-4.
This command (only necessary and available for T=0 Protocol) is used to transmit prepared data from the card to the interface device (case where a command had included both Lc and Le).
The GET RESPONSE command has to be issued immediately after the command preparing the data, otherwise, the data are lost. After the execution of the GET RESPONSE command (except if the error ‘61xx’ or ‘6Cxx’ occur, see below), the previously prepared data are no longer available.
|
TCS_79 |
Command Message
|
|
TCS_80 |
Response Message
|
3.5.7 PSO: VERIFY CERTIFICATE
This command is compliant with ISO/IEC 7816-8, but has a restricted usage compared to the command defined in the norm.
The VERIFY CERTIFICATE command is used by the card to obtain a Public Key from the outside and to check its validity.
3.5.7.1
|
TCS_81 |
This command variant is only supported by a generation 1 tachograph application. |
|
TCS_82 |
When a VERIFY CERTIFICATE command is successful, the Public Key is stored for a future use in the Security environment. This key shall be explicitly set for the use in security related commands (INTERNAL AUTHENTICATE, EXTERNAL AUTHENTICATE or VERIFY CERTIFICATE) by the MSE command (see § 3.5.11) using its key identifier. |
|
TCS_83 |
In any case, the VERIFY CERTIFICATE command uses the public key previously selected by the MSE command to open the certificate. This public key must be the one of a Member State or of Europe. |
|
TCS_84 |
Command Message
|
|
TCS_85 |
Response Message
|
3.5.7.2
Depending on the curve size ECC certificates may be so long that they cannot be transmitted in a single APDU. In this case command chaining according to ISO/IEC 7816-4 must be applied and the certificate transmitted in two consecutive PSO: Verify Certificate APDUs.
The certificate structure and the domain parameters are defined in Appendix 11.
|
TCS_86 |
The command can be performed in the MF, DF Tachograph and DF Tachograph_G2, see also TCS_33. |
|
TCS_87 |
Command Message
|
|
TCS_88 |
For short length APDUs the following provisions apply: The IFD shall use the minimum number of APDUs required to transmit the command payload and transmit the maximum number of bytes in the first command APDU according to the value of the Information Field Size Card Byte, see TCS_14. If the IFD behaves differently, the behavior of the card is out of scope. |
|
TCS_89 |
For extended length APDUs the following provisions apply: If the certificate does not fit into a single APDU, the card shall support command chaining. The IFD shall use the minimum number of APDUs required to transmit the command payload and transmit the maximum number of bytes in the first command APDU. If the IFD behaves differently, the behavior of the card is out of scope. Note: According to Appendix 11 the card stores the certificate or the relevant contents of the certificate and updates its currentAuthenticatedTime. The response message structure and status words are as defined in TCS_85. |
|
TCS_90 |
In addition to the error codes listed in TCS_85, the card may return the following error codes:
|
3.5.8 INTERNAL AUTHENTICATE
This command is compliant with ISO/IEC 7816-4.
|
TCS_91 |
All tachograph cards shall support this command in the DF Tachograph generation 1. The command may or may not be accessible in the MF and / or the DF Tachograph_G2. If so, the command shall terminate with a suitable error code as the private key of the card (Card.SK) for the generation 1 authentication protocol is only accessible in the DF_Tachograph generation 1. |
Using the INTERNAL AUTHENTICATE command, the IFD can authenticate the card. The authentication process is described in Appendix 11. It includes the following statements:
|
TCS_92 |
The INTERNAL AUTHENTICATE command uses the card Private Key (implicitly selected) to sign authentication data including K1 (first element for session key agreement) and RND1, and uses the Public Key currently selected (through the last MSE command) to encrypt the signature and form the authentication token (more details in Appendix 11). |
|
TCS_93 |
Command Message
|
|
TCS_94 |
Response Message
|
|
TCS_95 |
If the INTERNAL AUTHENTICATE command is successful, the current session key, if existing, is erased and no longer available. In order to have a new session key available, the EXTERNAL AUTHENTICATE command for the generation 1 authentication mechanism must be successfully performed. |
3.5.9 EXTERNAL AUTHENTICATE
This command is compliant with ISO/IEC 7816-4.
Using the EXTERNAL AUTHENTICATE command, the card can authenticate the IFD. The authentication process is described in Appendix 11 for Tachograph G1 and G2 (VU authentication).
|
TCS_96 |
The command variant for the generation 1 mutual authentication mechanism is only supported by a generation 1 tachograph application. |
|
TCS_97 |
The command variant for the second generation VU-card mutual authentication can be performed in the MF, DF Tachograph and DF Tachograph_G2, see also TCS_34. |
|
TCS_98 |
Command Message
|
|
TCS_99 |
Response Message
The Generation 1 Tachograph application may return the following additional error codes:
The command variant for the Generation 2 authentication may return the following additional error code:
|
3.5.10 GENERAL AUTHENTICATE
This command is used for the generation 2 chip authentication protocol specified in Appendix 11 Part B and is compliant with ISO/IEC 7816-4.
|
TCS_100 |
The command can be performed in the MF, DF Tachograph and DF Tachograph_G2, see also TCS_34. |
|
TCS_101 |
Command Message
|
|
TCS_102 |
Response Message
The response Dynamic Authentication Data object ‘7Ch’
|
3.5.11 MANAGE SECURITY ENVIRONMENT
This command is used to set a public key for authentication purpose.
3.5.11.1
This command is compliant with ISO/IEC 7816-4. The use of this command is restricted regarding the related standard.
|
TCS_103 |
This command is only supported by a generation 1 tachograph application. |
|
TCS_104 |
The key referenced in the MSE data field remains the current public key until the next correct MSE command, a DF is selected or the card is reset. |
|
TCS_105 |
If the key referenced is not (already) present into the card, the security environment remains unchanged. |
|
TCS_106 |
Command Message
|
|
TCS_107 |
Response Message
|
3.5.11.2
For the Generation 2 authentication the tachograph card supports the following MSE: Set command versions which are compliant with ISO/IEC 7816-4. These command versions are not supported for the Generation 1 authentication.
3.5.11.2.1
The following MSE:SET AT command is used to select the parameters for the Chip Authentication that is performed by a subsequent General Authenticate command.
|
TCS_108 |
The command can be performed in the MF, DF Tachograph and DF Tachograph_G2, see also TCS_34. |
|
TCS_109 |
MSE:SET AT Command Message for Chip Authentication
|
3.5.11.2.2
The following MSE:SET AT command is used to select the parameters and keys for the VU Authentication that is performed by a subsequent External Authenticate command.
|
TCS_110 |
The command can be performed in the MF, DF Tachograph and DF Tachograph_G2, see also TCS_34. |
|
TCS_111 |
MSE:SET AT Command Message for VU Authentication
|
3.5.11.2.3
The following MSE:SET DST command is used to set a public key either
|
— |
for the verification of a signature that is provided in a subsequent PSO: Verify Digital Signature command or |
|
— |
for the signature verification of a certificate that is provided in a subsequent PSO: Verify Certificate command |
|
TCS_112 |
The command can be performed in the MF, DF Tachograph and DF Tachograph_G2, see also TCS_33. |
|
TCS_113 |
MSE:SET DST Command Message
|
For all command versions the response message structure and status words are given by:
|
TCS_114 |
Response Message
|
3.5.12 PSO: HASH
This command is used to transfer to the card the result of a hash calculation on some data. This command is used for the verification of digital signatures. The hash value is stored temporarily for the subsequent command PSO: Verify Digital Signature
This command is compliant with ISO/IEC 7816-8. The use of this command is restricted regarding the related standard.
Only the control card is required to support this command in the DF Tachograph and DF Tachograph_G2.
Other types of tachograph cards may or may not implement this command. The command may or may not be accessible in the MF.
The control card application generation 1 supports only SHA-1.
|
TCS_115 |
The temporarily stored hash value shall be deleted if a new hash value is computed by means of the PSO: HASH command, if a DF is selected, and if the tachograph card is reset. |
|
TCS_116 |
Command Message
|
|
TCS_117 |
Response Message
|
3.5.13 PERFORM HASH of FILE
This command is not compliant with ISO/IEC 7816-8. Thus the CLA byte of this command indicates that there is a proprietary use of the PERFORM SECURITY OPERATION / HASH.
Only the driver card and the workshop card are required to support this command in the DF Tachograph and DF Tachograph_G2.
Other types of tachograph cards may or may not implement this command. If a company or control card implements this command, the command shall be implemented as specified in this chapter.
The command may or may not be accessible in the MF. If so, the command shall be implemented as specified in this chapter, i.e. shall not allow the calculation of a hash value, but terminate with a suitable error code.
|
TCS_118 |
The PERFORM HASH of FILE command is used to hash the data area of the currently selected transparent EF. |
|
TCS_119 |
A tachograph card shall support this command only for the EFs that are listed in chapter 4 under the DF_Tachograph and DF_Tachograph_G2 with the following exception. A tachograph card shall not support the command for the EF Sensor_Installation_Data of DF Tachograph_G2.. |
|
TCS_120 |
The result of the hash operation is stored temporarily in the card. It can then be used to get a digital signature of the file, using the PSO: COMPUTE DIGITAL SIGNATURE command. |
|
TCS_121 |
The temporarily stored hash of file value shall be deleted if a new hash of file value is computed by means of the PSO: Hash of File command, if a DF is selected, and if the tachograph card is reset. |
|
TCS_122 |
The Tachograph Generation 1 application shall support SHA-1. |
|
TCS_123 |
The Tachograph Generation 2 application shall support SHA-1 and SHA-2 (256, 384 and 512 bits). |
|
TCS_124 |
Command Message
|
|
TCS_125 |
Response Message
|
3.5.14 PSO: COMPUTE DIGITAL SIGNATURE
This command is used to compute the digital signature of previously computed hash code (see PERFORM HASH of FILE, §3.5.13).
Only the driver card and the workshop card are required to support this command in the DF Tachograph and DF Tachograph_G2.
Other types of tachograph cards may or may not implement this command, but shall not have a signature key. Therefore these cards cannot perform the command successfully, but terminate with a suitable error code.
The command may or may not be accessible in the MF. If so, the command shall terminate with a suitable error code.
This command is compliant with ISO/IEC 7816-8. The use of this command is restricted regarding the related standard.
|
TCS_126 |
This command shall not compute a digital signature of previously computed hash code with the PSO: HASH command. |
|
TCS_127 |
The card private key is used to compute the digital signature and is implicitly known by the card. |
|
TCS_128 |
The Generation 1 tachograph application performs a digital signature using a padding method compliant with PKCS1 (see Appendix 11 for details). |
|
TCS_129 |
The Generation 2 tachograph application computes an elliptic curve based digital signature (see Appendix 11 for details). |
|
TCS_130 |
Command Message
|
|
TCS_131 |
Response Message
|
3.5.15 PSO: VERIFY DIGITAL SIGNATURE
This command is used to verify the digital signature, provided as an input, whose hash is known to the card. The signature algorithm is implicitly known by the card.
This command is compliant with ISO/IEC 7816-8. The use of this command is restricted regarding the related standard.
Only the control card is required to support this command in the DF Tachograph and DF Tachograph_G2.
Other types of tachograph cards may or may not implement this command. The command may or may not be accessible in the MF.
|
TCS_132 |
The VERIFY DIGITAL SIGNATURE command always uses the public key selected by the previous Manage Security Environment MSE: Set DST command and the previous hash code entered by a PSO: HASH command. |
|
TCS_133 |
Command Message
|
|
TCS_134 |
Response Message
|
3.5.16 PROCESS DSRC MESSAGE
This command is used to verify the integrity and authenticity of the DSRC message and to decipher the data communicated from a VU to a control authority or a workshop over the DSRC link. The card derives the encryption key and the MAC key used to secure the DSRC message as described in Appendix 11 Part B chapter 13.
Only the control card and the workshop card are required to support this command in the DF Tachograph_G2.
Other types of tachograph cards may or may not implement this command, but shall not have a DSRC master key. Therefore these cards cannot perform the command successfully, but terminate with a suitable error code.
The command may or may not be accessible in the MF and / or the DF Tachograph. If so, the command shall terminate with a suitable error code.
|
TCS_135 |
The DSRC master key is accessible only in the DF Tachograph_G2, i.e. the control and workshop card shall support a successful execution of the command only in the DF Tachograph_G2. |
|
TCS_136 |
The command shall only decrypt the DSRC data and verify the cryptographic checksum, but not interpret the input data. |
|
TCS_137 |
The order of the data objects in the command data field is fixed by this specification. |
|
TCS_138 |
Command Message
|
|
TCS_139 |
Response Message
|
4. TACHOGRAPH CARDS STRUCTURE
This paragraph specifies the file structures of the Tachograph cards for storage of accessible data.
It does not specify card manufacturer dependent internal structures, such as e.g. file headers, nor storage and handling of data elements needed for internal use only such as|
TCS_140 |
A generation 2 tachograph card shall host the Master File MF and a generation 1 and a generation 2 tachograph application of the same type (e.g. driver card applications). |
|
TCS_141 |
A tachograph card shall support at least the minimum number of records specified for the corresponding applications and shall not support more records than the maximum number of records specified for the corresponding applications. The maximum and minimum numbers of records are specified in this chapter for the different applications. For the security conditions used in the access rules throughout this chapter please refer to chapter 3.3. In general the access mode ‘read’ denotes the READ BINARY command with even and if supported odd INS byte with the exception of the EF Sensor_Installation_Data on the workshop card, see TCS_156 and TCS_160. The access mode ‘update’ denotes the Update Binary command with even and if supported odd INS byte and the access mode ‘select’ the SELECT command. |
4.1. Master File MF
|
TCS_142 |
After its personalisation, the master file MF shall have the following permanent file structure and file access rules: Note: The short EF identifier SFID is given as decimal number, e.g. the value 30 corresponds to 11110 in binary.  Text of image
Text of image
The following abbreviation for the security condition is used in this table:
|
|
TCS_143 |
All EF structures shall be transparent. |
|
TCS_144 |
The Master File MF shall have the following data structure:  Text of image
Text of image
|
|
TCS_145 |
The elementary file EF DIR shall contain the following application related data objects: ‘61 08 4F 06 FF 54 41 43 48 4F 61 08 4F 06 FF 53 4D 52 44 54’ |
|
TCS_146 |
The elementary file EF ATR/INFO shall be present if the tachograph card indicates in its ATR that it supports extended length fields. In this case the EF ATR/INFO shall contain the extended length information data object (DO‘7F66’) as specified in ISO/IEC 7816-4:2013 clause 12.7.1. |
|
TCS_147 |
The elementary file EF Extended_Length shall be present if the tachograph card indicates in its ATR that it supports extended length fields. In this case the EF shall contain the following data object: ‘02 01 xx’ where the value ‘xx’ indicates whether extended length fields are supported for the T = 1 and / or T = 0 protocol. The value ‘01’ indicates extended length field support for the T = 1 protocol. The value ‘10’ indicates extended length field support for the T = 0 protocol. The value ‘11’ indicates extended length field support for the T = 1 and the T = 0 protocol. |
4.2. Driver card applications
4.2.1 Driver card application generation 1
|
TCS_148 |
After its personalisation, the driver card application generation 1 shall have the following permanent file structure and file access rules:  Text of image
Text of image
The following abbreviations for the security conditions are used in this table:
|
|
TCS_149 |
All EF structures shall be transparent. |
|
TCS_150 |
The driver card application generation 1 shall have the following data structure:  Text of image
Text of image
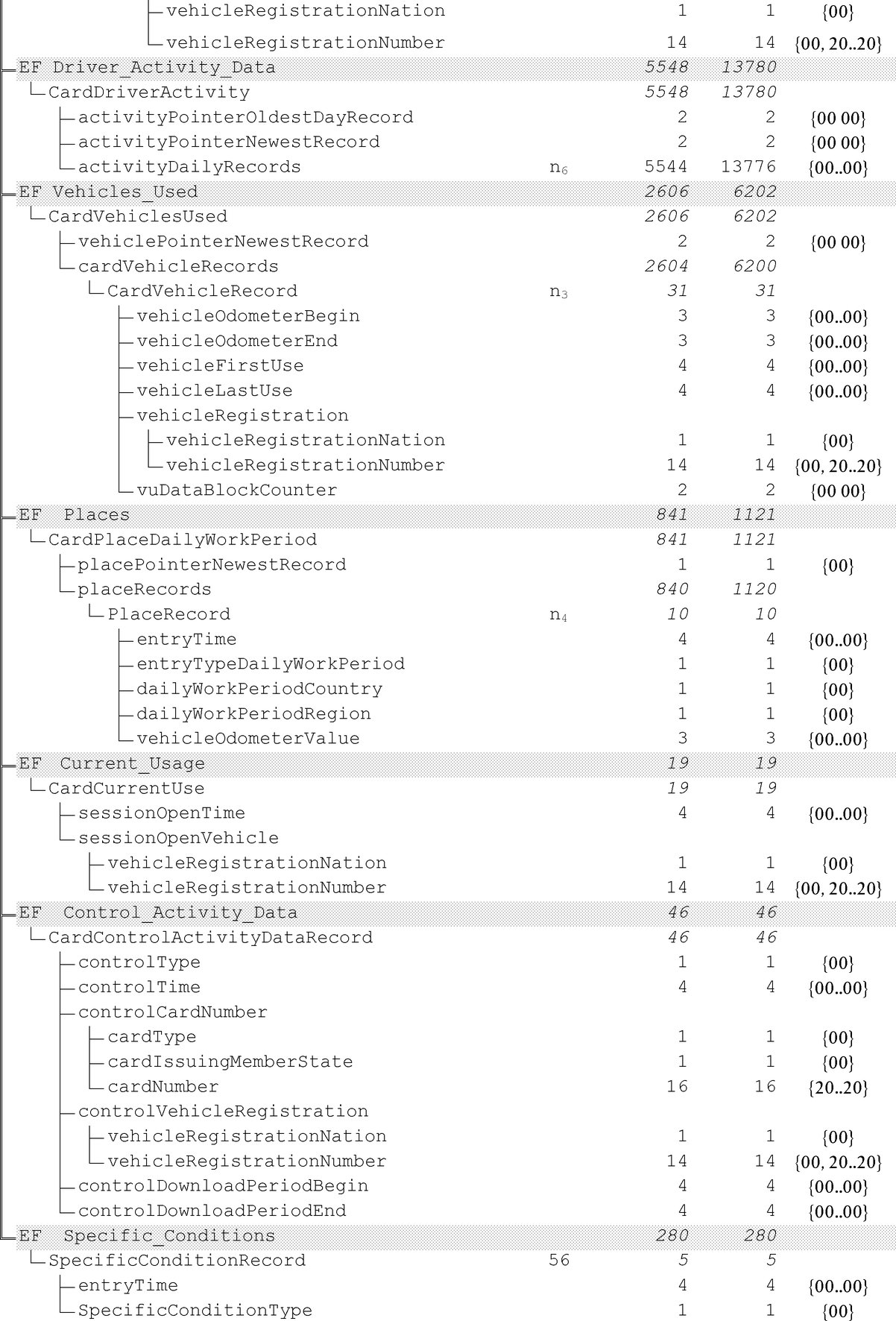 Text of image
Text of image
|
|
TCS_151 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the driver card data structure must use for a generation 1 application:  Text of image
Text of image
|
4.2.2 Driver card application generation 2
|
TCS_152 |
After its personalisation, the driver card application generation 2 shall have the following permanent file structure and file access rules. Note: The short EF identifier SFID is given as decimal number, e.g. the value 30 corresponds to 11110 in binary.  Text of image
Text of image
The following abbreviation for the security condition is used in this table:
|
|
TCS_153 |
All EF structures shall be transparent. |
|
TCS_154 |
The driver card application generation 2 shall have the following data structure:  Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
|
|
TCS_155 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the driver card data structure must use for a generation 2 application:  Text of image
Text of image
|
4.3. Workshop card applications
4.3.1 Workshop card application generation 1
|
TCS_156 |
After its personalisation, the workshop card application generation 1 shall have the following permanent file structure and file access rules:  Text of image
Text of image
The following abbreviations for the security conditions are used in this table:
|
|
TCS_157 |
All EF structures shall be transparent. |
|
TCS_158 |
The workshop card application generation 1 shall have the following data structure:  Text of image
Text of image
 Text of image
Text of image
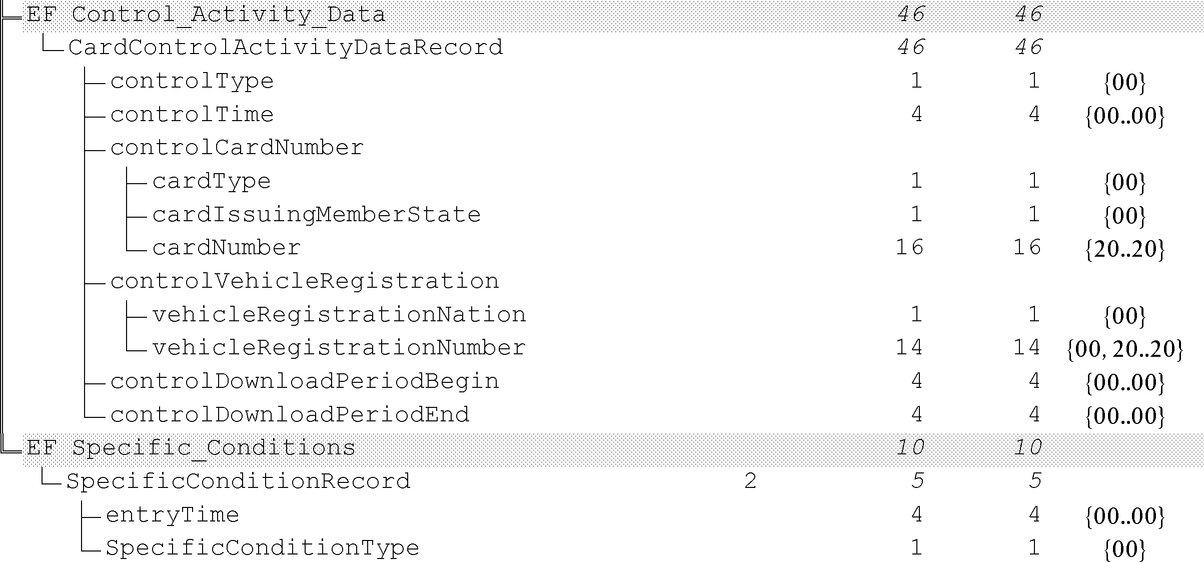 Text of image
Text of image
|
|
TCS_159 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the workshop card data structure must use for a generation 1 application:  Text of image
Text of image
|
4.3.2 Workshop card application generation 2
|
TCS_160 |
After its personalisation, the workshop card application generation 2 shall have the following permanent file structure and file access rules. Note: The short EF identifier SFID is given as decimal number, e.g. the value 30 corresponds to 11110 in binary.  Text of image
Text of image
The following abbreviations for the security conditions are used in this table:
|
|
TCS_161 |
All EFs structures shall be transparent. |
|
TCS_162 |
The workshop card application generation 2 shall have the following data structure:  Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
|
|
TCS_163 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the workshop card data structure must use for a generation 2 application:  Text of image
Text of image
|
4.4. Control card applications
4.4.1 Control Card application generation 1
|
TCS_164 |
After its personalisation, the control card application generation 1 shall have the following permanent file structure and file access rules:  Text of image
Text of image
The following abbreviations for the security conditions are used in this table:
|
|
TCS_165 |
All EF structures shall be transparent. |
|
TCS_166 |
The control card application generation 1 shall have the following data structure:  Text of image
Text of image
|
|
TCS_167 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the control card data structure must use for a generation 1 application: |
4.4.2 Control card application generation 2
|
TCS_168 |
After its personalisation, the control card application generation 2 shall have the following permanent file structure and file access rules. Note: The short EF identifier SFID is given as decimal number, e.g. the value 30 corresponds to 11110 in binary.  Text of image
Text of image
The following abbreviation for the security condition is used in this table:
|
|
TCS_169 |
All EF structures shall be transparent. |
|
TCS_170 |
The control card application generation2 shall have the following data structure:  Text of image
Text of image
|
|
TCS_171 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the control card data structure must use for a generation 2 application: |
4.5. Company card applications
4.5.1 Company card application generation 1
|
TCS_172 |
After its personalisation, the company card application generation 1 shall have the following permanent file structure and file access rules:  Text of image
Text of image
The following abbreviations for the security conditions are used in this table:
|
|
TCS_173 |
All EF structures shall be transparent. |
|
TCS_174 |
The company card application generation 1 shall have the following data structure:  Text of image
Text of image
|
|
TCS_175 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the company card data structure must use for a generation 1 application: |
4.5.2 Company card application generation 2
|
TCS_176 |
After its personalisation, the company card application generation 2 shall have the following permanent file structure and file access rules. Note: The short EF identifier SFID is given as decimal number, e.g. the value 30 corresponds to 11110 in binary.  Text of image
Text of image
The following abbreviation for the security condition is used in this table:
|
|
TCS_177 |
All EF structures shall be transparent. |
|
TCS_178 |
The company card application generation 2 shall have the following data structure:  Text of image
Text of image
|
|
TCS_179 |
The following values, used to provide sizes in the table above, are the minimum and maximum record number values the company card data structure must use for a generation 2 application: |
Appendix 3
PICTOGRAMS
|
PIC_001 |
The tachograph may optionally use the following pictograms and pictogram combinations (or pictograms and combination similar enough to be unambiguously identifiable with these):
Note: Additional pictogram combinations to form printout blocks or record identifiers are defined in Appendix 4. |
Appendix 4
PRINTOUTS
TABLE OF CONTENT
|
1. |
GENERALITIES | 243 |
|
2. |
DATA BLOCKS SPECIFICATION | 243 |
|
3. |
PRINTOUT SPECIFICATIONS | 250 |
|
3.1. |
Driver Activities from Card Daily Printout | 250 |
|
3.2. |
Driver Activities from VU Daily Printout | 251 |
|
3.3. |
Events and Faults from Card Printout | 252 |
|
3.4. |
Events and Faults from VU Printout | 252 |
|
3.5. |
Technical data Printout | 253 |
|
3.6. |
Over speeding Printout | 253 |
|
3.7 |
History of inserted cards | 254 |
1. GENERALITIES
Each printout is built up by chaining various data blocks, possibly identified with a block identifier.
A data block contains one or more records, possibly identified with a record identifier.
|
PRT_001 |
When a block identifier immediately precedes a record identifier, the record identifier is not printed. |
|
PRT_002 |
In the case where a data item is unknown, or must not be printed for data access rights reasons, spaces are printed instead. |
|
PRT_003 |
If the content of a complete line is unknown, or need not to be printed, then the complete line is omitted. |
|
PRT_004 |
Numerical data fields are printed right aligned, with a space separator for thousands and millions, and without leading zeros. |
|
PRT_005 |
String data fields are printed left aligned and filled up with spaces to data item length, or truncated to data item length when needed (names and addresses). |
|
PRT_006 |
In case of a line-break due to a long text a special character (dot at middle line-height, ‘ߦ’) should be printed as first character in the new line. |
2. DATA BLOCKS SPECIFICATION
In this chapter the following format notation conventions have been used:
|
— |
Characters printed in bold denote plain text to be printed (printing remains in normal characters), |
|
— |
Normal characters denote variables (pictograms or data) to be replaced by their values for printing, |
|
— |
Variable names have been padded with underscores to show the data item length available for the variable, |
|
— |
Dates are specified with a ‘dd/mm/yyyy’ (day, month, year) format. A ‘dd.mm.yyyy’ format may also be used, |
|
— |
The term ‘card identification’ denotes the composition of: the type of card through a card pictograms combination, the card issuing Member State code, a forward slash character and the card number with the replacement index and the renewal index separated with a space:
|
||||||||||||||||||||||||||||||||||||||||||||||||
|
PRT_007 |
Printouts shall use the following data blocks and/or data records, in accordance with the following meanings and formats:  Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
 Text of image
Text of image
|
3. PRINTOUT SPECIFICATIONS
In this chapter the following notation conventions have been used:
|
N |
Print block or record number N |
|
|
|
|
N |
Print block or record number N repeated as many times as necessary |
|
|
|
|
X/Y |
Print blocks or records X and/or Y as needed, and repeating as many times as necessary. |
3.1. Driver Activities from Card Daily Printout
|
PRT_008 |
The driver activities from card daily printout shall be in accordance with the following format:
|
3.2. Driver Activities from VU Daily Printout
|
PRT_009 |
The driver activities from VU daily printout shall be in accordance with the following format:
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
3.3. Events and Faults from Card Printout
|
PRT_010 |
The events and faults from card printout shall be in accordance with the following format:
|
3.4. Events and Faults from VU Printout
|
PRT_011 |
The events and faults from VU printout shall be in accordance with the following format:
|
3.5. Technical data Printout
|
PRT_012 |
The technical data printout shall be in accordance with the following format:
|
3.6. Over speeding Printout
|
PRT_013 |
The over speeding printout shall be in accordance with the following format:
|
3.7. Historic of inserted cards
|
PRT_014 |
The historic of inserted cards printout shall be in accordance with the following format:
|
Appendix 5
DISPLAY
In this appendix the following format notation conventions have been used:
|
— |
characters printed in bold denote plain text to be displayed (display remains in normal character), |
|
— |
normal characters denote variables (pictograms or data) to be replaced by their values for displaying:
|
|
DIS_001 |
The tachograph shall display data using the following formats:
|
||||||||||||||||||||||||||||||||||
Appendix 6
FRONT CONNECTOR FOR CALIBRATION AND DOWNLOAD
TABLE OF CONTENT
|
1. |
HARDWARE | 256 |
|
1.1. |
Connector | 256 |
|
1.2. |
Contact allocation | 257 |
|
1.3. |
Block diagram | 258 |
|
2. |
DOWNLOADING INTERFACE | 258 |
|
3. |
CALIBRATION INTERFACE | 259 |
1. HARDWARE
1.1. Connector
|
INT_001 |
The downloading/calibration connector shall be a 6 pin connector, accessible on the front panel without the need to disconnect any part of the tachograph, and shall comply with the following drawing (all dimensions in millimetres):
The following diagram shows a typical 6 pin mating plug:
|
1.2. Contact allocation
|
INT_002 |
Contacts shall be allocated in accordance with the following table:
|
1.3. Block diagram
|
INT_003 |
The block diagram shall comply with the following:
|
2. DOWNLOADING INTERFACE
|
INT_004 |
The downloading interface shall comply to RS232 specifications. |
|
INT_005 |
The downloading interface shall use one start bit, 8 data bits LSB first, one even parity bit and 1 stop bit.
|
Data byte organisation
|
Start bit |
: |
one bit with logic level 0; |
|
Data bits |
: |
transmitted with LSB first; |
|
Parity bit |
: |
even parity |
|
Stop bit |
: |
one bit with logic level 1 |
When numerical data composed by more than one byte are transmitted, the most significant byte is transmitted first and the least significant byte last.
|
INT_006 |
Transmission baud rates shall be adjustable from 9 600 bps to 115 200 bps. Transmission shall be achieved at the highest possible transmission speed, the initial baud rate after a start of communication being set at 9 600 bps. |
3. CALIBRATION INTERFACE
|
INT_007 |
The data communication shall comply to ISO 14230-1 Road vehicles — Diagnostic systems — Keyword protocol 2000 — Part 1: Physical layer, First edition: 1999. |
|
INT_008 |
The input/output signal shall comply with the following electrical specification:
|
|
INT_009 |
The input/output signal shall comply with the following timing diagrams:
|
Appendix 7
DATA DOWNLOADING PROTOCOLS
TABLE OF CONTENT
|
1. |
INTRODUCTION | 261 |
|
1.1. |
Scope | 261 |
|
1.2. |
Acronyms and notations | 261 |
|
2. |
V.U. DATA DOWNLOADING | 262 |
|
2.1. |
Download procedure | 262 |
|
2.2. |
Data download protocol | 262 |
|
2.2.1 |
Message structure | 262 |
|
2.2.2 |
Message types | 264 |
|
2.2.2.1 |
Start Communication Request (SID 81) | 266 |
|
2.2.2.2 |
Positive Response Start Communication (SID C1) | 266 |
|
2.2.2.3 |
Start Diagnostic Session Request (SID 10) | 266 |
|
2.2.2.4 |
Positive Response Start Diagnostic (SID 50) | 266 |
|
2.2.2.5 |
Link Control Service (SID 87) | 266 |
|
2.2.2.6 |
Link Control Positive Response (SID C7) | 266 |
|
2.2.2.7 |
Request Upload (SID 35) | 266 |
|
2.2.2.8 |
Positive Response Request Upload (SID 75) | 266 |
|
2.2.2.9 |
Transfer Data Request (SID 36) | 266 |
|
2.2.2.10 |
Positive Response Transfer Data (SID 76) | 267 |
|
2.2.2.11 |
Request Transfer Exit (SID 37) | 267 |
|
2.2.2.12 |
Positive Response Request Transfer Exit (SID 77) | 267 |
|
2.2.2.13 |
Stop Communication Request (SID 82) | 267 |
|
2.2.2.14 |
Positive Response Stop Communication (SID C2) | 267 |
|
2.2.2.15 |
Acknowledge Sub Message (SID 83) | 267 |
|
2.2.2.16 |
Negative Response (SID 7F) | 268 |
|
2.2.3 |
Message flow | 268 |
|
2.2.4 |
Timing | 269 |
|
2.2.5 |
Error handling | 270 |
|
2.2.5.1 |
Start Communication phase | 270 |
|
2.2.5.2 |
Communication phase | 270 |
|
2.2.6 |
Response Message content | 272 |
|
2.2.6.1 |
Positive Response Transfer Data Overview | 273 |
|
2.2.6.2 |
Positive Response Transfer Data Activities | 274 |
|
2.2.6.3 |
Positive Response Transfer Data Events and Faults | 275 |
|
2.2.6.4 |
Positive Response Transfer Data Detailed Speed | 276 |
|
2.2.6.5 |
Positive Response Transfer Data Technical Data | 276 |
|
2.3. |
ESM File storage | 277 |
|
3. |
TACHOGRAPH CARDS DOWNLOADING PROTOCOL | 277 |
|
3.1. |
Scope | 277 |
|
3.2. |
Definitions | 277 |
|
3.3. |
Card Downloading | 277 |
|
3.3.1 |
Initialisation sequence | 278 |
|
3.3.2 |
Sequence for un-signed data files | 278 |
|
3.3.3 |
Sequence for Signed data files | 279 |
|
3.3.4 |
Sequence for resetting the calibration counter. | 279 |
|
3.4. |
Data storage format | 280 |
|
3.4.1 |
Introduction | 280 |
|
3.4.2 |
File format | 280 |
|
4. |
DOWNLOADING A TACHOGRAPH CARD VIA A VEHICLE UNIT. | 281 |
1. INTRODUCTION
This appendix specifies the procedures to follow in order to perform the different types of data download to an External Storage Medium, together with the protocols that must be implemented to assure the correct data transfer and the full compatibility of the downloaded data format to allow any controller to inspect these data and be able to control their authenticity and their integrity before analysing them.
1.1. Scope
Data may be downloaded to an ESM:
|
— |
from a Vehicle Unit by an Intelligent Dedicated Equipment (IDE) connected to the VU, |
|
— |
from a tachograph card by an IDE fitted with a card interface device (IFD), |
|
— |
from a tachograph card via a vehicle unit by an IDE connected to the VU. |
To give the possibility to verify the authenticity and integrity of downloaded data stored on an ESM, data is downloaded with a signature appended in accordance with Appendix 11 Common Security Mechanisms. The source equipment (VU or card) identification and its security certificates (Member state and equipment) are also downloaded. The verifier of the data must possess independently a trusted European public key.
|
DDP_001 |
Data downloaded during one download session must be stored in the ESM within one single file. |
1.2. Acronyms and notations
The following acronyms are used in this appendix:
|
AID |
Application Identifier |
|
ATR |
Answer To Reset |
|
CS |
Checksum byte |
|
DF |
Dedicated File |
|
DS_ |
Diagnostic Session |
|
EF |
Elementary File |
|
ESM |
External Storage Medium |
|
FID |
File Identifier (File ID) |
|
FMT |
Format Byte (first byte of message header) |
|
ICC |
Integrated Circuit Card |
|
IDE |
Intelligent Dedicated Equipment: The equipment used to perform data downloading to the ESM (e.g. Personal Computer) |
|
IFD |
Interface Device |
|
KWP |
Keyword Protocol 2000 |
|
LEN |
Length Byte (last byte of message header) |
|
PPS |
Protocol Parameter Selection |
|
PSO |
Perform Security Operation |
|
SID |
Service Identifier |
|
SRC |
Source byte |
|
TGT |
Target Byte |
|
TLV |
Tag Length Value |
|
TREP |
Transfer Response Parameter |
|
TRTP |
Transfer Request Parameter |
|
VU |
Vehicle Unit |
2. V.U. DATA DOWNLOADING
2.1. Download procedure
In order to carry on a VU data download, the operator must perform the following operations:
|
— |
Insert his tachograph card inside a card slot of the VU (*); |
|
— |
Connect the IDE to the VU download connector; |
|
— |
Establish the connection between the IDE and the VU; |
|
— |
Select on the IDE the data to download and send the request to the VU; |
|
— |
Close the download session. |
2.2. Data download protocol
The protocol is structured on a master-slave basis, with the IDE playing the master role and the VU playing the slave role.
The message structure, types and flow are principally based on the Keyword Protocol 2000 (KWP) (ISO 14230-2 Road vehicles — Diagnostic systems — Keyword protocol 2000 — Part2: Data link layer).
The application layer is principally based on the current draft to date of ISO 14229-1 (Road vehicles — Diagnostic systems — Part 1: Diagnostic services, version 6 of 22 February 2001).
2.2.1 Message structure
|
DDP_002 |
All the messages exchanged between the IDE and the VU are formatted with a structure consisting of three parts:
The TGT and SRC byte represent the physical address of the recipient and originator of the message. Values are F0 Hex for the IDE and EE Hex for the VU. The LEN byte is the length of the Data field part. The Checksum byte is the 8 bit sum series modulo 256 of all the bytes of the message excluding the CS itself. FMT, SID, DS_, TRTP and TREP bytes are defined later in this document. |
|||||||||||||||||||||||||||||||||||||
|
DDP_003 |
In the case where the data to be carried by the message is longer than the space available in the data field part, the message is actually sent in several sub messages. Each sub message bears a header, the same SID, TREP and a 2-byte sub message counter indicating the sub message number within the total message. To enable error checking and abort the IDE acknowledges every sub message. The IDE can accept the sub message, ask for it to be re-transmitted, request the VU to start again or abort the transmission. |
|
DDP_004 |
If the last sub message contains exactly 255 bytes in the data field, a final sub message with an empty (except SID TREP and sub message counter) data field must be appended to show the end of the message. Example:
Will be transmitted as:
…
or as:
…
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
2.2.2 Message types
The communication protocol for data download between the VU and the IDE requires the exchange of 8 different message types.
The following table summarises these messages.
|
Message Structure |
Max 4 Bytes Header |
Max 255 Bytes Data |
1 Byte CheckSum |
||||||
|
IDE -> |
<- VU |
FMT |
TGT |
SRC |
LEN |
SID |
DS_/TRTP |
DATA |
CS |
|
Start Communication Request |
81 |
EE |
F0 |
|
81 |
|
|
E0 |
|
|
Positive Response Start Communication |
80 |
F0 |
EE |
03 |
C1 |
|
EA, 8F |
9B |
|
|
Start Diagnostic Session Request |
80 |
EE |
F0 |
02 |
10 |
81 |
|
F1 |
|
|
Positive Response Start Diagnostic |
80 |
F0 |
EE |
02 |
50 |
81 |
|
31 |
|
|
Link Control Service |
|
||||||||
|
Verify Baud Rate (stage 1) |
|||||||||
|
9 600 Bd |
80 |
EE |
F0 |
04 |
87 |
|
01,01,01 |
EC |
|
|
19 200 Bd |
80 |
EE |
F0 |
04 |
87 |
|
01,01,02 |
ED |
|
|
38 400 Bd |
80 |
EE |
F0 |
04 |
87 |
|
01,01,03 |
EE |
|
|
57 600 Bd |
80 |
EE |
F0 |
04 |
87 |
|
01,01,04 |
EF |
|
|
115 200 Bd |
80 |
EE |
F0 |
04 |
87 |
|
01,01,05 |
F0 |
|
|
Positive Response Verify Baud Rate |
80 |
F0 |
EE |
02 |
C7 |
|
01 |
28 |
|
|
Transition Baud Rate (stage 2) |
80 |
EE |
F0 |
03 |
87 |
|
02,03 |
ED |
|
|
Request Upload |
80 |
EE |
F0 |
0A |
35 |
|
00,00,00,00,00,FF,FF,FF,FF |
99 |
|
|
Positive Response Request Upload |
80 |
F0 |
EE |
03 |
75 |
|
00,FF |
D5 |
|
|
Transfer Data Request |
|
||||||||
|
Overview |
80 |
EE |
F0 |
02 |
36 |
01 |
|
97 |
|
|
Activities |
80 |
EE |
F0 |
06 |
36 |
02 |
Date |
CS |
|
|
Events & Faults |
80 |
EE |
F0 |
02 |
36 |
03 |
|
99 |
|
|
Detailed Speed |
80 |
EE |
F0 |
02 |
36 |
04 |
|
9A |
|
|
Technical Data |
80 |
EE |
F0 |
02 |
36 |
05 |
|
9B |
|
|
Card download |
80 |
EE |
F0 |
02 |
36 |
06 |
Slot |
CS |
|
|
Positive Response Transfer Data |
80 |
F0 |
EE |
Len |
76 |
TREP |
Data |
CS |
|
|
Request Transfer Exit |
80 |
EE |
F0 |
01 |
37 |
|
|
96 |
|
|
Positive Response Request Transfer Exit |
80 |
F0 |
EE |
01 |
77 |
|
|
D6 |
|
|
Stop Communication Request |
80 |
EE |
F0 |
01 |
82 |
|
|
E1 |
|
|
Positive Response Stop Communication |
80 |
F0 |
EE |
01 |
C2 |
|
|
21 |
|
|
Acknowledge sub message |
80 |
EE |
F0 |
Len |
83 |
|
Data |
CS |
|
|
Negative responses |
|
||||||||
|
General reject |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
10 |
CS |
|
|
Service not supported |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
11 |
CS |
|
|
Sub function not supported |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
12 |
CS |
|
|
Incorrect Message Length |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
13 |
CS |
|
|
Conditions not correct or Request sequence error |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
22 |
CS |
|
|
Request out of range |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
31 |
CS |
|
|
Upload not accepted |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
50 |
CS |
|
|
Response pending |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
78 |
CS |
|
|
Data not available |
80 |
F0 |
EE |
03 |
7F |
Sid Req |
FA |
CS |
|
Notes:
|
— |
Sid Req = the Sid of the corresponding request. |
|
— |
TREP = the TRTP of the corresponding request. |
|
— |
Dark cells denote that nothing is transmitted. |
|
— |
The term upload (as seen from the IDE) is used for compatibility with ISO 14229. It means the same as download (as seen from the VU). |
|
— |
Potential 2-byte sub message counters are not shown in this table. |
|
— |
Slot is the slot number, either “1” (card on driver slot) or “2” (card on co-driver slot) |
|
— |
In case the slot is not specified, the VU shall select slot 1 if a card is inserted in this slot and it shall select slot 2 only in case it is specifically selected by the user. |
2.2.2.1
|
DDP_005 |
This message is issued by the IDE to establish the communication link with the VU. Initial communications are always performed at 9 600 baud (until baud rate is eventually changed using the appropriate Link control services). |
2.2.2.2
|
DDP_006 |
This message is issued by the VU to answer positively to a start communication request. It includes the 2 key bytes ‘EA’‘8F’ indicating that the unit supports protocol with header including target source and length information. |
2.2.2.3
|
DDP_007 |
The Start Diagnostic Session request message is issued by the IDE in order to request a new diagnostic session with the VU. The sub function ‘default session’ (81 Hex) indicates a standard diagnostic session is to be opened. |
2.2.2.4
|
DDP_008 |
The Positive Response Start Diagnostic message is sent by the VU to answer positively to Diagnostic Session Request. |
2.2.2.5
|
DDP_052 |
The Link Control Service is used by the IDE to initiate a change in baud rate. This takes place in two steps. In step one the IDE proposes the baud rate change, indicating the new rate. On receipt of a positive message from the VU the IDE sends out confirmation of the baud rate change to the VU (step two). The IDE then changes to the new baud rate. After receipt of the confirmation the VU changes to the new baud rate |
2.2.2.6
|
DDP_053 |
The Link Control Positive Response is issued by the VU to answer positively to Link Control Service request (step one). Note that no response is given to the confirmation request (step two). |
2.2.2.7
|
DDP_009 |
The Request Upload message is issued by the IDE to specify to the VU that a download operation is requested. To meet the requirements of ISO14229 data is included covering address, the size and format details for the data requested. As these are not known to the IDE prior to a download, the memory address is set to 0, format is unencrypted and uncompressed and the memory size is set to the maximum. |
2.2.2.8
|
DDP_010 |
The Positive Response Request Upload message is sent by the VU to indicate to the IDE that the VU is ready to download data. To meet the requirements of ISO 14229 data is included in this positive response message, indicating to the IDE that further Positive Response Transfer Data messages will include 00FF hex bytes maximum. |
2.2.2.9
|
DDP_011 |
The Transfer Data Request is sent by the IDE to specify to the VU the type of data that are to be downloaded. A one byte Transfer Request Parameter (TRTP) indicates the type of transfer. There are six types of data transfer:
|
|
DDP_054 |
It is mandatory for the IDE to request the overview data transfer (TRTP 01) during a download session as this only will ensure that the VU certificates are recorded within the downloaded file (and allow for verification of digital signature). In the second case (TRTP 02) the Transfer Data Request message includes the indication of the calendar day ( |
2.2.2.10
|
DDP_012 |
The Positive Response Transfer Data is sent by the VU in response to the Transfer Data Request. The message contains the requested data, with a Transfer Response Parameter (TREP) corresponding to the TRTP of the request. |
|
DDP055 |
In the first case (TREP 01), the VU will send data helping the IDE operator to choose the data he wants to download further. The information contained within this message is:
|
2.2.2.11
|
DDP_013 |
The Request Transfer Exit message is sent by the IDE to inform the VU that the download session is terminated. |
2.2.2.12
|
DDP_014 |
The Positive Response Request Transfer Exit message is sent by the VU to acknowledge the Request Transfer Exit. |
2.2.2.13
|
DDP_015 |
The Stop Communication Request message is sent by the IDE to disconnect the communication link with the VU. |
2.2.2.14
|
DDP_016 |
The Positive Response Stop Communication message is sent by the VU to acknowledge the Stop Communication Request. |
2.2.2.15
|
DDP_017 |
The Acknowledge Sub Message is sent by the IDE to confirm receipt of each part of a message that is being transmitted as several sub messages. The data field contains the SID received from the VU and a 2-byte code as follows:
The last sub message of a message (LEN byte < 255) may be acknowledged using any of these codes or not acknowledged. The VU responses that will consist of several sub messages are:
|
2.2.2.16
|
DDP_018 |
The Negative Response message is sent by the VU in response to the above request messages when the VU cannot satisfy the request. The data fields of the message contains the SID of the response (7F), the SID of the request, and a code specifying the reason of the negative response. The following codes are available:
|
2.2.3 Message flow
A typical message flow during a normal data download procedure is the following:
|
IDE |
|
VU |
|
Start Communication Request |
⇨ |
|
|
|
⇦ |
Positive Response |
|
Start Diagnostic Service Request |
⇨ |
|
|
|
⇦ |
Positive Response |
|
Request Upload |
⇨ |
|
|
|
⇦ |
Positive Response |
|
Transfer Data Request Overview |
⇨ |
|
|
|
⇦ |
Positive Response |
|
Transfer Data Request #2 |
⇨ |
|
|
|
⇦ |
Positive Response #1 |
|
Acknowledge Sub Message #1 |
⇨ |
|
|
|
⇦ |
Positive Response #2 |
|
Acknowledge Sub Message #2 |
⇨ |
|
|
|
⇦ |
Positive Response #m |
|
Acknowledge Sub Message #m |
⇨ |
|
|
|
⇦ |
Positive Response (Data Field < 255 Bytes) |
|
Acknowledge Sub Message (optional) |
⇨ |
|
|
… |
||
|
Transfer Data Request #n |
⇨ |
|
|
|
⇦ |
Positive Response |
|
Request Transfer Exit |
⇨ |
|
|
|
⇦ |
Positive Response |
|
Stop Communication Request |
⇨ |
|
|
|
⇦ |
Positive Response |
2.2.4 Timing
|
DDP_019 |
During normal operation the timing parameters shown in the following figure are relevant: Figure 1 Message flow, timing 
Where:
The allowed values for the timing parameters are showed in the following table (KWP extended timing parameters set, used in case of physical addressing for faster communication).
|
2.2.5 Error handling
If an error occurs during the message exchange, the message flow scheme is modified depending on which equipment has detected the error and on the message generating the error.
In figure 2 and figure 3 the error handling procedures for the VU and the IDE are respectively shown.
2.2.5.1
|
DDP_020 |
If the IDE detects an error during the Start Communication phase, either by timing or by the bit stream, then it will wait for a period P3 min before issuing again the request. |
|
DDP_021 |
If the VU detects an error in the sequence coming from the IDE, it shall send no response and wait for another Start Communication Request message within a period P3 max. |
2.2.5.2
Two different error handling areas can be defined:
|
1. |
The VU detects an IDE transmission error.
Figure 2 VU error handling 
|
|
2. |
The IDE detects a VU transmission error.
Figure 3 IDE error handling 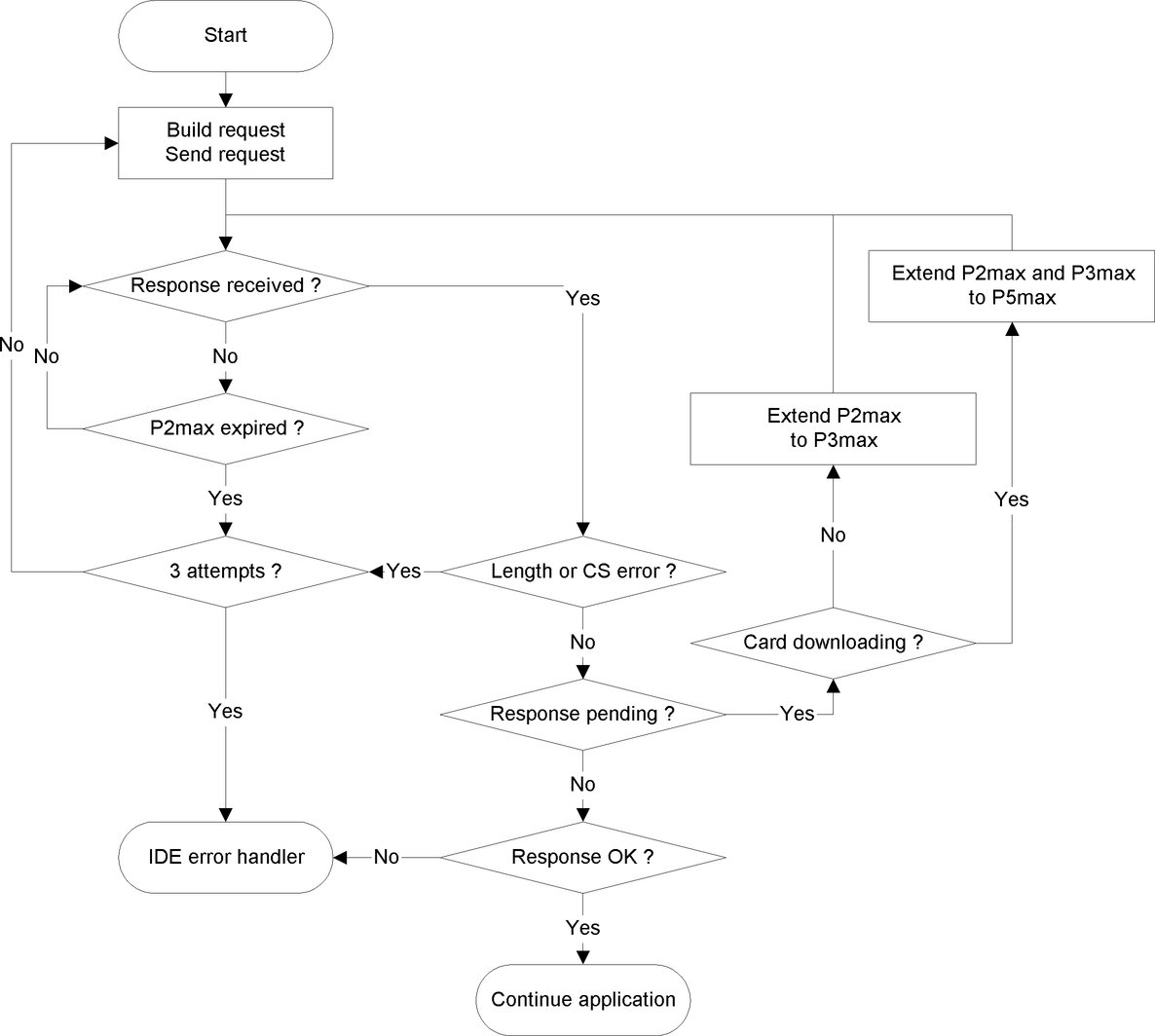
|
2.2.6 Response Message content
This paragraph specifies the content of the data fields of the various positive response messages.
Data elements are defined in Appendix 1 data dictionary.
Remark: For generation 2 downloads, each top-level data element is represented by a record array, even if it contains only one record. A record array starts with a header; this header contains the record type, the record size and the number of records. Record arrays are named by ‘…RecordArray’ (with header) in the following tables.
2.2.6.1
|
DDP_029 |
The data field of the ‘Positive Response Transfer Data Overview’ message shall provide the following data in the following order under the SID 76 Hex, the TREP 01 Hex and appropriate sub message splitting and counting: Data structure generation 1
Data structure generation 2
|
2.2.6.2
|
DDP_030 |
The data field of the ‘Positive Response Transfer Data Activities’ message shall provide the following data in the following order under the SID 76 Hex, the TREP 02 Hex and appropriate sub message splitting and counting: Data structure generation 1
Data structure generation 2
|
2.2.6.3
|
DDP_031 |
The data field of the ‘Positive Response Transfer Data Events and Faults’ message shall provide the following data in the following order under the SID 76 Hex, the TREP 03 Hex and appropriate sub message splitting and counting: Data structure generation 1
Data structure generation 2
|
2.2.6.4
|
DDP_032 |
The data field of the ‘Positive Response Transfer Data Detailed Speed’ message shall provide the following data in the following order under the SID 76 Hex, the TREP 04 Hex and appropriate sub message splitting and counting: Data structure generation 1
Data structure generation 2:
|
2.2.6.5
|
DDP_033 |
The data field of the ‘Positive Response Transfer Data Technical Data’ message shall provide the following data in the following order under the SID 76 Hex, the TREP 05 Hex and appropriate sub message splitting and counting: Data structure generation 1
Data structure generation 2:
|
2.3. ESM File storage
|
DDP_034 |
When a download session has included a VU data transfer, the IDE shall store within one single physical file all data received from the VU during the download session within Positive Response Transfer Data messages. Data stored excludes message headers, sub-message counters, empty sub-messages and checksums but include the SID and TREP (of the first sub-message only if several sub-messages). |
3. TACHOGRAPH CARDS DOWNLOADING PROTOCOL
3.1. Scope
This paragraph describes the direct card data downloading of a tachograph card to an IDE. The IDE is not part of the secure environment; therefore no authentication between the card and the IDE is performed.
3.2. Definitions
|
Download session |
: |
Each time a download of the ICC data is performed. The session covers the complete procedure from the reset of the ICC by an IFD until the deactivation of the ICC (withdraw of the card or next reset). |
|
Signed Data File |
: |
A file from the ICC. The file is transferred to the IFD in plain text. On the ICC the file is hashed and signed and the signature is transferred to the IFD. |
3.3. Card Downloading
|
DDP_035 |
The download of a tachograph card includes the following steps:
|
3.3.1 Initialisation sequence
|
DDP_036 |
The IDE shall initiate the sequence as follows:
It is optional to use PPS to switch to a higher baud rate as long as the ICC supports it. |
3.3.2 Sequence for un-signed data files
|
DDP_037 |
The sequence to download the EFs ICC, IC, Card_Certificate (or CardSignCertificate) and CA_Certificate is as follows:
Note 1: Before selecting the Card_Certificate (or CardSignCertificate) EF, the Tachograph Application must be selected (selection by AID). Note 2: Selecting and reading a file may also be performed in one step using a Read Binary command with a short EF identifier. |
3.3.3 Sequence for Signed data files
|
DDP_038 |
The following sequence shall be used for each of the following files that has to be downloaded with their signature:
Note: Selecting and reading a file may also be performed in one step using a Read Binary command with a short EF identifier. In this case the EF may be selected and read before the command Perform Hash of File is applied. |
3.3.4 Sequence for resetting the calibration counter.
|
DDP_039 |
The sequence to reset the
Note: Selecting and updating a file may also be performed in one step using an Update Binary command with a short EF identifier. |
3.4. Data storage format
3.4.1 Introduction
|
DDP_040 |
The downloaded data has to be stored according to the following conditions:
|
3.4.2 File format
|
DDP_041 |
The file format is a concatenation of several TLV objects. |
|
DDP_042 |
The tag for an EF shall be the FID plus the appendix „00“. |
|
DDP_043 |
The tag of an EF's signature shall be the FID of the file plus the appendix „01“. |
|
DDP_044 |
The length is a two byte value. The value defines the number of bytes in the value field. The value „FF FF“ in the length field is reserved for future use. |
|
DDP_045 |
When a file is not downloaded nothing related to the file shall be stored (no tag and no zero length). |
|
DDP_046 |
A signature shall be stored as the next TLV object directly after the TLV object that contains the data of the file.
Example of data in a download file on an ESM:
|
4. DOWNLOADING A TACHOGRAPH CARD VIA A VEHICLE UNIT.
|
DDP_047 |
The VU must allow for downloading the content of a driver card inserted to a connected IDE. |
|
DDP_048 |
The IDE shall send a ‘Transfer Data Request Card Download’ message to the VU to initiate this mode (see 2.2.2.9). |
|
DDP_049 |
The VU shall then download the whole card, file by file, in accordance with the card downloading protocol defined in paragraph 3, and forward all data received from the card to the IDE within the appropriate TLV file format (see 3.4.2) and encapsulated within a ‘Positive Response Transfer Data’ message. |
|
DDP_050 |
The IDE shall retrieve card data from the ‘Positive Response Transfer Data’ message (stripping all headers, SIDs, TREPs, sub message counters, and checksums) and store them within one single physical file as described in paragraph 2.3. |
|
DDP_051 |
The VU shall then, as applicable, update the
|
(*) The card inserted will trigger the appropriate access rights to the downloading function and to the data. It shall, however, be possible to download data from a driver card inserted into one of the VU slots when no other card type is inserted in the other slot.
(**) If the VU responds with a Negative Response containing a code meaning ‘request correctly received, response pending’, this value is extended to the same upper limit value of P3.
Appendix 8
CALIBRATION PROTOCOL
TABLE OF CONTENT
|
1. |
INTRODUCTION | 283 |
|
2. |
TERMS, DEFINITIONS AND REFERENCES | 283 |
|
3. |
OVERVIEW OF SERVICES | 284 |
|
3.1. |
Services available | 284 |
|
3.2. |
Response codes | 285 |
|
4. |
COMMUNICATION SERVICES | 285 |
|
4.1. |
StartCommunication Service | 285 |
|
4.2. |
StopCommunication Service | 287 |
|
4.2.1 |
Message description | 287 |
|
4.2.2 |
Message format | 288 |
|
4.2.3 |
Parameter Definition | 289 |
|
4.3. |
TesterPresent Service | 289 |
|
4.3.1 |
Message description | 289 |
|
4.3.2 |
Message format | 289 |
|
5. |
MANAGEMENT SERVICES | 291 |
|
5.1. |
StartDiagnosticSession service | 291 |
|
5.1.1 |
Message description | 291 |
|
5.1.2 |
Message format | 292 |
|
5.1.3 |
Parameter definition | 293 |
|
5.2. |
SecurityAccess service | 294 |
|
5.2.1 |
Message Description | 294 |
|
5.2.2 |
Message format — SecurityAccess — requestSeed | 295 |
|
5.2.3 |
Message format — SecurityAccess — sendKey | 296 |
|
6. |
DATA TRANSMISSION SERVICES | 297 |
|
6.1. |
ReadDataByIdentifier service | 298 |
|
6.1.1 |
Message description | 298 |
|
6.1.2 |
Message format | 298 |
|
6.1.3 |
Parameter Definition | 299 |
|
6.2. |
WriteDataByIdentifier service | 300 |
|
6.2.1 |
Message description | 300 |
|
6.2.2 |
Message format | 300 |
|
6.2.3 |
Parameter definition | 302 |
|
7. |
CONTROL OF TEST PULSES — INPUT/OUTPUT CONTROL FUNCTIONAL UNIT | 302 |
|
7.1. |
InputOutputControlByIdentifier service | 302 |
|
7.1.1 |
Message description | 302 |
|
7.1.2 |
Message format | 303 |
|
7.1.3 |
Parameter definition | 304 |
|
8. |
DATARECORDS FORMATS | 305 |
|
8.1. |
Transmitted parameter ranges | 305 |
|
8.2. |
dataRecords formats | 306 |
1. INTRODUCTION
This appendix describes how data is exchanged between a vehicle unit and a tester via the K-line which forms part of the calibration interface described in Appendix 6. It also describes control of the input/output signal line on the calibration connector.
Establishing K-line communications is described in Section 4 ‘Communication Services’.
This appendix uses the idea of diagnostic ‘sessions’ to determine the scope of K-line control under different conditions. The default session is the ‘StandardDiagnosticSession’ where all data can be read from a vehicle unit but no data can be written to a vehicle unit.
Selection of the diagnostic session is described in Section 5 ‘Management Services’.
This appendix has to be considered as relevant for both generations of VUs and of workshop cards, in compliance with the interoperability requirements laid down in this Regulation.
|
CPR_001 |
The ‘ECUProgrammingSession’ allows data entry into the vehicle unit. In the case of entry of calibration data, the vehicle unit must, in addition be in the CALIBRATION mode of operation. Data transfer via K-line is described in Section 6 ‘Data Transmission Services’. Formats of data transferred are detailed in Section 8 ‘dataRecords formats’. |
|
CPR_002 |
The ‘ECUAdjustmentSession’ allows the selection of the I/O mode of the calibration I/O signal line via the K-line interface. Control of the calibration I/O signal line is described in section 7 ‘Control of Test Pulses — Input/Output Control functional unit’. |
|
CPR_003 |
Throughout this document the address of the tester is referred to as ‘tt’. Although there may be preferred addresses for testers, the VU shall respond correctly to any tester address. The physical address of the VU is 0xEE. |
2. TERMS, DEFINITIONS AND REFERENCES
The protocols, messages and error codes are principally based on a draft of ISO 14229-1 (Road vehicles — Diagnostic systems — Part 1: Diagnostic services, version 6 of 22 February 2001).
Byte encoding and hexadecimal values are used for the service identifiers, the service requests and responses, and the standard parameters.
The term ‘tester’ refers to the equipment used to enter programming/calibration data into the VU.
The terms ‘client’ and ‘server’ refer to the tester and the VU respectively.
The term ECU means ‘Electronic Control Unit’ and refers to the VU.
References:
ISO 14230-2: Road Vehicles -Diagnostic Systems — Keyword Protocol 2000- Part 2: Data Link Layer.
First edition: 1999.
Vehicles — Diagnostic.
3. OVERVIEW OF SERVICES
3.1. Services available
The following table provides an overview of the services that will be available in the tachograph and are defined in this document.
|
CPR_004 |
The table indicates the services that are available in an enabled diagnostic session.
|
Table 1
Service Identifier value summary table
|
|
Diagnostic Sessions |
||||||
|
Diagnostic Service Name |
Section No. |
SId Req.Value |
SD |
ECUAS |
ECUPS |
||
|
StartCommunication |
4.1 |
81 |
■ |
■ |
■ |
||
|
StopCommunication |
4.2 |
82 |
■ |
|
|
||
|
TesterPresent |
4.3 |
3E |
■ |
■ |
■ |
||
|
StartDiagnosticSession |
5.1 |
10 |
■ |
■ |
■ |
||
|
SecurityAccess |
5.2 |
27 |
■ |
■ |
■ |
||
|
ReadDataByIdentifier |
6.1 |
22 |
■ |
■ |
■ |
||
|
WriteDataByIdentifier |
6.2 |
2E |
|
|
■ |
||
|
InputOutputControlByIdentifier |
7.1 |
2F |
|
■ |
|
||
|
|||||||
3.2. Response codes
Response codes are defined for each service.
4. COMMUNICATION SERVICES
Some services are necessary to establish and maintain communication. They do not appear on the application layer. The services available are detailed in the following table:
Table 2
Communication Services
|
Service name |
Description |
|
StartCommunication |
The client requests to start a communication session with a server(s). |
|
StopCommunication |
The client requests to stop the current communication session. |
|
TesterPresent |
The client indicates to the server that it is still present. |
|
CPR_005 |
The StartCommunication Service is used for starting a communication. In order to perform any service, communication must be initialised and the communication parameters need to be appropriate for the desired mode. |
4.1. StartCommunication Service
|
CPR_006 |
Upon receiving a StartCommunication indication primitive, the VU shall check if the requested communication link can be initialised under the present conditions. Valid conditions for the initialisation of a communication link are described in document ISO 14230-2. |
|
CPR_007 |
Then the VU shall perform all actions necessary to initialise the communication link and send a StartCommunication response primitive with the Positive Response parameters selected. |
|
CPR_008 |
If a VU that is already initialised (and has entered any diagnostic session) receives a new StartCommunication Request (e.g. due to error recovery in the tester) the request shall be accepted and the VU shall be reinitialised. |
|
CPR_009 |
If the communication link cannot be initialised for any reason, the VU shall continue operating as it was immediately prior to the attempt to initialise the communication link.. |
|
CPR_010 |
The StartCommunication Request message must be physically addressed. |
|
CPR_011 |
Initialising the VU for services is performed through a ‘fast initialisation’ method,
|
|
CPR_012 |
After completion of the initialisation,
|
|
CPR_014 |
The data rate on the K-line shall be 10 400 Baud. |
|
CPR_016 |
The fast initialisation is started by the tester transmitting a Wake up pattern (Wup) on the K-line. The pattern begins after the idle time on K-line with a low time of Tinil. The tester transmits the first bit of the StartCommunication Service after a time of Twup following the first falling edge.
|
|
CPR_017 |
The timing values for the fast initialisation and communications in general are detailed in the tables below. There are different possibilities for the idle time:
Table 3 Timing values for fast initialisation
Table 4 Communication timing values
|
|||||||||||||||||||||||||||||||||||||||||
|
CPR_018 |
The message format for fast initialisation is detailed in the following tables. (NOTE: Hex means hexadecimal) Table 5 StartCommunication Request Message
Table 6 StartCommunication Positive Response Message
|
|
CPR_019 |
There is no negative response to the StartCommunication Request message, if there is no positive response message to be transmitted then the VU is not initialised, nothing is transmitted and it remains in its normal operation. |
4.2. StopCommunication Service
4.2.1 Message description
The purpose of this communication layer service is to terminate a communication session.
|
CPR_020 |
Upon receiving a StopCommunication indication primitive, the VU shall check if the current conditions allow to terminate this communication. In this case the VU shall perform all actions necessary to terminate this communication. |
|
CPR_021 |
If it is possible to terminate the communication, the VU shall issue a StopCommunication response primitive with the Positive Response parameters selected, before the communication is terminated. |
|
CPR_022 |
If the communication cannot be terminated by any reason, the VU shall issue a StopCommunication response primitive with the Negative Response parameter selected. |
|
CPR_023 |
If time-out of P3 max is detected by the VU, the communication shall be terminated without any response primitive being issued. |
4.2.2 Message format
|
CPR_024 |
The message formats for the StopCommunication primitives are detailed in the following tables. Table 7 StopCommunication Request Message
Table 8 StopCommunication Positive Response Message
Table 9 StopCommunication Negative Response Message
|
4.2.3 Parameter Definition
This service does not require any parameter definition.
4.3. TesterPresent Service
4.3.1 Message description
The TesterPresent service is used by the tester to indicate to the server that it is still present, in order to prevent the server from automatically returning to normal operation and possibly stopping the communication. This service, sent periodically, keeps the diagnostic session/communication active by resetting the P3 timer each time a request for this service is received.
4.3.2 Message format
|
CPR_079 |
The message formats for the TesterPresent primitives are detailed in the following tables. Table 10 TesterPresent Request Message
|
||||||||||||||||||||||||||||||||||||||||||||
|
CPR_080 |
If the responseRequired parameter is set to ‘yes’, then the server shall respond with the following positive response message. If set to ‘no’, then no response is sent by the server. Table 11 TesterPresent Positive Response Message
|
|
CPR_081 |
The service shall support the following negative responses codes: Table 12 TesterPresent Negative Response Message
|
|||||||||||||||||||||||||||||||||||||||||||||||||
5. MANAGEMENT SERVICES
The services available are detailed in the following table:
Table 13
Management Services
|
Service name |
Description |
|
StartDiagnosticSession |
The client requests to start a diagnostic session with a VU. |
|
SecurityAccess |
The client requests access to functions restricted to authorised users. |
5.1. StartDiagnosticSession service
5.1.1 Message description
|
CPR_025 |
The service StartDiagnosticSession is used to enable different diagnostic sessions in the server. A diagnostic session enables a specific set of services according to Table 17. A session can enable vehicle manufacturer specific services which are not part of this document. Implementation rules shall conform to the following requirements:
|
|
CPR_026 |
A diagnostic session shall only be started if communication has been established between the client and the VU. |
|
CPR_027 |
The timing parameters defined in Table 4 shall be active after a successful StartDiagnosticSession with the diagnosticSession parameter set to ‘StandardDiagnosticSession’ in the request message if another diagnostic session was previously active. |
5.1.2 Message format
|
CPR_028 |
The message formats for the StartDiagnosticSession primitives are detailed in the following tables. Table 14 StartDiagnosticSession Request Message
Table 15 StartDiagnosticSession Positive Response Message
Table 16 StartDiagnosticSession Negative Response Message
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
5.1.3 Parameter definition
|
CPR_029 |
The parameter diagnosticSession (DS_) is used by the StartDiagnosticSession service to select the specific behaviour of the server(s). The following diagnostic sessions are specified in this document: Table 17 Definition of diagnosticSession Values
|
5.2. SecurityAccess service
Writing of calibration data is not possible unless the VU is in CALIBRATION mode. In addition to insertion of a valid workshop card into the VU, it is necessary to enter the appropriate PIN into the VU before access to the CALIBRATION mode is granted.
When the VU is in CALIBRATION or CONTROL mode, access to the calibration input/output line is also possible.
The SecurityAccess service provides a means to enter the PIN and to indicate to the tester whether or not the VU is in CALIBRATION mode.
It is acceptable that the PIN may be entered through alternative methods.
5.2.1 Message Description
The SecurityAccess service consists of a SecurityAccess ‘requestSeed’ message, eventually followed by a SecurityAccess ‘sendKey’ message. The SecurityAccess service must be carried out after the StartDiagnosticSession service.
|
CPR_033 |
The tester shall use the SecurityAccess ‘requestSeed’ message to check if the vehicle unit is ready to accept a PIN. |
|
CPR_034 |
If the vehicle unit is already in CALIBRATION mode, it shall answer the request by sending a ‘seed’ of 0x0000 using the service SecurityAccess Positive Response. |
|
CPR_035 |
If the vehicle unit is ready to accept a PIN for verification by a workshop card, it shall answer the request by sending a ‘seed’ greater than 0x0000 using the service SecurityAccess Positive Response. |
|
CPR_036 |
If the vehicle unit is not ready to accept a PIN from the tester, either because the workshop card inserted is not valid, or because no workshop card has been inserted, or because the vehicle unit expects the PIN from another method, it shall answer the request with a Negative Response with a response code set to conditionsNotCorrectOrRequestSequenceError. |
|
CPR_037 |
The tester shall then, eventually, use the SecurityAccess ‘sendKey’ message to forward a PIN to the Vehicle Unit. To allow time for the card authentication process to take place, the VU shall use the negative response code requestCorrectlyReceived-ResponsePending to extend the time to respond. However, the maximum time to respond shall not exceed 5 minutes. As soon as the requested service has been completed, the VU shall send a positive response message or negative response message with a response code different from this one. The negative response code requestCorrectlyReceived-ResponsePending may be repeated by the VU until the requested service is completed and the final response message is sent. |
|
CPR_038 |
The vehicle unit shall answer to this request using the service SecurityAccess Positive Response only when in CALIBRATION mode. |
|
CPR_039 |
In the following cases, the vehicle unit shall answer to this request with a Negative Response with a response code set to:
|
5.2.2 Message format — SecurityAccess — requestSeed
|
CPR_040 |
The message formats for the SecurityAccess ‘requestSeed’ primitives are detailed in the following tables. Table 18 SecurityAccess Request- requestSeed Message
Table 19 SecurityAccess — requestSeed Positive Response Message
Table 20 SecurityAccess Negative Response Message
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
5.2.3 Message format — SecurityAccess — sendKey
|
CPR_041 |
The message formats for the SecurityAccess ‘sendKey’ primitives are detailed in the following tables. Table 21 SecurityAccess Request — sendKey Message
Table 22 SecurityAccess — sendKey Positive Response Message
Table 23 SecurityAccess Negative Response Message
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
6. DATA TRANSMISSION SERVICES
The services available are detailed in the following table:
Table 24
Data Transmission Services
|
Service name |
Description |
|
ReadDataByIdentifier |
The client requests the transmission of the current value of a record with access by recordDataIdentifier. |
|
WriteDataByIdentifier |
The client requests to write a record accessed by recordDataIdentifier. |
6.1. ReadDataByIdentifier service
6.1.1 Message description
|
CPR_050 |
The ReadDataByIdentifier service is used by the client to request data record values from a server. The data are identified by a recordDataIdentifier. It is the VU manufacturer's responsibility that the server conditions are met when performing this service. |
6.1.2 Message format
|
CPR_051 |
The message formats for the ReadDataByIdentifier primitives are detailed in the following tables. Table 25 ReadDataByIdentifier Request Message
Table 26 ReadDataByIdentifier Positive Response Message
Table 27 ReadDataByIdentifier Negative Response Message
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
6.1.3 Parameter Definition
|
CPR_052 |
The parameter recordDataIdentifier (RDI_) in the ReadDataByIdentifier request message identifies a data record. |
|
CPR_053 |
recordDataIdentifier values defined by this document are shown in the table below. The recordDataIdentifier table consists of four columns and multiple lines.
Table 28 Definition of recordDataIdentifier values
|
|
CPR_054 |
The parameter dataRecord (DREC_) is used by the ReadDataByIdentifier positive response message to provide the data record value identified by the recordDataIdentifier to the client (tester). Data formats are specified in section 8. Additional user optional dataRecords including VU specific input, internal and output data may be implemented, but are not defined in this document. |
6.2. WriteDataByIdentifier service
6.2.1 Message description
|
CPR_056 |
The WriteDataByIdentifier service is used by the client to write data record values to a server. The data are identified by a recordDataIdentifier. It is the VU manufacturer's responsibility that the server conditions are met when performing this service. To update the parameters listed in Table 28 the VU must be in CALIBRATION mode. |
6.2.2 Message format
|
CPR_057 |
The message formats for the WriteDataByIdentifier primitives are detailed in the following tables. Table 29 WriteDataByIdentifier Request Message
Table 30 WriteDataByIdentifier Positive Response Message
Table 31 WriteDataByIdentifier Negative Response Message
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
6.2.3 Parameter definition
The parameter recordDataIdentifier (RDI_) is defined in Table 28.
The parameter dataRecord (DREC_) is used by the WriteDataByIdentifier request message to provide the data record values identified by the recordDataIdentifier to the server (VU). Data formats are specified in section 8.
7. CONTROL OF TEST PULSES — INPUT/OUTPUT CONTROL FUNCTIONAL UNIT
The services available are detailed in the following table:
Table 32
Input/Output Control functional unit
|
Service name |
Description |
|
InputOutputControlByIdentifier |
The client requests the control of an input/output specific to the server. |
7.1. InputOutputControlByIdentifier service
7.1.1 Message description
There is a connection via the front connector which allows test pulses to be controlled or monitored using a suitable tester.
|
CPR_058 |
This calibration I/O signal line can be configured by K-line command using the InputOutputControlByIdentifier service to select the required input or output function for the line. The available states of the line are:
|
|
CPR_059 |
The vehicle unit must have entered an adjustment session and must be in CALIBRATION or CONTROL mode to configure the state of the line. When the VU is in CALIBRATION mode, the four states of the line can be selected (disabled, speedSignalInput, realTimeSpeedSignalOutputSensor, RTCOutput). When the VU is in CONTROL mode, only two states of the lines can be selected (disabled, realTimeSpeedOutputSensor). On exit of the adjustment session or of the CALIBRATION or CONTROL mode the vehicle unit must ensure the calibration I/O signal line is returned to the ‘disabled’ (default) state. |
|
CPR_060 |
If speed pulses are received at the real time speed signal input line of the VU while the calibration I/O signal line is set to input then the calibration I/O signal line shall be set to output or returned to the disabled state. |
|
CPR_061 |
The sequence shall be:
|
7.1.2 Message format
|
CPR_062 |
The message formats for the InputOutputControlByIdentifier primitives are detailed in the following tables. Table 33 InputOutputControlByIdentifier Request Message
Note: The controlState parameter is present only in some cases (see 7.1.3). Table 34 InputOutputControlByIdentifier Positive Response Message
Table 35 InputOutputControlByIdentifier Negative Response Message
|
7.1.3 Parameter definition
|
CPR_064 |
The parameter inputOutputControlParameter (IOCP_) is defined in the following table. Table 36 Definition of inputOutputControlParameter values
|
|
CPR_065 |
The parameter controlState is present only when the inputOutputControlParameter is set to ShortTermAdjustment and is defined in the following table: Table 37 Definition of controlState values
|
8. DATARECORDS FORMATS
This section details:
|
— |
general rules that shall be applied to ranges of parameters transmitted by the vehicle unit to the tester, |
|
— |
formats that shall be used for data transferred via the Data Transmission Services described in section 6. |
|
CPR_067 |
All parameters identified shall be supported by the VU. |
|
CPR_068 |
Data transmitted by the VU to the tester in response to a request message shall be of the measured type (i.e. current value of the requested parameter as measured or observed by the VU). |
8.1. Transmitted parameter ranges
|
CPR_069 |
Table 38 defines the ranges used to determine the validity of a transmitted parameter. |
|
CPR_070 |
The values in the range ‘error indicator’ provide a means for the vehicle unit to immediately indicate that valid parametric data is not currently available due to some type of error in the tachograph. |
|
CPR_071 |
The values in the range ‘not available’ provide a means for the vehicle unit to transmit a message which contains a parameter that is not available or not supported in that module. The values in the range ‘not requested’ provide a means for a device to transmit a command message and identify those parameters where no response is expected from the receiving device. |
|
CPR_072 |
If a component failure prevents the transmission of valid data for a parameter, the error indicator as described in Table 38 should be used in place of that parameter's data. However, if the measured or calculated data has yielded a value that is valid yet exceeds the defined parameter range, the error indicator should not be used. The data should be transmitted using the appropriate minimum or maximum parameter value. Table 38 dataRecords ranges
|
|
CPR_073 |
For parameters coded in ASCII, the ASCII character ‘*’ is reserved as a delimiter. |
8.2. dataRecords formats
Table 39 to Table 42 below detail the formats that shall be used via the ReadDataByIdentifier and WriteDataByIdentifier Services.
|
CPR_074 |
Table 39 provides the length, resolution and operating range for each parameter identified by its recordDataIdentifier: Table 39 Format of dataRecords
|
|||||||||||||||||||||||||||||||||||||||||||||||||
|
CPR_075 |
Table 40 details the formats of the different bytes of the TimeDate parameter: Table 40 Detailed format of TimeDate (recordDataIdentifier value # F90B)
|
|
CPR_076 |
Table 41 details the formats of the different bytes of the NextCalibrationDate parameter. Table 41 Detailed format of NextCalibrationDate (recordDataIdentifier value # F922)
|
NOTE concerning the use of the ‘Day’ parameter:
|
1) |
A value of 0 for the date is null. The values 1, 2, 3, and 4 are used to identify the first day of the month; 5, 6, 7, and 8 identify the second day of the month; etc. |
|
2) |
This parameter does not influence or change the hours parameter above. |
NOTE concerning the use of byte ‘Year’ parameter:
A value of 0 for the year identifies the year 1985; a value of 1 identifies 1986; etc.
|
CPR_078 |
Table 42 details the formats of the different bytes of the VehicleRegistrationNumber parameter: Table 42 Detailed format of VehicleRegistrationNumber (recordDataIdentifier value # F97E)
|
(1) – the value inserted in byte #6 of the request message is not supported, i.e. not in Table 17,
(2) – the length of the message is wrong,
(3) – the criteria for the request StartDiagnosticSession are not met.
Appendix 9
TYPE APPROVAL LIST OF MINIMUM REQUIRED TESTS
TABLE OF CONTENT
|
1. |
INTRODUCTION | 309 |
|
2. |
VEHICLE UNIT FUNCTIONAL TESTS | 311 |
|
3. |
MOTION SENSOR FUNCTIONAL TESTS | 315 |
|
4. |
TACHOGRAPH CARDS FUNCTIONAL TESTS | 318 |
|
5. |
EXTERNAL GNSS FACILITY TESTS | 328 |
|
6. |
REMOTE COMMUNICATION FACILITY TESTS | 331 |
|
7. |
PAPER FUNCTIONAL TESTS | 333 |
|
8. |
INTEROPERABILITY TESTS | 335 |
1. INTRODUCTION
1.1. Type approval
The EC type approval for a recording equipment (or component) or a tachograph card is based on:
|
— |
a security certification, based on Common Criteria specifications, against a security target fully compliant with Appendix 10 to this Annex (To be completed/modified), |
|
— |
a functional certification performed by a Member State authority certifying that the item tested fulfils the requirements of this Annex in terms of functions performed, measurement accuracy and environmental characteristics, |
|
— |
an interoperability certification performed by the competent body certifying that the recording equipment (or tachograph card) is fully interoperable with the necessary tachograph card (or recording equipment) models (see Chapter 8 of this Annex). |
This Appendix specifies which tests, as a minimum, must be performed by a Member State authority during the functional tests, and which tests, as a minimum, must be performed by the competent body during the interoperability tests. Procedures to follow to carry out the tests or the type of tests are not specified further.
The security certification aspects are not covered by this Appendix. If some tests requested for type approval are performed during the security evaluation and certification process, then these tests do not need to be performed again. In this case, only the results of these security tests may be inspected. For information, the requirements expected to be tested (or closely related to tests expected to be performed) during the security certification, are marked with a ‘*’ in this Appendix.
The numbered requirements refer to the Annex corpus, while the other requirements refer to the other appendixes (e.g. PIC_001 refers to requirement PIC_001 of Appendix 3 Pictograms).
This Appendix considers separately the type approval of the motion sensor, of the vehicle unit, and of the external GNSS facility as components of the recording equipment. Each component will get its own type approval certificate in which the other compatible components will be indicated. The functional test of the motion sensor (or external GNSS facility) is done together with the vehicle unit and vice versa.
Interoperability between every model of motion sensor (resp. external GNSS facility) and every model of vehicle unit is not required. In that case the type approval for a motion sensor (resp. external GNSS facility) can be granted only in combination with the type approval of the relevant vehicle unit and vice versa.
1.2. References
The following references are used in this Appendix:
IEC 60068-2-1: Environmental testing — Part 2-1: Tests — Test A: Cold
IEC 60068-2-2: Basic environmental testing procedures; part 2: tests; tests B: dry heat (sinusoidal).
IEC 60068-2-6: Environmental testing — Part 2: Tests — Test Fc: Vibration
IEC 60068-2-14: Environmental testing; Part 2-14: Tests; Test N: Change of temperature
IEC 60068-2-27: Environmental testing. Part 2: Tests. Test Ea and guidance: Shock
IEC 60068-2-30: Environmental testing — Part 2-30: Tests — Test Db: Damp heat, cyclic (12 h + 12 h cycle)
IEC 60068-2-64: Environmental testing — Part 2-64: Tests — Test Fh: Vibration, broadband random and guidance
IEC 60068-2-78 Environmental testing — Part 2-78: Tests — Test Cab: Damp heat, steady state
ISO 16750-3 — Mechanical loads (2012-12)
ISO 16750-4 — Climatic loads(2010-04).
ISO 20653: Road vehicles — Degree of protection (IP code) — Protection of electrical equipment against foreign objects, water and access
ISO 10605:2008 + Technical Corrigendum:2010 + AMD1:2014 Road vehicles — Test methods for electrical disturbances from electrostatic discharge
ISO 7637-1:2002 + AMD1: 2008 Road vehicles — Electrical disturbances from conduction and coupling — Part 1: Definitions and general considerations.
ISO 7637-2 Road vehicles — Electrical disturbances from conduction and coupling — Part 2: Electrical transient conduction along supply lines only.
ISO 7637-3 Road vehicles — Electrical disturbances from conduction and coupling — Part 3: Electrical transient transmission by capacitive and inductive coupling via lines other than supply lines.
ISO/IEC 7816-1 Identification cards — Integrated circuit(s) cards with contacts — Part 1: Physical characteristics..
ISO/IEC 7816-2 Information technology — Identification cards — Integrated circuit(s) cards with contacts — Part 2: Dimensions and location of the contacts.
ISO/IEC 7816-3 Information technology — Identification cards — Integrated circuit(s) cards with contacts — Part 3: Electronic signals and transmission protocol.
ISO/IEC 10373-1:2006 + AMD1:2012 Identification cards — Test methods — Part 1: General characteristics
ISO/IEC 10373-3:2010 + Technical Corrigendum:2013 Identification cards — Test methods — Part 3: Integrated circuit cards with contacts and related interface devices
ISO 16844-3:2004, Cor 1:2006 Road vehicles — Tachograph systems — Part 3: Motion sensor interface (with vehicle units).
ISO 16844-4 Road vehicles — Tachograph systems — Part 4: CAN interface
ISO 16844-6 Road vehicles — Tachograph systems — Part 6: Diagnostics
ISO 16844-7 Road vehicles — Tachograph systems — Part 7: Parameters
ISO 534 Paper and board — Determination of thickness, density and specific volume
UN ECE R10 Uniform provisions concerning the approval of vehicles with regard to electromagnetic compatibility (United Nation Economic Commission for Europe)
2. VEHICLE UNIT FUNCTIONAL TESTS
|
No |
Test |
Description |
Related requirements |
|||||||||||||||||||||||||||||||
|
1 |
Administrative examination |
|||||||||||||||||||||||||||||||||
|
1.1 |
Documentation |
Correctness of documentation |
|
|||||||||||||||||||||||||||||||
|
1.2 |
Manufacturer test results |
Results of manufacturer test performed during integration. Paper demonstrations. |
88, 89,91 |
|||||||||||||||||||||||||||||||
|
2 |
Visual inspection |
|||||||||||||||||||||||||||||||||
|
2.1 |
Compliance with documentation |
|
||||||||||||||||||||||||||||||||
|
2.2 |
Identification/markings |
224 to 226 |
||||||||||||||||||||||||||||||||
|
2.3 |
Materials |
219 to 223 |
||||||||||||||||||||||||||||||||
|
2.4 |
Sealing |
398, 401 to 405 |
||||||||||||||||||||||||||||||||
|
2.5 |
External interfaces |
|
||||||||||||||||||||||||||||||||
|
3 |
Functional tests |
|||||||||||||||||||||||||||||||||
|
3.1 |
Functions provided |
03, 04, 05, 07, 382, |
||||||||||||||||||||||||||||||||
|
3.2 |
Modes of operation |
09 to 11*, 132, 133 |
||||||||||||||||||||||||||||||||
|
3.3 |
Functions and data access rights |
12* 13*,, 382, 383, 386 to 389 |
||||||||||||||||||||||||||||||||
|
3.4 |
Monitoring cards insertion and withdrawal |
15, 16, 17, 18, 19*, 20*, 132 |
||||||||||||||||||||||||||||||||
|
3.5 |
Speed and distance measurement |
21 to 31 |
||||||||||||||||||||||||||||||||
|
3.6 |
Time measurement (test performed at 20°C) |
38 to 43 |
||||||||||||||||||||||||||||||||
|
3.7 |
Monitoring driver activities |
44 to 53, 132 |
||||||||||||||||||||||||||||||||
|
3.8 |
Monitoring driving status |
54, 55, 132 |
||||||||||||||||||||||||||||||||
|
3.9 |
Manual entries |
56 to 62 |
||||||||||||||||||||||||||||||||
|
3.10 |
Company locks management |
63 to 68 |
||||||||||||||||||||||||||||||||
|
3.11 |
Monitoring control activities |
69, 70 |
||||||||||||||||||||||||||||||||
|
3.12 |
Detection of events and/or faults |
71 to 88 132 |
||||||||||||||||||||||||||||||||
|
3.13 |
Equipment identification data |
93*, 94*, 97, 100 |
||||||||||||||||||||||||||||||||
|
3.14 |
Driver card insertion and withdrawal data |
102* to 104* |
||||||||||||||||||||||||||||||||
|
3.15 |
Driver activity data |
105* to 107* |
||||||||||||||||||||||||||||||||
|
3.16 |
Places and positions data |
108* to 112* |
||||||||||||||||||||||||||||||||
|
3.17 |
Odometer data |
113* to 115* |
||||||||||||||||||||||||||||||||
|
3.18 |
Detailed speed data |
116* |
||||||||||||||||||||||||||||||||
|
3.19 |
Events data |
117* |
||||||||||||||||||||||||||||||||
|
3.20 |
Faults data |
118* |
||||||||||||||||||||||||||||||||
|
3.21 |
Calibration data |
119* to 121* |
||||||||||||||||||||||||||||||||
|
3.22 |
Time adjustment data |
124*, 125* |
||||||||||||||||||||||||||||||||
|
3.23 |
Control activity data |
126*, 127* |
||||||||||||||||||||||||||||||||
|
3.24 |
Company locks data |
128* |
||||||||||||||||||||||||||||||||
|
3.25 |
Download activity data |
129* |
||||||||||||||||||||||||||||||||
|
3.26 |
Specific conditions data |
130*, 131* |
||||||||||||||||||||||||||||||||
|
3.27 |
Recording and storing on tachographs cards |
134, 135, 136*, 137*, 139*, 140, 141 142, 143, 144*, 145*, 146*, 147, 148 |
||||||||||||||||||||||||||||||||
|
3.28 |
Displaying |
90, 132, 149 to 166, PIC_001, DIS_001 |
||||||||||||||||||||||||||||||||
|
3.29 |
Printing |
90, 132, 167 to 179, PIC_001, PRT_001 to PRT_014 |
||||||||||||||||||||||||||||||||
|
3.30 |
Warning |
132, 180 to 189, PIC_001 |
||||||||||||||||||||||||||||||||
|
3.31 |
Data downloading to external media |
90, 132, 190 to 194 |
||||||||||||||||||||||||||||||||
|
3.32 |
Remote communication for targeted roadside checks |
195 to 197 |
||||||||||||||||||||||||||||||||
|
3.33 |
Output data to additional external devices |
198, 199 |
||||||||||||||||||||||||||||||||
|
3.34 |
Calibration |
202 to 206*, 383, 384, 386 to 391 |
||||||||||||||||||||||||||||||||
|
3.35 |
Roadside calibration checking |
207 to 209 |
||||||||||||||||||||||||||||||||
|
3.36 |
Time adjustment |
210 to 212* |
||||||||||||||||||||||||||||||||
|
3.37 |
Non-interference of additional functions |
06, 425 |
||||||||||||||||||||||||||||||||
|
3.38 |
Motion sensor interface |
02, 122 |
||||||||||||||||||||||||||||||||
|
3.39 |
External GNSS facility |
03, 123 |
||||||||||||||||||||||||||||||||
|
3.40 |
Verify that the VU detects, records and stores the event(s) and/or fault(s) defined by the VU manufacturer when a paired motion sensor reacts to magnetic fields disturbing vehicle motion detection. |
217 |
||||||||||||||||||||||||||||||||
|
3.41 |
Cypher suite and standardized domain parameters |
CSM_48, CSM_50 |
||||||||||||||||||||||||||||||||
|
4 |
Environmental tests |
|||||||||||||||||||||||||||||||||
|
4.1 |
Temperature |
Verify functionality through:
|
213 |
|||||||||||||||||||||||||||||||
|
4.2 |
Humidity |
Verify that the vehicle unit can withstand a cyclic damp (heat test) through IEC IEC 60068-2-30, test Db, six 24 hours cycles, each temperature varying from + 25°C to + 55°C and a relative humidity of 97 % at + 25°C and equal to 93 % at + 55°C |
214 |
|||||||||||||||||||||||||||||||
|
4.3 |
Mechanical |
The tests described above are performed on different samples of the equipment type being tested. |
219 |
|||||||||||||||||||||||||||||||
|
4.4 |
Protection against water and foreign bodies |
Test according to ISO 20653: Road vehicles — Degree of protection (IP code) — Protection of electrical equipment against foreign objects, water and access (No change in parameters); Minimum value IP 40 |
220, 221 |
|||||||||||||||||||||||||||||||
|
4.5 |
Over-voltage protection |
Verify that the vehicle unit can withstand a power supply of: |
216 |
|||||||||||||||||||||||||||||||
|
24 V versions: |
34 V at + 40°C 1 hour |
|||||||||||||||||||||||||||||||||
|
12V versions: |
17V at +40°C 1 hour |
|||||||||||||||||||||||||||||||||
|
(ISO 16750-2) |
|
|||||||||||||||||||||||||||||||||
|
4.6 |
Reverse polarity protection |
Verify that the vehicle unit can withstand an inversion of its power supply (ISO 16750-2) |
216 |
|||||||||||||||||||||||||||||||
|
4.7 |
Short-circuit protection |
Verify that input output signals are protected against short circuits to power supply and ground (ISO 16750-2) |
216 |
|||||||||||||||||||||||||||||||
|
5 |
EMC tests |
|||||||||||||||||||||||||||||||||
|
5.1 |
Radiated emissions and susceptibility |
Compliance with Regulation ECE R10 |
218 |
|||||||||||||||||||||||||||||||
|
5.2 |
Electrostatic discharge |
Compliance with ISO 10605:2008 + Technical Corrigendum:2010 + AMD1:2014: +/– 4kV for contact and +/– 8kV for air discharge |
218 |
|||||||||||||||||||||||||||||||
|
5.3 |
Conducted transient susceptibility on power supply |
For 24V versions: compliance with ISO 7637-2 + ECE Regulation No. 10 Rev. 3:
For 12V versions: compliance with ISO 7637-1 + ECE Regulation No. 10 Rev. 3:
For load dump proposal, refer to ISO 16750-2, 4th edition, chapter 4.6.4. |
218 |
|||||||||||||||||||||||||||||||
3. MOTION SENSOR FUNCTIONAL TESTS
|
No |
Test |
Description |
Related requirements |
||||||||||||||||||||||||||||
|
1. |
Administrative examination |
||||||||||||||||||||||||||||||
|
1.1 |
Documentation |
Correctness of documentation |
|
||||||||||||||||||||||||||||
|
2. |
Visual inspection |
||||||||||||||||||||||||||||||
|
2.1. |
Compliance with documentation |
|
|||||||||||||||||||||||||||||
|
2.2. |
Identification/markings |
225, 226, |
|||||||||||||||||||||||||||||
|
2.3 |
Materials |
219 to 223 |
|||||||||||||||||||||||||||||
|
2.4. |
Sealing |
398, 401 to 405 |
|||||||||||||||||||||||||||||
|
3. |
Functional tests |
||||||||||||||||||||||||||||||
|
3.1 |
Sensor identification data |
95 to 97* |
|||||||||||||||||||||||||||||
|
3.2 |
Motion sensor — vehicle unit pairing |
122*, 204 |
|||||||||||||||||||||||||||||
|
3.3 |
Motion detection Motion measurement accuracy |
30 to 35 |
|||||||||||||||||||||||||||||
|
3.4 |
Vehicle unit interface |
02 |
|||||||||||||||||||||||||||||
|
3.5 |
Check that the motion sensor is immune to constant magnetic field. Alternatively, verify that the motion sensor reacts to constant magnetic fields disturbing vehicle motion detection so that a connected VU can detect, record and store sensor faults |
217 |
|||||||||||||||||||||||||||||
|
4. |
Environmental tests |
||||||||||||||||||||||||||||||
|
4.1 |
Operating temperature |
Verify functionality (as defined in test No 3.3) in temperature range [– 40°C; + 135°C] through:
|
213 |
||||||||||||||||||||||||||||
|
4.2 |
Temperature cycles |
Test according to ISO 16750-4: Chapter 5.3.2: Rapid change of temperature with specified transition duration (– 40°C/135 °C, 20 cycles, dwell time 30 min at each temperature) IEC 60068-2-14: Environmental testing; Part 2-14: Tests; Test N: Change of temperature |
213 |
||||||||||||||||||||||||||||
|
4.3 |
Humidity cycles |
Verify functionality (as defined in test No. 3.3) through IEC 60068-2-30, test Db, six 24 hours cycles, each temperature varying from + 25°C to + 55°C and a relative humidity of 97 % at + 25°C and equal to 93 % at + 55°C |
214 |
||||||||||||||||||||||||||||
|
4.4 |
Vibration |
ISO 16750-3: Chapter 4.1.2.6: Test VI: Commercial vehicle, engine, gearbox Mixed mode vibration test including
94 h per axis, including temperature cycle – 20…70°C) This test refers to IEC 60068-2-80: Environmental testing — Part 2-80: Tests — Test Fi: Vibration — Mixed mode |
219 |
||||||||||||||||||||||||||||
|
4.5 |
Mechanical shock |
ISO 16750-3: Chapter 4.2.3: Test VI: Test for devices in or on the gearbox half-sinusoidal shock, acceleration to be agreed in the range 3 000 …15 000 m/s2, pulse duration to be agreed, however < 1 ms, number of shocks: to be agreed This test refers to IEC 60068-2-27: Environmental testing. Part 2: Tests. Test Ea and guidance: Shock |
219 |
||||||||||||||||||||||||||||
|
4.6 |
Protection against water and foreign bodies |
Test according to ISO 20653: Road vehicles — Degree of protection (IP code) — Protection of electrical equipment against foreign objects, water and access (Target value IP 64) |
220, 221 |
||||||||||||||||||||||||||||
|
4.7 |
Reverse polarity protection |
Verify that the motion sensor can withstand an inversion of its power supply |
216 |
||||||||||||||||||||||||||||
|
4.8 |
Short circuit protection |
Verify that input output signals are protected against short circuits to power supply and ground |
216 |
||||||||||||||||||||||||||||
|
5. |
EMC |
||||||||||||||||||||||||||||||
|
5.1 |
radiated emissions and susceptibility |
Verify compliance with Regulation ECE R10 |
218 |
||||||||||||||||||||||||||||
|
5.2 |
Electrostatic discharge |
Compliance with ISO 10605:2008 + Technical Corrigendum:2010 + AMD1:2014: +/– 4kV for contact and +/– 8kV for air discharge |
218 |
||||||||||||||||||||||||||||
|
5.3 |
Conducted transient susceptibility on data lines) |
For 24V versions: compliance with ISO 7637-2 + ECE Regulation No. 10 Rev. 3:
For 12V versions: compliance with ISO 7637-1 + ECE Regulation No. 10 Rev. 3:
Pulse 5 shall be tested only for vehicle units designed to be installed in vehicles for which no external common protection against load dump is implemented For load dump proposal, refer to ISO 16750-2, 4th edition, chapter 4.6.4 |
218 |
||||||||||||||||||||||||||||
4. TACHOGRAPH CARDS FUNCTIONAL TESTS
Tests according to this Section 4,
|
|
no. 5 ‘Protocol tests’, |
|
|
no. 6 ‘Card structure’ and |
|
|
no. 7 ‘Functional tests’ |
can be performed by the evaluator or certifier during the Common Criteria (CC) security certification process for the chip module.
Tests number 2.3 and 4.2 are the same. These are the mechanical tests of the combination card body and chip module. If one of these components (card body, chip module) is changed, then these tests are necessary.
|
No |
Test |
Description |
Related requirements |
||||||||||||||||
|
1. |
Administrative examination |
||||||||||||||||||
|
1.1 |
Documentation |
Correctness of documentation |
|
||||||||||||||||
|
2 |
Card Body |
||||||||||||||||||
|
2.1 |
Printed Design |
Make sure that all features for protection and visible data are correctly printed on the card and compliant. [Designator] Annex 1C, chapter 4.1 ‘Visible data’, 227) The front page shall contain: the words ‘Driver card’ or ‘Control card’ or ‘Workshop card’ or ‘Company card’ printed in capital letters in the official language or languages of the Member State issuing the card, according to the type of the card. [Member State name] Annex 1C, chapter 4.1 ‘Visible data’, 228) The front page shall contain: the name of the Member State issuing the card (optional). [Sign] Annex 1C, chapter 4.1 ‘Visible data’, 229) The front page shall contain: the distinguishing sign of the Member State issuing the card, printed in negative in a blue rectangle and encircled by 12 yellow stars. [Enumeration] Annex 1C, chapter 4.1 ‘Visible data’, 232) The reverse page shall contain: an explanation of the numbered items which appear on the front page of the card. [Colour] Annex 1C, chapter 4.1 ‘Visible data’, 234) Tachograph cards shall be printed with the following background predominant colours:
[Security] Annex 1C, chapter 4.1 ‘Visible data’, 235) Tachograph cards shall bear at least the following features for protection of the card body against counterfeiting and tampering:
[Markings] Annex 1C, chapter 4.1 ‘Visible data’, 236) Member States may add colours or markings, such as national symbols and security features. [Approval mark] Tachograph cards shall contain an approval mark. The approval mark shall be made up of:
|
227 to 229, 232, 234 to 236 |
||||||||||||||||
|
2.2 |
Mechanical Tests |
[Card size] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [5] Dimension of card, [5.1] Card size, [5.1.1] Card dimensions and tolererances, card type ID-1 Unused card [Card edges] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [5] Dimension of card, [5.1] Card size, [5.1.2] Card edges [Card construction] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [6] Card construction [Card materials] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [7] Card materials [Bending stiffness] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.1] Bending stiffness [Toxicity] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.3] Toxicity [Resistance to chemicals] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.4] Resistance to chemicals [Card stability] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.5] Card dimensional stability and warpage with temperature and humidity [Light] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.6] Light [Durability] Annex 1C, chapter 4.4 ‘Environmental and electrical specifications’, 241) Tachograph cards shall be capable of operating correctly for a five-year period if used within the environmental and electrical specifications. [Peel strength] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.8] Peel strength [Adhesion or blocking] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.9] Adhesion or blocking [Warpage] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.11] Overall card warpage [Resistance to heat] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.12] Resistance to heat [Surface distortions] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.13] Surface distortions [Contamination] Tachograph cards must conform to standard ISO/IEC 7810, Identification cards — Physical characteristics, [8] Card characteristics, [8.14] Contamination and interaction of card components |
240, 243 ISO/IEC 7810 |
||||||||||||||||
|
2.3 |
Mechanical tests with chip module embedded |
[Bending] Tachograph cards must conform to standard ISO/IEC 7810:2003/Amd. 1:2009, Identification cards — Physical characteristics, Amendment 1: Criteria for cards containing integrated circuits [9.2] Dynamic bending stress Total number of bending cycles: 4 000 . [Torsion] Tachograph cards must conform to standard ISO/IEC 7810:2003/Amd. 1:2009, Identification cards — Physical characteristics, Amendment 1: Criteria for cards containing integrated circuits [9.3] Dynamic torsional stress Total number of torsion cycles: 4 000 . |
ISO/IEC 7810 |
||||||||||||||||
|
3 |
Module |
||||||||||||||||||
|
3.1 |
Module |
Module is the chip encapsulation and the contact plate. [Surface profile] Tachograph cards must conform to standard ISO/IEC 7816-1:2011, Identification cards — Integrated circuit cards — Part 1: Cards with contacts — Physical characteristics [4.2] Surface profile of contacts [Mechanical strength] Tachograph cards must conform to standard ISO/IEC 7816-1:2011, Identification cards — Integrated circuit cards — Part 1: Cards with contacts — Physical characteristics [4.3] Mechanical strength (of a card and contacts) [Electrical resistance] Tachograph cards must conform to standard ISO/IEC 7816-1:2011, Identification cards — Integrated circuit cards — Part 1: Cards with contacts — Physical characteristics [4.4] Electrical resistance (of contacts) [Dimension] Tachograph cards must conform to standard ISO/IEC 7816-2:2007, Identification cards — Integrated circuit cards — Part 2: Cards with contacts — Dimension and location of the contacts [3] Dimension of the contacts [Location] Tachograph cards must conform to standard ISO/IEC 7816-2:2007, Identification cards — Integrated circuit cards — Part 2: Cards with contacts — Dimension and location of the contacts [4] Number and location of the contacts In case of modules with six contacts, contact ‘C4’ and ‘C8’ are not part of this test requirement. |
ISO/IEC 7816 |
||||||||||||||||
|
4 |
Chip |
||||||||||||||||||
|
4.1 |
Chip |
[Operating temperature] The Tachograph card chip shall operate in an ambient temperature range between – 25 °C and + 85 °C. [Temperature and humidity] Annex 1C, chapter 4.4 ‘Environmental and electrical specifications’, 241) Tachograph cards shall be capable of operating correctly in all the climatic conditions normally encountered in Community territory and at least in the temperature range – 25°C to + 70°C with occasional peaks of up to + 85°C, ‘occasional’ meaning not more than 4 hours each time and not over 100 times during the life time of the card. The Tachograph cards are exposed in consecutive steps to the following temperatures and humidities for the given time. After each step the Tachograph cards are tested for electrical functionality.
[Humidity] Annex 1C, chapter 4.4 ‘Environmental and electrical specifications’, 242) Tachograph cards shall be capable of operating correctly in the humidity range 10 % to 90 %. [Electromagnetic compatibility — EMC] Annex 1C, chapter 4.4 ‘Environmental and electrical specifications’ 244) During operation, Tachograph cards shall conform to ECE R10 related to electromagnetic compatibility. [Static electricity] Annex 1C, chapter 4.4 ‘Environmental and electrical specifications’, 244) During operation, Tachograph cards shall be protected against electrostatic discharges. Tachograph cards must conform to standard ISO/IEC 7810:2003/Amd. 1:2009, Identification cards — Physical characteristics, Amendment 1: Criteria for cards containing integrated circuits [9.4] Static electricity [9.4.1] Contact IC cards Test voltage: 4 000 V. [X-rays] Tachograph cards must conform to standard ISO/IEC 7810:2003/Amd. 1:2009, Identification cards — Physical characteristics, Amendment 1: Criteria for cards containing integrated circuits [9.1] X-rays [Ultraviolet light] ISO/IEC 10373-1:2006, Identification cards — Test methods — Part 1: General characteristics [5.11] Ultraviolet light [3-wheel] Tachograph cards must conform to standard ISO/IEC 10373-1:2006/Amd. 1:2012, Identification cards — Test methods — Part 1: General characteristics, Amendment 1 [5.22] ICC — Mechanical strength: 3 wheel test for ICCs with contacts [Wrapping] Tachograph cards must conform to standard MasterCard CQM V2.03:2013 [11.1.3] R-L3-14-8: Wrapping Test Robustness [13.2.1.32] TM-422: Mechanical Reliability: Wrapping Test |
241 to 244 ECE R10 ISO/IEC 7810 ISO/IEC 10373 |
||||||||||||||||
|
4.2 |
Mechanical tests chip module embedded in the card body-> same as 2.3 |
[Bending] Tachograph cards must conform to standard ISO/IEC 7810:2003/Amd. 1:2009, Identification cards — Physical characteristics, Amendment 1: Criteria for cards containing integrated circuits [9.2] Dynamic bending stress Total number of bending cycles: 4 000 . [Torsion] Tachograph cards must conform to standard ISO/IEC 7810:2003/Amd. 1:2009, Identification cards — Physical characteristics, Amendment 1: Criteria for cards containing integrated circuits [9.3] Dynamic torsional stress Total number of torsion cycles: 4 000 . |
ISO/IEC 7810 |
||||||||||||||||
|
5 |
Protocol tests |
||||||||||||||||||
|
5.1 |
ATR |
Check that the ATR is compliant |
ISO/IEC 7816-3 TCS_14, TCS_17, TCS_18 |
||||||||||||||||
|
5.2 |
T=0 |
Check that T=0 protocol is compliant |
ISO/IEC 7816-3 TCS_11, TCS_12, TCS_13, TCS_15 |
||||||||||||||||
|
5.3 |
PTS |
Check that the PTS command is compliant by setting T=1 from T=0. |
ISO/IEC 7816-3 TCS_12, TCS_19, TCS_20, TCS_21 |
||||||||||||||||
|
5.4 |
T=1 |
Check that T=1 protocol is compliant |
ISO/IEC 7816-3 TCS_11, TCS_13, TCS_16 |
||||||||||||||||
|
6 |
Card structure |
||||||||||||||||||
|
6.1 |
|
Test that the file structure of the card is compliant by checking the presence of the mandatory files in the card and their access conditions |
TCS_22 to TCS_28 TCS_140 to TCS_179 |
||||||||||||||||
|
7 |
Functional tests |
||||||||||||||||||
|
7.1 |
Normal processing |
Test at least once each allowed usage of each command (ex: test the UPDATE BINARY command with CLA = ‘00’, CLA = ‘0C’ and with different P1,P2 and Lc parameters) Check that the operations have actually been performed in the card (ex: by reading the file the command has been performed on) |
TCS_29 to TCS_139 |
||||||||||||||||
|
7.2 |
Error messages |
Test at least once each error message (as specified in Appendix 2) for each command Test at least once every generic error (except ‘6400’ integrity errors checked during security certification) |
|||||||||||||||||
|
7.3 |
Cypher suite and standardized domain parameters |
CSM_48, CSM_50 |
|||||||||||||||||
|
8 |
Personalisation |
||||||||||||||||||
|
8.1 |
Optical personalisation |
Annex 1C, chapter 4.1 ‘Visible data’, 230) The front page shall contain: information specific to the card issued. Annex 1C, chapter 4.1 ‘Visible data’, 231) The front page shall contain: dates using a ‘dd/mm/yyyy’ or ‘dd.mm.yyyy’ format (day, month, year). Annex 1C, chapter 4.1 ‘Visible data’, 235) Tachograph cards shall bear at least the following features for protection of the card body against counterfeiting and tampering:
|
230, 231, 235 |
||||||||||||||||
5. EXTERNAL GNSS FACILITY TESTS
|
No |
Test |
Description |
Related requirements |
|||||||||||||||||||||||||||||
|
1. |
Administrative examination |
|||||||||||||||||||||||||||||||
|
1.1 |
Documentation |
Correctness of documentation |
|
|||||||||||||||||||||||||||||
|
2. |
Visual inspection for external GNSS facility |
|||||||||||||||||||||||||||||||
|
2.1. |
Compliance with documentation |
|
||||||||||||||||||||||||||||||
|
2.2. |
Identification/markings |
224 to 226 |
||||||||||||||||||||||||||||||
|
2.3 |
Materials |
219 to 223 |
||||||||||||||||||||||||||||||
|
3. |
Functional tests |
|||||||||||||||||||||||||||||||
|
3.1 |
Sensor identification data |
98,99 |
||||||||||||||||||||||||||||||
|
3.2 |
External GNSS module — vehicle unit coupling |
123, 205 |
||||||||||||||||||||||||||||||
|
3.3 |
GNSS position |
36, 37 |
||||||||||||||||||||||||||||||
|
3.4 |
Vehicle unit interface when the GNSS receiver is external to the Vehicle Unit |
03 |
||||||||||||||||||||||||||||||
|
3.5 |
Cypher suite and standardized domain parameters |
CSM_48, CSM_50 |
||||||||||||||||||||||||||||||
|
4. |
Environmental tests |
|||||||||||||||||||||||||||||||
|
4.1 |
Temperature |
Verify functionality through:
|
213 |
|||||||||||||||||||||||||||||
|
4.2 |
Humidity |
Verify that the vehicle unit can withstand a cyclic damp (heat test) through IEC 60068-2-30, test Db, six 24 hours cycles, each temperature varying from + 25 °C to + 55 °C and a relative humidity of 97 % at + 25 °C and equal to 93 % at + 55 °C |
214 |
|||||||||||||||||||||||||||||
|
4.3 |
Mechanical |
The tests described above are performed on different samples of the equipment type being tested. |
219 |
|||||||||||||||||||||||||||||
|
4.4 |
Protection against water and foreign bodies |
Test according to ISO 20653: Road vehicles — Degree of protection (IP code) — Protection of electrical equipment against foreign objects, water and access (No change in parameters) |
220, 221 |
|||||||||||||||||||||||||||||
|
4.5 |
Over-voltage protection |
Verify that the vehicle unit can withstand a power supply of: |
216 |
|||||||||||||||||||||||||||||
|
24 V versions: |
34 V at + 40 °C 1 hour |
|||||||||||||||||||||||||||||||
|
12V versions: |
17 V at + 40 °C 1 hour |
|||||||||||||||||||||||||||||||
|
( ISO 16750-2, chapter 4.3) |
||||||||||||||||||||||||||||||||
|
4.6 |
Reverse polarity protection |
Verify that the vehicle unit can withstand an inversion of its power supply (ISO 16750-2, chapter 4.7) |
216 |
|||||||||||||||||||||||||||||
|
4.7 |
Short-circuit protection |
Verify that input output signals are protected against short circuits to power supply and ground (ISO 16750-2, chapter 4.10]) |
216 |
|||||||||||||||||||||||||||||
|
5 |
EMC tests |
|||||||||||||||||||||||||||||||
|
5.1 |
Radiated emissions and susceptibility |
Compliance with Regulation ECE R10 |
218 |
|||||||||||||||||||||||||||||
|
5.2 |
Electrostatic discharge |
Compliance with ISO 10605:2008 + Technical Corrigendum: 2010 + AMD1:2014: +/– 4kV for contact and +/– 8kV for air discharge |
218 |
|||||||||||||||||||||||||||||
|
5.3 |
Conducted transient susceptibility on power supply |
For 24V versions: compliance with ISO 7637-2 + ECE Regulation No. 10 Rev. 3:
For 12V versions: compliance with ISO 7637-1 + ECE Regulation No. 10 Rev. 3:
Pulse 5 shall be tested only for vehicle units designed to be installed in vehicles for which no external common protection against load dump is implemented For load dump proposal, refer to ISO 16750-2, 4th edition, chapter 4.6.4. |
218 |
|||||||||||||||||||||||||||||
6. REMOTE COMMUNICATION FACILITY TESTS
|
No |
Test |
Description |
Related requirements |
||||||||||||||||||||||||||||
|
1. |
Administrative examination |
||||||||||||||||||||||||||||||
|
1.1 |
Documentation |
Correctness of documentation |
|
||||||||||||||||||||||||||||
|
2. |
Visual inspection |
||||||||||||||||||||||||||||||
|
2.1. |
Compliance with documentation |
|
|||||||||||||||||||||||||||||
|
2.2. |
Identification/markings |
225, 226 |
|||||||||||||||||||||||||||||
|
2.3 |
Materials |
219 to 223 |
|||||||||||||||||||||||||||||
|
4. |
Environmental tests |
||||||||||||||||||||||||||||||
|
4.1 |
Temperature |
Verify functionality through:
|
213 |
||||||||||||||||||||||||||||
|
4.4 |
Protection against water and foreign bodies |
Test according to ISO 20653: Road vehicles — Degree of protection (IP code) — Protection of electrical equipment against foreign objects, water and access (targeted value IP40) |
220, 221 |
||||||||||||||||||||||||||||
|
5 |
EMC tests |
||||||||||||||||||||||||||||||
|
5.1 |
Radiated emissions and susceptibility |
Compliance with Regulation ECE R10 |
218 |
||||||||||||||||||||||||||||
|
5.2 |
Electrostatic discharge |
Compliance with ISO 10605:2008 + Technical Corrigendum:2010 + AMD1:2014: +/– 4kV for contact and +/– 8kV for air discharge |
218 |
||||||||||||||||||||||||||||
|
5.3 |
Conducted transient susceptibility on power supply |
For 24V versions: compliance with ISO 7637-2 + ECE Regulation No. 10 Rev. 3:
For 12V versions: compliance with ISO 7637-1 + ECE Regulation No. 10 Rev. 3:
Pulse 5 shall be tested only for vehicle units designed to be installed in vehicles for which no external common protection against load dump is implemented For load dump proposal, refer to ISO 16750-2, 4th edition, chapter 4.6.4. |
218 |
||||||||||||||||||||||||||||
7. PAPER FUNCTIONAL TESTS
|
No |
Test |
Description |
Related requirements |
|
1. |
Administrative examination |
||
|
1.1 |
Documentation |
Correctness of documentation |
|
|
2 |
General Tests |
||
|
2.1 |
Number of characters per line |
Visual inspection of printouts. |
172 |
|
2.2 |
Minimum character size |
Visual inspection of printout and character inspection. |
173 |
|
2.3 |
Supported character sets |
The printer shall support characters specified in Appendix 1 Chapter 4 ‘Character sets’. |
174 |
|
2.4 |
Printouts definition |
Check of tachograph type approval and visual inspection of printouts |
174 |
|
2.5 |
Legibility and identification of printouts |
Inspection of printouts Demonstrated by test reports and test protocols by manufacturer. All homologation number(s) of tachographs with which the printer paper may be used are imprinted on the paper. |
175, 177, 178 |
|
2.6 |
Addition of handwritten notes |
Visual inspection: Field for signature of the driver is available. Fields for additional other handwritten entries are available. |
180 |
|
2.7 |
Additional details on paper faces. |
Paper's face and reverse side may feature additional details and information. These additional details and information may not interfere with the legibility of the printouts. Visual inspection. |
177, 178 |
|
3 |
Storage Tests |
||
|
3.1 |
Dry Heat |
Preconditioning: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity Test environment: 72 hours at + 70 °C ± 2 °C Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 IEC 60068-2-2-Bb |
|
2.2 |
Damp Heat |
Preconditioning: 16 hours at + 23 °C ± 2 °C/55 % ±3 % relative humidity Test environment: 144 hours at + 55 °C ± 2 °C and 93 % ± 3 % r.h. Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 IEC 60068-2-78-Cab |
|
4 |
Paper In-Service Tests |
||
|
4.1 |
Humidity resistance background (unprinted paper) |
Preconditioning: 16 hours at + 23 °C ± 2 °C/55 % ±3 % relative humidity Test environment: 144 hours at + 55 °C ± 2 °C and 93 % ± 3 % r.h. Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 IEC 60068-2-78-Cab |
|
4.2 |
Printability |
Preconditioning: 24 hours at + 40 °C ± 2 °C/93 % ± 3 % relative humidity Test environment: printout produced at + 23 °C ± 2 °C Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 |
|
4.3 |
Heat resistance |
Preconditioning: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity Test environment: 2 hours at + 70 °C ± 2 °C, dry heat Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 IEC 60068-2-2-Bb |
|
4.4 |
Low temperature resistance |
Preconditioning: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity Test environment: 24 hours – 20 °C ± 3 °C, dry cold Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 ISO 60068-2-1-Ab |
|
4.5 |
Light resistance |
Preconditioning: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity Test environment: 100 hours under 5 000 Lux illumination at + 23 °C ± 2 °C/55 % ± 3 % relative humidity Recovery: 16 hours at + 23 °C ± 2 °C/55 % ± 3 % relative humidity |
176, 178 |
Legibility criteria for tests 3.x and 4.x:
Printout legibility is assured if optical densities comply with the following limits:
|
|
Printed characters: min. 1,0 |
|
|
Background (unprinted paper): max. 0,2 |
Optical densities of the resulting printouts shall be measured according to DIN EN ISO 534.
Printouts shall show no dimensional changes and remain clearly legible.
8. INTEROPERABILITY TESTS
|
No |
Test |
Description |
| 9.1 Interoperability tests between vehicle units and tachograph cards |
||
|
1 |
Mutual authentication |
Check that the mutual authentication between the vehicle unit and the tachograph card runs normally |
|
2 |
Write/read tests |
Execute a typical activity scenario on the vehicle unit. The scenario shall be adapted to the type of card being tested and involve writings in as many EFs as possible in the card Verify through a vehicle unit downloading that all corresponding recordings have been properly made Verify through a card downloading that all corresponding recordings have been properly made Verify through daily printouts that all corresponding recordings can be properly read |
| 9.2 Interoperability tests between vehicle units and motion sensors |
||
|
1 |
Pairing |
Check that the pairing between the vehicle units and the motion sensors runs normally |
|
2 |
Activity tests |
Execute a typical activity scenario on the motion sensor. The scenario shall involve a normal activity and creating as many events or faults as possible. Verify through a vehicle unit downloading that all corresponding recordings have been properly made Verify through a card downloading that all corresponding recordings have been properly made Verify through a daily printout that all corresponding recordings can be properly read |
| 9.3 Interoperability tests between vehicle units and external GNSS facilities (when applicable) |
||
|
1 |
Mutual Authentication |
Check that the mutual authentication (coupling) between the vehicle unit and the external GNSS module runs normally. |
|
2 |
Activity tests |
Execute a typical activity scenario on the external GNSS. The scenario shall involve a normal activity and creating as many events or faults as possible. Verify through a vehicle unit downloading that all corresponding recordings have been properly made Verify through a card downloading that all corresponding recordings have been properly made Verify through a daily printout that all corresponding recordings can be properly read |
Appendix 10
SECURITY REQUIREMENTS
This appendix specifies the IT security requirements for the smart tachograph system components (second-generation tachograph).
|
SEC_001 |
The following components of the smart tachograph system shall be security certified according to the Common Criteria scheme:
|
|
SEC_002 |
The minimum IT security requirements to be met by each component needing to be security certified shall be defined in a component Protection Profile, according to the Common Criteria scheme. |
|
SEC_003 |
The European Commission shall make sure that four Protection Profiles compliant with this Annex are sponsored, developed, approved by the governmental IT security certification bodies organised within the Joint Interpretation Working Group (JIWG) which is supporting the mutual recognition of certificates under the umbrella of the European SOGIS-MRA (Agreement on Mutual Recognition of Information Technology Security Evaluation Certificates) and registered:
|
The Protection Profile for vehicle unit shall address the cases when the VU is designed to be used or not with an external GNSS facility. In the former case, the security requirements of the external GNSS facility are provided in the dedicated Protection Profile.
|
SEC_004 |
Component manufacturers shall refine and complete the appropriate component Protection Profile as necessary, without amending or deleting existing threats, objectives, procedural means and security enforcing functions specifications, in order to build a Security Target against which they shall seek the security certification of the component. |
|
SEC_005 |
Strict conformance of such specific Security Target with the corresponding Protection Profile must be stated during the evaluation process. |
|
SEC_006 |
The assurance level for each Protection Profile shall be EAL4 augmented by the assurance components ATE_DPT.2 and AVA_VAN.5. |
Appendix 11
COMMON SECURITY MECHANISMS
TABLE OF CONTENTS
| PREAMBLE | 340 |
|
PART A |
FIRST-GENERATION TACHOGRAPH SYSTEM | 341 |
|
1. |
INTRODUCTION | 341 |
|
1.1. |
References | 341 |
|
1.2. |
Notations and abbreviated terms | 341 |
|
2. |
CRYPTOGRAPHIC SYSTEMS AND ALGORITHMS | 343 |
|
2.1. |
Cryptographic systems | 343 |
|
2.2. |
Cryptographic algorithms | 343 |
|
2.2.1 |
RSA algorithm | 343 |
|
2.2.2 |
Hash algorithm | 343 |
|
2.2.3 |
Data Encryption Algorithm | 343 |
|
3. |
KEYS AND CERTIFICATES | 343 |
|
3.1. |
Keys generation and distribution | 343 |
|
3.1.1 |
RSA Keys generation and distribution | 343 |
|
3.1.2 |
RSA Test keys | 345 |
|
3.1.3 |
Motion sensor keys | 345 |
|
3.1.4 |
T-DES session keys generation and distribution | 345 |
|
3.2. |
Keys | 345 |
|
3.3. |
Certificates | 345 |
|
3.3.1 |
Certificates content | 346 |
|
3.3.2 |
Certificates issued | 348 |
|
3.3.3 |
Certificate verification and unwrapping | 349 |
|
4. |
MUTUAL AUTHENTICATION MECHANISM | 349 |
|
5. |
VU-CARDS DATA TRANSFER CONFIDENTIALITY, INTEGRITY AND AUTHENTICATION MECHANISMS | 352 |
|
5.1. |
Secure Messaging | 352 |
|
5.2. |
Treatment of Secure Messaging errors | 354 |
|
5.3. |
Algorithm to compute Cryptographic Checksums | 354 |
|
5.4. |
Algorithm to compute cryptograms for confidentiality DOs | 355 |
|
6. |
DATA DOWNLOAD DIGITAL SIGNATURE MECHANISMS | 355 |
|
6.1. |
Signature generation | 355 |
|
6.2. |
Signature verification | 356 |
|
PART B |
SECOND-GENERATION TACHOGRAPH SYSTEM | 357 |
|
7. |
INTRODUCTION | 357 |
|
7.1. |
References | 357 |
|
7.2. |
Notations and Abbreviations | 357 |
|
7.3. |
Definitions | 359 |
|
8. |
CRYPTOGRAPHIC SYSTEMS AND ALGORITHMS | 359 |
|
8.1. |
Cryptographic Systems | 359 |
|
8.2. |
Cryptographic Algorithms | 360 |
|
8.2.1 |
Symmetric Algorithms | 360 |
|
8.2.2 |
Asymmetric Algorithms and Standardized Domain Parameters | 360 |
|
8.2.3 |
Hashing algorithms | 361 |
|
8.2.4 |
Cipher Suites | 361 |
|
9. |
KEYS AND CERTIFICATES | 361 |
|
9.1. |
Asymmetric Key Pairs and Public Key Certificates | 361 |
|
9.1.1 |
General | 361 |
|
9.1.2 |
European Level | 362 |
|
9.1.3 |
Member State Level | 362 |
|
9.1.4 |
Equipment Level: Vehicle Units | 363 |
|
9.1.5 |
Equipment Level: Tachograph Cards | 365 |
|
9.1.6 |
Equipment Level: External GNSS Facilities | 366 |
|
9.1.7 |
Overview: Certificate Replacement | 367 |
|
9.2. |
Symmetric Keys | 368 |
|
9.2.1 |
Keys for Securing VU — Motion Sensor Communication | 368 |
|
9.2.2 |
Keys for Securing DSRC Communication | 372 |
|
9.3. |
Certificates | 375 |
|
9.3.1 |
General | 375 |
|
9.3.2 |
Certificate Content | 375 |
|
9.3.3 |
Requesting Certificates | 377 |
|
10. |
VU- CARD MUTUAL AUTHENTICATION AND SECURE MESSAGING | 378 |
|
10.1. |
General | 378 |
|
10.2. |
Mutual Certificate Chain Verification | 379 |
|
10.2.1 |
Card Certificate Chain Verification by VU | 379 |
|
10.2.2 |
VU Certificate Chain Verification by Card | 381 |
|
10.3. |
VU Authentication | 384 |
|
10.4. |
Chip Authentication and Session Key Agreement | 385 |
|
10.5. |
Secure Messaging | 387 |
|
10.5.1 |
General | 387 |
|
10.5.2 |
Secure Message Structure | 388 |
|
10.5.3 |
Secure Messaging Session Abortion | 391 |
|
11. |
VU — EXTERNAL GNSS FACILITY COUPLING, MUTUAL AUTHENTICATION AND SECURE MESSAGING | 392 |
|
11.1. |
General | 392 |
|
11.2. |
VU and External GNSS Facility Coupling | 393 |
|
11.3. |
Mutual Certificate Chain Verification | 393 |
|
11.3.1 |
General | 393 |
|
11.3.2 |
During VU — EGF Coupling | 393 |
|
11.3.3 |
During Normal Operation | 394 |
|
11.4. |
VU Authentication, Chip Authentication and Session Key Agreement | 395 |
|
11.5. |
Secure Messaging | 395 |
|
12. |
VU — MOTION SENSOR PAIRING AND COMMUNICATION | 396 |
|
12.1. |
General | 396 |
|
12.2. |
VU — Motion Sensor Pairing Using Different Key Generations | 396 |
|
12.3. |
VU — Motion Sensor Pairing and Communication using AES | 397 |
|
12.4. |
VU — Motion Sensor Pairing For Different Equipment Generations | 399 |
|
13. |
SECURITY FOR REMOTE COMMUNICATION OVER DSRC | 399 |
|
13.1. |
General | 399 |
|
13.2. |
Tachograph Payload Encryption and MAC Generation | 400 |
|
13.3. |
Verification and Decryption of Tachograph Payload | 401 |
|
14. |
SIGNING DATA DOWNLOADS AND VERIFYING SIGNATURES | 401 |
|
14.1. |
General | 401 |
|
14.2. |
Signature generation | 402 |
|
14.3. |
Signature verification | 402 |
PREAMBLE
This Appendix specifies the security mechanisms ensuring
|
— |
mutual authentication between different components of the tachograph system. |
|
— |
confidentiality, integrity, authenticity and/or non-repudiation of data transferred between different components of the tachograph system or downloaded to external storage media. |
This Appendix consists of two parts. Part A defines the security mechanisms for the first-generation tachograph system (digital tachograph). Part B defines the security mechanisms for the second-generation tachograph system (smart tachograph).
The mechanisms specified in Part A of this Appendix shall apply if at least one of the components of the tachograph system involved in a mutual authentication and/or data transfer process is of the first generation.
The mechanisms specified in Part B of this Appendix shall apply if both components of the tachograph system involved in the mutual authentication and/or data transfer process are of the second generation.
Appendix 15 provides more information regarding the use of first generation components in combination with second-generation components.
PART A
FIRST-GENERATION TACHOGRAPH SYSTEM
1. INTRODUCTION
1.1. References
The following references are used in this Appendix:
|
SHA-1 |
National Institute of Standards and Technology (NIST). FIPS Publication 180-1: Secure Hash Standard. April 1995. |
|
PKCS1 |
RSA Laboratories. PKCS # 1: RSA Encryption Standard. Version 2.0. October 1998. |
|
TDES |
National Institute of Standards and Technology (NIST). FIPS Publication 46-3: Data Encryption Standard. Draft 1999. |
|
TDES-OP |
ANSI X9.52, Triple Data Encryption Algorithm Modes of Operation. 1998. |
|
ISO/IEC 7816-4 |
Information Technology — Identification cards — Integrated circuit(s) cards with contacts — Part 4: Interindustry commands for interexchange. First edition: 1995 + Amendment 1: 1997. |
|
ISO/IEC 7816-6 |
Information Technology — Identification cards — Integrated circuit(s) cards with contacts — Part 6: Interindustry data elements. First edition: 1996 + Cor 1: 1998. |
|
ISO/IEC 7816-8 |
Information Technology — Identification cards — Integrated circuit(s) cards with contacts — Part 8: Security related interindustry commands. First edition 1999. |
|
ISO/IEC 9796-2 |
Information Technology — Security techniques — Digital signature schemes giving message recovery — Part 2: Mechanisms using a hash function. First edition: 1997. |
|
ISO/IEC 9798-3 |
Information Technology — Security techniques — Entity authentication mechanisms — Part 3: Entity authentication using a public key algorithm. Second edition 1998. |
|
ISO 16844-3 |
Road vehicles — Tachograph systems — Part 3: Motion sensor interface. |
1.2. Notations and abbreviated terms
The following notations and abbreviated terms are used in this Appendix:
|
(Ka, Kb, Kc) |
a key bundle for use by the Triple Data Encryption Algorithm, |
|
CA |
Certification Authority, |
|
CAR |
Certification Authority Reference, |
|
CC |
Cryptographic Checksum, |
|
CG |
Cryptogram, |
|
CH |
Command Header, |
|
CHA |
Certificate Holder Authorisation, |
|
CHR |
Certificate Holder Reference, |
|
D() |
Decryption with DES, |
|
DE |
Data Element, |
|
DO |
Data Object, |
|
d |
RSA private key, private exponent, |
|
e |
RSA public key, public exponent, |
|
E() |
Encryption with DES, |
|
EQT |
Equipment, |
|
Hash() |
hash value, an output of Hash, |
|
Hash |
hash function, |
|
KID |
Key Identifier, |
|
Km |
TDES key. Master Key defined in ISO 16844-3. |
|
KmVU |
TDES key inserted in vehicle units. |
|
KmWC |
TDES key inserted in workshop cards. |
|
m |
message representative, an integer between 0 and n-1, |
|
n |
RSA keys, modulus, |
|
PB |
Padding Bytes, |
|
PI |
Padding Indicator byte (for use in Cryptogram for confidentiality DO), |
|
PV |
Plain Value, |
|
s |
signature representative, an integer between 0 and n-1, |
|
SSC |
Send Sequence Counter, |
|
SM |
Secure Messaging, |
|
TCBC |
TDEA Cipher Block Chaining Mode of Operation |
|
TDEA |
Triple Data Encryption Algorithm, |
|
TLV |
Tag Length Value, |
|
VU |
Vehicle Unit, |
|
X.C |
the certificate of user X issued by a certification authority, |
|
X.CA |
a certification authority of user X, |
|
X.CA.PK o X.C |
the operation of unwrapping a certificate to extract a public key. It is an infix operator, whose left operand is the public key of a certification authority, and whose right operand is the certificate issued by that certification authority. The outcome is the public key of the user X whose certificate is the right operand, |
|
X.PK |
RSA public key of a user X, |
|
X.PK[I] |
RSA encipherment of some information I, using the public key of user X, |
|
X.SK |
RSA private key of a user X, |
|
X.SK[I] |
RSA encipherment of some information I, using the private key of user X, |
|
‘xx’ |
an Hexadecimal value, |
|
|| |
concatenation operator. |
2. CRYPTOGRAPHIC SYSTEMS AND ALGORITHMS
2.1. Cryptographic systems
|
CSM_001 |
Vehicle units and tachograph cards shall use a classical RSA public-key cryptographic system to provide the following security mechanisms:
|
|
CSM_002 |
Vehicle units and tachograph cards shall use a Triple DES symmetric cryptographic system to provide a mechanism for data integrity during user data exchange between vehicle units and tachograph cards, and to provide, where applicable, confidentiality of data exchange between vehicle units and tachograph cards. |
2.2. Cryptographic algorithms
2.2.1 RSA algorithm
|
CSM_003 |
The RSA algorithm is fully defined by the following relations:
A more comprehensive description of the RSA function can be found in reference [PKCS1]. Public exponent, e, for RSA calculations is an integer between 3 and n-1 satisfying gcd(e, lcm(p-1, q-1))=1. |
2.2.2 Hash algorithm
|
CSM_004 |
The digital signature mechanisms shall use the SHA-1 hash algorithm as defined in reference [SHA-1]. |
2.2.3 Data Encryption Algorithm
|
CSM_005 |
DES based algorithms shall be used in Cipher Block Chaining mode of operation. |
3. KEYS AND CERTIFICATES
3.1. Keys generation and distribution
3.1.1 RSA Keys generation and distribution
|
CSM_006 |
RSA keys shall be generated through three functional hierarchical levels:
|
|
CSM_007 |
At European level, a single European key pair (EUR.SK and EUR.PK) shall be generated. The European private key shall be used to certify the Member States public keys. Records of all certified keys shall be kept. These tasks shall be handled by a European Certification Authority, under the authority and responsibility of the European Commission. |
|
CSM_008 |
At Member State level, a Member State key pair (MS.SK and MS.PK) shall be generated. Member States public keys shall be certified by the European Certification Authority. The Member State private key shall be used to certify public keys to be inserted in equipment (vehicle unit or tachograph card). Records of all certified public keys shall be kept with the identification of the equipment to which it is intended. These tasks shall be handled by a Member State Certification Authority. A Member State may regularly change its key pair. |
|
CSM_009 |
At equipment level, one single key pair (EQT.SK and EQT.PK) shall be generated and inserted in each equipment. Equipment public keys shall be certified by a Member State Certification Authority. These tasks may be handled by equipment manufacturers, equipment personalisers or Member State authorities. This key pair is used for authentication, digital signature and encipherement services |
|
CSM_010 |
Private keys confidentiality shall be maintained during generation, transport (if any) and storage. The following picture summarises the data flow of this process:
|
3.1.2 RSA Test keys
|
CSM_011 |
For the purpose of equipment testing (including interoperability tests) the European Certification Authority shall generate a different single European test key pair and at least two Member State test key pairs, the public keys of which shall be certified with the European private test key. Manufacturers shall insert, in equipment undergoing type approval tests, test keys certified by one of these Member State test keys. |
3.1.3 Motion sensor keys
The confidentiality of the three Triple DES keys described below shall be appropriately maintained during generation, transport (if any) and storage.
In order to support tachograph components compliant with ISO 16844, the European Certification Authority and the Member State Certification Authorities shall, in addition, ensure the following:
|
CSM_036 |
The European Certification authority shall generate KmVU and KmWC, two independent and unique Triple DES keys, and generate Km as: Km = KmVU XOR KmWC
. The European Certification Authority shall forward these keys, under appropriately secured procedures, to Member States Certification Authorities at their request. |
|
CSM_037 |
Member States Certification Authorities shall:
|
3.1.4 T-DES session keys generation and distribution
|
CSM_012 |
Vehicle units and tachograph cards shall, as a part of the mutual authentication process, generate and exchange necessary data to elaborate a common Triple DES session key. This exchange of data shall be protected for confidentiality through an RSA crypt-mechanism. |
|
CSM_013 |
This key shall be used for all subsequent cryptographic operations using secure messaging. Its validity shall expire at the end of the session (withdrawal of the card or reset of the card) and/or after 240 use (one use of the key = one command using secure messaging sent to the card and associated response). |
3.2. Keys
|
CSM_014 |
RSA keys shall have (whatever the level) the following lengths: modulus n1 024 bits, public exponent e 64 bits maximum, private exponent d1 024 bits. |
|
CSM_015 |
Triple DES keys shall have the form (Ka, Kb, Ka) where Ka and Kb are independent 64 bits long keys. No parity error detecting bits shall be set. |
3.3. Certificates
|
CSM_016 |
RSA Public key certificates shall be ‘non self-descriptive’‘Card Verifiable’ certificates (Ref.: ISO/IEC 7816-8) |
3.3.1 Certificates content
|
CSM_017 |
RSA Public key certificates are built with the following data in the following order:
Notes:
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
3.3.2 Certificates issued
|
CSM_018 |
The certificate issued is a digital signature with partial recovery of the certificate content in accordance with ISO/IEC 9796-2 (except for its annex A4), with the ‘Certification Authority Reference’ appended. X.C = X.CA.SK[‘6A’ || Cr || Hash(Cc) || ‘BC’] || Cn || X.CAR
Notes:
|
|||||||||||||||||||||||||||||||||||||||
3.3.3 Certificate verification and unwrapping
Certificate verification and unwrapping consists in verifying the signature in accordance with ISO/IEC 9796-2, retrieving the certificate content and the public key contained: X.PK = X.CA.PK o X.C, and verifying the validity of the certificate.
|
CSM_019 |
It involves the following steps:
|
4. MUTUAL AUTHENTICATION MECHANISM
Mutual authentication between cards and VUs is based on the following principle:
Each party shall demonstrate to the other that it owns a valid key pair, the public key of which has been certified by a Member State certification authority, itself being certified by the European certification authority.
Demonstration is made by signing with the private key a random number sent by the other party, who must recover the random number sent when verifying this signature.
The mechanism is triggered at card insertion by the VU. It starts with the exchange of certificates and unwrapping of public keys, and ends with the setting of a session key.
|
CSM_020 |
The following protocol shall be used (arrows indicate commands and data exchanged (see Appendix 2)):
|
5. VU-CARDS DATA TRANSFER CONFIDENTIALITY, INTEGRITY AND AUTHENTICATION MECHANISMS
5.1. Secure Messaging
|
CSM_021 |
VU-Cards data transfers integrity shall be protected through Secure Messaging in accordance with references [ISO/IEC 7816-4] and [ISO/IEC 7816-8]. |
|
CSM_022 |
When data need to be protected during transfer, a Cryptographic Checksum Data Object shall be appended to the Data Objects sent within the command or the response. The Cryptographic Checksum shall be verified by the receiver. |
|
CSM_023 |
The cryptographic checksum of data sent within a command shall integrate the command header, and all data objects sent (=>CLA = ‘0C’, and all data objects shall be encapsulated with tags in which b1=1). |
|
CSM_024 |
The response status-information bytes shall be protected by a cryptographic checksum when the response contains no data field. |
|
CSM_025 |
Cryptographic checksums shall be 4 Bytes long. The structure of commands and responses when using secure messaging is therefore the following:
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
5.2. Treatment of Secure Messaging errors
|
CSM_026 |
When the tachograph card recognises an SM error while interpreting a command, then the status bytes must be returned without SM. In accordance with ISO/IEC 7816-4, the following status bytes are defined to indicate SM errors:
|
|
CSM_027 |
When the tachograph card returns status bytes without SM DOs or with an erroneous SM DO, the session must be aborted by the VU. |
5.3. Algorithm to compute Cryptographic Checksums
|
CSM_028 |
Cryptographic checksums are built using a retail MACs in accordance with ANSI X9.19 with DES:
where E() means encryption with DES, and D() means decryption with DES. The four most significant bytes of the cryptographic checksum are transferred |
|
CSM_029 |
The Send Sequence Counter (SSC) shall be initiated during key agreement procedure to: Initial SSC: Rnd3 (4 least significant bytes) || Rnd1 (4 least significant bytes). |
|
CSM_030 |
The Send Sequence Counter shall be increased by 1 each time before a MAC is calculated (i.e. the SSC for the first command is Initial SSC + 1, the SSC for the first response is Initial SSC + 2). The following figure shows the calculation of the retail MAC:
|
5.4. Algorithm to compute cryptograms for confidentiality DOs
|
CSM_031 |
Cryptograms are computed using TDEA in TCBC mode of operation in accordance with references [TDES] and [TDES-OP] and with the Null vector as Initial Value block. The following figure shows the application of keys in TDES:
|
6. DATA DOWNLOAD DIGITAL SIGNATURE MECHANISMS
|
CSM_032 |
The Intelligent Dedicated Equipment (IDE) stores data received from an equipment (VU or card) during one download session within one physical data file. This file must contain the certificates MSi.C and EQT.C. The file contains digital signatures of data blocks as specified in Appendix 7 Data Downloading Protocols. |
|
CSM_033 |
Digital signatures of downloaded data shall use a digital signature scheme with appendix such, that downloaded data may be read without any decipherment if desired. |
6.1. Signature generation
|
CSM_034 |
Data signature generation by the equipment shall follow the signature scheme with appendix defined in reference [PKCS1] with the SHA-1 hash function:
|
6.2. Signature verification
|
CSM_035 |
Data signature verification on downloaded data shall follow the signature scheme with appendix defined in reference [PKCS1] with the SHA-1 hash function. The European public key EUR.PK needs to be known independently (and trusted) by the verifier. The following table illustrates the protocol an IDE carrying a Control card can follow to verify the integrity of data downloaded and stored on the ESM (External Storage media). The control card is used to perform the decipherement of digital signatures. This function may in this case not be implemented in the IDE. The equipment that has downloaded and signed the data to be analysed is denoted EQT.
|
PART B
SECOND-GENERATION TACHOGRAPH SYSTEM
7. INTRODUCTION
7.1. References
The following references are used in this part of this Appendix.
|
AES |
National Institute of Standards and Technology (NIST), FIPS PUB 197: Advanced Encryption Standard (AES), November 26, 2001 |
|
DSS |
National Institute of Standards and Technology (NIST), FIPS PUB 186-4: Digital Signature Standard (DSS), July 2013 |
|
ISO 7816-4 |
ISO/IEC 7816-4, Identification cards — Integrated circuit cards — Part 4: Organization, security and commands for interchange. Third edition 2013-04-15 |
|
ISO 7816-8 |
ISO/IEC 7816-8, Identification cards — Integrated circuit cards — Part 8: Commands for security operations. Second edition 2004-06-01 |
|
ISO 8825-1 |
ISO/IEC 8825-1, Information technology — ASN.1 encoding rules: Specification of Basic Encoding Rules (BER), Canonical Encoding Rules (CER) and Distinguished Encoding Rules (DER). Fourth edition, 2008-12-15 |
|
ISO 9797-1 |
ISO/IEC 9797-1, Information technology — Security techniques — Message Authentication Codes (MACs) — Part 1: Mechanisms using a block cipher. Second edition, 2011-03-01 |
|
ISO 10116 |
ISO/IEC 10116, Information technology — Security techniques — Modes of operation of an n-bit block cipher. Third edition, 2006-02-01 |
|
ISO 16844-3 |
ISO/IEC 16844-3, Road vehicles — Tachograph systems — Part 3: Motion sensor interface. First edition 2004, including Technical Corrigendum 1 2006 |
|
RFC 5480 |
Elliptic Curve Cryptography Subject Public Key Information, March 2009 |
|
RFC 5639 |
Elliptic Curve Cryptography (ECC) — Brainpool Standard Curves and Curve Generation, 2010 |
|
RFC 5869 |
HMAC-based Extract-and-Expand Key Derivation Function (HKDF), May 2010 |
|
SHS |
National Institute of Standards and Technology (NIST), FIPS PUB 180-4: Secure Hash Standard, March 2012 |
|
SP 800-38B |
National Institute of Standards and Technology (NIST), Special Publication 800-38B: Recommendation for Block Cipher Modes of Operation: The CMAC Mode for Authentication, 2005 |
|
TR-03111 |
BSI Technical Guideline TR-03111, Elliptic Curve Cryptography, version 2.00, 2012-06-28 |
7.2. Notations and Abbreviations
The following notations and abbreviated terms are used in this Appendix:
|
AES |
Advanced Encryption Standard |
|
CA |
Certificate Authority |
|
CAR |
Certificate Authority Reference |
|
CBC |
Cipher Block Chaining (mode of operation) |
|
CH |
Command Header |
|
CHA |
Certificate Holder Authorisation |
|
CHR |
Certificate Holder Reference |
|
CV |
Constant Vector |
|
DER |
Distinguished Encoding Rules |
|
DO |
Data Object |
|
DSRC |
Dedicated Short Range Communication |
|
ECC |
Elliptic Curve Cryptography |
|
ECDSA |
Elliptic Curve Digital Signature Algorithm |
|
ECDH |
Elliptic Curve Diffie-Hellman (key agreement algorithm) |
|
EGF |
External GNSS Facility |
|
EQT |
Equipment |
|
IDE |
Intelligent Dedicated Equipment |
|
KM |
Motion Sensor Master Key, allowing the pairing of a Vehicle Unit to a Motion Sensor |
|
KM-VU |
Key inserted in vehicle units, allowing a VU to derive the Motion Sensor Master Key if a workshop card is inserted into the VU |
|
KM-WC |
Key inserted in workshop cards, allowing a VU to derive the Motion Sensor Master Key if a workshop card is inserted into the VU |
|
MAC |
Message Authentication Code |
|
MoS |
Motion Sensor |
|
MSB |
Most Significant Bit |
|
PKI |
Public Key Infrastructure |
|
RCF |
Remote Communication Facility |
|
SSC |
Send Sequence Counter |
|
SM |
Secure Messaging |
|
TDES |
Triple Data Encryption Standard |
|
TLV |
Tag Length Value |
|
VU |
Vehicle Unit |
|
X.C |
the public key certificate of user X |
|
X.CA |
the certificate authority that issued the certificate of user X |
|
X.CAR |
the certificate authority reference mentioned in the certificate of user X |
|
X.CHR |
the certificate holder reference mentioned in the certificate of user X |
|
X.PK |
public key of user X |
|
X.SK |
private key of user X |
|
X.PKeph |
ephemeral public key of user X |
|
X.SKeph |
ephemeral private key of user X |
|
‘xx’ |
a hexadecimal value |
|
|| |
concatenation operator |
7.3. Definitions
The definitions of terms used in this Appendix are included in section I of Annex 1C.
8. CRYPTOGRAPHIC SYSTEMS AND ALGORITHMS
8.1. Cryptographic Systems
|
CSM_38 |
Vehicle units and tachograph cards shall use an elliptic curve-based public-key cryptographic system to provide the following security services:
|
|
CSM_39 |
Vehicle units and external GNSS facilities shall use an elliptic curve-based public-key cryptographic system to provide the following security services:
|
|
CSM_40 |
Vehicle units and tachograph cards shall use an AES-based symmetric cryptographic system to provide the following security services:
|
|
CSM_41 |
Vehicle units and external GNSS facilities shall use an AES-based symmetric cryptographic system to provide the following security services:
|
|
CSM_42 |
Vehicle units and motion sensors shall use an AES-based symmetric cryptographic system to provide the following security services:
|
|
CSM_43 |
Vehicle units and control cards shall use an AES-based symmetric cryptographic system to provide the following security services on the remote communication interface:
Notes:
|
8.2. Cryptographic Algorithms
8.2.1 Symmetric Algorithms
|
CSM_44 |
Vehicle units, tachograph cards, motion sensors and external GNSS facilities shall support the AES algorithm as defined in [AES], with key lengths of 128, 192 and 256 bits. |
8.2.2 Asymmetric Algorithms and Standardized Domain Parameters
|
CSM_45 |
Vehicle units, tachograph cards and external GNSS facilities shall support elliptic curve cryptography with a key size of 256, 384 and 512/521 bits. |
|
CSM_46 |
Vehicle units, tachograph cards and external GNSS facilities shall support the ECDSA signing algorithm, as specified in [DSS]. |
|
CSM_47 |
Vehicle units, tachograph cards and external GNSS facilities shall support the ECKA-EG key agreement algorithm, as specified in [TR 03111]. |
|
CSM_48 |
Vehicle units, tachograph cards and external GNSS facilities shall support all standardized domain parameters specified in Table 1 below for elliptic curve cryptography. Table 1 Standardized domain parameters
Note: the object identifiers mentioned in the last column of Table 1 are specified in [RFC 5639] for the Brainpool curves and in [RFC 5480] for the NIST curves.  Text of image
Text of image
|
8.2.3 Hashing algorithms
|
CSM_49 |
Vehicle units and tachograph cards shall support the SHA-256, SHA-384 and SHA-512 algorithms specified in [SHS]. |
8.2.4 Cipher Suites
|
CSM_50 |
In case a symmetric algorithm, an asymmetric algorithm and/or a hashing algorithm are used together to form a security protocol, their respective key lengths and hash sizes shall be of (roughly) equal strength. Table 2 shows the allowed cipher suites: Table 2 Allowed cipher suites
Note: ECC keys sizes of 512 bits and 521 bits are considered to be equal in strength for all purposes within this Appendix. |
9. KEYS AND CERTIFICATES
9.1. Asymmetric Key Pairs and Public Key Certificates
9.1.1 General
Note: the keys described in this section are used for mutual authentication and secure messaging between vehicle units and tachograph cards and between vehicle units and external GNSS facilities. These processes are described in detail in chapters 10 and 11 of this Appendix.
|
CSM_51 |
Within the European Smart Tachograph system, ECC key pairs and corresponding certificates shall be generated and managed through three functional hierarchical levels:
|
|
CSM_52 |
Within the entire European Smart Tachograph system, public and private keys and certificates shall be generated, managed and communicated using standardized and secure methods. |
9.1.2 European Level
|
CSM_53 |
At European level, a single unique ECC key pair designated as EUR shall be generated. It shall consist of a private key (EUR.SK) and a public key (EUR.PK). This key pair shall form the root key pair of the entire European Smart Tachograph PKI. This task shall be handled by a European Root Certificate Authority (ERCA), under the authority and responsibility of the European Commission. |
|
CSM_54 |
The ERCA shall use the European private key to sign a (self-signed) root certificate of the European public key, and shall communicate this European root certificate to all Member States. |
|
CSM_55 |
The ERCA shall use the European private key to sign the certificates of the Member States public keys upon request. The ERCA shall keep records of all signed Member State public key certificates. |
|
CSM_56 |
As shown in Figure 1 in section 9.1.7, the ERCA shall generate a new European root key pair every 17 years. Whenever the ERCA generates a new European root key pair, it shall create a new self-signed root certificate for the new European public key. The validity period of a European root certificate shall be 34 years plus 3 months. Note: The introduction of a new root key pair also implies that ERCA will generate a new motion sensor master key and a new DSRC master key, see sections 9.2.1.2 and 9.2.2.2. |
|
CSM_57 |
Before generating a new European root key pair, the ERCA shall conduct an analysis of the cryptographic strength that is needed for the new key pair, given it should stay secure for the next 34 years. If found necessary, the ERCA shall switch to a cipher suite that is stronger than the current one, as specified in CSM_50. |
|
CSM_58 |
Whenever it generates a new European root key pair, the ERCA shall create a link certificate for the new European public key and sign it with the previous European private key. The validity period of the link certificate shall be 17 years. This is shown in Figure 1 in section 9.1.7 as well. Note: Since a link certificate contains the ERCA generation X public key and is signed with the ERCA generation X-1 private key, a link certificate offers equipment issued under generation X-1 a method to trust equipment issued under generation X. |
|
CSM_59 |
The ERCA shall not use the private key of a root key pair for any purpose after the moment a new root key certificate becomes valid. |
|
CSM_60 |
At any moment in time, the ERCA shall dispose of the following cryptographic keys and certificates:
|
9.1.3 Member State Level
|
CSM_61 |
At Member State level, all Member States required to sign tachograph card certificates shall generate one or more unique ECC key pairs designated as MSCA_Card. All Member States required to sign certificates for vehicle units or external GNSS facilities shall additionally generate one or more unique ECC key pairs designated as MSCA_VU-EGF. |
|
CSM_62 |
The task of generating Member State key pairs shall be handled by a Member State Certificate Authority (MSCA). Whenever a MSCA generates a Member State key pair, it shall send the public key to the ERCA in order to obtain a corresponding Member State certificate signed by the ERCA. |
|
CSM_63 |
An MSCA shall choose the strength of a Member State key pair equal to the strength of the European root key pair used to sign the corresponding Member State certificate. |
|
CSM_64 |
An MSCA_VU-EGF key pair, if present, shall consist of private key MSCA_VU-EGF.SK and public key MSCA_VU-EGF.PK. An MSCA shall use the MSCA_VU-EGF.SK private key exclusively to sign the public key certificates of vehicle units and external GNSS facilities. |
|
CSM_65 |
An MSCA_Card key pair shall consist of private key MSCA_Card.SK and public key MSCA_Card.PK. An MSCA shall use the MSCA_Card.SK private key exclusively to sign the public key certificates of tachograph cards. |
|
CSM_66 |
An MSCA shall keep records of all signed VU certificates, external GNSS facility certificates and card certificates, together with the identification of the equipment for which each certificate is intended. |
|
CSM_67 |
The validity period of an MSCA_VU-EGF certificate shall be 17 years plus 3 months. The validity period of an MSCA_Card certificate shall be 7 years plus 1 month. |
|
CSM_68 |
As shown in Figure 1 in section 9.1.7, the private key of a MSCA_VU-EGF key pair and the private key of a MSCA_Card key pair shall have a key usage period of two years. |
|
CSM_69 |
An MSCA shall not use the private key of an MSCA_VU-EGF key pair for any purpose after the moment its usage period has ended. Neither shall an MSCA use the private key of an MSCA_Card key pair for any purpose after the moment its usage period has ended. |
|
CSM_70 |
At any moment in time, an MSCA shall dispose of the following cryptographic keys and certificates:
|
|
CSM_71 |
If an MSCA is required to sign certificates for vehicle units or external GNSS facilities, it shall additionally dispose of the following keys and certificates:
|
9.1.4 Equipment Level: Vehicle Units
|
CSM_72 |
Two unique ECC key pairs shall be generated for each vehicle unit, designated as VU_MA and VU_Sign. This task is handled by VU manufacturers. Whenever a VU key pair is generated, the party generating the key shall send the public key to the MSCA of the country in which it resides, in order to obtain a corresponding VU certificate signed by the MSCA. The private key shall be used only by the vehicle unit. |
|
CSM_73 |
The VU_MA and VU_Sign certificates of a given vehicle unit shall have the same Certificate Effective Date. |
|
CSM_74 |
A VU manufacturer shall choose the strength of a VU key pair equal to the strength of the MSCA key pair used to sign the corresponding VU certificate. |
|
CSM_75 |
A vehicle unit shall use its VU_MA key pair, consisting of private key VU_MA.SK and public key VU_MA.PK, exclusively to perform VU Authentication towards tachograph cards and external GNSS facilities, as specified in sections 10.3 and 11.4 of this Appendix. |
|
CSM_76 |
A vehicle unit shall be capable of generating ephemeral ECC key pairs and shall use an ephemeral key pair exclusively to perform session key agreement with a tachograph card or external GNSS facility, as specified in sections 10.4 and 11.4 of this Appendix. |
|
CSM_77 |
A vehicle unit shall use the private key VU_Sign.SK of its VU_Sign key pair exclusively to sign downloaded data files, as specified in chapter 14 of this Appendix. The corresponding public key VU_Sign.PK shall be used exclusively to verify signatures created by the vehicle unit. |
|
CSM_78 |
As shown in Figure 1 in section 9.1.7, the validity period of a VU_MA certificate shall be 15 years and 3 months. The validity period of a VU_Sign certificate shall also be 15 years and 3 months. Notes:
|
|
CSM_79 |
A vehicle unit shall not use the private key of a VU key pair for any purpose after the corresponding certificate has expired. |
|
CSM_80 |
The VU key pairs (except ephemeral keys pairs) and corresponding certificates of a given vehicle unit shall not be replaced or renewed in the field once the vehicle unit has been put in operation. Notes:
|
|
CSM_81 |
When put in operation, vehicle units shall contain the following cryptographic keys and certificates:
|
|
CSM_82 |
In addition to the cryptographic keys and certificates listed in CSM_81, vehicle units shall also contain the keys and certificates specified in Part A of this Appendix, allowing a vehicle unit to interact with first-generation tachograph cards. |
9.1.5 Equipment Level: Tachograph Cards
|
CSM_83 |
One unique ECC key pair, designated as Card_MA, shall be generated for each tachograph card. A second unique ECC key pair, designated as Card_Sign, shall additionally be generated for each driver card and each workshop card. This task may be handled by card manufacturers or card personalisers. Whenever a card key pair is generated, the party generating the key shall send the public key to the MSCA of the country in which it resides, in order to obtain a corresponding card certificate signed by the MSCA. The private key shall be used only by the tachograph card. |
|
CSM_84 |
The Card_MA and Card_Sign certificates of a given driver card or workshop card shall have the same Certificate Effective Date. |
|
CSM_85 |
A card manufacturer or card personaliser shall choose the strength of a card key pair equal to the strength of the MSCA key pair used to sign the corresponding card certificate. |
|
CSM_86 |
A tachograph card shall use its Card_MA key pair, consisting of private key Card_MA.SK and public key Card_MA.PK, exclusively to perform mutual authentication and session key agreement towards vehicle units, as specified in sections 10.3 and 10.4 of this Appendix. |
|
CSM_87 |
A driver card or workshop card shall use the private key Card_Sign.SK of its Card_Sign key pair exclusively to sign downloaded data files, as specified in chapter 14 of this Appendix. The corresponding public key Card_Sign.PK shall be used exclusively to verify signatures created by the card. |
|
CSM_88 |
The validity period of a Card_MA certificate shall be as follows:
|
|
CSM_89 |
The validity period of a Card_Sign certificate shall be as follows:
Note: the extended validity period of a Card_Sign certificate allows a driver card to create valid signatures over downloaded data during the first month after it has expired. This is necessary in view of Regulation (EU) No 581/2010, which requires that a data download from a driver card must be possible up to 28 days after the last data has been recorded. |
|
CSM_90 |
The key pairs and corresponding certificates of a given tachograph card shall not be replaced or renewed once the card has been issued. |
|
CSM_91 |
When issued, tachograph cards shall contain the following cryptographic keys and certificates:
|
|
CSM_92 |
In addition to the cryptographic keys and certificates listed in CSM_91, tachograph cards shall also contain the keys and certificates specified in Part A of this Appendix, allowing these cards to interact with first-generation VUs. |
9.1.6 Equipment Level: External GNSS Facilities
|
CSM_93 |
One unique ECC key pair shall be generated for each external GNSS facility, designated as EGF_MA. This task is handled by external GNSS facility manufacturers. Whenever an EGF_MA key pair is generated, the public key shall be sent to the MSCA of the country in which it resides, in order to obtain a corresponding EGF_MA certificate signed by the MSCA. The private key shall be used only by the external GNSS facility. |
|
CSM_94 |
An EGF manufacturer shall choose the strength of an EGF_MA key pair equal to the strength of the MSCA key pair used to sign the corresponding EGF_MA certificate. |
|
CSM_95 |
An external GNSS facility shall use its EGF_MA key pair, consisting of private key EGF_MA.SK and public key EGF_MA.PK, exclusively to perform mutual authentication and session key agreement towards vehicle units, as specified in section 11.4 and 11.4 of this Appendix. |
|
CSM_96 |
The validity period of an EGF_MA certificate shall be 15 years. |
|
CSM_97 |
An external GNSS facility shall not use the private key of its EGF_MA key pair for coupling to a vehicle unit after the corresponding certificate has expired. Note: as explained in section 11.3.3, an EGF may potentially use its private key for mutual authentication towards the VU it is already coupled to, even after the corresponding certificate has expired. |
|
CSM_98 |
The EGF_MA key pair and corresponding certificate of a given external GNSS facility shall not be replaced or renewed in the field once the EGF has been put in operation. Note: This requirement does not forbid the possibility of replacing EGF key pairs during a refurbishment or repair in a secure environment controlled by the EGF manufacturer. |
|
CSM_99 |
When put in operation, an external GNSS facility shall contain the following cryptographic keys and certificates:
|
9.1.7 Overview: Certificate Replacement
Figure 1 below shows how different generations of ERCA root certificates, ERCA link certificates, MSCA certificates and equipment (VU and card) certificates are issued and used over time:
Figure 1
Issuance and usage of different generations of ERCA root certificates, ERCA link certificates, MSCA certificates and equipment certificates

Notes to Figure 1:
|
1. |
Different generations of the root certificate are indicated by a number in brackets. E.g. ERCA (1) is the first generation of ERCA root certificate; ERCA (2) is the second generation, etc. |
|
2. |
Other certificates are indicated by two numbers in brackets, the first one indicating the root certificate generation under which they are issued, the second one the generation of the certificate itself. E.g. MSCA_Card (1-1) is the first MSCA_Card certificate issued under ERCA (1); MSCA_Card (2-1) is the first MSCA_Card certificate issued under ERCA (2); MSCA_Card (2-last) is the last MSCA_Card certificate issued under ERCA (2); Card_MA(2-1) is the first Card certificate for mutual authentication that is issued under ERCA (2), etc. |
|
3. |
The MSCA_Card (2-1) and MSCA_Card (1-last) certificates are issued at almost but not exactly the same date. MSCA_Card (2-1) is the first MSCA_Card certificate issued under ERCA (2) and will be issued slightly later than MSCA_Card (1-last), the last MSCA_Card certificate under ERCA (1). |
|
4. |
As shown in the figure, the first VU and Card certificates issued under ERCA (2) will appear almost two years before the last VU and Card certificates issued under ERCA (1) will appear. This is because of the fact that VU and Card certificates are issued under an MSCA certificate, not directly under the ERCA certificate. The MSCA (2-1) certificate will be issued directly after ERCA (2) becomes valid, but the MSCA (1-last) certificate will be issued only slightly before that time, at the last moment the ERCA (1) certificate is still valid. Therefore, these two MSCA certificates will have almost the same validity period, despite the fact that they are of different generations. |
|
5. |
The validity period shown for cards is the one for driver cards (5 years). |
|
6. |
To save space, the difference in validity period between the Card_MA and Card_Sign certificates and between the VU_MA and VU_Sign certificates is shown only for the first generation. |
9.2. Symmetric Keys
9.2.1 Keys for Securing VU — Motion Sensor Communication
9.2.1.1 General
Note: readers of this section are supposed to be familiar with the contents of [ISO 16844-3] describing the interface between a vehicle unit and a motion sensor. The pairing process between a VU and a motion sensor is described in detail in chapter 12 of this Appendix.
|
CSM_100 |
A number of symmetric keys is needed for pairing vehicle units and motion sensors, for mutual authentication between vehicle units and motion sensors and for encrypting communication between vehicle units and motion sensors, as shown in Table 3. All of these keys shall be AES keys, with a key length equal to the length of the motion sensor master key, which shall be linked to the length of the (foreseen) European root key pair as described in CSM_50. Table 3 Keys for securing vehicle unit — motion sensor communication
|
|
CSM_101 |
The European Root Certificate Authority shall generate KM-VU and KM-WC, two random and unique AES keys from which the motion sensor master key KM can be calculated as KM-VU XOR KM-WC. The ERCA shall communicate KM, KM-VU and KM-WC to Member State Certificate Authorities upon their request. |
|
CSM_102 |
The ERCA shall assign to each motion sensor master key KM a unique version number, which shall also be applicable for the constituting keys KM-VU and KM-WC and for the related identification key KID. The ERCA shall inform the MSCAs about the version number when sending KM-VU and KM-WC to them. Note: The version number is used to distinguish different generations of these keys, as explained in detail in section 9.2.1.2. |
|
CSM_103 |
A Member State Certificate Authority shall forward KM-VU, together with its version number, to vehicle unit manufacturers upon their request. The VU manufacturers shall insert KM-VU and its version number in all manufactured VUs. |
|
CSM_104 |
A Member State Certificate Authority shall ensure that KM-WC, together with its version number, is inserted in every workshop card issued under its responsibility. Notes:
|
|
CSM_105 |
In addition to the AES key specified in CSM_104, a MSCA shall ensure that the TDES key KmWC, specified in requirement CSM_037 in Part A of this Appendix, is inserted in every workshop card issued under its responsibility. Notes:
|
|
CSM_106 |
An MSCA involved in issuing motion sensors shall derive the identification key from the motion sensor master key by XORing it with a constant vector CV. The value of CV shall be as follows:
Note: the constant vectors have been generated as follows:
|
|
CSM_107 |
Motion sensor manufacturers shall generate a random and unique pairing key KP for every motion sensor, and shall send each pairing key to a Member State Certificate Authority. The MSCA shall encrypt each pairing key separately with the motion sensor master key KM and shall return the encrypted key to the motion sensor manufacturer. For each encrypted key, the MSCA shall notify the motion sensor manufacturer of the version number of the associated KM. Note: as explained in section 9.2.1.2, in fact a motion sensor manufacturer may have to generate multiple unique pairing keys for a single motion sensor. |
|
CSM_108 |
Motion sensor manufacturers shall generate a unique serial number for every motion sensor, and shall send all serial numbers to a Member State Certificate Authority. The MSCA shall encrypt each serial number separately with the identification key KID and shall return the encrypted serial number to the motion sensor manufacturer. For each encrypted serial number, the MSCA shall notify the motion sensor manufacturer of the version number of the associated KID. |
|
CSM_109 |
For requirements CSM_107 and CSM_108, the MSCA shall use the AES algorithm in the Cipher Block Chaining mode of operation, as defined in [ISO 10116], with an interleave parameter m = 1 and an initialization vector SV = ‘00’ {16}, i.e. sixteen bytes with binary value 0. When necessary, the MSCA shall use padding method 2 defined in [ISO 9797-1]. |
|
CSM_110 |
The motion sensor manufacturer shall store the encrypted pairing key and the encrypted serial number in the intended motion sensor, together with the corresponding plain text values and the version number of KM and KID used for encrypting. Note: as explained in section 9.2.1.2, in fact a motion sensor manufacturer may have to insert multiple encrypted pairing keys and multiple encrypted serial numbers in a single motion sensor. |
|
CSM_111 |
In addition to the AES-based cryptographic material specified in CSM_110, a motion sensor manufacturer may also store in each motion sensor the TDES-based cryptographic material specified in requirement CSM_037 in Part A of this Appendix. Note: doing so will allow a second-generation motion sensor to be coupled to a first-generation VU. |
|
CSM_112 |
The length of the session key KS generated by a VU during the pairing to a motion sensor shall be linked to the length of its KM-VU, as described in CSM_50. |
9.2.1.2 Motion Sensor Master Key Replacement in Second-Generation Equipment
|
CSM_113 |
Each motion sensor master key and all related keys (see Table 3) is associated to a particular generation of the ERCA root key pair. These keys shall therefore be replaced every 17 years. The validity period of each motion sensor master key generation shall begin one year before the associated ERCA root key pair becomes valid and shall end when the associated ERCA root key pair expires. This is depicted in Figure 2. Figure 2 Issuance and usage of different generations of the motion sensor master key in vehicle units, motions sensors and workshop cards 
|
|
CSM_114 |
At least one year before generating a new European root key pair, as described in CSM_56, the ERCA shall generate a new motion sensor master key KM by generating a new KM-VU and KM-WC. The length of the motion sensor master key shall be linked to the foreseen strength of the new European root key pair, according to CSM_50. The ERCA shall communicate the new KM, KM-VU and KM-WC to the MSCAs upon their request, together with their version number. |
|
CSM_115 |
An MSCA shall ensure that all valid generations of KM-WC are stored in every workshop card issued under its authority, together with their version numbers, as shown in Figure 2. Note: this implies that in the last year of the validity period of an ERCA certificate, workshop cards will be issued with three different generations of KM-WC, as shown in Figure 2. |
|
CSM_116 |
In relation to the process described in CSM_107 and CSM_108 above: An MSCA shall encrypt each pairing key KP it receives from a motion sensor manufacturer separately with each valid generation of the motion sensor master key KM. An MSCA shall also encrypt each serial number it receives from a motion sensor manufacturer separately with each valid generation of the identification key KID. A motion sensor manufacturer shall store all encryptions of the pairing key and all encryptions of the serial number in the intended motion sensor, together with the corresponding plain text values and the version number(s) of KM and KID used for encrypting. Note: This implies that in the last year of the validity period of an ERCA certificate, motion sensors will be issued with encrypted data based on three different generations of KM, as shown in Figure 2. |
|
CSM_117 |
In relation to the process described in CSM_107 above: Since the length of the pairing key KP shall be linked to the length of KM (see CSM_100), a motion sensor manufacturer may have to generate up to three different pairing keys (of different lengths) for one motion sensor, in case subsequent generations of KM have different lengths. In such a case, the manufacturer shall send each pairing key to the MSCA. The MSCA shall ensure that each pairing key is encrypted with the correct generation of the motion sensor master key, i.e. the one having the same length. Note: In case the motion sensor manufacturer chooses to generate a TDES-based pairing key for a second-generation motion sensor (see CSM_111), the manufacturer shall indicate to the MSCA that the TDES-based motion sensor master key must be used for encrypting this pairing key. This is because the length of a TDES key may be equal to that of an AES key, so the MSCA cannot judge from the key length alone. |
|
CSM_118 |
Vehicle unit manufacturers shall insert only one generation of KM-VU in each vehicle unit, together with its version number. This KM-VU generation shall be linked to the ERCA certificate upon which the VU's certificates are based. Notes:
|
9.2.2 Keys for Securing DSRC Communication
9.2.2.1 General
|
CSM_119 |
The authenticity and confidentiality of data communicated from a vehicle unit to a control authority over a DSRC remote communication channel shall be ensured by means of a set of VU-specific AES keys derived from a single DSRC master key, KMDSRC. |
|
CSM_120 |
The DSRC master key KMDSRC shall be an AES key that is securely generated, stored and distributed by the ERCA. The key length may be 128, 192 or 256 bits and shall be linked to the length of the European root key pair, as described in CSM_50. |
|
CSM_121 |
The ERCA shall communicate the DSRC master key to Member State Certificate Authorities upon their request in a secure manner, to allow them to derive VU-specific DSRC keys and to ensure that the DSRC master key is inserted in all control cards and workshop cards issued under their responsibility. |
|
CSM_122 |
The ERCA shall assign to each DSRC master key a unique version number. The ERCA shall inform the MSCAs about the version number when sending the DSRC master key to them. Note: The version number is used to distinguish different generations of the DSRC master key, as explained in detail in section 9.2.2.2. |
|
CSM_123 |
For every vehicle unit, the vehicle unit manufacturer shall create a unique VU serial number and shall send this number to its Member State Certificate Authority in a request to obtain a set of two VU-specific DSRC keys. The VU serial number shall have data type
|
|
CSM_124 |
Upon receiving a request for VU-specific DSRC keys, the MSCA shall derive two AES keys for the vehicle unit, called K_VUDSRC_ENC and K_VUDSRC_MAC. These VU-specific keys shall have the same length as the DSRC master key. The MSCA shall use the key derivation function defined in [RFC 5869]. The hash function that is necessary to instantiate the HMAC-Hash function shall be linked to the length of the DSRC master key, as described in CSM_50. The key derivation function in [RFC 5869] shall be used as follows:
|
|
CSM_125 |
The MSCA shall distribute K_VUDSRC_ENC and K_VUDSRC_MAC to the VU manufacturer in a secure manner for insertion in the intended vehicle unit. |
|
CSM_126 |
When issued, a vehicle unit shall have stored K_VUDSRC_ENC and K_VUDSRC_MAC in its secure memory, in order to be able to ensure the integrity, authenticity and confidentiality of data sent over the remote communication channel. A vehicle unit shall also store the version number of the DSRC master key used to derive these VU-specific keys. |
|
CSM_127 |
When issued, control cards and workshop cards shall have stored KMDSRC in their secure memory, in order to be able to verify the integrity and authenticity of data sent by a VU over the remote communication channel and to decrypt this data. Control cards and workshop cards shall also store the version number of the DSRC master key. Note: as explained in section 9.2.2.2, in fact multiple generations of KMDSRC may have to be inserted in a single workshop card or control card. |
|
CSM_128 |
The MSCA shall keep records of all VU-specific DSRC keys it generated, their version number and the identification of the VU for which each set of keys is intended. |
9.2.2.2 DSRC Master Key Replacement
|
CSM_129 |
Each DSRC master key is associated to a particular generation of the ERCA root key pair. The ERCA shall therefore replace the DSRC master key every 17 years. The validity period of each DSRC master key generation shall begin two years before the associated ERCA root key pair becomes valid and shall end when the associated ERCA root key pair expires. This is depicted in Figure 3. Figure 3 Issuance and usage of different generations of the DSRC master key in vehicle units, workshop cards and control cards 
|
|
CSM_130 |
At least two years before generating a new European root key pair, as described in CSM_56, the ERCA shall generate a new DSRC master key. The length of the DSRC key shall be linked to the foreseen strength of the new European root key pair, according to CSM_50. The ERCA shall communicate the new DSRC master key to the MSCAs upon their request, together with its version number. |
|
CSM_131 |
An MSCA shall ensure that all valid generations of KMDSRC are stored in every control card issued under its authority, together with their version numbers, as shown in Figure 3. Note: this implies that in the last two years of the validity period of an ERCA certificate, control cards will be issued with three different generations of KMDSRC, as shown in Figure 3. |
|
CSM_132 |
An MSCA shall ensure that all generations of KMDSRC that have been valid for at least a year and are still valid, are stored in every workshop card issued under its authority, together with their version numbers, as shown in Figure 3. Note: this implies that in the last year of the validity period of an ERCA certificate, workshop cards will be issued with three different generations of KMDSRC, as shown in Figure 3. |
|
CSM_133 |
Vehicle unit manufacturers shall insert only one set of VU-specific DSRC keys into each vehicle unit, together with its version number. This set of keys shall be derived from the KMDSRC generation linked to the ERCA certificate upon which the VU's certificates are based. Notes:
|
9.3. Certificates
9.3.1 General
|
CSM_134 |
All certificates in the European Smart Tachograph system shall be self-descriptive, card-verifiable (CV) certificates according to [ISO 7816-4] and [ISO 7816-8]. |
|
CSM_135 |
The Distinguished Encoding Rules (DER) according to [ISO 8825-1] shall be used to encode both ASN.1 data structures and (application specific) data objects within certificates. Note: this encoding results in a Tag-Length-Value (TLV) structure as follows:
|
9.3.2 Certificate Content
|
CSM_136 |
All certificates shall have the structure shown in the certificate profile in Table 4. Table 4 Certificate Profile version 1
Note: the Field ID will be used in later sections of this Appendix to indicate individual fields of a certificate, e.g. X.CAR is the Certificate Authority Reference mentioned in the certificate of user X. |
9.3.2.1 Certificate Profile Identifier
|
CSM_137 |
Certificates shall use a Certificate Profile Identifier to indicate the certificate profile used. Version 1, as specified in Table 4, shall be identified by a value of ‘00’. |
9.3.2.2 Certificate Authority Reference
|
CSM_138 |
The Certificate Authority Reference shall be used to identify the public key to be used to verify the certificate signature. The Certificate Authority Reference shall therefore be equal to the Certificate Holder Reference in the certificate of the corresponding certificate authority. |
|
CSM_139 |
An ERCA root certificate shall be self-signed, i.e., the Certificate Authority Reference and the Certificate Holder Reference in the certificate shall be equal. |
|
CSM_140 |
For an ERCA link certificate, the Certificate Holder Reference shall be equal to the CHR of the new ERCA root certificate. The Certificate Authority Reference for a link certificate shall be equal to the CHR of the previous ERCA root certificate. |
9.3.2.3 Certificate Holder Authorisation
|
CSM_141 |
The Certificate Holder Authorisation shall be used to identify the type of certificate. It consists of the six most significant bytes of the Tachograph Application ID, concatenated with the type of equipment for which the certificate is intended. |
9.3.2.4 Public Key
The Public Key nests two data elements: the standardized domain parameters to be used with the public key in the certificate and the value of the public point.
|
CSM_142 |
The data element Domain Parameters shall contain one of the object identifiers specified in Table 1 to reference a set of standardized domain parameters. |
|
CSM_143 |
The data element Public Point shall contain the public point. Elliptic curve public points shall be converted to octet strings as specified in [TR-03111]. The uncompressed encoding format shall be used. When recovering an elliptic curve point from its encoded format, the validations described in [TR-03111] shall always be carried out. |
9.3.2.5 Certificate Holder Reference
|
CSM_144 |
The Certificate Holder Reference is an identifier for the public key provided in the certificate. It shall be used to reference this public key in other certificates. |
|
CSM_145 |
For card certificates and external GNSS facility certificates, the Certificate Holder Reference shall have the
|
|
CSM_146 |
For vehicle units, the manufacturer, when requesting a certificate, may or may not know the manufacturer-specific serial number of the VU for which that certificate and the associated private key is intended. In the first case, the Certificate Holder Reference shall have the
|
|
CSM_147 |
For ERCA and MSCA certificates, the Certificate Holder Reference shall have the
|
9.3.2.6 Certificate Effective Date
|
CSM_148 |
The Certificate Effective Date shall indicate the starting date and time of the validity period of the certificate. The Certificate Effective Date shall be the date of the certificate generation. |
9.3.2.7 Certificate Expiration Date
|
CSM_149 |
The Certificate Expiration Date shall indicate the end date and time of the validity period of the certificate. |
9.3.2.8 Certificate Signature
|
CSM_150 |
The signature on the certificate shall be created over the encoded certificate body, including the certificate body tag and length. The signature algorithm shall be ECDSA, as specified in [DSS], using the hashing algorithm linked to the key size of the signing authority, as specified in CSM_50. The signature format shall be plain, as specified in [TR-03111]. |
9.3.3 Requesting Certificates
|
CSM_151 |
When requesting a certificate, a requester shall send the following data to its Certificate Authority:
|
|
CSM_152 |
In addition to the data in CSM_151, an MSCA shall send the following data in a certificate request to the ERCA, allowing the ERCA to create the Certificate Holder Reference of the new MSCA certificate:
|
|
CSM_153 |
In addition to the data in CSM_151, an equipment manufacturer shall send the following data in a certificate request to an MSCA, allowing the MSCA to create the Certificate Holder Reference of the new equipment certificate:
The manufacturer shall ensure that this data is correct and that the certificate returned by the MSCA is inserted in the intended equipment. |
|
CSM_154 |
In the case of a VU, the manufacturer, when requesting a certificate, may or may not know the manufacturer-specific serial number of the VU for which that certificate and the associated private key is intended. If known, the VU manufacturer shall send the serial number to the MSCA. If not known, the manufacturer shall uniquely identify each certificate request and send this certificate request serial number to the MSCA. The resulting certificate will then contain the certificate request serial number. After inserting the certificate in a specific VU, the manufacturer shall communicate the connection between the certificate request serial number and the VU identification to the MSCA. |
10. VU- CARD MUTUAL AUTHENTICATION AND SECURE MESSAGING
10.1. General
|
CSM_155 |
On a high level, secure communication between a vehicle unit and a tachograph card shall be based on the following steps:
|
|
CSM_156 |
The mechanism described in CSM_155 shall be triggered by the vehicle unit whenever a card is inserted into one of its card slots. |
10.2. Mutual Certificate Chain Verification
10.2.1 Card Certificate Chain Verification by VU
|
CSM_157 |
Vehicle units shall use the protocol depicted in Figure 4 for verifying a tachograph card's certificate chain. Notes to Figure 4:
|
|
CSM_158 |
As depicted in Figure 4, verification of the card's certificate chain shall begin upon card insertion. The vehicle unit shall read the card holder reference (
Note: There are three ways in which the VU may know the Card.CA.EUR certificate:
|
|
CSM_159 |
As indicated in Figure 4, once the VU has verified the authenticity and validity of a previously unknown certificate, it may store this certificate for future reference, such that it does not need to verify that certificate's authenticity again if it is presented to the VU again. Instead of storing the entire certificate, a VU may choose to store only the contents of the Certificate Body, as specified in section 9.3.2. |
|
CSM_160 |
The VU shall verify the temporal validity of any certificate read from the card or stored in its memory, and shall reject expired certificates. For verifying the temporal validity of a certificate presented by the card a VU shall use its internal clock. |
Figure 4
Protocol for Card Certificate Chain Verification by VU

10.2.2 VU Certificate Chain Verification by Card
|
CSM_161 |
Tachograph cards shall use the protocol depicted in Figure 5 for verifying a VU's certificate chain. |
Figure 5
Protocol for VU Certificate Chain Verification by Card

Notes to Figure 5:
|
— |
The VU certificates and public keys mentioned in the figure are those for mutual authentication. Section 9.1.4 denotes these as VU_MA. |
|
— |
The VU.CA certificates and public keys mentioned in the figure are those for signing VU and external GNSS facility certificates. Section 9.1.3 denotes these as MSCA_VU-EGF. |
|
— |
The VU.CA.EUR certificate mentioned in the figure is the European root certificate that is indicated in the CAR of the VU.CA certificate. |
|
— |
The VU.Link certificate mentioned in the figure is the VU's link certificate, if present. As specified in section 9.1.2, this is a link certificate for a new European root key pair created by the ERCA and signed by the previous European private key. |
|
— |
The VU.Link.EUR certificate is the European root certificate that is indicated in the CAR of the VU.Link certificate. |
|
CSM_162 |
As depicted in Figure 5, verification of the certificate chain of the vehicle unit shall begin with the vehicle unit attempting to set its own public key for use in the tachograph card. If this succeeds, it means that the card successfully verified the VU's certificate chain in the past, and has stored the VU certificate for future reference. In this case, the VU certificate is set for use and the process continues with VU Authentication. If the card does not know the VU certificate, the VU shall successively present the VU.CA certificate to be used for verifying its VU certificate, the VU.CA.EUR certificate to be used for verifying the VU.CA certificate, and possibly the link certificate, in order to find a certificate known or verifiable by the card. If such a certificate is found, the card shall use that certificate to verify the underlying VU certificates presented to it. If successful, the VU shall finally set its public key for use in the tachograph card. If not successful, the VU shall ignore the card. Note: There are three ways in which the card may know the VU.CA.EUR certificate:
|
|
CSM_163 |
The VU shall use the MSE: Set AT command to set its public key for use in the tachograph card. As specified in Appendix 2, this command contains an indication of the cryptographic mechanism that will be used with the key that is set. This mechanism shall be ‘VU Authentication using the ECDSA algorithm, in combination with the hashing algorithm linked to the key size of the VU's VU_MA key pair, as specified in CSM_50’. |
|
CSM_164 |
The MSE: Set AT command also contains an indication of the ephemeral key pair which the VU will use during session key agreement (see section 10.4). Therefore, before sending the MSE: Set AT command, the VU shall generate an ephemeral ECC key pair. For generating the ephemeral key pair, the VU shall use the standardized domain parameters indicated in the card certificate. The ephemeral key pair is denoted as (VU.SKeph, VU.PKeph, Card.DP). The VU shall take the x-coordinate of the ECDH ephemeral public point as the key identification; this is called the compressed representation of the public key and denoted as Comp(VU.PKeph). |
|
CSM_165 |
If the MSE: Set AT command is successful, the card shall set the indicated VU.PK for subsequent use during Vehicle Authentication, and shall temporarily store Comp(VU.PKeph). In case two or more successful MSE: Set AT commands are sent before session key agreement is performed, the card shall store only the last Comp(VU.PKeph) received. |
|
CSM_166 |
The card shall verify the temporal validity of any certificate presented by the VU or referenced by the VU while stored in the card's memory, and shall reject expired certificates. |
|
CSM_167 |
For verifying the temporal validity of a certificate presented by the VU, each tachograph card shall internally store some data representing the current time. This data shall not be directly updatable by a VU. At issuance, the current time of a card shall be set equal to the Effective Date of the card's Card_MA certificate. A card shall update its current time if the Effective Date of an authentic ‘valid source of time’ certificate presented by a VU is more recent than the card's current time. In that case, the card shall set its current time to the Effective Date of that certificate. The card shall accept only the following certificates as a valid source of time:
Note: the last requirement implies that a card shall be able to recognize the CAR of the VU certificate, i.e. the MSCA_VU-EGF certificate. This will not be the same as the CAR of its own certificate, which is the MSCA_Card certificate. |
|
CSM_168 |
As indicated in Figure 5, once the card has verified the authenticity and validity of a previously unknown certificate, it may store this certificate for future reference, such that it does not need to verify that certificate's authenticity again if it is presented to the card again. Instead of storing the entire certificate, a card may choose to store only the contents of the Certificate Body, as specified in section 9.3.2. |
10.3. VU Authentication
|
CSM_169 |
Vehicle units and cards shall use the VU Authentication protocol depicted in Figure 6 to authenticate the VU towards the card. VU Authentication enables the tachograph card to explicitly verify that the VU is authentic. To do so, the VU shall use its private key to sign a challenge generated by the card. |
|
CSM_170 |
Next to the card challenge, the VU shall include in the signature the card holder reference taken from the card certificate. Note: This ensures that the card to which the VU authenticates itself is the same card whose certificate chain the VU has verified previously. |
|
CSM_171 |
The VU shall also include in the signature the identifier of the ephemeral public key Comp(VU.PKeph) which the VU will use to set up Secure Messaging during the Chip Authentication process specified in section 10.4. Note: This ensures that the VU with which a card communicates during a Secure Messaging session is the same VU that was authenticated by the card. |
Figure 6
VU Authentication protocol

|
CSM_172 |
If multiple GET CHALLENGE commands are sent by the VU during VU Authentication, the card shall return a new 8-byte random challenge each time, but shall store only the last challenge. |
|
CSM_173 |
The signing algorithm used by the VU for VU Authentication shall be ECDSA as specified in [DSS], using the hashing algorithm linked to the key size of the VU's VU_MA key pair, as specified in CSM_50. The signature format shall be plain, as specified in [TR-03111]. The VU shall send the resulting signature to the card. |
|
CSM_174 |
Upon receiving the VU's signature in an EXTERNAL AUTHENTICATE command, the card shall
|
10.4. Chip Authentication and Session Key Agreement
|
CSM_175 |
Vehicle units and cards shall use the Chip Authentication protocol depicted in Figure 7 to authenticate the card towards the VU. Chip Authentication enables the vehicle unit to explicitly verify that the card is authentic. |
Figure 7
Chip Authentication and session key agreement

|
CSM_176 |
The VU and the card shall take the following steps:
|
|
CSM_177 |
In step 3 above, the card shall compute Comp(VU.PKeph) as the x-coordinate of the public point in VU.PKeph. |
|
CSM_178 |
In steps 4 and 7 above, the card and the vehicle unit shall use the ECKA-EG algorithm as defined in [TR-03111]. |
|
CSM_179 |
In steps 5 and 8 above, the card and the vehicle unit shall use the key derivation function for AES session keys defined in [TR-03111], with the following precisions and changes:
The length of the session keys (i.e. the length at which the hash is truncated) shall be linked to the size of the Card_MA key pair, as specified in CSM_50. |
|
CSM_180 |
In steps 6 and 9 above, the card and the vehicle unit shall use the AES algorithm in CMAC mode, as specified in [SP 800-38B]. The length of TPICC shall be linked to the length of the AES session keys, as specified in CSM_50. |
10.5. Secure Messaging
10.5.1 General
|
CSM_181 |
All commands and responses exchanged between a vehicle unit and a tachograph card after successful Chip Authentication took place and until the end of the session shall be protected by Secure Messaging. |
|
CSM_182 |
Except when reading from a file with access condition SM-R-ENC-MAC-G2 (see Appendix 2, section 4), Secure Messaging shall be used in authentication-only mode. In this mode, a cryptographic checksum (a.k.a. MAC) is added to all commands and responses to ensure message authenticity and integrity. |
|
CSM_183 |
When reading data from a file with access condition SM-R-ENC-MAC-G2, Secure Messaging shall be used in encrypt-then-authenticate mode, i.e. the response data is encrypted first to ensure message confidentiality, and afterwards a MAC over the formatted encrypted data is calculated to ensure authenticity and integrity. |
|
CSM_184 |
Secure Messaging shall use AES as defined in [AES] with the session keys KMAC and KENC that were agreed during Chip Authentication. |
|
CSM_185 |
An unsigned integer shall be used as the Send Sequence Counter (SSC) to prevent replay attacks. The size of the SSC shall be equal to the AES block size, i.e. 128 bits. The SSC shall be in MSB-first format. The Send Sequence Counter shall be initialized to zero (i.e. ‘00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00’) when Secure Messaging is started. The SSC shall be increased every time before a command or response APDU is generated, i.e. since the starting value of the SSC in a SM session is 0, in the first command the value of the SSC will be 1. The value of SSC for the first response will be 2. |
|
CSM_186 |
For message encryption, KENC shall be used with AES in the Cipher Block Chaining (CBC) mode of operation, as defined in [ISO 10116], with an interleave parameter m = 1 and an initialization vector SV = E(KENC, SSC), i.e. the current value of the Send Sequence Counter encrypted with KENC. |
|
CSM_187 |
For message authentication, KMAC shall be used with AES in CMAC mode as specified in [SP 800-38B]. The length of the MAC shall be linked to the length of the AES session keys, as specified in CSM_50. The Send Sequence Counter shall be included in the MAC by prepending it before the datagram to be authenticated. |
10.5.2 Secure Message Structure
|
CSM_188 |
Secure Messaging shall make use only of the Secure Messaging data objects (see [ISO 7816-4]) listed in Table 5. In any message, these data objects shall be used in the order specified in this table. Table 5 Secure Messaging Data Objects
Note: As specified in Appendix 2, tachograph cards may support the READ BINARY and UPDATE BINARY command with an odd INS byte (‘B1’ resp. ‘D7’). These command variants are required to read and update files with more than 32 768 bytes or more. In case such a variant is used, a data object with tag ‘B3’ shall be used instead of an object with tag ‘81’. See Appendix 2 for more information. |
|||||||||||||||||||||||||||||||
|
CSM_189 |
All SM data objects shall be encoded in DER TLV as specified in [ISO 8825-1]. This encoding results in a Tag-Length-Value (TLV) structure as follows:
|
|
CSM_190 |
APDUs protected by Secure Messaging shall be created as follows:
|
|
CSM_191 |
Any data object to be encrypted shall be padded according to [ISO 7816-4] using padding-content indicator ‘01’. For the calculation of the MAC, each data object in the APDU shall also be separately padded according to [ISO 7816-4]. Note: Padding for Secure Messaging is always performed by the secure messaging layer, not by the CMAC or CBC algorithms. |
Summary and Examples
A command APDU with applied Secure Messaging will have the following structure, depending on the case of the respective unsecured command (DO is data object):
|
Case 1: |
CLA INS P1 P2 || Lc' || DO ‘8E’ || Le |
|
Case 2: |
CLA INS P1 P2 || Lc' || DO ‘97’ || DO‘8E’ || Le |
|
Case 3 (even INS byte): |
CLA INS P1 P2 || Lc' || DO ‘81’ || DO‘8E’ || Le |
|
Case 3 (odd INS byte): |
CLA INS P1 P2 || Lc' || DO ‘B3’ || DO‘8E’ || Le |
|
Case 4 (even INS byte): |
CLA INS P1 P2 || Lc' || DO ‘81’ || DO‘97’ || DO‘8E’ || Le |
|
Case 4 (odd INS byte): |
CLA INS P1 P2 || Lc' || DO ‘B3’ || DO‘97’ || DO‘8E’ || Le |
where Le = ‘00’ or ‘00 00’ depending on whether short length fields or extended length fields are used; see [ISO 7816-4].
A response APDU with applied Secure Messaging will have the following structure, depending on the case of the respective unsecured response:
|
Case 1 or 3: |
DO ‘99’ || DO ‘8E’ || SW1SW2 |
|
Case 2 or 4 (even INS byte) with encryption: |
DO ‘81’ || DO ‘99’ || DO ‘8E’ || SW1SW2 |
|
Case 2 or 4 (even INS byte) without encryption: |
DO ‘87’ || DO ‘99’ || DO ‘8E’ || SW1SW2 |
|
Case 2 or 4 (odd INS byte) without encryption: |
DO ‘B3’ || DO ‘99’ || DO ‘8E’ || SW1SW2 |
Note: Case 2 or 4 (odd INS byte) with encryption is never used in the communication between a VU and a card.
Below are three example APDU transformations for commands with even INS code. Figure 8 shows an authenticated Case 4 command APDU, Figure 9 shows an authenticated Case 2/Case 4 response APDU, and Figure 10 shows an encrypted and authenticated Case 2/Case 4 response APDU.
Figure 8
Transformation of an authenticated Case 4 Command APDU

Figure 9
Transformation of an authenticated Case 1 / Case 3 Response APDU

Figure 10
Transformation of an encrypted and authenticated Case 2/Case 4 Response APDU

10.5.3 Secure Messaging Session Abortion
|
CSM_192 |
A vehicle unit shall abort an ongoing Secure Messaging session if and only if one of the following conditions occur:
|
|
CSM_193 |
A tachograph card shall abort an ongoing Secure Messaging session if and only if one of the following conditions occur:
|
|
CSM_194 |
Regarding SM error handling by a tachograph card:
In such a case, the status bytes shall be returned without using SM. |
|
CSM_195 |
If a Secure Messaging session between a VU and a tachograph card is aborted, the VU and the tachograph card shall
|
|
CSM_196 |
If for any reason the VU decides to restart mutual authentication towards an inserted card, the process shall restart with verification of the card certificate chain, as described in section 10.2, and shall continue as described in sections 10.2 — 10.5. |
11. VU — EXTERNAL GNSS FACILITY COUPLING, MUTUAL AUTHENTICATION AND SECURE MESSAGING
11.1. General
|
CSM_197 |
The GNSS facility used by a VU to determine its position may be internal, (i.e. built into the VU casing and not detachable), or it may be an external module. In the first case, there is no need to standardize the internal communication between the GNSS facility and the VU, and the requirements in this chapter do not apply. In the latter case, communication between the VU and the external GNSS facility shall be standardized and protected as described in this chapter. |
|
CSM_198 |
Secure communication between a vehicle unit and an external GNSS facility shall take place in the same way as secure communication between a vehicle unit and a tachograph card, with the external GNSS facility (EGF) taking the role of the card. All requirements mentioned in chapter 10 for tachograph cards shall be satisfied by an EGF, taking into account the deviations, clarifications and additions mentioned in this chapter. In particular, mutual certificate chain verification, VU Authentication and Chip Authentication shall be performed as described in sections 11.3 and 11.4. |
|
CSM_199 |
Communication between a vehicle unit and an EGF differs from communication between a vehicle unit and a card in the fact that a vehicle unit and an EGF must be coupled once in a workshop before the VU and the EGF can exchange GNSS-based data during normal operation. The coupling process is described in section 11.2. |
|
CSM_200 |
For communication between a vehicle unit and an EGF, APDU commands and responses based on [ISO 7816-4] and [ISO 7816-8] shall be used. The exact structure of these APDUs is defined in Appendix 2 of this Annex. |
11.2. VU and External GNSS Facility Coupling
|
CSM_201 |
A vehicle unit and an EGF in a vehicle shall be coupled by a workshop. Only a coupled vehicle unit and EGF shall be able to communicate during normal operation. |
|
CSM_202 |
Coupling of a vehicle unit and an EGF shall only be possible if the vehicle unit is in calibration mode. The coupling shall be initiated by the vehicle unit. |
|
CSM_203 |
A workshop may re-couple a vehicle unit to another EGF or to the same EGF at any time. During re-coupling, the VU shall securely destroy the existing EGF_MA certificate in its memory and shall store the EGF_MA certificate of the EGF to which it is being coupled. |
|
CSM_204 |
A workshop may re-couple an external GNSS facility to another VU or to the same VU at any time. During re-coupling, the EGF shall securely destroy the existing VU_MA certificate in its memory and shall store the VU_MA certificate of the VU to which it is being coupled. |
11.3. Mutual Certificate Chain Verification
11.3.1 General
|
CSM_205 |
Mutual certificate chain verification between a VU and an EGF shall take place only during the coupling of the VU and the EGF by a workshop. During normal operation of a coupled VU and EGF, no certificates shall be verified. Instead, the VU and EGF shall trust the certificates they stored during the coupling, after checking the temporal validity of these certificates. The VU and the EGF shall not trust any other certificates for protecting the VU — EGF communication during normal operation. |
11.3.2 During VU — EGF Coupling
|
CSM_206 |
During the coupling to an EGF, a vehicle unit shall use the protocol depicted in Figure 4 (section 10.2.1) for verifying the external GNSS facility's certificate chain. Notes to Figure 4 within this context:
|
|
CSM_207 |
Once it has verified the EGF_MA certificate, the vehicle unit shall store this certificate for use during normal operation; see section 11.3.3. |
|
CSM_208 |
During the coupling to a VU, an external GNSS unit shall use the protocol depicted in Figure 5 (section 10.2.2) for verifying the VU's certificate chain. Notes to Figure 5 within this context:
|
|
CSM_209 |
In deviation from requirement CSM_167, an EGF shall use the GNSS time to verify the temporal validity of any certificate presented. |
|
CSM_210 |
Once it has verified the VU_MA certificate, the external GNSS unit shall store this certificate for use during normal operation; see section 11.3.3. |
11.3.3 During Normal Operation
|
CSM_211 |
During normal operation, a vehicle unit and an EGF shall use the protocol depicted in Figure 11 for verifying the temporal validity of the stored EGF_MA and VU_MA certificates and for setting the VU_MA public key for subsequent VU Authentication. No further mutual verification of the certificate chains shall take place during normal operation. Note that Figure 11 in essence consists of the first steps shown in Figure 4 and Figure 5. Again, note that since an EGF is not a smart card, the VU will probably not send a Reset to initiate the communication and will not receive an ATR. In any case this is out of the scope of this Appendix. |
Figure 11
Mutual verification of certificate temporal validity during normal VU — EGF operation

|
CSM_212 |
As shown in Figure 11, the vehicle unit shall log an error if the EGF_MA certificate is no longer valid. However, mutual authentication, key agreement and subsequent communication via secure messaging shall proceed normally. |
11.4. VU Authentication, Chip Authentication and Session Key Agreement
|
CSM_213 |
VU Authentication, Chip Authentication and session key agreement between a VU and an EGF shall take place during coupling and whenever a Secure Messaging session is re-established during normal operation. The VU and the EGF shall carry out the processes described in sections 10.3 and 10.4. All requirements in these sections shall apply. |
11.5. Secure Messaging
|
CSM_214 |
All commands and responses exchanged between a vehicle unit and an external GNSS facility after successful Chip Authentication took place and until the end of the session shall be protected by Secure Messaging.in authentication-only mode. All requirements in section 10.5 shall apply. |
|
CSM_215 |
If a Secure Messaging session between a VU and an EGF is aborted, the VU shall immediately establish a new Secure Messaging session, as described in section 11.3.3 and 11.4. |
12. VU — MOTION SENSOR PAIRING AND COMMUNICATION
12.1. General
|
CSM_216 |
A vehicle unit and a motion sensor shall communicate using the interface protocol specified in [ISO 16844-3] during pairing and in normal operation, with the changes described in this chapter and in section 9.2.1. Note: readers of this chapter are supposed to be familiar with the contents of [ISO 16844-3]. |
12.2. VU — Motion Sensor Pairing Using Different Key Generations
As explained in section 9.2.1, the motion sensor master key and all associated keys are regularly replaced. This leads to the presence of up to three motion sensor-related AES keys KM-WC (of consecutive key generations) in workshop cards. Similarly, in motion sensors up to three different AES-based encryptions of data (based on consecutive generations of the motion sensor master key KM) may be present. A vehicle unit contains only one motion sensor-related key KM-VU.
|
CSM_217 |
A second-generation VU and a second-generation motion sensor shall be paired as follows (compare Table 6 in [ISO 16844-3]):
Note that steps 2 and 5 are different from the standard process in [ISO 16844-3]; the other steps are standard. Example: Suppose a pairing takes place in the first year of the validity of the ERCA (3) certificate; see Figure 2 in section 9.2.1.2. Moreover
In this case, the following will happen in steps 2 — 5:
|
12.3. VU — Motion Sensor Pairing and Communication using AES
|
CSM_218 |
As specified in Table 3 in section 9.2.1, all keys involved in the pairing of a (second-generation) vehicle unit and a motion sensor and in subsequent communication shall be AES keys, rather than double-length TDES keys as specified in [ISO 16844-3]. These AES keys may have a length of 128, 192 or 256 bits. Since the AES block size is 16 bytes, the length of an encrypted message must be a multiple of 16 bytes, compared to 8 bytes for TDES. Moreover, some of these messages will be used to transport AES keys, the length of which may be 128, 192 or 256 bits. Therefore, the number of data bytes per instruction in Table 5 of [ISO 16844-3] shall be changed as shown in Table 6: Table 6 Number of plaintext and encrypted data bytes per instruction defined in [ISO 16844-3]
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
CSM_219 |
The pairing information that is sent in instructions 43 (VU request) and 50 (MoS reply) shall be assembled as specified in section 7.6.10 of [ISO 16844-3], except that the AES algorithm shall be used instead of the TDES algorithm in the pairing data encryption scheme, thus resulting in two AES encryptions, and adopting the padding specified in CSM_220 to fit with the AES block size. The key K'p used for this encryption shall be generated as follows:
where Ns is the 8-byte serial number of the motion sensor. |
|
CSM_220 |
In case the plaintext data length (using AES keys) is not a multiple of 16 bytes, padding method 2 defined in [ISO 9797-1] shall be used. Note: in [ISO 16844-3], the number of plaintext data bytes is always a multiple of 8, such that padding is not necessary when using TDES. The definition of data and messages in [ISO 16844-3] is not changed by this part of this Appendix, thus necessitating the application of padding. |
|
CSM_221 |
For instruction 11 and in case more than one block of data must be encrypted, the Cipher Block Chaining mode of operation shall be used as defined in [ISO 10116], with an interleave parameter m = 1. The IV to be used shall be
Note: As shown in section 7.6.5 and 7.6.6 of [ISO 16844-3], when the MoS encrypts data files for inclusion in instruction 11, the authentication block is both
|
12.4. VU — Motion Sensor Pairing For Different Equipment Generations
|
CSM_222 |
As explained in section 9.2.1, a second-generation motion sensor may contain the TDES-based encryption of the pairing data (as defined in Part A of this Appendix), which allows the motion sensor to be paired to a first-generation VU. If this is the case, a first-generation VU and a second-generation motion sensor shall be paired as described in Part A of this Appendix and in [ISO 16844-3]. For the pairing process either a first-generation or a second-generation workshop card may be used. Notes:
|
13. SECURITY FOR REMOTE COMMUNICATION OVER DSRC
13.1. General
As specified in Appendix 14, a VU regularly generates Remote Tachograph Monitoring (RTM) data and sends this data to the (internal or external) Remote Communication Facility (RCF). The remote communication facility is responsible for sending this data over the DSRC interface described in Appendix 14 to the remote interrogator. Appendix 1 specifies that the RTM data is the concatenation of:
Encrypted tachograph payload the encryption of the plaintext tachograph payload
DSRC security data described below
The plaintext tachograph payload data format is specified in Appendix 1 and further described in Appendix 14. This section describes the structure of the DSRC security data; the formal specification is in Appendix 1.
|
CSM_223 |
The plaintext
|
|
CSM_224 |
The DSRC security data shall consist of the concatenation of the following data elements in the following order; see also Figure 12:
|
|
CSM_225 |
The 3-byte counter in the DSRC security data shall be in MSB-first format. The first time a VU calculates a set of RTM data after it is taken into production, it shall set the value of the counter to 0. The VU shall increase the value of the counter data by 1, each time before it calculates a next set of RTM data. |
13.2. Tachograph Payload Encryption and MAC Generation
|
CSM_226 |
Given a plaintext data element with data type
|
|
CSM_227 |
A VU shall calculate the MAC in the DSRC security data as shown in Figure 12: the MAC shall be calculated over all preceding bytes in the RTM data, up to and including the DSRC master key version number, and including the tags and lengths of the data objects. The VU shall use its DSRC key for authenticity K_VUDSRC_MAC (see section 9.2.2) with the AES algorithm in CMAC mode as specified in [SP 800-38B]. The length of the MAC shall be linked to the length of the VU-specific DSRC keys, as specified in CSM_50. |
Figure 12
Tachograph payload encryption and MAC generation

13.3. Verification and Decryption of Tachograph Payload
|
CSM_228 |
When a remote interrogator receives RTM data from a VU, it shall send the entire RTM data to a control card in the data field of a PROCESS DSRC MESSAGE command, as described in Appendix 2. Then:
|
|
CSM_229 |
In order to prevent replay attacks, the remote interrogator shall verify the freshness of the RTM data by verifying that the current date time in the DSRC security data does not deviate too much from the current time of the remote interrogator. Notes:
|
|
CSM_230 |
When a workshop verifies the correct functioning of the DSRC functionality of a VU, it shall send the entire RTM data received from the VU to a workshop card in the data field of a PROCESS DSRC MESSAGE command, as described in Appendix 2. The workshop card shall perform all checks and actions specified in CSM_228. |
14. SIGNING DATA DOWNLOADS AND VERIFYING SIGNATURES
14.1. General
|
CSM_231 |
The Intelligent Dedicated Equipment (IDE) shall store data received from a VU or a card during one download session within one physical data file. Data may be stored on an ESM (external storage medium). This file contains digital signatures over data blocks, as specified in Appendix 7. This file shall also contain the following certificates (refer to section 9.1):
|
|
CSM_232 |
The IDE shall also dispose of.
Note: the method the IDE uses to retrieve these certificates is not specified in this Appendix. |
14.2. Signature generation
|
CSM_233 |
The signing algorithm to create digital signatures over downloaded data shall be ECDSA as specified in [DSS], using the hashing algorithm linked to the key size of the VU or the card, as specified in CSM_50. The signature format shall be plain, as specified in [TR-03111]. |
14.3. Signature verification
|
CSM_234 |
An IDE may perform verification of a signature over downloaded data itself or it may use a control card for this purpose. In case it uses a control card, signature verification shall take place as shown in Figure 13. In case it performs signature verification itself, the IDE shall verify the authenticity and validity of all certificates in the certificate chain in the data file, and it shall verify the signature over the data following the signature scheme defined in [DSS]. Notes to Figure 13:
|
|
CSM_235 |
For calculating the hash M sent to the control card in the PSO:Hash command, the IDE shall use the hashing algorithm linked to the key size of the VU or the card from which the data is downloaded, as specified in CSM_50. |
|
CSM_236 |
For verifying the EQT's signature, the control card shall follow the signature scheme defined in [DSS]. Note: This document does not specify any action to undertake if a signature over a downloaded data file cannot be verified or if the verification is unsuccessful. |
Figure 13
Protocol for verification of the signature over a downloaded data file

(*) Storage of KM and KID is optional, as these keys can be derived from KM-VU, KM-WC and CV.
(1) Note that the generation-1, generation-2 and generation-3 pairing keys may actually be the same key, or may be three different keys having different lengths, as explained in CSM_117.
Appendix 12
POSITIONING BASED ON GLOBAL NAVIGATION SATELLITE SYSTEM (GNSS)
TABLE OF CONTENT
|
1. |
INTRODUCTION | 405 |
|
1.1. |
Scope | 405 |
|
1.2. |
Acronyms and notations | 405 |
|
2. |
SPECIFICATION OF THE GNSS RECEIVER | 406 |
|
3. |
NMEA SENTENCES | 406 |
|
4. |
VEHICLE UNIT WITH AN EXTERNAL GNSS FACILITY | 408 |
|
4.1. |
Configuration | 408 |
|
4.1.1 |
Main components and interfaces | 408 |
|
4.1.2 |
External GNSS facility state at the end of production | 408 |
|
4.2. |
Communication between the external GNSS facility and the vehicle unit | 409 |
|
4.2.1 |
Communication Protocol | 409 |
|
4.2.2 |
Secure transfer of GNSS data | 411 |
|
4.2.3 |
Structure of the Read Record command | 412 |
|
4.3. |
Coupling, mutual authentication and session key agreement of the external GNSS facility with vehicle unit | 413 |
|
4.4. |
Error Handling | 413 |
|
4.4.1 |
Communication error with the external GNSS facility | 413 |
|
4.4.2 |
Breach of the physical integrity of the external GNSS facility | 413 |
|
4.4.3 |
Absence of position information from GNSS receiver | 413 |
|
4.4.4 |
External GNSS facility certificate expired | 414 |
|
5. |
VEHICLE UNIT WITHOUT AN EXTERNAL GNSS FACILITY | 414 |
|
5.1. |
Configuration | 414 |
|
5.2. |
Error Handling | 414 |
|
5.2.1 |
Absence of position information from GNSS receiver | 414 |
|
6. |
GNSS TIME CONFLICT | 414 |
|
7. |
VEHICLE MOTION CONFLICT | 415 |
1. INTRODUCTION
This Appendix provides the technical requirements for the GNSS data used by the Vehicle Unit, including the protocols that must be implemented to assure the secure and correct data transfer of the positioning information.
The main articles in this Regulation (EU) No 165/2014 driving these requirements are: ‘Article 8 Recording of the position of the vehicle at certain points during the daily working period’, ‘Article 10 Interface with Intelligent Transport Systems’ and ‘Article 11 Detailed provisions for smart tachographs’.
1.1. Scope
|
GNS_1 |
The Vehicle Unit shall collect location data from at least one GNSS to support the implementation of Article 8. |
The Vehicle Unit may be with or without an external GNSS facility as described in Figure 1:
Figure 1
Different configurations for GNSS receiver

1.2. Acronyms and notations
The following acronyms are used in this appendix:
|
DOP |
Dilution of Precision |
|
EGF |
Elementary file GNSS Facility |
|
EGNOS |
European Geostationary Navigation Overlay Service |
|
GNSS |
Global Navigation Satellite System |
|
GSA |
GPS DOP and active satellites |
|
HDOP |
Horizontal Dilution of Precision |
|
ICD |
Interface Control Document |
|
NMEA |
National Marine Electronics Association |
|
PDOP |
Position Dilution of Precision |
|
RMC |
Recommended Minimum Specific |
|
SIS |
Signal in Space |
|
VDOP |
Vertical Dilution of Precision |
|
VU |
Vehicle Unit |
2. SPECIFICATION OF THE GNSS RECEIVER
Regardless of the configuration of the Smart Tachograph with or without an external GNSS facility, the provision of accurate and reliable positioning information is an essential element of the effective operation of the Smart Tachograph. Therefore, it is appropriate to require its compatibility with the services provided by the Galileo and European Geostationary Navigation Overlay Service (EGNOS) programmes as set out in Regulation (EU) No 1285/2013 of the European Parliament and of the Council (1). The system established under the Galileo programme is an independent global satellite navigation system and the one established under the EGNOS programme is a regional satellite navigation system improving the quality of the Global Positioning System signal.
|
GNS_2 |
Manufacturers shall ensure that the GNSS receivers in the Smart Tachographs are compatible with the positioning services provided by the Galileo and the EGNOS systems. Manufacturers may also choose, in addition, compatibility with other satellite navigation systems. |
|
GNS_3 |
The GNSS receiver shall have the capability to support Authentication on the Open Service of Galileo when such service will be provided by the Galileo system and supported by GNSS receiver manufacturers. However, for smart tachographs introduced in the market before the previous conditions are satisfied and not having the capability to support Authentication of the Open Service of Galileo, no retrofitting will be required. |
3. NMEA SENTENCES
This section describes the NMEA sentences used in the functioning of the Smart Tachograph. This section is valid both for the configuration of the Smart Tachograph with or without an external GNSS facility.
|
GNS_4 |
The location data is based on the NMEA sentence Recommended Minimum Specific (RMC) GNSS Data, which contains the Position information (Latitude, Longitude), Time in UTC format (hhmmss.ss), and Speed Over Ground in Knots plus additional values. |
The format of the RMC sentence is the following (as from NMEA V4.1 standard):
Figure 2
Structure of the RMC sentence

The Status gives indication if the GNSS signal is available. Until the value of the Status is not set to A, the received data (e.g., on Time or Latitude/Longitude) cannot be used to record the position of the vehicle in the VU.
The resolution of the position is based on the format of the RMC sentence described above. The first part of the fields 3) and 5) (the first two numbers) are used to represent the degrees. The rest are used to represent the minutes with three decimals. So the resolution is 1/1000 of minute or 1/60000 of degree (because one minute is 1/60 of a degree).
|
GNS_5 |
The Vehicle Unit shall store in the VU database the position information for latitude and longitude with a resolution of 1/10 of minute or 1/600 of a degree as described in Appendix 1 for type GeoCoordinates. The GPS DOP and active satellites (GSA) command can be used by the VU to determine and record the signal availability and accuracy. In particular the HDOP is used to provide an indication on the level of accuracy of the recorded location data (see 4.2.2). The VU will store the value of the Horizontal Dilution of Precision (HDOP) calculated as the minimum of the HDOP values collected on the available GNSS systems. The GNSS System Id indicates GPS, Glonass, Galileo, Beidou or Satellite-Based Augmentation System (SBAS). |
Figure 3
Structure of the GSA sentence

Where the Mode (2) gives an indication if a fix is not available (Mode = 1) or a fix is available for 2D (Mode = 2) or 3D (Mode = 3).
|
GNS_6 |
The GSA sentence shall be stored with record number ‘06’. |
|
GNS_7 |
The maximum size of the NMEA sentences (e.g., RMC, GSA or others), which can be used for the sizing of the read record command shall be 85 bytes (see Table 1). |
4. VEHICLE UNIT WITH AN EXTERNAL GNSS FACILITY
4.1. Configuration
4.1.1 Main components and interfaces
In this configuration, the GNSS receiver is a part of the external GNSS facility.
|
GNS_8 |
The external GNSS facility must be powered with a specific vehicle interface. |
|
GNS_9 |
The external GNSS facility shall consist of the following components (see Figure 4):
|
|
GNS_10 |
The external GNSS facility has at least the following external interfaces:
|
|
GNS_11 |
In the VU, the VU Secure Transceiver is the other end of the secure communication with the GNSS Secure Transceiver and it must support ISO/IEC 7816-4:2013 for the connection to the external GNSS facility. |
|
GNS_12 |
For the physical layer of the communication with the external GNSS facility, the vehicule unit shall support ISO/IEC 7816-12:2005 or another standard able to support ISO/IEC 7816-4:2013. (see 4.2.1). |
4.1.2 External GNSS facility state at the end of production
|
GNS_13 |
The external GNSS facility shall store the following values in the non-volatile memory of the GNSS Secure Transceiver when it leaves the factory:
|
4.2. Communication between the external GNSS facility and the vehicle unit
4.2.1 Communication Protocol
|
GNS_14 |
The communication protocol between the external GNSS facility and the vehicle unit shall support three functions:
|
|
GNS_15 |
The communication protocol shall be based on standard ISO/IEC 7816-4:2013 with the VU Secure Transceiver playing the master role and the GNSS Secure Transceiver playing the slave role. The physical connection between the external GNSS facility and the vehicule unit is based on ISO/IEC 7816-12:2005 or another standard able to support ISO/IEC 7816-4:2013 |
|
GNS_16 |
In the communication protocol, extended length fields shall not supported. |
|
GNS_17 |
The communication protocol of ISO 7816 (both *-4:2013 and *-12:2005) between the external GNSS facility and the VU shall be set to T = 1. |
|
GNS_18 |
Regarding the functions 1) the collection and distribution of GNSS data and 2) the collection of the configuration data of the external GNSS facility and 3) management protocol, the GNSS Secure Transceiver shall simulate a smart card with a file system architecture composed by a Master File (MF), a Directory File (DF) with Application Identifier specified in Appendix 1 chapter 6.2 (‘FF 44 54 45 47 4D’) and with 3 EFs containing certificates and one single Elementary File (EF.EGF) with file identifier equal to ‘2F2F’ as described in Table 1. |
|
GNS_19 |
The GNSS Secure Transceiver shall store the data coming from the GNSS receiver and the configuration in the EF.EGF. This is a linear, variable-length record file with an identifier equal to ‘2F2F’ in hexadecimal format. |
|
GNS_20 |
The GNSS Secure Transceiver shall use a memory to store the data able to perform at least 20 millions write/read cycles. Apart from this aspect, the internal design and implementation of the GNSS Secure Transceiver is left to the manufacturers. The mapping of record numbers and data is provided in Table 1. Note that there are four GSA sentences for the four satellite systems and Satellite-Based Augmentation System (SBAS). |
|
GNS_21 |
The file structure is provided in Table 1. For the access conditions (ALW, NEV, SM-MAC) see Appendix 2 chapter 3.5. Table 1 File Structure
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
4.2.2 Secure transfer of GNSS data
|
GNS_22 |
The secure transfer of GNSS position data shall be allowed only in the following conditions:
|
|
GNS_23 |
Every T seconds, where T is a value lower or equal to 10, unless coupling or mutual authentication and session key agreement takes place, the VU requests from the external GNSS facility the position information on the basis of the following flow:
|
4.2.3 Structure of the Read Record command
This section describes in detail the structure of the Read Record command. Secure messaging (authentication-only mode) is added as described in Appendix 11 Common security mechanisms.
|
GNS_24 |
The command shall support the Secure Messaging authentication-only-mode, see Appendix 11. |
|
GNS_25 |
Command Message
|
|
GNS_26 |
The record referenced in P1 becomes the current record.
|
|
GNS_27 |
The GNSS Secure Transceiver shall support the following tachograph generation 2 commands specified in Appendix 2:
|
4.3. Coupling, mutual authentication and session key agreement of the external GNSS facility with vehicle unit
The coupling, mutual authentication and session key agreement of the external GNSS facility with the vehicle unit is described in Appendix 11. Common security mechanisms, Chapter 11.
4.4. Error Handling
This section describes how potential error conditions by the external GNSS facility are addressed and recorded in the VU.
4.4.1 Communication error with the external GNSS facility
|
GNS_28 |
If the VU does not manage to communicate to the coupled external GNSS facility for more than 20 continuous minutes, the VU shall generate and record in the VU an event of type EventFaultType with the value of enum ‘53’H External GNSS communication fault and with the timestamp set to the current time. The event will be generated only if the following two conditions are satisfied: (a) the Smart Tachograph is not in calibration mode and (b) the vehicle is moving. In this context, a communication error is triggered when the VU Secure Transceiver does not receive a response message after a request message as described in 4.2. |
4.4.2 Breach of the physical integrity of the external GNSS facility
|
GNS_29 |
If the external GNSS facility has been breached, the GNSS Secure Transceiver shall erase all its memory including cryptographic material. As described in GNS_25 and GNS_26, the VU shall detect tampering if the Response has status ‘6690’. The VU shall then generate an event of type EventFaultType enum ‘55’H Tamper detection of GNSS. |
4.4.3 Absence of position information from GNSS receiver
|
GNS_30 |
If the GNSS Secure Transceiver does not receive data from the GNSS receiver for more than 3 continuous hours, the GNSS Secure Transceiver shall generate a response message to the READ RECORD command with RECORD number equal to ‘01’ with a Data Field of 12 bytes all set to 0xFF. Upon reception of the Response message with this value of the data field, the VU shall generate and record an event of type EventFaultType enum ‘52’H external GNSS receiver fault with a timestamp equal to the current value of time only if the following two conditions are satisfied: a) the Smart Tachograph is not in calibration mode and b) the vehicle is moving. |
4.4.4 External GNSS facility certificate expired
|
GNS_31 |
If the VU detects that the EGF certificate used for mutual authentication is not valid any longer, the VU shall generate and record a recording equipment fault of typeEventFaultType enum ‘56’H External GNSS facility certificate expired with a timestamp equal to the current value of time. The VU shall still use the received GNSS position data. |
Figure 4
Schema of the external GNSS facility

5. VEHICLE UNIT WITHOUT AN EXTERNAL GNSS FACILITY
5.1. Configuration
In this configuration, the GNSS receiver is inside the Vehicle Unit as described in Figure 1.
|
GNS_32 |
The GNSS receiver shall act as a talker and transmit NMEA sentences to the VU processor, which shall act as a listener with a frequency of 1/10 Hz or faster for the pre-defined set of NMEA sentences, which shall include at least the RMC and GSA sentences. |
|
GNS_33 |
An external GNSS antenna installed on the vehicle or an internal GNSS antenna shall be connected to the VU. |
5.2. Error Handling
5.2.1 Absence of position information from GNSS receiver
|
GNS_34 |
If the VU does not receive data from the GNSS receiver for more than 3 continous hours, the VU shall generate and record an event of type EventFaultType enum ‘51’H Internal GNSS receiver fault with a timestamp equal to the current value of time only if the following two conditions are satisfied: (a) the Smart Tachograph is not in calibration mode and (b) the vehicle is moving. |
6. GNSS TIME CONFLICT
If the VU detects a discrepancy of more than 1 minute between the time of the vehicle unit's time measurement function and the time originating from the GNSS receiver, the VU will record an event of type EventFaultType enum ‘0B’H Time conflict (GNSS versus VU internal clock). This event is recorded together with the internal clock value of the vehicle unit and comes together with an automatic time adjustment. After a time conflict event has been triggered, the VU will not check the time discrepancy for the next 12 hours. This event shall not be triggered in cases no valid GNSS signal was detectable by the GNSS receiver within the last 30 days. However, when the position information from the GNSS receiver is available again, the automatic time adjustment shall be done.
7. VEHICLE MOTION CONFLICT
|
GNS_35 |
The VU shall trigger and record an Vehicle Motion Conflict event (see in requirement 84 in this Annex) with a timestamp equal to the current value of time, in case motion information calculated from the motion sensor is contradicted by motion information calculated from the internal GNSS receiver or from the external GNSS facility. For the purpose of detecting such contradictions, the median value of the speed differences between these sources shall be used, as specified below:
The Vehicle Motion Conflict event shall be triggered if the median value is above 10 Km/h for five uninterrupted minutes of vehicle movement. Other independent sources of vehicle motion detection may optionnally be used, so that a more reliable detection of tachograph manipulations is provided. (Note: the use of the median on the last 5 minutes is applied to mitigate the risk of measurement outliers and transient values). This event shall not be triggered in the following conditions: (a) during a ferry/train crossing, (b) when the position information from the GNSS receiver shall not be available and (c) while in calibration mode. |
(1) Regulation (EU) No 1285/2013 of the European Parliament and of the Council of 11 December 2013 on the implementation and exploitation of European satellite navigation systems and repealing Council Regulation (EC) No 876/2002 and Regulation (EC) No 683/2008 of the European Parliament and of the Council (OJ L 347, 20.12.2013, p. 1).
Appendix 13
ITS INTERFACE
TABLE OF CONTENTS
|
1. |
INTRODUCTION | 416 |
|
2. |
SCOPE | 416 |
|
2.1. |
Acronyms, definitions and notations | 417 |
|
3. |
REFERENCED REGULATIONS AND STANDARDS | 418 |
|
4. |
INTERFACE WORKING PRINCIPLES | 418 |
|
4.1. |
Preconditions to data transfer via the ITS interface | 418 |
|
4.1.1 |
Data provided through the ITS interface | 418 |
|
4.1.2 |
Content of the Data | 418 |
|
4.1.3 |
ITS Applications | 418 |
|
4.2. |
Communication technology | 419 |
|
4.3. |
PIN authorization | 419 |
|
4.4. |
Message Format | 421 |
|
4.5. |
Driver consent | 425 |
|
4.6. |
Standard data retrieval | 426 |
|
4.7. |
Personal data retrieval | 426 |
|
4.8. |
Event and fault data retrieval | 426 |
1. INTRODUCTION
This Appendix specifies the design and the procedures to follow in order to implement the interface with Intelligent Transport Systems (ITS) as required in Article 10 of Regulation (EU) No. 165/2014 (the Regulation).
The Regulation specifies that the tachographs of vehicles may be equipped with standardised interfaces allowing the data recorded or produced by tachograph to be used in operational mode, by an external device, provided that the following conditions are met:
|
(a) |
the interface does not affect the authenticity and the integrity of the data of the tachograph; |
|
(b) |
the interface complies with the detailed provisions of Article 11 of the Regulation; |
|
(c) |
the external device connected to the interface has access to personal data, including geopositioning data, only after the verifiable consent of the driver to whom the data relates. |
2. SCOPE
The scope of this Appendix is to specify how applications hosted on external devices can via a Bluetooth® connection obtain data (the Data) from a tachograph.
The Data available via this interface is described in the Annex 1 of the present document. This interface does not prohibit the implementation of other interfaces (e.g. via the CAN bus) to transmit the data of the VU to other vehicle processing units.
This Appendix specifies:
|
— |
The Data available through the ITS interface |
|
— |
The Bluetooth® profile that is used to transfer the data |
|
— |
The enquiry and download procedures and sequence of operations |
|
— |
The pairing mechanism between the tachograph and the external device |
|
— |
The consent mechanism available to the driver |
For clarification, this Annex does not specify:
|
— |
The collection of the Data operation and management within the VU (which shall be specified elsewhere within the Regulation or otherwise shall be a function of product design). |
|
— |
The form of presentation of collected data to application hosted on the external device. |
|
— |
Data security provisions above what provides Bluetooth® (such as encryption) concerning the content of the Data (which shall be specified elsewhere within the Regulation [Appendix 10 Common Security Mechanisms]). |
|
— |
The Bluetooth® protocols used by the ITS interface |
2.1. Acronyms, definitions and notations
The following acronyms and definitions specific to this Appendix are used in this appendix:
|
the Communication |
exchange of information/data between a master unit (i.e. the tachographs) and an external unit through the ITS interface over Bluetooth®. |
|
the Data |
Data sets as specified in Annex 1. |
|
the Regulation |
Regulation (EU) No 165/2014 of the European Parliament and of the Council of 4 February 2014 on tachographs in road transport, repealing Council Regulation (EEC) No 3821/85 on recording equipment in road transport and amending Regulation (EC) No 561/2006 of the European Parliament and of the Council on the harmonisation of certain social legislation relating to road transport |
|
BR |
Basic Rate |
|
EDR |
Enhanced Data Rate |
|
GNSS |
Global Navigation Satellite System |
|
IRK |
Identity Resolution Key |
|
ITS |
Intelligent Transport System |
|
LE |
Low Energy |
|
PIN |
Personal Identification Number |
|
PUC |
Personal Unblocking Code |
|
SID |
Service Identifier |
|
SPP |
Serial Port Profile |
|
SSP |
Secure Simple Pairing |
|
TRTP |
Transfer Request Parameter |
|
TREP |
Transfer Response Parameter |
|
VU |
Vehicle Unit |
3. REFERENCED REGULATIONS AND STANDARDS
The specification defined in this Appendix refers to and depends upon all or parts of the following regulations and standards. Within the clauses of this Appendix the relevant standards, or relevant clauses of standards, are specified. In the event of any contradiction the clauses of this Appendix shall take precedence.
Regulations and standards referenced in this Appendix are:
|
— |
Regulation (EU) No 165/2014 of the European Parliament and of the Council of 4 February 2014 on tachographs in road transport, repealing Council Regulation (EEC) No 3821/85 on recording equipment in road transport and amending Regulation (EC) No 561/2006 of the European Parliament and of the Council on the harmonisation of certain social legislation relating to road transport. |
|
— |
Regulation (EC) No 561/2006 of the European Parliament and of the Council of 15 March 2006 on the harmonisation of certain social legislation relating to road transport and amending Council Regulations (EEC) No 3821/85 and (EC) No 2135/98 and repealing Council Regulation (EEC) No 3820/85. |
|
— |
ISO 16844 — 4: Road vehicles — Tachograph systems — Part 4: Can interface |
|
— |
ISO 16844 — 7: Road vehicles — Tachograph systems — Part 7: Parameters |
|
— |
Bluetooth® — Serial Port Profile — V1.2 |
|
— |
Bluetooth® — Core Version 4.2 |
|
— |
NMEA 0183 V4.1 protocol |
4. INTERFACE WORKING PRINCIPLES
4.1. Preconditions to data transfer via the ITS interface
The VU shall be responsible to keep updated and maintain the data to be stored in the VU, without any involvement of the ITS interface. The means by which this is achieved is internal to the VU, specified elsewhere in the Regulation, and is not specified in this Appendix.
4.1.1 Data provided through the ITS interface
The VU shall be responsible to update the data that will be available through the ITS interface at a frequency determined within VU procedures, without any involvement of ITS interface. The VU data shall be used as a basis to populate and update the Data, the means by which this is achieved is specified elsewhere in the Regulation or if there is no such specification is a function of product design and is not specified in this Appendix.
4.1.2 Content of the Data
The content of the Data shall be as specified in Annex 1 of this appendix.
4.1.3 ITS Applications
ITS applications will be using the data made available through the ITS interface for instance to optimize driver activities management while respecting the Regulation, to detect possible faults of the tachograph or to use the GNSS data. The specification of the applications is not within the scope of this Appendix.
4.2. Communication technology
The Data exchange using the ITS interface shall be performed via a Bluetooth® interface compatible via version 4.2 or later. Bluetooth® operates in the unlicensed industrial, scientific and medical (ISM) band at 2.4 to 2.485 GHz. Bluetooth® 4.2 offers enhanced privacy and security mechanisms and increases speed and reliability of data transfers. For the purpose of this specification is Bluetooth® class 2 radio used with a range up to 10 meters. More information on Bluetooth® 4.2 is available on www.bluetooth.com (https://www.bluetooth.org/en-us/specification/adopted-specifications?_ga=1.215147412.2083380574.1435305676).
The Communication shall be established with the communications equipment after a pairing process has been completed by an authorized device. As Bluetooth® is using a master/slave model to control when and where devices can send data, the tachograph will play the role of master while the external device will be the slave.
When an external device comes within range of the VU for the first time, the Bluetooth® pairing process can be initiated (see also annex 2). The devices share their addresses, names, and profiles and common secret key, which allows them to bond whenever they're together in the future. Once this step is completed, the external device is trusted and is in state to initiate requests to download data from the tachograph. It is not foreseen to add encryption mechanisms beyond what Bluetooth® provides. However, if additional security mechanisms are needed, this will be done in accordance with Appendix 10 Common Security Mechanisms.
The overall communication principle is described in the following figure.

The SPP (Serial Port Profile) profile of Bluetooth® shall be used to transfer data from the VU to the external device.
4.3. PIN authorization
For security reasons, the VU shall inforce a PIN code authorization system separated from the Bluetooth pairing. Each VU shall be able to generate PIN codes for authentication purposes composed of at least 4 digits. Every time an external device pairs with the VU, it must provide the correct PIN code before receiving any data.
Succeeding entering the PIN shall result in putting the device on the whitelist. The whitelist shall store at least 64 devices paired with the particular VU.
Failing to provide the correct PIN code three times in a row shall result in putting temporarily the device on the blacklist. While blacklisted, every new attempt from the device shall be rejected. Further failure to provide the correct PIN code three times in a row shall result in increasingly longer ban duration (See table 1). Providing the correct PIN code shall reset the ban duration and the number of attempt. Figure 1 in Annex 2 represents the sequence diagram of a PIN validation attempt.
Table 1
Ban duration depending on the number of consecutive failure to provide the correct PIN code
|
Number of consecutive failure |
Ban duration |
|
3 |
30 seconds |
|
6 |
5 minutes |
|
9 |
1 hour |
|
12 |
24 hours |
|
15 |
Permanent |
Failing to provide the correct PIN code fifteen times (5×3) in a row shall result in a permanent blacklisting of the ITS Unit. Only providing the correct PUC code shall overturn this permanent ban.
The PUC code shall be composed of 8 digits and provided by the manufacturer with the VU. Failing to provide the correct PUC code ten times in a row will irrevocably blacklist the ITS Unit.
While the manufacturer may offers an option to change the PIN code directly through the VU, the PUC code shall not be alterable. Modifying the PIN code, if possible, shall require to enter the current PIN code directly in the VU.
Furthermore any devices stored in the whitelist shall be kept until manual removal of by the user (e.g. via the man-machine-interface of the VU or other means). By doing so lost or stolen ITS-units may be removed from the whitelist. Also, any ITS Unit leaving the Bluetooth connection range for more than 24 hours shall be automatically removed from the VU whitelist and must provide the correct PIN code again when the connection is established again.
The format of the messages between the VU interface and the VU are not provided but left to the discretion of the manufacturer. Said manufacturer shall however ensure the message format between the ITS Unit and the VU interface is respected (see ASN.1 specifications).
Any data request shall thus be met with the proper verification of the sender's credential before any form of treatment. Figure 2 of Annex 2 represents the sequence diagram for this procedure. Any blacklisted device shall receive an automatic rejection, any non-blacklisted non-whitelisted device shall receive a PIN request it needs to fulfill before resending its data request.
4.4. Message Format
All messages exchanged between the ITS Unit and the VU interface shall be formatted with a structure consisting of three parts: A header composed by a target byte (TGT), a source byte (SRC) and a length byte (LEN).
The data field composed by a service identifier byte (SID) and a variable amount of data bytes (maximum 255).
The checksum byte is the 1 byte sum series modulo 256 of all the bytes of the message excluding the CS itself.
The message shall be Big Endian.
Table 2
General message format
|
Header |
Data Field |
Checksum |
||||||
|
TGT |
SRC |
LEN |
SID |
TRTP |
CC |
CM |
DATA |
CS |
|
3 bytes |
Max. 255 bytes |
1 byte |
||||||
Header
TGT and SRC: the ID of the Target (TGT) and Source (SRC) devices of the message. The VU Interface shall have the default ID “EE”. This ID cannot be changed. The ITS Unit shall use the default ID “A0” for its first message of the communication session. The VU Interface shall then assign an unique ID to the ITS Unit and informs it of this ID for future messages during the session.
The LEN byte shall only take into account the ‘DATA’ part of the Data Field (see Table 2), the 4 first bytes are implicit.
The VU Interface shall confirm the authenticity of the message's sender by cross-checking its own IDList with the Bluetooth data by checking the ITS Unit listed at the provided ID is currently in the range of the Bluetooth connection.
Data Field
Besides the SID, the Data Field shall also contain other parameters: a transfer request parameter (TRTP) and Counter bytes.
If the data which need to be carried is too long than the available space in one message, it will be split in several submessage. Each submessage shall have the same Header and SID, but will contain a 2-bytes counter, Counter Current (CC) and Counter Max (CM), to indicate the submessage number. To enable error checking and abort the receiving device acknowledges every submessage. The receiving device can accept the submessage, ask for it to be re-transmitted, request the sending device to start again or abort the transmission.
If not used, CC and CM shall be given the value 0xFF.
For instance, the following message
|
HEADER |
SID |
TRTP |
CC |
CM |
DATA |
CS |
|
3 bytes |
Longer than 255 bytes |
1 byte |
||||
Shall be transmitted as such:
|
HEADER |
SID |
TRTP |
01 |
n |
DATA |
CS |
|
3 bytes |
255 bytes |
1 byte |
||||
|
HEADER |
SID |
TRTP |
02 |
n |
DATA |
CS |
|
3 bytes |
255 bytes |
1 byte |
||||
…
|
HEADER |
SID |
TRTP |
N |
N |
DATA |
CS |
|
3 bytes |
Max. 255 bytes |
1 byte |
||||
Table 3 contains the messages the VU and the ITS Unit shall be able to exchange. The content of each parameter is given in hexadecimal. Aren't represented in the table CC and CM for clarity, see above for complete format.
Table 3
Detailed message content
|
Message |
Header |
DATA |
Checksum |
||||
|
TGT |
SRC |
LEN |
SID |
TRTP |
DATA |
|
|
|
RequestPIN |
ITSID |
EE |
00 |
01 |
FF |
|
|
|
SendITSID |
ITSID |
EE |
01 |
02 |
FF |
ITSID |
|
|
SendPIN |
EE |
ITSID |
04 |
03 |
FF |
4*INTEGER (0..9) |
|
|
PairingResult |
ITSID |
EE |
01 |
04 |
FF |
BOOLEAN (T/F) |
|
|
SendPUC |
EE |
ITSID |
08 |
05 |
FF |
8*INTEGER (0..9) |
|
|
BanLiftingResult |
ITSID |
EE |
01 |
06 |
FF |
BOOLEAN (T/F) |
|
|
RequestRejected |
ITSID |
EE |
08 |
07 |
FF |
Time |
|
|
RequestData |
|
||||||
|
standardTachData |
EE |
ITSID |
01 |
08 |
01 |
|
|
|
personalTachData |
EE |
ITSID |
01 |
08 |
02 |
|
|
|
gnssData |
EE |
ITSID |
01 |
08 |
03 |
|
|
|
standardEventData |
EE |
ITSID |
01 |
08 |
04 |
|
|
|
personalEventData |
EE |
ITSID |
01 |
08 |
05 |
|
|
|
standardFaultData |
EE |
ITSID |
01 |
08 |
06 |
|
|
|
manufacturerData |
EE |
ITSID |
01 |
08 |
07 |
|
|
|
ResquestAccepted |
ITSID |
EE |
Len |
09 |
TREP |
Data |
|
|
DataUnavailable |
|
||||||
|
No data available |
ITSID |
EE |
02 |
0A |
TREP |
10 |
|
|
Personal data not shared |
ITSID |
EE |
02 |
0A |
TREP |
11 |
|
|
NegativeAnswer |
|
||||||
|
General reject |
ITSID |
EE |
02 |
0B |
SID Req |
10 |
|
|
Service not supported |
ITSID |
EE |
02 |
0B |
SID Req |
11 |
|
|
Sub function not supported |
ITSID |
EE |
02 |
0B |
SID Req |
12 |
|
|
Incorrect message length |
ITSID |
EE |
02 |
0B |
SID Req |
13 |
|
|
Conditions not correct or request sequence error |
ITSID |
EE |
02 |
0B |
SID Req |
22 |
|
|
Request out of range |
ITSID |
EE |
02 |
0B |
SID Req |
31 |
|
|
Response pending |
ITSID |
EE |
02 |
0B |
SID Req |
78 |
|
|
ITSID Mismatch |
ITSID |
EE |
02 |
0B |
SID Req |
FC |
|
|
ITSID Not Found |
ITSID |
EE |
02 |
0B |
SID Req |
FB |
|
RequestPIN (SID 01)
This message is issued by the VU Interface if a non-blacklisted but non-whitelisted ITS unit is sending any data request.
SendITSID (SID 02)
This message is issued by the VU Interface whenever a new device is sending a request. This device shall use the default ID “A0” before getting assigned an unique ID for the communication session.
SendPIN (SID 03)
This message is issued by the ITS Unit to be whitelisted from the VU interface. The content of this message is a 4 INTEGER between 0 and 9 code.
PairingResult (SID 04)
This message is issued by the VU Interface to inform the ITS Unit if the PIN code it sent was correct. The content of this message shall be a BOOLEAN with the value ‘True’ if the PIN code was correct and ‘False’ otherwise.
SendPUC (SID 05)
This message is issued by the ITS Unit to lift a blacklist sanction from the VU interface. The content of this message is a 8 INTEGER between 0 and 9 code.
BanLiftingResult (SID 06)
This message is issued by the VU Interface to inform the ITS Unit if the PUC code it sent was correct. The content of this message shall be a BOOLEAN with the value ‘True’ if the PUC code was correct and ‘False’ otherwise.
RequestRejected (SID 07)
This message is issued by the VU Interface as a reply to any message from a blacklisted ITS Unit except ‘SendPUC’. The message shall contain the remaining time the ITS Unit is blacklisted, following the ‘Time’ sequence format as defined in Annex 3.
RequestData (SID 08)
This message for data accessing is issued by the ITS Unit. A one byte transfer request parameter (TRTP) indicates the type of data required. There are several types of data:
|
— |
standardTachData (TRTP 01): Data available from the tachograph classified as non-personal. |
|
— |
personalTachData (TRTP 02): Data available from the tachograph classified as personal. |
|
— |
gnssData (TRTP 03): GNSS data, always personal. |
|
— |
standardEventData (TRTP 04): Recorded event data classified as non-personal. |
|
— |
personalEventData (TRTP 05): Recorded event data classified as personal. |
|
— |
standardFaultData (TRTP 06): Recorded faults classified as non-personal. |
|
— |
manufacturerData (TRTP 07): data made available by the manufacturer. |
See Annex 3 of this appendix for more information about the content of each data type.
See Appendix 12 for more information about the format and content of GNSS data.
See Annex IB and IC for more information about event data code and faults.
ResquestAccepted (SID 09)
This message is issued by the VU Interface if a ITS Unit ‘RequestData’ message has been accepted. This message contains a 1-byte TREP, which is the TRTP byte of the associated RequestData message, and all the data of the requested type.
DataUnavailable (SID 0A)
This message is issued by the VU Interface if, for a certain reason, the requested data aren't available to be sent to a whitelisted ITS Unit. The message contains a 1byte TREP which is the TRTP of the required data and a 1 byte error code specified in the table 3. The Following codes are available:
|
— |
No data available (10): The VU interface can't access the VU data for unspecified reasons. |
|
— |
Personal data not shared (11): The ITS Unit tries to retrieve personal data when they are not shared. |
NegativeAnswer (SID 0B)
These messages are issued by the VU Interface if a request cannot be completed for any other reason than the unavailability of the data. These messages are typically the result of a bad request format (Length, SID, ITSID…) but aren't limited to that. The TRTP in the Data Field contains the SID of the request. The Data Field contains a code identifying the reason of the negative answer. The following codes are available:
|
— |
General Reject (code: 10) |
|
— |
The action can't be performed for a reason which isn't cited below nor in section (Enter DataUnavailable section number). |
|
— |
Service not supported (code: 11) |
|
— |
The request's SID isn't understood. |
|
— |
Sub function not supported (code: 12) |
|
— |
The request's TRTP isn't understood. It can be for instance missing or out of accepted values. |
|
— |
Incorrect message length (code: 13) |
|
— |
The length of the received message is wrong (mismatch between the LEN byte and the actual message length). |
|
— |
Conditions not correct or request sequence error (code: 22) |
|
— |
The required service is not active or the sequence of request messages is not correct |
|
— |
Request out of range (code: 33) |
|
— |
The request parameter record (data field) is not valid |
|
— |
Response pending (code: 78) |
|
— |
The action requested cannot be completed in time and the VU is not ready to accept another request. |
|
— |
ITSID Mismatch (code: FB) |
|
— |
The SRC ITSID doesn't match the associated device after comparison with the Bluetooth information. |
|
— |
ITSID Not Found (code: FC) |
|
— |
The SRC ITSID isn't associated with any device. |
Lines 1 through 72 (FormatMessageModule) of the ASN.1 code in Annex 3 specify the messages format as described in table 3. More details about the messages content is given below.
4.5. Driver consent
All the data available are classified as either standard or personal. Personal data shall only be accessible if the driver gave his/her consent, accepting his/her tachograph personal data can leave the vehicle network for third party applications.
Driver consent is given when, at first insertion of a given driver card or workshop card currently unknown to the vehicle unit, the cardholder is invited to express his consent for tachograph related personal data output through the optional ITS interface. (see also Annex I C paragraph 3.6.2).
The consent status (enabled/disabled) is recorded in the memory of the tachograph.
In case of multiple drivers, only the personal data about the drivers who gave their consent shall be shared with the ITS interface. For instance, if there's two drivers in the vehicle, and only the first driver accepted to share his personal data, the ones concerning the second driver shall not be shared.
4.6. Standard data retrieval
Figure 3 of Annex 2 represents the sequence diagrams of a valid request sent by the ITS Unit to access standard data. The ITS Unit is properly whitelisted and isn't requesting personal data, no further verification is required. The diagrams consider the proper procedure illustrated in Figure 2 of Annex 2 has already been followed. They can be equated to the REQUEST TREATMENT gray box of Figure 2.
Amongst available data, shall be considered standard:
|
— |
standardTachData (TRTP 01) |
|
— |
StandardEventData (TRTP 04) |
|
— |
standardFaultData (TRTP 06) |
4.7. Personal data retrieval
Figure 4 of Annex 2 represents the sequence diagram for personal data request processing. As previously stated, the VU interface shall only send personal data if the driver has given his explicit consent (see also 4.5). Otherwise, the request must be automatically rejected.
Amongst available data, shall be considered personal:
|
— |
personalTachData (TRTP 02) |
|
— |
gnssData (TRTP 03) |
|
— |
personalEventData (TRTP 05) |
|
— |
manufacturerData (TRTP 07) |
4.8. Event and fault data retrieval
ITS units shall be able to request events data containing the list of all the unexpected events. These data are considered standard or personal, see Annex 3. The content of each event is in accordance with the documentation provided in Annex 1 of this appendix.
ANNEX 1
LIST OF AVAILABLE DATA THROUGH THE ITS INTERFACE
|
Data |
Source |
Data classification (personal/not personal) |
|
VehicleIdentificationNumber |
Vehicle Unit |
not personal |
|
CalibrationDate |
Vehicle Unit |
not personal |
|
TachographVehicleSpeed speed instant t |
Vehicle Unit |
personal |
|
Driver1WorkingState Selector driver |
Vehicle Unit |
personal |
|
Driver2WorkingState |
Vehicle Unit |
personal |
|
DriveRecognize Speed Threshold detected |
Vehicle Unit |
not personal |
|
Driver1TimeRelatedStates Weekly day time |
Driver Card |
personal |
|
Driver2TimeRelatedStates |
Driver Card |
personal |
|
DriverCardDriver1 |
Vehicle Unit |
not personal |
|
DriverCardDriver2 |
Vehicle Unit |
not personal |
|
OverSpeed |
Vehicle Unit |
personal |
|
TimeDate |
Vehicle Unit |
not personal |
|
HighResolutionTotalVehicleDistance |
Vehicle Unit |
not personal |
|
ServiceComponentIdentification |
Vehicle Unit |
not personal |
|
ServiceDelayCalendarTimeBased |
Vehicle Unit |
not personal |
|
Driver1Identification |
Driver Card |
personal |
|
Driver2Identification |
Driver Card |
personal |
|
NextCalibrationDate |
Vehicle Unit |
not personal |
|
Driver1ContinuousDrivingTime |
Driver Card |
personal |
|
Driver2ContinuousDrivingTime |
Driver Card |
personal |
|
Driver1CumulativeBreakTime |
Driver Card |
personal |
|
Driver2CumulativeBreakTime |
Driver Card |
personal |
|
Driver1CurrentDurationOfSelectedActivity |
Driver Card |
personal |
|
Driver2CurrentDurationOfSelectedActivity |
Driver Card |
personal |
|
SpeedAuthorised |
Vehicle Unit |
not personal |
|
TachographCardSlot1 |
Driver Card |
not personal |
|
TachographCardSlot2 |
Driver Card |
not personal |
|
Driver1Name |
Driver Card |
personal |
|
Driver2Name |
Driver Card |
personal |
|
OutOfScopeCondition |
Vehicle Unit |
not personal |
|
ModeOfOperation |
Vehicle Unit |
not personal |
|
Driver1CumulatedDrivingTimePreviousAndCurrentWeek |
Driver Card |
personal |
|
Driver2CumulatedDrivingTimePreviousAndCurrentWeek |
Driver Card |
personal |
|
EngineSpeed |
Vehicle Unit |
personal |
|
RegisteringMemberState |
Vehicle Unit |
not personal |
|
VehicleRegistrationNumber |
Vehicle Unit |
not personal |
|
Driver1EndOfLastDailyRestPeriod |
Driver Card |
personal |
|
Driver2EndOfLastDailyRestPeriod |
Driver Card |
personal |
|
Driver1EndOfLastWeeklyRestPeriod |
Driver Card |
personal |
|
Driver2EndOfLastWeeklyRestPeriod |
Driver Card |
personal |
|
Driver1EndOfSecondLastWeeklyRestPeriod |
Driver Card |
personal |
|
Driver2EndOfSecondLastWeeklyRestPeriod |
Driver Card |
personal |
|
Driver1CurrentDailyDrivingTime |
Driver Card |
personal |
|
Driver2CurrentDailyDrivingTime |
Driver Card |
personal |
|
Driver1CurrentWeeklyDrivingTime |
Driver Card |
personal |
|
Driver2CurrentWeeklyDrivingTime |
Driver Card |
personal |
|
Driver1TimeLeftUntilNewDailyRestPeriod |
Driver Card |
personal |
|
Driver2TimeLeftUntilNewDailyRestPeriod |
Driver Card |
personal |
|
Driver1CardExpiryDate |
Driver Card |
personal |
|
Driver2CardExpiryDate |
Driver Card |
personal |
|
Driver1CardNextMandatoryDownloadDate |
Driver Card |
personal |
|
Driver2CardNextMandatoryDownloadDate |
Driver Card |
personal |
|
TachographNextMandatoryDownloadDate |
Vehicle Unit |
not personal |
|
Driver1TimeLeftUntilNewWeeklyRestPeriod |
Driver Card |
personal |
|
Driver2TimeLeftUntilNewWeeklyRestPeriod |
Driver Card |
personal |
|
Driver1NumberOfTimes9hDailyDrivingTimesExceeded |
Driver Card |
personal |
|
Driver2NumberOfTimes9hDailyDrivingTimesExceeced |
Driver Card |
personal |
|
Driver1CumulativeUninterruptedRestTime |
Driver Card |
personal |
|
Driver2CumulativeUninterruptedRestTime |
Driver Card |
personal |
|
Driver1MinimumDailyRest |
Driver Card |
personal |
|
Driver2MinimumDailyRest |
Driver Card |
personal |
|
Driver1MinimumWeeklyRest |
Driver Card |
personal |
|
Driver2MinimumWeeklyRest |
Driver Card |
personal |
|
Driver1MaximumDailyPeriod |
Driver Card |
personal |
|
Driver2MaximumDailyPeriod |
Driver Card |
personal |
|
Driver1MaximumDailyDrivingTime |
Driver Card |
personal |
|
Driver2MaximumDailyDrivingTime |
Driver Card |
personal |
|
Driver1NumberOfUsedReducedDailyRestPeriods |
Driver Card |
personal |
|
Driver2NumberOfUsedReducedDailyRestPeriods |
Driver Card |
personal |
|
Driver1RemainingCurrentDrivingTime |
Driver Card |
personal |
|
Driver2RemainingCurrentDrivingTime |
Driver Card |
personal |
|
GNSS position |
Vehicle Unit |
personal |
(2) CONTINUOUS GNSS DATA AVAILABLE AFTER DRIVER CONSENT
See Appendix 12 — GNSS.
(3) EVENT CODES AVAILABLE WITHOUT DRIVER CONSENT
|
Event |
Storage rules |
Data to be recorded per event |
||||||||||||
|
Insertion of a non-valid card |
|
|
||||||||||||
|
Card conflict |
|
|
||||||||||||
|
Last card session not correctly closed |
|
|
||||||||||||
|
Power supply interruption (2) |
|
|
||||||||||||
|
Communication error with the remote communication facility |
|
|
||||||||||||
|
Absence of position information from GNSS receiver |
|
|
||||||||||||
|
Motion data error |
|
|
||||||||||||
|
Vehicle motion conflict |
|
|
||||||||||||
|
Security breach attempt |
the 10 most recent events per type of event. |
|
||||||||||||
|
Time conflict |
|
|
(4) EVENT CODES AVAILABLE WITH DRIVER CONSENT
|
Event |
Storage rules |
Data to be recorded per event |
||||||||||||||||||
|
Driving without an appropriate card |
|
|
||||||||||||||||||
|
Card insertion while driving |
|
|
||||||||||||||||||
|
Over speeding (1) |
|
|
(5) FAULT DATA CODES AVAILABLE WITHOUT DRIVER CONSENT
|
Fault |
Storage rules |
Data to be recorded per fault |
||||||||||||
|
Card fault |
|
|
||||||||||||
|
Recording equipment faults |
|
|
This fault shall be triggered for any of these failures, while not in calibration mode:
|
— |
VU internal fault |
|
— |
Printer fault |
|
— |
Display fault |
|
— |
Downloading fault |
|
— |
Sensor fault |
|
— |
GNSS receiver or external GNSS facility fault |
|
— |
Remote Communication facility fault |
(6) MANUFACTURER SPECIFIC EVENTS AND FAULTS WITHOUT DRIVER CONSENT
|
Event or Fault |
Storage rules |
Data to be recorded per event |
|
To be defined by Manufacturer |
To be defined by Manufacturer |
To be defined by Manufacturer |
ANNEX 2
SEQUENCE DIAGRAMS OF MESSAGES EXCHANGES WITH THE ITS UNIT.
Figure 1
Sequence Diagram for PIN validation attempt

Figure 2
Sequence Diagram for ITS Unit's authorization verification

Figure 3
Sequence Diagram to process a request for data classified as non-personal (after correct PIN access)

Figure 4
Sequence Diagram to process a request for data classified as personal (after correct PIN access)
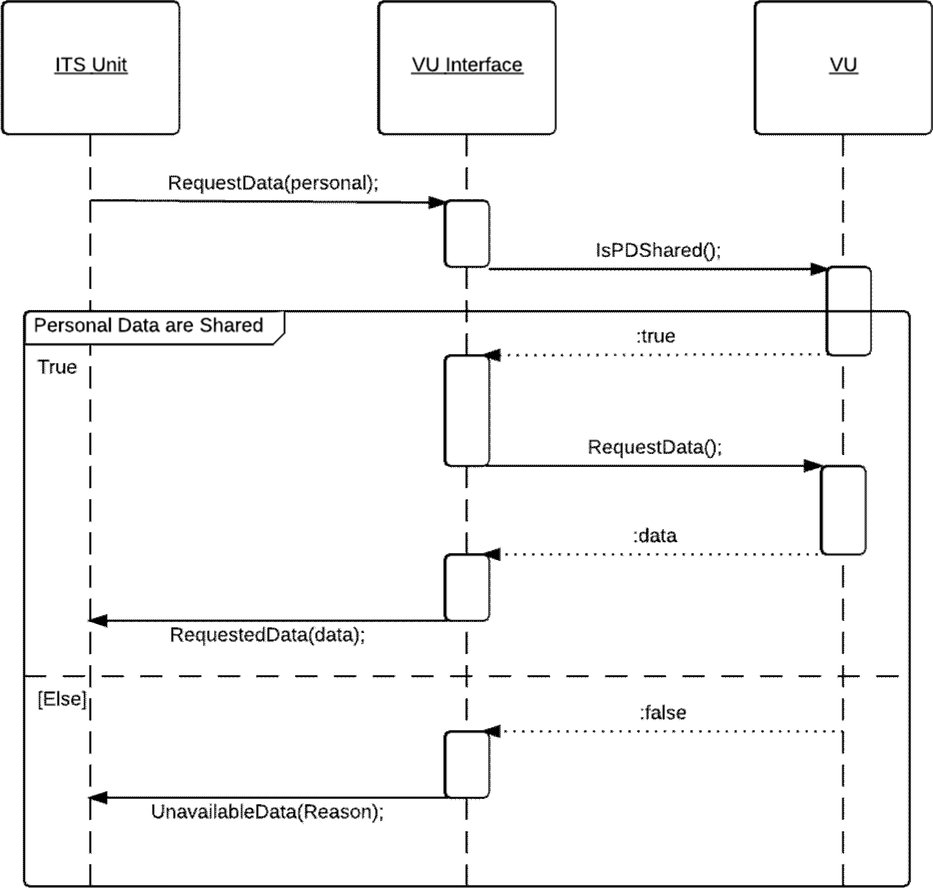
Figure 5
Sequence Diagram for PUC validation attempt
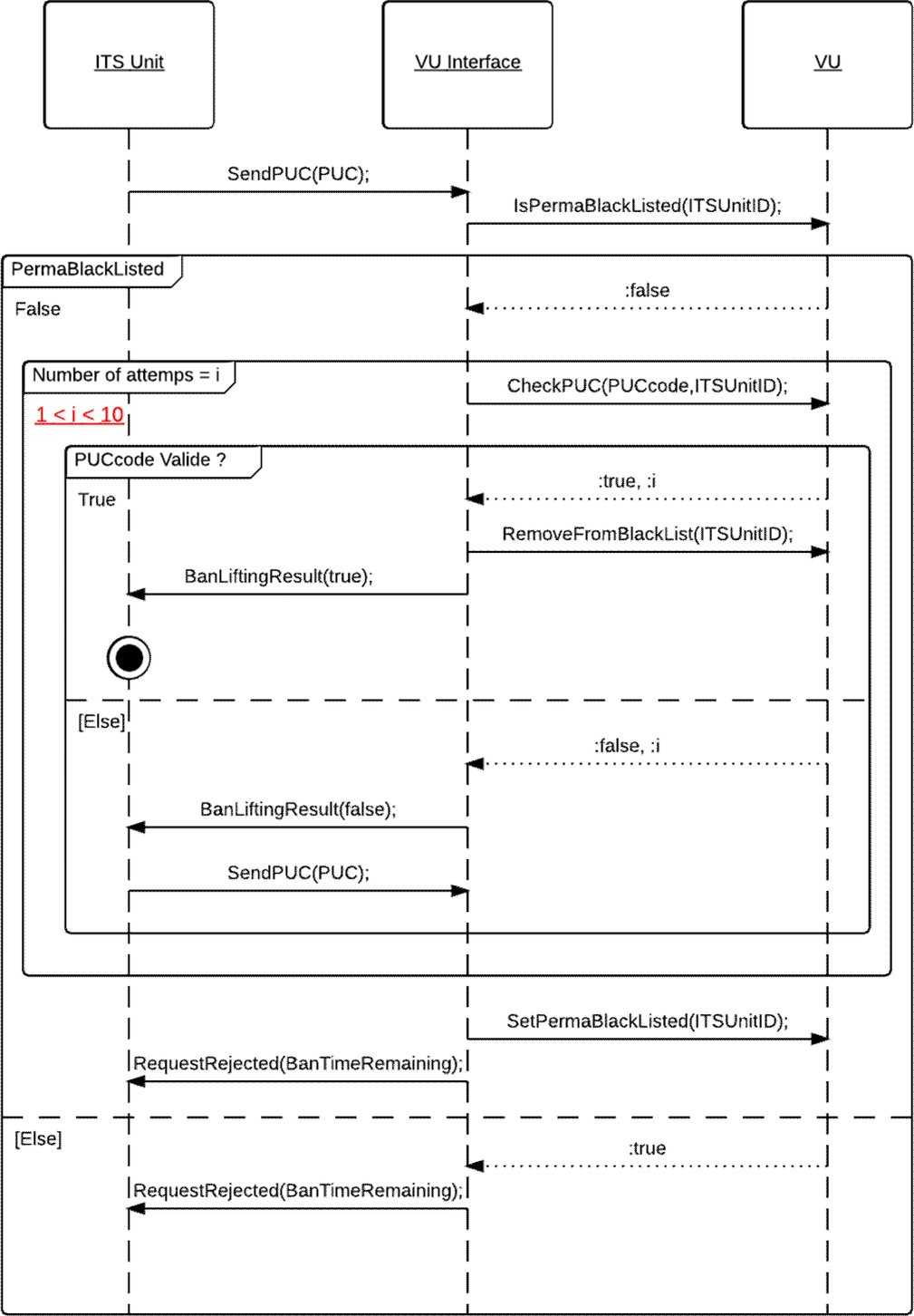
ANNEX 3
ASN.1 SPECIFICATIONS












Appendix 14
REMOTE COMMUNICATION FUNCTION
TABLE OF CONTENTS
|
1. |
INTRODUCTION | 450 |
|
2. |
SCOPE | 451 |
|
3. |
ACRONYMS, DEFINITIONS AND NOTATIONS | 452 |
|
4. |
OPERATIONAL SCENARIOS | 454 |
|
4.1 |
Overview | 454 |
|
4.1.1 |
Preconditions to data transfer via 5.8 GHz DSRC interface | 454 |
|
4.1.2 |
Profile 1a: via a hand aimed or temporary roadside mounted and aimed Remote Early Detection Communication Reader | 455 |
|
4.1.3 |
Profile 1b: via a vehicle mounted and directed Remote Early Detection Communication Reader (REDCR) | 456 |
|
4.2 |
Security/Integrity | 456 |
|
5. |
REMOTE COMMUNICATION DESIGN AND PROTOCOLS | 456 |
|
5.1 |
Design | 456 |
|
5.2 |
Workflow | 459 |
|
5.2.1 |
Operations | 459 |
|
5.2.2 |
Interpretation of the Data received via the DSRC communication | 461 |
|
5.3 |
DSRC Physical interface parameters for remote communication | 461 |
|
5.3.1 |
Location constraints | 461 |
|
5.3.2 |
Downlink and uplink parameters | 461 |
|
5.3.3 |
Antenna design | 466 |
|
5.4 |
DSRC Protocol requirements for RTM | 466 |
|
5.4.1 |
Overview | 466 |
|
5.4.2 |
Commands | 469 |
|
5.4.3 |
Interrogation command sequence | 469 |
|
5.4.4 |
Data structures | 470 |
|
5.4.5 |
Elements of RtmData, actions performed and definitions | 472 |
|
5.4.6 |
Data transfer mechanism | 476 |
|
5.4.7 |
Detailed DSRC transaction description | 476 |
|
5.4.8 |
DSRC Test transaction description | 486 |
|
5.5 |
Support for Directive 2015/71/EC | 490 |
|
5.5.1 |
Overview | 490 |
|
5.5.2 |
Commands | 490 |
|
5.5.3 |
Interrogation command sequence | 490 |
|
5.5.4 |
Data structures | 490 |
|
5.5.5 |
ASN.1 module for the OWS DSRC transaction | 491 |
|
5.5.6 |
Elements of OwsData, actions performed and definitions | 492 |
|
5.5.7 |
Data transfer mechanisms | 492 |
|
5.6 |
Data transfer between the DSRC-VU and VU | 492 |
|
5.6.1 |
Physical Connection and interfaces | 492 |
|
5.6.2 |
Application Protocol | 493 |
|
5.7 |
Error handling | 494 |
|
5.7.1 |
Recording and communication of the Data in the DSRC-VU | 494 |
|
5.7.2 |
Wireless Communication errors | 494 |
|
6. |
COMMISSIONING AND PERIODIC INSPECTION TESTS FOR THE REMOTE COMMUNICATION FUNCTION | 496 |
|
6.1 |
General | 496 |
|
6.2 |
ECHO | 496 |
|
6.3 |
Tests to validate the secure data content | 496 |
1. INTRODUCTION
This Appendix specifies the design and the procedures to follow in order to perform the remote communication function (the Communication) as required in Article 9 of Regulation (EU) No 165/2014 (the Regulation).
|
DSC_1 |
Regulation (EU) No 165/2014 determines that the tachograph shall be equipped with a remote communication functionality that shall enable agents of the competent control authorities to read tachograph information from passing vehicles by using remote interrogation equipment (the Remote early detection communication reader [REDCR]), specifically, interrogation equipment connecting wirelessly using CEN 5.8 GHz Dedicated Short Range Communication (DSRC) interfaces. It is important to comprehend that this functionality is intended to serve only as a pre-filter in order to select vehicles for closer inspection, and it does not replace the formal inspection process as determined in the provisions of Regulation (EU) No 165/2014. See recital 9 in the preamble of this regulation, stating that remote communication between the tachograph and control authorities for roadside control purposes facilitates targeted roadside checks. |
|
DSC_2 |
The Data shall be exchanged using the Communication which shall be a wireless intercourse using 5.8 GHz DSRC wireless communications consistent with this Appendix and tested against the appropriate parameters of EN 300 674-1, {Electromagnetic compatibility and Radio spectrum Matters (ERM); Road Transport and Traffic Telematics (RTTT); Dedicated Short Range Communication (DSRC) transmission equipment (500 kbit/s / 250 kbit/s) operating in the 5,8 GHz Industrial, Scientific and Medical (ISM) band; Part 1: General characteristics and test methods for Road Side Units (RSU) and On -Board Units (OBU)}. |
|
DSC_3 |
The Communication shall be established with the communications equipment only when so requested by the equipment of the competent control authority using compliant radio-communication means (the Remote early detection communication reader (REDCR)). |
|
DSC_4 |
The Data shall be secured to ensure integrity. |
|
DSC_5 |
Access to the Data communicated shall be restricted to competent control authorities authorised to check infringements of Regulation (EC) No 561/2006 and of Regulation (EU) No 165/2014 and to workshops in so far as it is necessary to verify the correct functioning of the tachograph. |
|
DSC_6 |
The Data exchanged during the Communication shall be limited to the data necessary for the purpose of targeting roadside checks of vehicles with a potentially manipulated or misused tachograph. |
|
DSC_7 |
Data integrity and security shall be obtained by securing the Data within the Vehicle Unit (VU) and by passing only the secured payload data and security related data (see 5.4.4) across the wireless 5.8 GHz DSRC remote communication medium, meaning that only authorised persons of competent control authorities have the means to understand the data passed across the Communication and to verify its authenticity. See Appendix 11 Common Security Mechanisms. |
|
DSC_8 |
The Data shall contain a timestamp for the time of its last update. |
|
DSC_9 |
The content of the security data shall be known only to and within the control of the competent control authorities, and those parties with whom they share this information and is outwith the provisions of the Communication that is the subject of this Appendix, save that the Communication makes provision to transfer a packet of security data with every packet of payload data. |
|
DSC_10 |
The same architecture and equipment shall be capable be used to acquire other data concepts (such as weigh–on-board) using the architecture specified herein. |
|
DSC_11 |
For clarification, in accordance with the provisions of Regulation (EU) No 165/2014 (Article 7), data concerning the identity of the driver shall not be communicated across the Communication. |
2. SCOPE
The scope of this Appendix is to specify how agents of the competent control authorities use a specified 5.8 GHz DSRC wireless communication to remotely obtain data (the Data) from a targeted vehicle that identifies that the targeted vehicle is in potential violation of Regulation (EU) No 165/2014 and should be targeted for consideration to be stopped for further investigation.
Regulation (EU) No 165/2014 requires that the Data collected shall be limited to data or pertaining to data that identifies a potential infringement, as defined in Article 9 of Regulation (EU) No 165/2014.
In this scenario, the time available for communication is limited, because the Communication is targeted and of a short- range design. Further, the same communication means for remote tachograph monitoring (RTM) may also be used by the competent control authorities for other applications (such as the maximal weights and dimensions for heavy goods vehicles defined in Directive 2015/719/EU) and such operations may be separate or sequential at the discretion of the competent control authorities.
This Appendix specifies:
|
— |
The communications equipment, procedures and protocols to be used for the Communication |
|
— |
The Standards and Regulations to which the radio equipment shall comply |
|
— |
The presentation of the Data to the Communication equipment |
|
— |
The enquiry and download procedures and sequence of operations |
|
— |
The Data to be transferred |
|
— |
Potential interpretation of the Data transferred across the Communication |
|
— |
The provisions for security data relating to the Communication |
|
— |
The availability of the Data to the competent control authorities |
|
— |
How the Remote early detection communication reader can request different freight and fleet data concepts |
For clarification, this Appendix does not specify:
|
— |
the collection of the Data operation and management within the VU (which shall be a function of product design unless specified elsewhere within Regulation (EU) No 165/2014) |
|
— |
the form of presentation of collected data to the agent of the competent control authorities, nor the criteria which shall be used by the competent control authorities to decide which vehicles to stop (which shall be a function of product design unless specified elsewhere within Regulation (EU) No 165/2014 or a policy decision of the competent control authorities). For clarification: the Communication only makes the Data available to the competent control authorities in order that they may make informed decisions |
|
— |
Data security provisions (such as encryption) concerning the content of the Data (which shall be specified within Appendix 11 Common Security Mechanisms). |
|
— |
detail of any data concepts other than RTM which may be obtained using the same architecture and equipment |
|
— |
detail of the behaviour and management between VU's and the DSRC-VU, nor the behaviour within the DSRC-VU (other than to provide the Data when so requested by an REDCR). |
3. ACRONYMS, DEFINITIONS AND NOTATIONS
The following acronyms and definitions specific to this Appendix are used in this appendix:
|
the Antenna |
electrical device which converts electric power into radio waves, and vice versa used in combination with a radio transmitter or radio receiver. In operation, a radio transmitter supplies an electric current oscillating at radio frequency to the antenna's terminals, and the antenna radiates the energy from the current as electromagnetic waves (radio waves). In reception, an antenna intercepts some of the power of an electromagnetic wave in order to produce a tiny voltage at its terminals, that is applied to a receiver to be amplified |
|
the Communication |
exchange of information/data between a DSRC-REDCR and a DSRC-VU according to section 5 in a master-slave relationship to obtain the Data. |
|
the Data |
secured data of defined format (see 5.4.4) requested by the DSRC-REDCR and provided to the DSRC-REDCR by the DSRC-VU across a 5.8 GHz DSRC link as defined in 5 below |
|
Regulation (EC) No 165/2014 |
Regulation (EU) No 165/2014 of the European Parliament and of the Council of 4 February 2014 on tachographs in road transport, repealing Council Regulation (EEC) No 3821/85 on recording equipment in road transport and amending Regulation (EC) No 561/2006 of the European Parliament and of the Council on the harmonisation of certain social legislation relating to road transport |
|
AID |
Application Identifier |
|
BLE |
Bluetooth Low Energy |
|
BST |
Beacon Service Table |
|
CIWD |
Card insertion while driving |
|
CRC |
cyclic redundancy check |
|
DSC (n) |
identifier of a requirement for a specific DSRC appendix |
|
DSRC |
Dedicated Short Range Communication |
|
DSRC-REDCR |
DSRC — Remote Early Detection Communication Reader. |
|
DSRC-VU |
DSRC — Vehicle Unit. This is the ‘remote early detection facility’ defined in Annex 1C. |
|
DWVC |
Driving without valid card |
|
EID |
Element Identifier |
|
LLC |
Logical Link Control |
|
LPDU |
LLC Protocol Data Unit |
|
OWS |
Onboard Weighing System |
|
PDU |
Protocol Data Unit |
|
REDCR |
Remote early detection communication reader. This is the ‘remote early detection communication reader equipment’ defined in Annex 1C. |
|
RTM |
Remote Tachograph Monitoring |
|
SM-REDCR |
Security Module-Remote early detection communication reader |
|
TARV |
Telematics Applications for Regulated Vehicles (ISO 15638 series of Standards) |
|
VU |
Vehicle Unit |
|
VUPM |
Vehicle Unit Payload Memory |
|
VUSM |
Vehicle Unit Security Module |
|
VST |
Vehicle Service Table |
|
WIM |
Weigh in motion |
|
WOB |
Weigh on board |
The specification defined in this Appendix refers to and depends upon all or parts of the following regulations and standards. Within the clauses of this Appendix the relevant standards, or relevant clauses of standards, are specified. In the event of any contradiction the clauses of this Appendix shall take precedence. In the event of any contradiction where no specification is clearly determined in this Appendix, operating within ERC 70-03 (and tested against the appropriate parameters of EN 300 674-1) shall take precedence, followed in descending order of preference by EN 12795, EN 12253 EN 12834 and EN 13372, 6.2, 6.3, 6.4 and 7.1.
Regulations and standards referenced in this Appendix are:
|
[1] |
Regulation (EU) No 165/2014 of the European Parliament and of the Council of 4 February 2014 on tachographs in road transport, repealing Council Regulation (EEC) No 3821/85 on recording equipment in road transport and amending Regulation (EC) No 561/2006 of the European Parliament and of the Council on the harmonisation of certain social legislation relating to road transport. |
|
[2] |
Regulation (EC) No 561/2006 of the European Parliament and of the Council of 15 March 2006 on the harmonisation of certain social legislation relating to road transport and amending Council Regulations (EEC) No 3821/85 and (EC) No 2135/98 and repealing Council Regulation (EEC) No 3820/85 (Text with EEA relevance). |
|
[3] |
ERC 70-03 CEPT: ECC Recommendation 70-03: Relating to the Use of Short Range Devices (SRD) |
|
[4] |
ISO 15638 Intelligent transport systems — Framework for cooperative telematics applications for regulated commercial freight vehicles (TARV). |
|
[5] |
EN 300 674-1 Electromagnetic compatibility and Radio spectrum Matters (ERM); Road Transport and Traffic Telematics (RTTT); Dedicated Short Range Communication (DSRC) transmission equipment (500 kbit/s / 250 kbit/s) operating in the 5,8 GHz Industrial, Scientific and Medical (ISM) band; Part 1: General characteristics and test methods for Road Side Units (RSU) and On-Board Units (OBU). |
|
[6] |
EN 12253 Road transport and traffic telematics — Dedicated short-range communication — Physical layer using microwave at 5.8 GHz. |
|
[7] |
EN 12795 Road transport and traffic telematics — Dedicated short-range communication — Data link layer: medium access and logical link control. |
|
[8] |
EN 12834 Road transport and traffic telematics — Dedicated short-range communication — Application layer. |
|
[9] |
EN 13372 Road transport and traffic telematics — Dedicated short-range communication — Profiles for RTTT applications |
|
[10] |
ISO 14906 Electronic fee collection — Application interface definition for dedicated short- range communication |
4. OPERATIONAL SCENARIOS
4.1 Overview
Regulation (EU) No 165/2014 provides specific and controlled scenarios within which the Communication is to be used.
The scenarios supported are:
‘Communication Profile 1: Roadside inspection using a short range wireless communication Remote Early Detection Communication Reader instigating a physical roadside inspection (master-:-slave)
Reader Profile 1a: via a hand aimed or temporary roadside mounted and aimed Remote Early Detection Communication
Reader Profile 1b: via a vehicle mounted and directed Remote Early Detection Communication Reader’.
4.1.1 Preconditions to data transfer via 5,8 GHz DSRC interface
NOTE: In order to understand the context of the preconditions the reader is referred to Figure 14.3 below.
4.1.1.1 Data held in VU
|
DSC_12 |
The VU shall be responsible to keep updated every 60 seconds and maintain the data to be stored in the VU, without any involvement of the DSRC communication function. The means by which this is achieved is internal to the VU, specified in Regulation (EU) No 165/2014, Annex 1 C, section 3.19 ‘Remote communication for targeted roadside checks’ and is not specified in this Appendix. |
4.1.1.2 Data provided to DSRC-VU Facility
|
DSC_13 |
The VU shall be responsible to update the DSRC tachograph data (the Data) whenever the data stored in the VU is updated at the interval determined in 4.1.1.1 (DSC_12), without any involvement of the DSRC communication function. |
|
DSC_14 |
The VU data shall be used as a basis to populate and update the Data, the means by which this is achieved, is specified in Annex 1.C, section 3.19 ‘Remote communication for targeted roadside checks’ or if there is no such specification it is a function of product design and is not specified in this Appendix. For the design of the connection between DSRC-VU facility and the VU, please refer to section 5.6. |
4.1.1.3 Content of the Data
|
DSC_15 |
The content and format of the Data shall be such that, once decrypted, it shall be structured and made available in the form and format specified in 5.4.4 of this Appendix (Data structures). |
4.1.1.4 Data presentation
|
DSC_16 |
The Data, having been kept frequently updated in accordance with the procedures determined in 4.1.1.1, shall be secured prior to presentation to the DSRC-VU, and presented as a secured data concept value, for temporary storage in the DSRC-VU as the current version of the Data. This data is transferred from the VUSM to the DSRC function VUPM. The VUSM and VUPM are functions and not necessarily physical entities. The form of physical instantiation to perform these functions shall be a matter of product design unless specified elsewhere in Regulation (EU) No 165/2014. |
4.1.1.5 Security data
|
DSC_17 |
Security data (securityData), comprising the data required by the REDCR to complete its ability to decrypt the Data shall be supplied as defined in Appendix 11 Common Security Mechanisms and presented as a data concept value, for temporary storage in the DSRC-VU as the current version of securityData, in the form defined in this Appendix section 5.4.4. |
4.1.1.6 VUPM data available for transfer across the DSRC interface
|
DSC_18 |
The data concept which shall always be available in the DSRC function VUPM for immediate transfer upon request by the REDCR is defined in section 5.4.4 for full ASN.1 Module specifications. |
General overview of communication Profile 1
This profile covers the use case where an agent of the competent control authorities, uses a short range remote communication Remote Early Detection Communication Reader (5.8 GHz DSRC interfaces operating within ERC 70-03, and tested against the appropriate parameters of EN 300 674-1 as described in section 5) (the REDCR) to remotely identify a vehicle which is potentially in violation of Regulation (EU) No 165/2014. Once identified, the agent of the competent control authorities who is controlling the interrogation decides whether the vehicle should be stopped.
4.1.2 Profile 1a: via a hand aimed or temporary roadside mounted and aimed Remote Early Detection Communication Reader
In this use case the agent of the competent control authorities is situated at the roadside, and aims a hand held, tripod mounted, or similar portable, REDCR from the roadside towards the centre of the windshield of the targeted vehicle. The interrogation is made using 5.8 GHz DSRC interfaces operating within ERC 70-03, and tested against the appropriate parameters of EN 300 674-1 as described in section 5. See Figure 14.1 (Use Case 1).
Figure 14.1
Roadside interrogation using 5,8 GHz DSRC

4.1.3 Profile 1b: via a vehicle mounted and directed Remote Early Detection Communication Reader (REDCR)
In this use case the agent of the competent control authorities is situated within a moving vehicle, and either aims a hand held, portable REDCR from the vehicle towards the centre of the windshield of the targeted vehicle, or the REDCR is mounted within or on the vehicle so as to point towards the centre of the windshield of the targeted vehicle when the Remote Early Detection Communication Reader's vehicle is in a particular position relevant to the targeted vehicle (for example directly ahead in a stream of traffic). The interrogation is made using 5.8 GHz DSRC interfaces operating within ERC 70-03, and tested against the appropriate parameters of EN 300 674-1 as described in section 5. See Figure 14.2. (Use Case 2).
Figure 14.2
Vehicle based interrogation using 5,8 GHz DSRC

4.2 Security/Integrity
To give the possibility to verify the authenticity and integrity of downloaded data through the remote communication, the secured Data is verified and decrypted in accordance with Appendix 11 Common Security Mechanisms.
5. REMOTE COMMUNICATION DESIGN AND PROTOCOLS
5.1 Design
The design of the remote communication function in the Smart Tachograph is shown as described in Figure 14.3.
Figure 14.3
Design of the remote communication function

|
DSC_19 |
The following functions are located in the VU:
|
|
DSC_20 |
The Antenna and The Communication shall operate within ERC 70-03, tested against the appropriate parameters of EN 300 674-1 as described in section 5. The Antenna and the Communication can implement mitigation techniques against the risk of wireless interference as described in ECC report 228 using e.g., filters in the CEN DSRC 5.8 GHz communication. |
|
DSC_21 |
The DSRC antenna shall be connected to the DSRC-VU facility either directly within the module mounted to or close to the windshield, or through a dedicated cable constructed in a manner to make illegal disconnection difficult. Disconnection of or interference with the functioning of Antenna shall be a violation of Regulation (EU) No 165/2014. Deliberate masking or otherwise detrimentally affecting the operational performance of the Antenna shall be construed as a violation of Regulation (EU) No 165/2014. |
|
DSC_22 |
The form factor of the antenna is not defined and shall be a commercial decision, so long as the fitted DSRC-VU meets the conformance requirements defined in section 5 below. The antenna shall be positioned as determined in DSC_19 and shown in figure 14.4 (oval line) and it efficiently supports the use cases described in in 4.1.2 and 4.1.3. |
Figure 14.4
Example of positioning of the 5,8 GHz DSRC antenna in the windshield of regulated vehicles

The form factor of the REDCR and its antenna may vary according to the circumstances of the reader (tripod mounted, hand held, vehicle mounted, etc.) and the modus operandi employed by the agent of the competent control authorities.
A display and/or notification function is used to present the results of the remote communication function to the agent of the competent control authorities. A display may be provided on a screen, as a printed output, an audio signal, or a combination of such notifications. The form of such display and/or notification is a matter of the requirements of the agents of the competent control authorities and equipment design and is not specified within this Appendix.
|
DSC_23 |
The design and form factor of the REDCR shall be a function of commercial design, operating within ERC 70-03, and the design and performance specifications defined in this Appendix, (section 5.3.2), thus providing the marketplace maximum flexibility to design and provide equipment to cover the specific interrogation scenarios of any particular competent control authority. |
|
DSC_24 |
The design and form factor of the DSRC-VU and its positioning inside or outside the VU shall be a function of commercial design, operating within ERC 70-03 and the design and performance specifications defined in this Appendix (section 5.3.2) and within this Clause (5.1). |
|
DSC_25 |
However, the DSRC-VU shall be reasonably capable to accept data concept values from other intelligent vehicle equipment by means of an open industry standard connection and protocols. (For example from weigh on board equipment), so long as such data concepts are identified by unique and known application identifiers/file names, and the instructions to operate such protocols shall be made available to the European Commission, and available without charge to manufacturers of relevant equipment. |
5.2 Workflow
5.2.1 Operations
The workflow of operations is represented in Figure 14.5.
Figure 14.5
Workflow for remote communication function

The steps are described below:
|
a. |
Whenever the vehicle is in operation (ignition ON) the tachograph is providing data to the VU function. The VU function prepares the Data for the remote communication function (encrypted) and updates the VUPM held in the memory of the DSRC-VU (as defined in 4.1.1.1 — 4.1.1.2). The Data collected shall be formatted as determined in 5.4.4 — 5.4.5 below. |
|
b. |
On every occasion that the Data is updated, the timestamp defined in the security data concept shall be updated. |
|
c. |
The VUSM function secures the data in accordance with the procedures determined in Appendix 11. |
|
d. |
On every occasion that the Data is updated (see 4.1.1.1 — 4.1.1.2), the Data shall be transferred to the DSRC-VU, where it replaces any previous data, in order that updated current data (the Data) shall always be available to be provided in the event of an interrogation by an REDCR. When supplied by the VU to the DSRC-VU the Data shall be identifiable by the filename RTMData or by ApplicationID and Attribute identifiers. |
|
e. |
If an agent of the competent control authorities wishes to target a vehicle and collect the Data from the targeted vehicle, the agent of the competent control authorities shall first insert his/her smartcard in the REDCR to enable the Communication and to allow the SM-REDCR to verify its authenticity and decrypt the data. |
|
f. |
The agent of the competent control authority then targets a vehicle and requests the data through remote communication. The REDCR opens a 5.8 GHz DSRC interface session with the DSRC-VU of the targeted vehicle, and requests the Data. The Data is transferred to the REDCR through the wireless communication system as a DSRC Attribute using the Application service GET as defined in 5.4. The Attribute contains the encrypted payload data values and the DSRC security data. |
|
g. |
The data is analyzed by the REDCR equipment and provided to the agent of the competent control authority. |
|
h. |
The agent of the competent control authority uses the data to assist in a decision of whether or not to stop for a detailed inspection, or ask another agent of the competent control authority to stop the vehicle. |
5.2.2 Interpretation of the Data received via the DSRC communication
|
DSC_26 |
Data received across the 5.8 GHz interface shall carry the meaning and import defined in 5.4.4 and 5.4.5 below and only that meaning and import, and shall be understood within the objectives defined therein. In accordance with the provisions of Regulation (EU) No 165/2014, the Data shall be used only to provide relevant information to a competent control authority to assist them to determine which vehicle should be stopped for physical inspection, and shall be subsequently destroyed in accordance with Article 9 of Regulation (EU) No 165/2014. |
5.3 DSRC Physical interface parameters for remote communication
5.3.1 Location constraints
|
DSC_27 |
The remote interrogation of vehicles using a 5.8GHz DSRC interface should not be used within 200 metres of an operational 5.8 GHz DSRC gantry. |
5.3.2 Downlink and uplink parameters
|
DSC_28 |
The equipment used for remote tachograph monitoring shall conform to and operate within ERC70-03 and the parameters defined in Tables 14.1 and 14.2 below. |
|
DSC_29 |
Further, to ensure compatibility with the operational parameters of other standardised 5.8 GHz DSRC systems, the equipment used for remote tachograph monitoring shall conform to parameters from EN 12253 and EN 13372. |
Namely:
Table 14.1
Downlink parameters
|
Item No |
Parameter |
Value(s) |
Remark |
||||||||
|
D1 |
Downlink Carrier Frequencies |
There are four alternatives which may be used by an REDCR:
|
Within ERC 70-03. Carrier Frequencies may be selected by the implementer of the roadside system and need not be known in the DSRC-VU (Consistent with EN 12253, EN 13372) |
||||||||
|
D1a (*) |
Tolerance of Carrier Frequencies |
within ± 5 ppm |
(Consistent with EN 12253) |
||||||||
|
D2 (*) |
RSU (REDCR) Transmitter Spectrum Mask |
Within ERC 70-03. REDCR shall be according to Class B,C as defined in EN 12253. No other specific requirement within this Annex |
Parameter used for controlling interference between interrogators in proximity (as defined in EN 12253 and EN 13372). |
||||||||
|
D3 |
OBU(DSRC-VU) Minimum Frequency Range |
5,795 — 5,815 GHz |
(Consistent with EN 12253) |
||||||||
|
D4 (*) |
Maximum E.I.R.P. |
Within ERC 70-03 (unlicensed) and within National Regulation Maximum + 33 dBm |
(Consistent with EN 12253) |
||||||||
|
D4a |
Angular E.I.R.P. mask |
According to declared and published specification of interrogator designer |
(Consistent with EN 12253) |
||||||||
|
D5 |
Polarisation |
Left hand circular |
(Consistent with EN 12253) |
||||||||
|
D5a |
Cross-Polarisation |
XPD: In bore sight: (REDCR) RSU t ≥ 15 dB (DSRC-VU) OBU r ≥ 10 dB At -3 dB area: (REDCR) RSU t ≥ 10 dB (DSRC-VU) OBU r ≥ 6 dB |
(Consistent with EN 12253) |
||||||||
|
D6 (*) |
Modulation |
Two level amplitude modulation. |
(Consistent with EN 12253) |
||||||||
|
D6a (*) |
Modulation Index |
0,5 ... 0,9 |
(Consistent with EN 12253) |
||||||||
|
D6b |
Eye Pattern |
≥ 90 % (time) / ≥ 85 % (amplitude) |
|
||||||||
|
D7 (*) |
Data Coding |
FM0 ‘1’ bit has transitions only at the beginning and end of the bit interval. ‘0’ bit has an additional transition in the middle of the bit interval compared to the ‘1’ bit. |
(Consistent with EN 12253) |
||||||||
|
D8 (*) |
Bit rate |
500 kBit/s |
(Consistent with EN 12253) |
||||||||
|
D8a |
Tolerance of Bit Clock |
better than ± 100 ppm |
(Consistent with EN 12253) |
||||||||
|
D9 (*) |
Bit Error Rate (B.E.R.) for communication |
≤ 10– 6 when incident power at OBU (DSRC-VU) is in the range given by [D11a to D11b]. |
(Consistent with EN 12253) |
||||||||
|
D10 |
Wake-up trigger for OBU (DSRC-VU) |
OBU (DSRC-VU) shall wake up on receiving any frame with 11 or more octets (including preamble) |
No special wake-up pattern is necessary. DSRC-VU may wake up on receiving a frame with less than 11 octets (Consistent with EN 12253) |
||||||||
|
D10a |
Maximum Start Time |
≤ 5 ms |
(Consistent with EN 12253) |
||||||||
|
D11 |
Communication zone |
Spatial region within which a B.E.R. according to D9a is achieved |
(Consistent with EN 12253) |
||||||||
|
D11a (*) |
Power Limit for communication (upper). |
– 24dBm |
(Consistent with EN 12253) |
||||||||
|
D11b (*) |
Power Limit for communication (lower). |
Incident power:
|
(Consistent with EN 12253) Extended requirement for horizontal angles up to ±45°, due to the use cases defined in this annex. |
||||||||
|
D12 (*) |
Cut-off power level of (DSRC-VU) |
– 60 dBm |
(Consistent with EN 12253) |
||||||||
|
D13 |
Preamble |
Preamble is mandatory. |
(Consistent with EN 12253) |
||||||||
|
D13a |
Preamble Length and Pattern |
16 bits ± 1 bit of FM0 coded ‘1’ bits |
(Consistent with EN 12253) |
||||||||
|
D13b |
Preamble Wave form |
An alternating sequence of low level and high level with pulse duration of 2 μs. The tolerance is given byD8a |
(Consistent with EN 12253) |
||||||||
|
D13c |
Trailing Bits |
The RSU (REDCR) is permitted to transmit a maximum of 8 bits after the end flag. An OBU (DSRC-VU) is not required to take these additional bits into account. |
(Consistent with EN 12253) |
Table 14.2
Uplink parameters
|
Item No. |
Parameter |
Value(s) |
Remark |
||||||
|
U1 (**) |
Sub-carrier Frequencies |
A OBU (DSRC-VU) shall support 1,5 MHz and 2,0 MHz An RSU (REDCR) shall support 1,5 MHz or 2,0 MHz or both. U1-0: 1,5 MHz U1-1: 2,0 MHz |
Selection of sub-carrier frequency (1,5 MHz or 2,0 MHz) depends on the EN 13372 profile selected. |
||||||
|
U1a (**) |
Tolerance of Sub- carrier Frequencies |
within ± 0,1 % |
(Consistent with EN 12253) |
||||||
|
U1b |
Use of Side Bands |
Same data on both sides |
(Consistent with EN 12253) |
||||||
|
U2 (**) |
OBU (DSRC-VU) Transmitter Spectrum Mask |
According to EN12253
|
(Consistent with EN 12253) |
||||||
|
U4a (**) |
Maximum Single Side Band E.I.R.P. (boresight) |
Two options:
|
According to declared and published specification of equipment designer |
||||||
|
U4b (**) |
Maximum Single Side Band E.I.R.P. (35°) |
Two options:
|
According to declared and published specification of equipment designer |
||||||
|
U5 |
Polarisation |
Left hand circular |
(Consistent with EN 12253) |
||||||
|
U5a |
Cross Polarisation |
XPD: In bore sight: (REDCR) RSU r ≥ 15 dB (DSRC-VU) OBU t ≥ 10 dB At – 3 dB: (REDCR) RSU r ≥ 10 dB (DSRC-VU) OBU t ≥ 6 dB |
(Consistent with EN 12253) |
||||||
|
U6 |
Sub-Carrier Modulation |
2-PSK Encoded data synchronised with sub-carrier: Transitions of encoded data coincide with transitions of sub- carrier. |
(Consistent with EN 12253) |
||||||
|
U6b |
Duty Cycle |
Duty Cycle: 50 % ± α, α ≤ 5 % |
(Consistent with EN 12253) |
||||||
|
U6c |
Modulation on Carrier |
Multiplication of modulated sub- carrier with carrier. |
(Consistent with EN 12253) |
||||||
|
U7 (**) |
Data Coding |
NRZI (No transition at beginning of ‘1’ bit, transition at beginning of ‘0’ bit, no transition within bit) |
(Consistent with EN 12253) |
||||||
|
U8 (**) |
Bit Rate |
250 kbit/s |
(Consistent with EN 12253) |
||||||
|
U8a |
Tolerance of Bit Clock |
Within ± 1 000 ppm |
(Consistent with EN 12253) |
||||||
|
U9 |
Bit Error Rate (B.E.R.) for communication |
≤10– 6 |
(Consistent with EN 12253) |
||||||
|
U11 |
Communication Zone |
The spatial region within which the DSRC-VU is situated such that its transmissions are received by the REDCR with a B.E.R. of less than that given by U9a. |
(Consistent with EN 12253) |
||||||
|
U12a (**) |
Conversion Gain (lower limit) |
1 dB for each side band Range of angle: Circularly symmetric between bore sight and ± 35° and |
|
||||||
|
within – 45° ± 45° Corresponding to the plane parallel to the road surface when the DSRC-VU later is installed in the vehicle (Azimuth) |
Greater that the specified value range for horizontal angles up to ± 45°, due to the use cases defined in this annex. |
||||||||
|
U12b (**) |
Conversion Gain (upper limit) |
10 dB for each side band |
Less than the specified value range for each side band within a circular cone around boresight of ± 45° opening angle |
||||||
|
U13 |
Preamble |
Preamble is mandatory. |
(Consistent with EN 12253) |
||||||
|
U13a |
Preamble Length and Pattern |
32 to 36 μs modulated with sub- carrier only, then 8 bits of NRZI coded ‘0’ bits. |
(Consistent with EN 12253) |
||||||
|
U13b |
Trailing Bits |
The DSRC-VU is permitted to transmit a maximum of 8 bits after the end flag. A RSU (REDCR) is not required to take these additional bits into account. |
(Consistent with EN 12253) |
5.3.3 Antenna design
5.3.3.1 REDCR antenna
|
DSC_30 |
The design of the REDCR antenna shall be a function of commercial design, operating within the limits defined in 5.3.2 which is adapted to optimise the reading performance of the DSRC-REDCR for the specific purpose and read circumstances in which the REDCR has been designed to operate. |
5.3.3.2 VU antenna
|
DSC_31 |
The design of the DSRC-VU antenna shall be a function of commercial design, operating within the limits defined in 5.3.2 which is adapted to optimise the reading performance of the DSRC-REDCR for the specific purpose and read circumstances in which the REDCR has been designed to operate. |
|
DSC_32 |
The VU antenna shall be fixed to, or close to, the front windshield of the vehicle as specified in 5.1 above. |
|
DSC_33 |
In the test environment in a workshop (see section 6.3), a DSRC-VU antenna, affixed according to 5.1 above, shall successfully connect with a standard test communication and successfully provide an RTM transaction as defined within this Appendix, at a distance between 2 and 10 meters, better than 99 % of the time, averaged over 1 000 read interrogations. |
5.4 DSRC Protocol requirements for RTM
5.4.1 Overview
|
DSC_34 |
The transaction protocol to download the Data across the 5.8 GHz DSRC interface link shall be according to the following steps. This section describes a transaction flow under ideal conditions without retransmissions or communication interrupts. NOTE The purpose of the initialisation phase (Step 1) is to set up the communication between the REDCR and DSRC-VUs that have entered the 5.8 GHz DSRC (master-slave) transaction zone but have not yet established communication with the REDCR, and to notify the application processes.
|
— |
Step 1
Initialisation. The REDCR sends a frame containing a ‘beacon service table’ (BST) that includes the application identifiers (AIDs) in the service list that it supports. In the RTM application this will simply be the service with the AID value = 2 (Freight&Fleet). The DSRC-VU evaluates the received BST, and shall respond (see below) with the list of the supported applications within the Freight&Fleet domain, or shall not respond if none are supported. If the REDCR does not offer AID=2, the DSRC-VU shall not answer to the REDCR.
— |
Step 2
The DSRC-VU sends a frame containing a request for a private window allocation.
— |
Step 3
The REDCR sends a frame containing a private window allocation.
— |
Step 4
The DSRC-VU uses the allocated private window to send a frame containing its vehicle service table (VST). This VST includes a list of all the different application instantiations that this DSRC-VU supports in the framework of AID=2. The different instantiations shall be identified by means of uniquely generated EIDs, each associated with an Application Context Mark parameter value indicating the application and standard supported.
— |
Step 5
Next the REDCR analyses the offered VST, and either terminates the connection (RELEASE) since it is not interested in anything the VST has to offer (i.e. it is receiving a VST from a DSRC-VU that is not supporting the RTM transaction), or, if it receives an appropriate VST it starts an app instantiation.
— |
Step 6
To bring this about, the REDCR shall send a frame containing a command to retrieve the RTM data, identifying the RTM application instantiation by specifying the identifier corresponding to the RTM application instantiation (as specified by the DSRC-VU in the VST), and shall allocate a private window.
— |
Step 7
The DSRC-VU uses the newly allocated private window to send a frame that contains the addressed identifier corresponding to the RTM application instantiation as provided in the VST, followed by the attribute RtmData (payload element + security element).
— |
Step 8
If there are multiple services requested, the value ‘n’ is changed to the next service reference number and the process repeated.
— |
Step 9
The REDCR confirms receipt of the data by sending a frame containing a RELEASE command to the DSRC-VU to terminate the session OR if it has failed to validate a successful receipt of the LDPU goes back to step 6.
Figure 14.6
RTM over 5,8 GHz DSRC process flow

5.4.2 Commands
|
DSC_35 |
The following commands are the only functions used in an RTM transaction phase — INITIALISATION.request : A command, issued from the REDCR in the form of a broadcast with definition of applications that the REDCR supports. — INITIALISATION.response : An answer from the DSRC-VU confirming the connection and containing a list of supported application instances with characteristics and information how to address them (EID). — GET.request : A command, issued from the REDCR to the DSRC-VU, that specifies the application instantiation to be addressed by means of a defined EID, as received in the VST, instructing the DSRC-VU to send the selected attribute(s) with the Data. The objective of the GET command is for the REDCR to obtain the Data from the DSRC-VU. — GET.response : An answer from the DSRC-VU that contains the Data requested. — ACTION.request ECHO : A command, instructing the DSRC-VU to send back data from the DSRC-VU to the REDCR. The objective of the ECHO command is to enable workshops or type approval test facilities to test that the DSRC link is working without needing access to security credentials. — ACTION.response ECHO: An answer from the DSRC VU on the ECHO command. — EVENT_REPORT.request RELEASE: A command, instructing the DSRC-VU that the transaction is ended. The objective of the RELEASE command is to end the session with the DSRC-VU. On receipt of the RELEASE the DSRC-VU shall not respond to any further interrogations under the current connection. Note that according to EN 12834 a DSRC-VU will not connect twice to the same interrogator unless it has been out of the communication zone for 255 seconds or if the Beacon ID of the interrogator is changed. |
5.4.3 Interrogation command sequence
|
DSC_36 |
From the perspective of the command and response sequence, the transaction is described as follows:
An example of the transaction sequence and contents of the exchanged frames is defined in clauses 5.4.7 and 5.4.8 |
5.4.4 Data structures
|
DSC_37 |
The semantic structure of the Data when passed across the 5.8 GHz DSRC interface shall be consistent with what described in this Appendix. The way these data are structured is specified in this clause. |
|
DSC_38 |
The payload (RTM data) consists of the concatenation of
|
|
DSC_39 |
The RTM Data is being addressed as RTM Attribute=1 and is transferred in the RTM container = 10. |
|
DSC_40 |
The RTM Context Mark shall identify the supported standard part in the TARV series of standards (RTM corresponds to Part 9) The ASN.1 module definition for the DSRC data within the RTM application is defined as follows:  Text of image
Text of image
 Text of image
Text of image
|
5.4.5 Elements of RtmData, actions performed and definitions
|
DSC_41 |
The data values to be calculated by the VU and used to update the secured data in the DSRC-VU shall be calculated according to the rules defined in Table 14.3: Table 14.3 Elements of RtmData, actions performed and definitions
|
5.4.6 Data transfer mechanism
|
DSC_42 |
Payload data defined previously are requested by the REDCR after initialisation phase, and consequently transmitted by the DSRC-VU in the allocated window. The command GET is used by the REDCR to retrieve data. |
|
DSC_43 |
For all DSRC exchanges, data shall be encoded using PER (Packed Encoding Rules). |
5.4.7 Detailed DSRC transaction description
|
DSC_44 |
Initialisation is performed according to DSC_44 — DSC_48 and Tables 14.4 — 14.9. In the initialisation phase, the REDCR starts sending a frame containing a BST (Beacon Service Table) according to EN 12834 and EN 13372, 6.2, 6.3, 6.4 and 7.1 with settings as specified in the following Table 14.4. Table 14.4 Initialisation — BST frame settings
A practical example of the settings specified in Table 14.4, with an indication of bit encodings, is given in the following Table 14.5. Table 14.5 Initialisation — BST frame contents example
|
|
DSC_45 |
A DSRC-VU, when receiving a BST, requires the allocation of a private window, as specified by EN 12795 and EN 13372, 7.1.1, with no specific RTM settings. Table 14.6 provides an example of bit encoding. Table 14.6 Initialisation — Private window allocation request frame contents
|
|
DSC_46 |
The REDCR then answers by allocating a private window, as specified by EN 12795 and EN 13372, 7.1.1 with no specific RTM settings. Table 14.7 provides an example of bit encoding. Table 14.7 Initialisation — Private window allocation frame contents
|
|
DSC_47 |
The DSRC-VU, when receiving the private window allocation, sends its VST (Vehicle Service Table) as defined in EN 12834 and EN 13372, 6.2, 6.3, 6.4 and 7.1 with settings as specified Table 14.8, using the allocated transmission window. Table 14.8 Initialisation — VST frame settings
|
|
DSC_48 |
The DSRC-VU shall support the ‘Freight and Fleet’ application, identified by the Application Identifier ‘2’. Other Application Identifiers may be supported, but shall not be present in this VST, as the BST only requires AID=2. The ‘Applications’ field contains a list of the supported application instances in the DSRC-VU. For each supported application instantiation, a reference to the appropriate standard is given, made of an Rtm Context mark, which is composed of an OBJECT IDENTIFIER representing the related standard, its part (9 for RTM) and possibly its version, plus an EID that is generated by the DSRC-VU, and associated to that application instance. A practical example of the settings specified in Table 14.8, with an indication of bit encodings, is given in Table 14.9. Table 14.9 Initialisation — VST frame contents example
|
|
DCS_49 |
The REDCR then reads the data by issuing a GET command, conforming to the GET command defined in EN 13372, 6.2, 6.3, 6.4 and EN 12834, with settings as specified in Table 14.10. Table 14.10 Presentation — GET request frame settings
Table 14.11 shows an example of reading the RTM data. Table 14.11 Presentation — Get Request frame example
|
|
DSC_50 |
The DSRC-VU, when receiving the GET request, sends a GET response with the requested data conforming to the GET response defined in EN 13372, 6.2, 6.3, 6.4 and EN 12834, with settings as specified in Table 14.12. Table 14.12 Presentation — GET response frame settings
Table 14.13 shows an example of reading the RTM data. Table 14.13 Presentation — Response frame contents example
|
|
DSC_51 |
The REDCR then closes the connection by issuing a EVENT_REPORT, RELEASE command conforming to EN 13372, 6.2, 6.3, 6.4 and EN 12834,7.3.8, with no specific RTM settings. Table 14.14 shows a bit encoding example of the RELEASE command. Table 14.14 Termination. EVENT_REPORT Release frame contents
|
|
DSC_52 |
The DSRC-VU is not expected to answer to the Release command. The communication is then closed. |
5.4.8 DSRC Test transaction description
|
DSC_53 |
Full tests that include securing the data, need to be carried out as defined in Appendix 11 Common Security Mechanisms, by authorised persons with access to security procedures, using the normal GET command as defined above. |
|
DSC_54 |
Commissioning and periodic inspection tests that require decrypting and comprehension of the decrypted data content shall be undertaken as specified in Appendix 11 Common Security Mechanisms and Appendix 9, Type Approval List of Minimum required tests. However, the basic DSRC communication can be tested by the command ECHO. Such tests may be required on commissioning, at periodic inspection, or otherwise to the requirement of the competent control authority or Regulation (EU) No 165/2014 (See 6 below) |
|
DSC_55 |
In order to effect this basic communication test, the ECHO command is issued by the REDCR during a session, i.e., after an initialisation phase has been completed successfully. The sequence of interactions is thus similar to that of an interrogation:
|
— | Step 1
The REDCR sends a ‘beacon service table’ (BST) that includes the application identifiers (AIDs) in the service list that it supports. In the RTM applications this will simply be the service with the AID value = 2.
— |
Step 2
The DSRC-VU sends a request for a private window allocation.
— |
Step 3
The REDCR sends a private window allocation.
— |
Step 4
The DSRC-VU uses the allocated private window to send its vehicle service table (VST). This VST includes a list of all the different application instantiations that this DSRC-VU supports in the framework of AID=2. The different instantiations shall be identified by means of uniquely EIDs, each associated with a parameter value indicating the instance of the application that is supported.
— |
Step 5
Next the REDCR analyses the offered VST, and either terminates the connection (RELEASE) since it is not interested in anything the VST has to offer (i.e., it is receiving a VST from a DSRC-VU that is not an RTM VU, or, if it receives an appropriate VST it starts an app instantiation.
— |
Step 6
The REDCR shall issue a command (ECHO) to the specific DSRC-VU, and allocates a private window.
— |
Step 7
The DSRC-VU uses the newly allocated private window to send an ECHO response frame.
The following tables give a practical example of an ECHO exchange session.
|
DSC_56 |
Initialisation is performed according to 5.4.7 (DSC_44 — DSC_48) and Tables 14.4 — 14.9 |
|
DSC_57 |
The REDCR then issues an ACTION, ECHO command conforming to ISO 14906, containing 100 octets of data and with no specific settings for RTM. Table 14.15 shows the contents of the frame sent by the REDCR. Table 14.15 ACTION, ECHO request frame example
|
|
DSC_58 |
The DSRC-VU, when receiving the ECHO request, sends an ECHO response of 100 octets of data by reflecting the received command, according to ISO 14906, with no specific settings for RTM. Table 14.16 shows a bit level encoding example. Table 14.16 ACTION, ECHO response frame example
|
5.5 Support for Directive 2015/71/EC
5.5.1 Overview
|
DSC_59 |
To support the Directive 2015/719/EC on the maximal weights and dimensions for heavy goods vehicles, the transaction protocol to download OWS data across the 5.8 GHz DSRC interface link will be the same as that used for the RTM data (see 5.4.1), the only difference being that the Object Identifier that relates to the TARV standard will be addressing the ISO 15638 standard (TARV) Part 20 related to WOB/OWS. |
5.5.2 Commands
|
DSC_60 |
The commands used for an OWS transaction will be the same as those used for an RTM transaction. |
5.5.3 Interrogation command sequence
|
DSC_61 |
The interrogation command sequence for OWS data will be the same as for RTM data. |
5.5.4 Data structures
|
DSC_62 |
The payload (OWS data) consists of the concatenation of
|
5.5.5 ASN.1 module for the OWS DSRC transaction
|
DSC_63. |
The ASN.1 module definition for the DSRC data within the RTM application is defined as follows:  Text of image
Text of image
|
5.5.6 Elements of OwsData, actions performed and definitions
The elements of OwsData are defined to support Directive 2015/719/EC on the maximal weights and dimensions for heavy goods vehicles. Their meaning is:
|
— |
recordedWeight represents the total measured weight of the heavy goods vehicle with a resolution of 10 Kg as defined in EN ISO 14906. For example, a value of 2500, represent a weight of 25 tons. |
|
— |
axlesConfiguration represents the configuration of the heavy goods vehicle as number of axles. The configuration is defined with the bit mask of 20 bits (extended from EN ISO 14906). A bit mask of 2 bits represents the configuration of an axle with the following format:
The last 4 bits are reserved for future uses.
|
||||||||||||||||||||||||||||||||||||||||
|
— |
axlesRecordedWeight represent the specific weight recorded for each axle with a resolution of 10 Kg. Two octets are used for each axle. For example, a value of 150, represent a weight of 1 500 Kgs. |
The other data types are defined in 5.4.5.
5.5.7 Data transfer mechanisms
|
DSC_64 |
The Data transfer mechanism for OWS data between the Interrogator and the DSRC facility in the vehicle shall be the same as for RTM data (see 5.4.6). |
|
DSC_65 |
The Data transfer between the platform collecting the maximal weights data and the DSRC facility in the vehicle shall be based on the physical connection and interfaces and protocol defined in section 5.6. |
5.6 Data transfer between the DSRC-VU and VU
5.6.1 Physical Connection and interfaces
|
DSC_66 |
The connection between the VU and the DSRC-VU can be either by physical cable or short range wireless communication based on Bluetooth v4.0 BLE. |
|
DSC_67 |
Regardless of the choice of the physical connection and interface, the following requirements shall be satisfied: |
|
DSC_68 |
|
|
DSC_69 |
|
|
DSC_70 |
|
5.6.2 Application Protocol
|
DSC_71 |
The application protocol between the VU Remote Communication facility and DSRC-VU is responsible for periodically transferring the remote communication data from the VU to the DSRC. |
|
DSC_72 |
The following main commands are identified:
|
|
DSC_73 |
In ASN1.0, the previous commands may be defined as:  Text of image
Text of image
|
|
DSC_74 |
The description of the commands and parameters is following:
|
|
DSC_75 |
The initialization of the communication link shall be done only after installation, calibration, and start of the engine/VU is switched on.
|
|
DSC_76 |
At the restart of the DSRC-VU or a VU, all the existing Communication Links should be removed as there could be ‘dangling’ Links due to the sudden shutdown of a VU.
|
5.7 Error handling
5.7.1 Recording and communication of the Data in the DSRC-VU
|
DSC_77 |
The Data shall be provided, already secured, by the VUSM function to the DSRC-VU. The VUSM shall verify that data recorded in the DSRC-VU has been recorded correctly. The recording and reporting of any errors in the transfer of data from the VU to the memory of the DSRC-VU shall be recorded with type EventFaultType and enum value set to ‘62’H Remote Communication Facility communication fault together with the timestamp. |
|
DSC_78 |
The VU shall maintain a file identified by a unique name that is easily identifiable by inspectors for the purpose of recording ‘VU internal communication failures’. |
|
DSC_79 |
If the VUPM attempts to obtain VU data from the security module (to pass to the VU-DSRC), but fails to do so, it shall record that failure with type EventFaultType and enum value set to ‘62’H Remote Communication Facility' communication fault together with the timestamp. The failure of the communication is detected when a
|
5.7.2 Wireless Communication errors
|
DSC_80 |
Communication error handling shall be consistent with the related DSRC standards, namely EN 300 674-1, EN 12253, EN 12795, EN 12834 and the appropriate parameters of EN 13372. |
5.7.2.1 Encryption and signature errors
|
DSC_81 |
Encryption and signature errors shall be handled as defined in Appendix 11 Common Security Mechanisms and are not present in any error messages associated with the DSRC transfer of data. |
5.7.2.2 Recording of errors
The DSRC medium is a dynamic wireless communication in an environment of uncertain atmospheric and interference conditions, particularly in the ‘portable REDCR’ and ‘moving vehicle’ combinations involved in this application. It is therefore necessary to ascertain the difference between a ‘read failure’ and an ‘error’ condition. In a transaction across a wireless interface, read failure is common and the consequence is usually to retry, i.e. rebroadcast the BST and reattempt the sequence, which will in most circumstances lead to a successful communication connection and transfer of data, unless the target vehicle moves out of range during the time required to retransmit. (A ‘successful’ instance of a ‘read’ may have involved several attempts and retries).
Read failure may be because the antennas were not paired properly (failure of ‘aiming’); because one of the antennas is shielded — this may be deliberate, but also can be caused by the physical presence of another vehicle; radio interference, especially from circa 5.8 GHz WIFI or other public access wireless communications, or may be caused by radar interference, or difficult atmospheric conditions (e.g. during a thunderstorm); or simply by moving out of the range of the DSRC communication. Individual instances of read failures, by their nature, cannot be recorded, simply because the communication simply did not occur.
However, if the agent of the competent control authority targets a vehicle and attempts to interrogate its DSRC-VU, but no successful transfer of data ensues, this failure could have occurred because of deliberate tampering, and therefore the agent of the competent control authority needs a means to log the failure, and alert colleagues downstream that there may be a violation. The colleagues can then stop the vehicle and carry out a physical inspection. However, as no successful communication has taken place, the DSRC-VU cannot provide data concerning the failure. Such reporting shall therefore be a function of REDCR equipment design.
‘Failure to read’ is technically different to an ‘error’. In this context an ‘error’ is the acquisition of a wrong value.
Data transferred to the DSRC-VU is supplied already secured, therefore must be verified by the supplier of the data (see 5.4).
Data subsequently transferred across the air interface is checked by cyclic redundancy checks at the communications level. If the CRC validates, then the data is correct. If the CRC does not validate, the data is retransmitted. The probability that data could successfully pass through a CRC incorrectly is statistically so highly improbable that it may be discounted.
If the CRC does not validate and there is no time to retransmit and receive the correct data, then the result will not be an error, but an instantiation of a specific type of read failure.
The only meaningful ‘failure’ data that can be recorded is that of the number of successful initiations of transactions that occur, that do not result in a successful transfer of data to the REDCR.
|
DSC_82 |
The REDCR shall therefore record, time-stamped, the number of occasions where the ‘initialisation’ phase of a DSRC interrogation is successful, but the transaction terminated before the Data was successfully retrieved by the REDCR. This data shall be available to agent of the competent control authority and shall be stored in the memory of the REDCR equipment. The means by which this is achieved shall be a matter of product design or the specification of a competent control authority. The only meaningful ‘error’ data that can be recorded is the number of occasions where the REDCR fails to decrypt the Data received. However, it should be noted that this will only relate to the efficiency of the REDCR software. Data may be technically decrypted, but make no semantic sense. |
|
DSC_83 |
The REDCR shall therefore record, time-stamped, the number of occasions where it has attempted but failed to decipher data received across the DSRC interface. |
6. COMMISSIONING AND PERIODIC INSPECTION TESTS FOR THE REMOTE COMMUNICATION FUNCTION
6.1 General
|
DSC_84 |
Two type of tests are foreseen for the remote communication function:
|
6.2 ECHO
This clause contains provisions specifically made to test only that the DSRC-REDCR >>-:-<DSRC-VU is functionally active.
The objective of the ECHO command is to enable workshops or type approval test facilities to test that the DSRC link is working without needing access to security credentials. The tester's equipment therefore only needs to be able to initialise a DSRC communication (sending a BST with AID=2) and then send the ECHO command, and, assuming the DSRC is working, will receive the ECHO response. See 5.4.8 for details. Assuming it receives this response correctly, the DSRC link (DSRC-REDCR >>-:-<DSRC-VU) may be validated as functioning correctly.
6.3 Tests to validate the secure data content
|
DSC_85 |
This test is execute to validate the end-to-end security flow of data. A DSRC test reader is needed for such test. The DSRC test reader performs the same functionality and it is implemented with the same specifications of the reader used by the law enforcers, with the difference that a workshop card shall be used to authenticate the user of the DSRC test reader rather than a control card. The test can be executed after the initial activation of a Smart Tachograph or at the end of the calibration procedure. After the activation, the vehicle unit shall generate and communicate to the DSRC-VU the secured early detection data. |
|
DSC_86 |
The workshop personnel must position the DSRC test reader at a distance between 2 and 10 metres in front of the vehicle. |
|
DSC_87 |
Then the workshop personnel will insert a workshop card in the DSRC test reader to request the interrogation of the early detection data to the vehicle unit. After a successful interrogation, the workshop personnel will access the received data to ensure that it has been successfully validated for integrity and decrypted. |
(*) – Downlink parameters subject to conformance testing in accordance with relevant parameter test from EN 300 674-1.
(**) – Uplink parameters subject to conformance testing in accordance with relevant parameter test from EN 300 674-1
Appendix 15
MIGRATION: MANAGING THE CO-EXISTENCE OF EQUIPMENT GENERATIONS
TABLE OF CONTENT
|
1. |
DEFINITIONS | 497 |
|
2. |
GENERAL PROVISIONS | 497 |
|
2.1. |
Overview of the transition | 497 |
|
2.2. |
Interoperability between vu and cards | 498 |
|
2.3. |
Interoperability between VU and MS | 498 |
|
2.4. |
Interoperability between vehicle units, tachograph cards and equipment for data download | 498 |
|
2.4.1 |
Direct card download by IDE | 498 |
|
2.4.2 |
Card download through a vehicle unit | 499 |
|
2.4.3 |
Vehicle unit download | 499 |
|
2.5. |
Interoperability between VU and calibration equipment | 499 |
|
3. |
MAIN STEPS DURING THE PERIOD BEFORE THE INTRODUCTION DATE | 499 |
|
4. |
PROVISIONS FOR THE PERIOD AFTER THE INTRODUCTION DATE | 499 |
1. DEFINITIONS
For the purposes of this Appendix, the following definitions are used.
smart tachograph system as defined by this Annex (chapter 1: definition bbb);
first generation tachograph system as defined by this Regulation (article 2: definition 1);
second generation tachograph system as defined by this Regulation (article 2: definition 7);
introduction date as defined by this Annex (chapter 1: definition ccc);
Intelligent Dedicated Equipment (IDE) equipment used to perform data downloading, as defined in Appendix 7 of this Annex.
2. GENERAL PROVISIONS
2.1. Overview of the transition
The preamble of this Annex provides an overview of the transition between the first and the second generation tachograph systems.
In addition to the provisions of this preamble:
|
— |
first generation motion sensors will not be interoperable with second generation vehicle units. |
|
— |
second generation motion sensors will start to be installed in vehicles at the same time as second generation vehicle units. |
|
— |
data download and calibration equipment will need to evolve, in order to support use of both generation of recording equipment and tachograph cards. |
2.2. Interoperability between VU and cards
It is understood that first generation tachograph cards are interoperable with first generation vehicle units (in compliance with Annex 1B of this Regulation), while second generation tachograph cards are interoperable with second generation vehicle units (in compliance with Annex 1C of this Regulation). In addition, the requirements below shall apply.
|
MIG_001 |
Except as provided for in requirement MIG_004 and MIG_005, first generation tachograph cards may continue to be used in second generation vehicle units until their end of validity date. Their holders may however ask for their replacement by second generation tachograph cards as soon as they are available. |
|
MIG_002 |
Second generation vehicle units shall be able to use any valid first generation driver, control and company card inserted. |
|
MIG_003 |
This capability may be suppressed once and forever in such vehicle units by workshops, so that first generation tachograph cards cannot be accepted anymore. This may only be done after the European Commission has launched a procedure aiming to request workshops to do so, for example during each periodic inspection of tachograph. |
|
MIG_004 |
Second generation vehicle units shall only be able to use second generation workshop cards. |
|
MIG_005 |
For determining the mode of operation, second generation vehicle units shall only consider the types of the valid cards inserted, regardless of their generations. |
|
MIG_006 |
Any valid second generation tachograph card shall be able to be used in first generation vehicle units exactly the same manner as a first generation tachograph card of the same type. |
2.3. Interoperability between VU and MS
It is understood that first generation motion sensors are interoperable with first generation vehicle units, while second generation motion sensors are interoperable with second generation vehicle units. In addition, the requirements below shall apply.
|
MIG_007 |
Second generation vehicle units will not be able to be paired and used with first generation motion sensors. |
|
MIG_008 |
Second generation motion sensors may be paired and used with second generation vehicle units only, or with both generations of vehicle units. |
2.4. Interoperability between vehicle units, tachograph cards and equipment for data download
|
MIG_009 |
Equipment for data download may be used with one generation only of vehicle units and tachograph cards, or with both. |
2.4.1 Direct card download by IDE
|
MIG_010 |
Data shall be downloaded by IDE from tachograph cards of one generation inserted in their card readers, using the security mechanisms and the data download protocol of this generation, and downloaded data shall have the format defined for this generation. |
|
MIG_011 |
To allow drivers' control by non EU control authorities, it shall also be possible to download second generation driver (and workshop) cards exactly the same manner as 1st generation drivers (and workshop) cards. Such download shall include:
Such download shall not include application data EFs only present in second generation driver (and workshop) cards (application data EFs within |
2.4.2 Card download through a vehicle unit
|
MIG_012 |
Data shall be downloaded from a second generation card inserted in a first generation vehicle unit using the first generation data download protocol. The card shall answer to the vehicle unit commands exactly the same manner as a first generation card and downloaded data shall have the same format as data downloaded from a first generation card. |
|
MIG_013 |
Data shall be downloaded from a first generation card inserted in a second generation vehicle unit using the data download protocol defined in Appendix 7 of this Annex. The vehicle unit shall send commands to the card exactly the same manner as a first generation vehicle unit, and downloaded data shall respect the format defined for first generation cards. |
2.4.3 Vehicle unit download
|
MIG_014 |
Data shall be downloaded from second generation vehicle units using the second generation security mechanisms, and the data download protocol specified in Appendix 7 of this Annex. |
|
MIG_015 |
To allow drivers' control by non EU control authorities and vehicle unit data download by non EU workshops, it may optionally also be possible to download data from second generation vehicle units using the first generation security mechanisms, and the first generation data download protocol. Downloaded data shall have the same format as data downloaded from a first generation vehicle unit. This capability may be selected through commands in the menu. |
2.5. Interoperability between VU and calibration equipment
|
MIG_016 |
Calibration equipment shall be able to perform calibration of each generation of tachograph, using the calibration protocol of this generation. Calibration equipment may be used with one generation only of tachograph, or with both. |
3. MAIN STEPS DURING THE PERIOD BEFORE THE INTRODUCTION DATE
|
MIG_017 |
Test keys and certificates shall be available to manufacturers at the latest 30 months before the introduction date. |
|
MIG_018 |
Interoperability tests shall be ready to start if requested by manufacturers at the latest 15 months before the introduction date. |
|
MIG_019 |
Official keys and certificates shall be available to manufacturers at the latest 12 months before the introduction date. |
|
MIG_020 |
Member states shall be able to issue second generation workshop cards at the latest 3 months before the introduction date. |
|
MIG_021 |
Member States shall be able to issue all types of second generation tachograph cards at the latest 1 month before the introduction date. |
4. PROVISIONS FOR THE PERIOD AFTER THE INTRODUCTION DATE
|
MIG_022 |
After the introduction date, Member States shall only issue second generation tachograph cards. |
|
MIG_023 |
Vehicle units/motion sensors manufacturers shall be allowed to produce first generation vehicle units/motion sensors as long as they are used in the field, so that malfunctioning components can be replaced. |
|
MIG_024 |
Vehicle units/motion sensors manufacturers shall be allowed to request and obtain type approval maintenance of first generation vehicle units/motion sensors types already type approved. |
Appendix 16
ADAPTOR FOR M1 AND N1 CATEGORY VEHICLES
TABLE OF CONTENTS
|
1. |
ABBREVIATIONS AND REFERENCE DOCUMENTS | 501 |
|
1.1. |
Abbreviations | 501 |
|
1.2. |
Reference standards | 501 |
|
2. |
GENERAL CHARACTERISTICS AND FUNCTIONS OF THE ADAPTOR | 502 |
|
2.1. |
Adaptor general description | 502 |
|
2.2. |
Functions | 502 |
|
2.3. |
Security | 502 |
|
3. |
REQUIREMENTS FOR THE RECORDING EQUIPMENT WHEN AN ADAPTOR IS INSTALLED | 502 |
|
4. |
CONSTRUCTION AND FUNCTIONAL REQUIREMENTS FOR THE ADAPTOR | 503 |
|
4.1. |
Interfacing and adapting incoming speed pulses | 503 |
|
4.2. |
Inducing the incoming pulses to the embedded motion sensor | 503 |
|
4.3. |
Embedded motion sensor | 503 |
|
4.4. |
Security requirements | 503 |
|
4.5. |
Performance characteristics | 504 |
|
4.6. |
Materials | 504 |
|
4.7. |
Markings | 504 |
|
5. |
INSTALLATION OF THE RECORDING EQUIPMENT WHEN AN ADAPTOR IS USED | 504 |
|
5.1. |
Installation | 504 |
|
5.2. |
Sealing | 505 |
|
6. |
CHECKS, INSPECTIONS AND REPAIRS | 505 |
|
6.1. |
Periodic inspections | 505 |
|
7. |
TYPE APPROVAL OF RECORDING EQUIPMENT WHEN AN ADAPTOR IS USED | 505 |
|
7.1. |
General points | 505 |
|
7.2. |
Functional certificate | 506 |
1. ABBREVIATIONS AND REFERENCE DOCUMENTS
1.1. Abbreviations
|
TBD |
To Be Defined |
|
VU |
Vehicle Unit |
1.2. Reference standards
ISO16844-3 Road vehicles — Tachograph systems — Part 3: Motion sensor interface
2. GENERAL CHARACTERISTICS AND FUNCTIONS OF THE ADAPTOR
2.1. Adaptor general description
|
ADA_001 |
The adaptor shall provide a connected VU with secured motion data permanently representative of vehicle speed and distance travelled. The adaptor is only intended for those vehicles that are required to be equipped with recording equipment in compliance with this Regulation. It shall be installed and used only in those types of vehicle defined in definition yy) ‘adaptor’ of Annex IC where it is not mechanically possible to install any other type of existing motion sensor which is otherwise compliant with the provisions of this Annex and its Appendixes 1 to 16. The adaptor shall not be mechanically interfaced to a moving part of the vehicle, but connected to the speed/distance impulses which are generated by integrated sensors or alternative interfaces. |
|
ADA_002 |
A type approved motion sensor (according to the provisions of this Annex IC, section 8, Type approval of recording equipment and tachograph cards) shall be fitted into the adaptor housing, which shall also include a pulse converter device inducing the incoming pulses to the embedded motion sensor. The embedded motion sensor itself shall be connected to the VU, so that the interface between the VU and the adaptor shall be compliant with the requirements set out in ISO16844-3. |
2.2. Functions
|
ADA_003 |
The adaptor shall include the following functions:
|
2.3. Security
|
ADA_004 |
The adaptor shall not be security certified according to the motion sensor generic security target defined in Appendix 10 of this Annex. Security related requirements specified in section 4.4 of this Appendix shall apply instead. |
3. REQUIREMENTS FOR THE RECORDING EQUIPMENT WHEN AN ADAPTOR IS INSTALLED
The requirements in the following Chapters indicate how the requirements of this Annex shall be understood when an adaptor is used. The related requirement numbers of Annex IC are provided between brackets.
|
ADA_005 |
The recording equipment of any vehicle fitted with an adaptor must comply with all the provisions of this Annex, except otherwise specified in this Appendix. |
|
ADA_006 |
When an adaptor is installed, the recording equipment includes cables, the adaptor (including a motion sensor), and a VU [01]. |
|
ADA_007 |
The detection of events and/or faults function of the recording equipment is modified as follows:
|
|
ADA_008 |
The adaptor faults detectable by the recording equipment shall be those related with the embedded motion sensor [88]. |
|
ADA_009 |
The VU calibration function shall allow to automatically pair the embedded motion sensor with the VU [202, 204]. |
4. CONSTRUCTION AND FUNCTIONAL REQUIREMENTS FOR THE ADAPTOR
4.1. Interfacing and adapting incoming speed pulses
|
ADA_011 |
The adaptor input interface shall accept frequency pulses representative of the vehicle speed and distance travelled. Electrical characteristics of the incoming pulses are: TBD by the manufacturer. Adjustments accessible to only the adaptor manufacturer, and to the approved workshop performing the adaptor installation shall allow the correct interfacing of the adaptor input to the vehicle, if applicable. |
|
ADA_012 |
The adaptor input interface shall be able, if applicable, to multiply or divide the frequency pulses of the incoming speed pulses by a fixed factor, to adapt the signal to the k factor range defined by this Annex (4 000 to 25 000 pulses/km). This fixed factor may only be programmed by the adaptor manufacturer, and the approved workshop performing the adaptor installation. |
4.2. Inducing the incoming pulses to the embedded motion sensor
|
ADA_013 |
The incoming pulses, possibly adapted as specified above, shall be induced to the embedded motion sensor, so that each incoming pulse shall be detected by the motion sensor. |
4.3. Embedded motion sensor
|
ADA_014 |
The embedded motion sensor shall be stimulated by the induced pulses, thus allowing it to generate motion data accurately representing the vehicle movement, as if it was mechanically interfaced to a moving part of the vehicle. |
|
ADA_015 |
The identification data of the embedded motion sensor shall be used by the VU to identify the adaptor [95]. |
|
ADA_016 |
The installation data stored in the embedded motion sensor shall be considered to represent the adaptor installation data [122]. |
4.4. Security requirements
|
ADA_017 |
The adaptor housing shall be designed so that it cannot be opened. It shall be sealed, so that physical tampering attempts can be easily detected (e.g. through visual inspection, see ADA_035). Seals shall follow the same requirements of motion sensor seals [398 to 406] |
|
ADA_018 |
It shall not be possible to remove the embedded motion sensor from the adaptor without breaking the seal(s) of the adaptor housing, or breaking the seal between the sensor and the adaptor housing (see ADA_034). |
|
ADA_019 |
The adaptor shall ensure that motion data may only been processed and derived from the adaptor input. |
4.5. Performance characteristics
|
ADA_020 |
The adaptor shall be fully operational in the temperature range defined by the manufacturer. |
|
ADA_021 |
The adaptor shall be fully operational in the humidity range 10 % to 90 % [214]. |
|
ADA_022 |
The adaptor shall be protected against over-voltage, inversion of its power supply polarity, and short circuits [216]. |
|
ADA_023 |
The adaptor shall either:
|
|
ADA_024 |
The adaptor shall conform to international regulation UN ECE R10, related to electromagnetic compatibility, and shall be protected against electrostatic discharges and transients [218]. |
4.6. Materials
|
ADA_025 |
The adaptor shall meet the protection grade (TBD by the manufacturer, depending on the installation position) [220, 221]. |
|
ADA_026 |
The colour of the adaptor housing shall be yellow. |
4.7. Markings
|
ADA_027 |
A descriptive plaque shall be affixed to the adaptor and shall show the following details:
|
|
ADA_028 |
The descriptive plaque shall also show the following details (if not directly readable from the outside on the embedded motion sensor):
|
5. INSTALLATION OF THE RECORDING EQUIPMENT WHEN AN ADAPTOR IS USED
5.1. Installation
|
ADA_029 |
Adaptors to be installed in vehicles shall only be installed by vehicle manufacturers, or by approved workshops, authorised to install, activate and calibrate digital and smart tachographs. |
|
ADA_030 |
Such approved workshop installing the adaptor shall adjust the input interface and select the division ratio of the input signal (if applicable). |
|
ADA_031 |
Such approved workshop installing the adaptor shall seal the adaptor housing. |
|
ADA_032 |
The adaptor shall be fitted as close as possible to that part of the vehicle which provides its incoming pulses. |
|
ADA_033 |
The cables for providing the adaptor power supply shall be red (positive supply) and black (ground). |
5.2. Sealing
|
ADA_034 |
The following sealing requirements shall apply:
|
6. CHECKS, INSPECTIONS AND REPAIRS
6.1. Periodic inspections
|
ADA_035 |
When an adaptor is used, each periodic inspection (periodic inspections means in compliance with Requirement [409] through to Requirement [413] of Annex 1C) of the recording equipment shall include the following checks:
|
|
ADA_036 |
These inspections shall include a calibration and a replacement of all seals, whatever their state. |
7. TYPE APPROVAL OF RECORDING EQUIPMENT WHEN AN ADAPTOR IS USED
7.1. General points
|
ADA_037 |
Recording equipment shall be submitted for type approval complete, with the adaptor [425]. |
|
ADA_038 |
Any adaptor may be submitted for its own type approval, or for type approval as a component of a recording equipment. |
|
ADA_039 |
Such type approval shall include functional tests involving the adaptor. Positive results to each of these tests are stated by an appropriate certificate [426]. |
7.2. Functional certificate
|
ADA_040 |
A functional certificate of an adaptor or of recording equipment including an adaptor shall be delivered to the adaptor manufacturer only after all the following minimum functional tests have been successfully passed.
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||